Code 41 - What is it?
Poor PC maintenance can lead to error message pop-ups like error code 41. Code 41 is one of the several Device Manager Error codes.
This error indicates 2 things: issues with the device driver for the hardware you wish to use, or the hardware device is not properly attached to your system.
The error code 41 is usually displayed in the following format:
“Windows successfully loaded the device driver for this hardware but cannot find the hardware device.”
Code 41
Solution
 Error Causes
Error Causes
For successful installation of a new hardware piece, it is imperative to follow the installation routine correctly and allow it to complete properly, especially with USB devices.
This is important largely because if installation is not followed and executed properly, code 41 can pop up.
Code 41 is also related to device driver problems. It can occur if your system device drivers are outdated. Also, if the device is a CD/DVD drive, code 41 can occur due to conflicts with 3rd party disc burning software.
Although Device Manager Error code 41 is not detrimental, it is still advisable to repair it as quickly as you can. Code 41 can negatively affect your PC. It can:
- Lower your PC’s Performance
- Limit your ability to use your desired piece of hardware device
Further Information and Manual Repair
As compared to the blue screen of death errors, Device Manager Error codes are much easier to resolve.
Here are some of the best, effective and easy-to-resolve methods to help you fix code 41 on your PC, in a few minutes.
To work around these methods, you don’t have to be a technical whiz or a computer programmer. Simply follow these steps to resolve:
Method 1 - Uninstall Faulty Drivers and then Reinstall
To repair code 41 on your system, try uninstalling problematic drivers and then reinstalling new drivers. To do this, follow these instructions:
- Click the start button
- Then type Device Manager in the search bar and press enter
- Once the Device Manager opens, look for problematic devices
- Click on the device whose driver you wish to uninstall
- Double click to uninstall
- Windows will prompt you to confirm the device removal
- Accept changes and confirm by clicking on OK
- Now reboot your PC to activate changes
- The next step is to reinstall the driver properly. To do this, simply follow the same steps. Once you access the Device Manager,
- Click on the Action tab in the toolbar
- After that select the option ‘Scan for Hardware Changes’
This will hopefully resolve error code 41 on your system and you will be able to use your desired hardware device without any hassle. Nonetheless, if the error code continues to persist, try other methods illustrated below.
Method 2 - Replace the Hardware or Try Reattaching it to your System
Sometimes the error may pop up due to poorly configured devices. This is common if it is a plug-and-play device. The best way to resolve is to remove the device, reattach it properly, and then try using it again.
However, if the problem is with the hardware, then it is advisable to replace the hardware with a new device compatible with your Windows version.
Method 3 - Update the Drivers Manually
If the underlying cause for error code 41 is outdated or corrupted drivers, then it is advisable to update the drivers.
However, when updating drivers and ensuring that the newly installed drivers work perfectly, make sure you install versions that are compatible with your device and Windows. Incompatible drivers are no good.
You will continue to face Device Manager Errors if you install incompatible drivers.
To update drivers, here’s what you have to do:
- Identify the problematic drivers
- Go to the Device Manager and locate all drivers with yellow exclamation marks
- Now install new and compatible driver versions from the manufacturers’ site
Method 4 - Download Driver Assist to Update Drivers Automatically
Updating drivers manually will take time, so perform this task when you are free and have nothing else on your mind. However, if you wish to resolve the issue immediately and have the time to invest in manual updates, then consider downloading DriverFIX.
DriverFIX is a feature-rich and an innovative software program deployed with an intelligent programming system and intuitive technology.
It is exclusively designed to resolve PC device driver problems. Once installed on your system, it scans your PC and identifies problematic drivers.
After that it matches latest and compatible driver versions and updates them immediately within a few seconds. DriverFIX updates drivers both automatically and on a regular basis.
Click here to download DriverFIX to update drivers and repair error code 41.



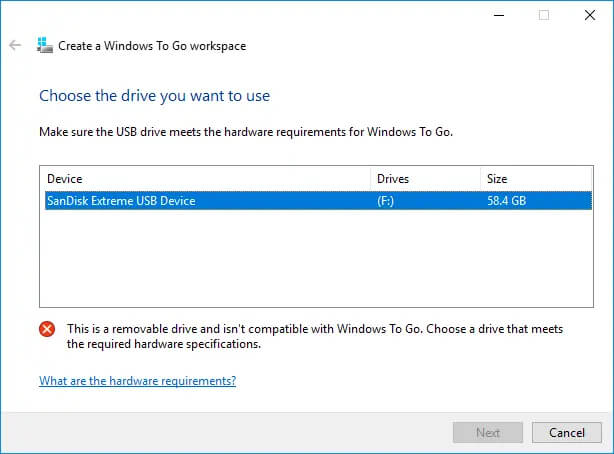 Many Linux users if not all of them can run their distros from a USB drive but did you know you can run Windows 10 from a USB drive as well?
Microsoft has introduced all the way back to Windows 8 one feature called Windows To Go and it kept it in Windows 8.1 and in Windows 10 as well.
This feature is intended as a convenient way for workers to carry their corporate environments with them, but having your own copy of Windows on a thumb drive could be handy for backup purposes, too, or if you frequently use public machines that lack your preferences/applications or that have a restricted OS.
Many Linux users if not all of them can run their distros from a USB drive but did you know you can run Windows 10 from a USB drive as well?
Microsoft has introduced all the way back to Windows 8 one feature called Windows To Go and it kept it in Windows 8.1 and in Windows 10 as well.
This feature is intended as a convenient way for workers to carry their corporate environments with them, but having your own copy of Windows on a thumb drive could be handy for backup purposes, too, or if you frequently use public machines that lack your preferences/applications or that have a restricted OS.
