Outlook PST Errors
Problems occur when your PST file becomes corrupted or hits the size limit. Outlook will start to display error messages. These errors include like 0x80040119, 0x80040600, and 0x8004060c.
Error Causes
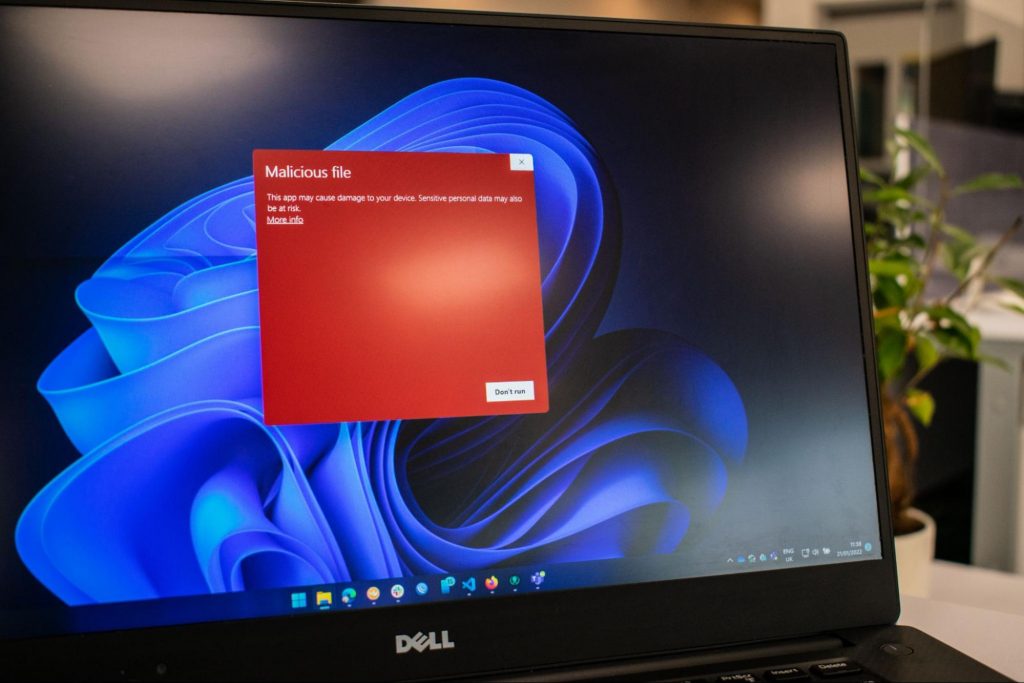
You might think Outlook problems are just a minor inconvenience. You can’t access your emails and contact information, but that doesn’t actually affect computer security, right? Wrong! Outlook problems can indicate serious corruption issues within your system.
In many cases, your PST file can even be targeted specifically by a virus.
Today, many viruses are specially designed to steal personal information and then sell that information on the online black market. Since so much personal data is stored within Outlook’s PST file, this is often the first place that viruses look.
If you don’t want some hacker in a foreign country to read your emails, steal your contact information, or do all sorts of other dangerous tasks, then we advise you to fix your PST problem as soon as possible.
Other causes include hitting the 2GB memory limit on older versions of Outlook, erroneous SMTP settings, etc,.
Further Information and Manual Repair
PST errors are an incredibly annoying problem. However, thanks to powerful software like Stellar Phoenix Outlook PST Repair, it has never been easier to fix Outlook and recover all of the data inside your PST file. That means that you won’t lose contact information, calendar entries, emails, or any other information stored in Outlook.
ScanPST.exe rarely fixes problems with the PST file. Since the application is only a few megabytes in size, its effectiveness is very limited. Although Microsoft designed ScanPST.exe to be an effective solution to any PST files, it fails miserably.
Better Alternatives to Microsoft's ScanPST.Exe
Ultimately, after downloading ScanPST.exe and running it, your Microsoft Outlook will still be unable to send or receive emails. And, to make matters worse, you might also be unable to access contact data or read your old emails.
Unlike other PST repair solutions, ScanPST.exe will not recover deleted emails or other lost Outlook data. In fact, using ScanPST.exe can sometimes cause your personal data to become even more difficult to recover.
If you do want to try out ScanPST.exe, then go ahead. While it probably won’t make your PST errors worse, it won’t even come close to fixing them. If you’re ready for a more serious solution to PST problems, then keep reading.
Why are Outlook problems dangerous?
You might think Outlook problems are just a minor inconvenience. You can’t access your emails and contact information, but that doesn’t actually affect computer security, right? Wrong!
Outlook problems can indicate serious corruption issues within your system. In many cases, your PST file can even be targeted specifically by a virus.
Today, many viruses are specially designed to steal personal information and then sell that information on the online black market. Since so much personal data is stored within Outlook’s PST file, this is often the first place that viruses look.
If you don’t want some hacker in a foreign country to read your emails, steal your contact information, or do all sorts of other dangerous tasks, then we advise you to fix your PST problem as soon as possible.
How do I actually fix Microsoft Outlook PST errors?
Microsoft’s ScanPST.exe application clearly doesn’t work. So what’s the next best option? Well, a program called Stellar Phoenix Outlook PST Repair has been helping PC users solve Outlook problems for several years. As the world’s leading Outlook solution, Stellar Phoenix Outlook PST Repair will quickly and effectively repair any PST problems you encounter.
So how does Stellar Phoenix Outlook Repair work? Well, it starts by finding your PST file. Once the PST file has been found, Stellar Phoenix Outlook PST Repair determines if the file is corrupt or full. It will then repair your PST file either by removing the size limit or by fixing the corrupt files.
How Does Stellar Phoenix Outlook Repair Work?
Once Stellar Phoenix Outlook PST Repair determines that your calendar appointments, contact data, and emails have all been successfully recovered, it permanently restores access to your PST file.
In fact, Stellar Phoenix Outlook PST Repair can even restore Outlook data that you deleted a long time ago. So, instead of just being a PST error recovery tool, Stellar Phoenix Outlook PST Repair is also a powerful data recovery program.
After letting Stellar Phoenix Outlook PST Repair go to work, open up Outlook and try it out. You’ll have full access to all of your Outlook files and folders, and all of those ScanPST.exe problems will be a thing of the past.
Advantages of Stellar Phoenix Outlook PST Repair Software
Stellar Phoenix Outlook PST Repair comes with many advantages. Here are just a few reasons why it’s such a popular program:
- Easy-to-use: Don’t worry if you’re not a computer genius. Stellar Phoenix Outlook Repair is incredibly easy to use. Even if you barely know how to send an email over your computer, the program has a straightforward interface that anybody can understand. If you can click the left mouse button, then Stellar Phoenix will be easy to use.
- Goes to work instantly: It takes only seconds to download and install Stellar Phoenix Outlook PST Repair. Once you’re ready to perform a scan, the program goes to work instantly. It identifies your PST file in an incredibly short amount of time, and before long, you’ll be able to access Outlook once more.
- Effective: Unlike the infamously useless ScanPST.exe application, Stellar Phoenix Outlook PST Repair actually works like it’s supposed to. It allows users to safely recover all of their most important data. While ScanPST.exe can actually damage your PST file, Stellar Phoenix Outlook PST Repair simply goes to work quickly and effectively.
- Multiple support packages: Stellar Phoenix Outlook Repair comes with three different pricing plans. One is designed for people who only need to install the program on a single computer. Another is designed for businesses or households that want to install the program on multiple PCs.And with the third option, the technician package, users can install Stellar Phoenix Outlook PST Repair on an unlimited number of computers. One of the biggest advantages of these packages is that you can spread out the cost of the program among multiple users. If several different people at your workplace are having PST error problems, for example, then you can buy a multiple-license package and share the cost.
- Data recovery: Along with fixing corrupt PST files and removing the size limits from the PST file, Stellar Phoenix Outlook PST Repair can actually recover any Outlook data on your computer. This is useful if you uninstalled Outlook a few months ago but still need to recover that data. In fact, Stellar Phoenix can recover Outlook data even if Outlook is not currently installed on your computer. In that sense, Stellar Phoenix Repair is more than just an Outlook repair program; it’s also a full-service data recovery solution.
Stellar Phoenix PST Repair is superior to ScanPST.exe in every way. But Stellar Phoenix’s most important advantage is that it actually works. If you’re ready to quickly fix your Outlook PST errors, then Stellar Phoenix Outlook PST Repair can help. Download it here today to experience the magic of PST repair for yourself.
 Error Causes
Error Causes