The Internet has come a long way from its infant stages and has become so large and huge that it has gained the status of basic human rights. There are very useful information and a lot of great content on it and among them, there are social media websites and other types of websites where you have, most likely placed some personal pictures or other information.
One day you might want to cancel some of the services or you would like to take a break from it all. In this guide we will show you how to do exactly that, to delete and remove your data from the internet.
How to Delete Your Google Account
Google is arguably one of the most visited places on the Web. It stores a huge amount of data for delivering personalized content. It saves personal information, web searches, watched videos, location data, etc. You can view a summary of the data saved by different Google services by visiting your
Google Dashboard.
To delete personal data from Google, go to
myactivity.google.com. Select the
Delete activity by from the left menu to start deleting activities.
Select
All time to delete all of your activities from different Google services. You can also delete
files saved to Google services, such as Google Photos, Google Drive, and Keep. Just visit the site, select the files, and delete them.
Note that Google retains some information even after you delete all data. They do this to meet business needs and legal requirements. These will be deleted when you delete your Google account altogether.
How to Delete Your Facebook Account
Facebook stores a huge amount of data for each user. Some of the personal information stored in Facebook’s databases includes name and email, check-ins, location, images, videos, events, etc. You can view and download all of your personal data using
Facebook’s information download tool. However, you will need to delete your account altogether for removing your personal data from Facebook.
Follow the below steps to delete your Facebook account.
- Log in to your Facebook account and go to Settings & privacy > Setttings.
- Select Your Facebook Information.
- Select Deactivation and Deletion.
- Select Delete Account.
- Select Continue to Account Deletion.
- Select Delete Account.
- Enter your password and click Continue.
It can take up to 90 days for Facebook to delete your personal data from the Internet. You will not be able to access any of the data once the deletion starts. However, you can cancel this within the first 30 days.
Twitter has also followed in the footsteps of Facebook when it comes to harvesting your personal data. It utilizes this information for delivering personalized ads and tweets. You can download an archive of all of your personal data from Twitter. It makes it easy to monitor what information is available to the platform.
Click the
More button from the left menu and head over to
Settings and privacy. Follow the below steps to download your personal information.
- Select Download an archive of your data from the Your Account section.
- Select Request archive from under the Twitter data section. Enter your password when prompted.
- It will take some time for Twitter to make the data available to you. You’ll receive an email once the data is ready to be downloaded.
It would be best if you also restrict data sharing and off-site activities. Head over to
Privacy and safety and inspect the options under the
Data sharing and off-Twitter activity section.
Look in the
Interests and
Your advertiser list sections from the
Ads preferences tab. You can disable Twitter from tracking you in the
Off-Twitter activity tab. Uncheck the options from the
Data sharing with business partners and
Location information tabs.
Finally, you need to deactivate your account for deleting all personal information from Twitter. You’ll have 30 days to reactivate the account. After that, Twitter will begin erasing your information from its systems. Note that they can still retain some information subjected to platform regulations.
How to Delete Your Instagram Account
Instagram has risen to prominence in the last couple of years. The company collects a huge amount of personal information from its users, including media, name, email, and much more. You’ll need to deactivate your account altogether if you want to delete everything Instagram knows about you.
Head over to the
Delete your account page and select the reason you want to delete it. Enter your Instagram password to verify your identity, then click on the Delete button. Instagram will hide your account details for the next 30 days and delete all personal data after the given period.
How to Delete Your TikTok Account
TikTok is another emerging platform that has become quite popular among millennials. Users share a lot of personal information through personalized music videos. You need to delete your TikTok account permanently to remove all personal data from TikTok.
To do this, head over to
Me, then tap on the
… icon in the top-right corner of the window. Select
Delete account from under the
Manage Account section. Follow the instructions provided there to continue deactivating your account. Like Instagram, TikTok also offers a 30-day time period to allow users to change their minds. It will delete your personal data from the Internet after this period.
How to Delete Your Snapchat Account
- Go to Snapchat’s Accounts Portal and log in with your name and password.
- Select the Delete My Account option.
- You’ll be taken to the Delete Account page directly.
- Retype your password once more.
- Click on the yellow Continue button.
Do keep in mind that Snapchat will hold on to your data for another 30 days, just in case you change your mind and decide to return. If you do decide to come back, all you need to do is visit the Accounts Portal again and log in to your account. This will reactivate your account. While your account is in this deactivated phase, your friends will not be able to contact you or interact with you in any manner on Snapchat. After the 30-day period has elapsed, your account will be permanently deleted.




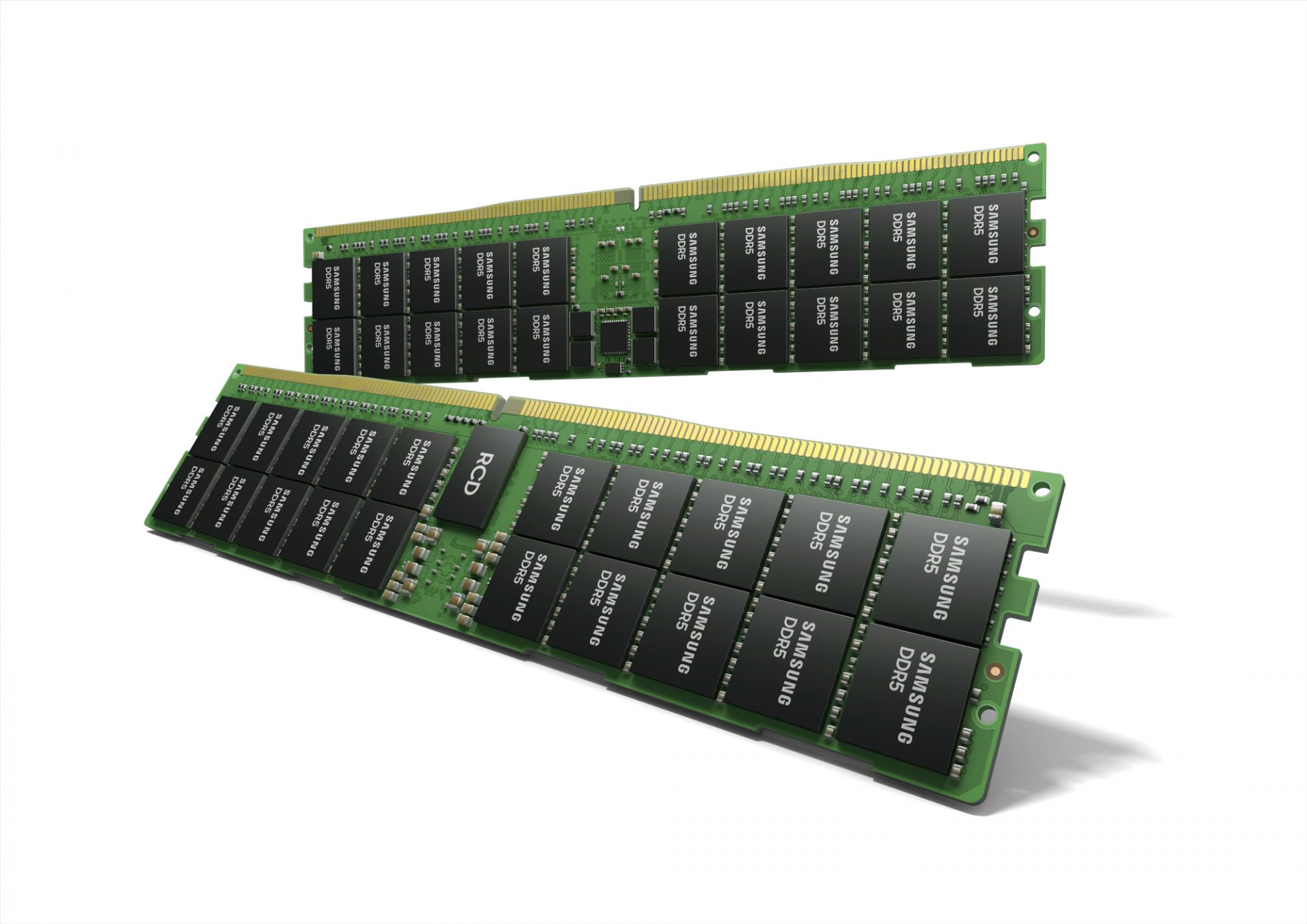 Next-generation of RAM, DDR5 supposed to hit shelves around late summer or fall in 2021if everything goes as planned.
Its goal is to increase speed and efficiency, wants to pack more memory in a single stick, and have better power management.
Next-generation of RAM, DDR5 supposed to hit shelves around late summer or fall in 2021if everything goes as planned.
Its goal is to increase speed and efficiency, wants to pack more memory in a single stick, and have better power management.
