There are cases when you want to undo some changes you’ve made to your computer and to do that you have to perform the System Restore task. However, if you encounter an error that states “To use System Restore you must specify which Windows installation to restore”, when doing so, read on as this post will help you fix the problem.
This kind of error in System Restore could be due to corrupted files in the system. There are also situations where you are not able to boot up once you encounter this error which could be a big problem. On the other hand, this error might have something to do with corrupted BCD files. Whatever the cause is, here are some potential fixes you have to try.
Like pointed out, since the error might be due to corrupted system files, you can try to run System File Checker offline. How? Refer to these steps:
You can also run the DISM tool to repair the potentially corrupted system image. First, you have to check the health of the system like checking the integrity of the system files and Windows services. To run DISM, follow the given steps below sequentially.
As mentioned, the error could also be due to corruption in BCD, and to fix it, you can use Bootrec.exe – a built-in command-line tool used to troubleshot issues related to boot up and Windows Startup. Before you run this tool, make sure that you have inserted a bootable USB or DVD into your computer. Once you have that covered, follow these steps:
You might also want to use Automatic Repair in fixing the error. To do so, follow the steps below.
If the four options given above didn’t help fix the problem, you could try running Windows Repair and a Windows bootable USB or DVD.
Since you probably can’t boot into your Windows 10 computer, you can try to run System Restore again in the Advanced Startup Options.
Note: You need to replace “C” with the drive where Windows Installation is located.

When you upgrade your Windows 7 or Windows 8.1 system to Windows 10, you’ll undergo a phase called Out of Box Experience, or simply OOBE. This phase is intended to allow users to customize their Windows 10 experience, which includes defining personal settings, creating user accounts, and more. Some users reported having issues when creating their user account during the Out of Box Experience (OOBE) on Windows 10 upgrade. Some also reported issues about non-responsive behavior (Welcome Back) page.
 Error Causes
Error CausesUnfortunately, there’s no known cause for this error. However, some users reported that this occurs when:
Your Windows 10 upgrade will not be successful if you’re not able to create a user account or finish the Out of the Box (OOBE) phase of the installation. Here are some methods that will help you fix this manually.
Some users reported that waiting for about an hour and retrying the process again will solve this problem. It’s also recommended that you keep your computer in a ventilated place while you wait to retry the process.
This method has 2 requirements in order to work.
If you meet these two requirements, you can solve the error by following the steps below:
This method only applies if you’re a laptop user.
Instead of connecting to a Microsoft Account after the set-up, you might want to try creating a local account. To do this, follow the steps below:
If the steps above don’t work, you might want to try Startup repair.
In order to do this step, you need to have official Windows 10 ISO files.
After doing the steps above, there’s a chance you get an error message that says “installation cannot be completed in safe mode”. When you see this, just press Shift+F10. This will execute and open the command prompt of your computer.
From the command prompt, you can try and create a new user account.
For example, net user Username Password /add
The username here should be replaced with the account name you want to add, and the Password here should be replaced with the password you want to use for the account.
After replacing the username and password on the text, press the Enter button on your keyboard. You’ll know if the command is successful once you see the message, “The command completed successfully.”
You can now close the command prompt. Restart your computer and try to log in using the account you just created.
If all the above methods still don’t work, it might be best to try automated software to help you fix this problem.
So, you have finished with work, game, movie, music, email, or whatever on your PC, you look at the clock, it is late, you decide to go to sleep or outside, you click on the power button and choose shutdown. Now when a PC is shut down you feel good and go with your business but the next time you power it up you get the same error like the computer never really shut down in the first place. You wonder why and reboot it, just in case and all of the sudden error is gone.
If something similar has happened to you or you had the feeling that after shutting down your computer has not really felt like shutting it down, do not seek professional help, everything is OK with you because when you click on shut down, your computer does not really shut down!
Truth is that Microsoft has changed how to shut down works and how rebooting works in Windows with an update but has not publicly said anything about it so some users may experience this feeling of not shutdown phenomenon and might even think there is something wrong with their PC.
A few years ago shutdown button and option in Windows were really shutting down OS, but things changed when Microsoft wanted to increase boot-up speed. Now when that decision was made shutdown option was changed. So, what was changed? Well in order to increase Windows booting time, the shutdown will now turn off power to PC components and it will look like everything is indeed shutdown but the Windows kernel will actually be saved to a hard drive with all settings and just awaken once the PC is turned back ON. This will result in all errors and other stuff being just still present same as they were once the system was instructed to be turned off.
Rebooting your PC will now clear kernel and file from the hard drive and you will get a clean system startup without any issues tied with the kernel itself.
Now that we know why and what change has been made to Windows logical question is can we shut down our PC at all properly? Luckily for us, the answer is yes and we will not need any external application to do it, we can still do it inside Windows itself and it is quite quick and easy.
In order to bring the old shutdown functionality of your PC please follow the instructions but be aware that by doing this your PC will boot a little bit slower since it will have to load the kernel from scratch each time computer is turned ON.
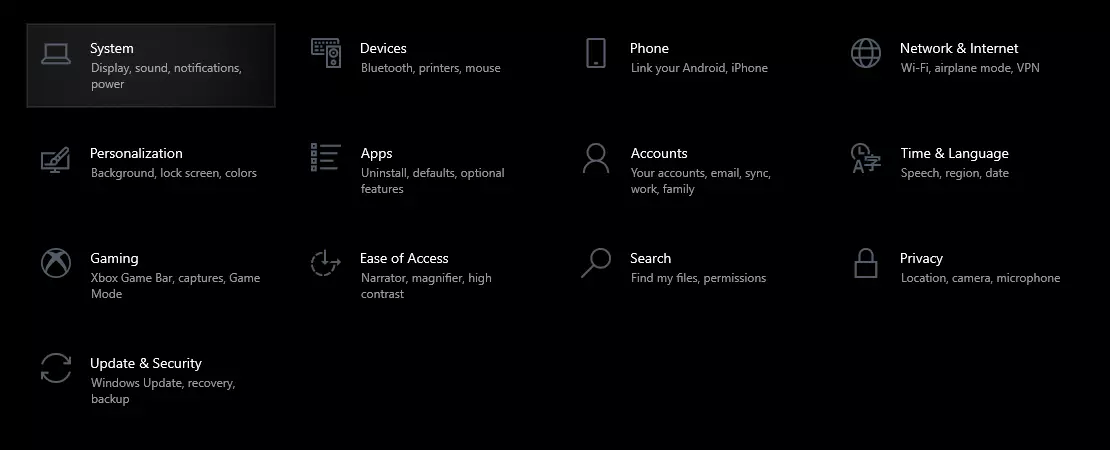
First thing is to go to settings and go to System
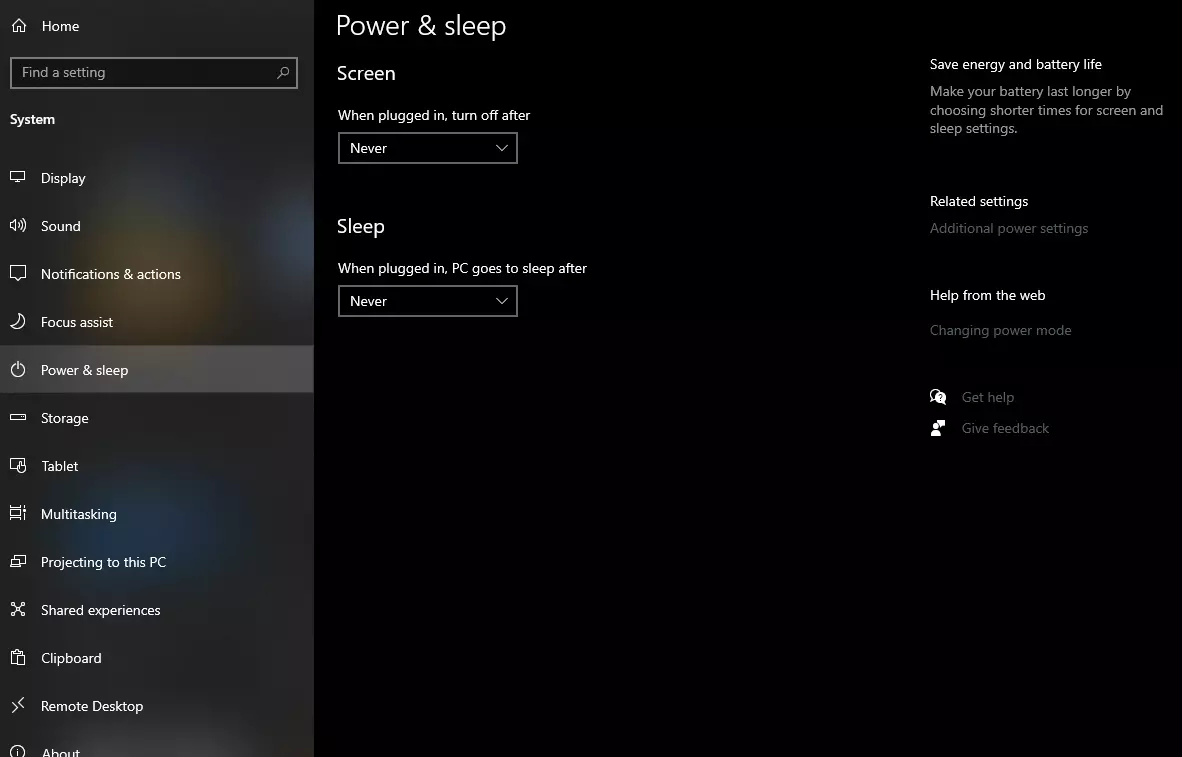
Then once you are inside the system, navigate to the power and sleep and click on it to select it. Once you have it selected to all the way to the right and click on additional power settings.
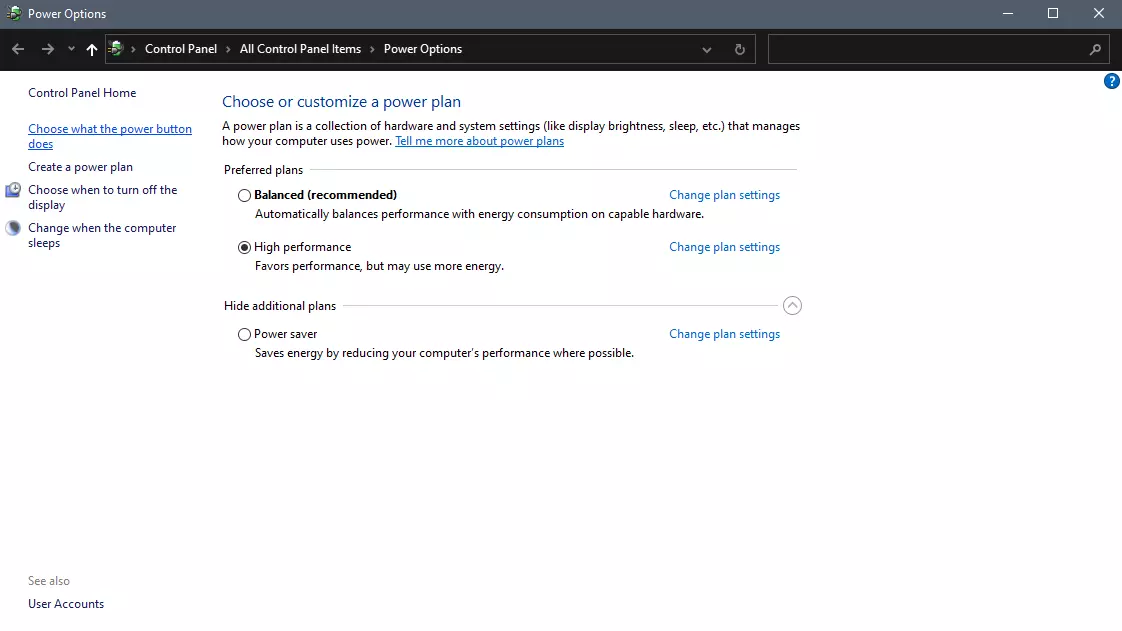
When you click on advanced power settings you should be led to the control panel's power options. Inside this panel click on top left link where it says Choose what the power button does.
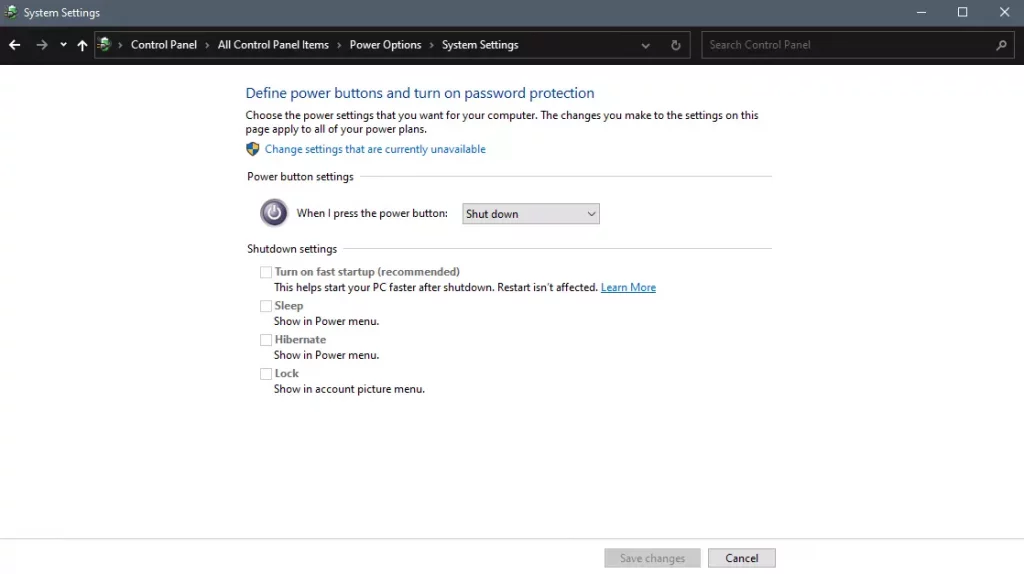
Inside options, you will need to untick the box next to Turn on fast startup (recommended), this option has been ticked ON by the Windows update and probably without notifying you. Option means exactly what was described, it will save kernel state on the hard drive for faster boot time but sadly it can cause some issues since it will never be reloaded from 0.
If you are unable to uncheck the box click on the text beside the shield icon that says: Change settings that are currently unavailable (you will have to be logged in as administrator).
Altho turning off fast startup and shutting down the PC completely will for sure extend your bootup time I still believe that it is the right choice since sometimes a lot of clutter and bad things accumulate over time inside the OS and can cause a vast variety of problems in a long run. So stay safe and shut down that PC as it used to be in the past.
Error Code 0x80070032 is a command that most often relates to codes or commands that have not been entered correctly or do not apply to the given program. It can also appear when mail folders in Windows Mail are not able to sync in the way that they should between the local device and the servers owned by Microsoft.
Common symptoms include:
The primary methods used to address Error Code 0x80070032 are fairly basic and easy to complete. Most users should be able to complete these methods on their own and they do not require a lot of time to do. However, if you don’t feel like you have the experience, skills, or knowledge necessary to complete the steps listed below, consider getting in touch with a qualified Windows repair technician to assist you.
 Error Causes
Error CausesThere are three basic methods that users can try in order to resolve Error Code 0x80070032 on their machine. These are fairly simple and easy to complete. However, if the methods below aren’t successful in resolving the error code or if you do not feel confident in your ability to use them, get in touch with a certified Windows repair professional to assist you.
If you believe that you are seeing the error due to entering a command that didn’t work, use Method One first. If you believe it is due to a mail syncing error, use Methods Two or Three.
Here are the top methods for addressing Error Code 0x80070032:
If you believe that you are experiencing Error Code 0x80070032 because of a command that you have entered, the best solution is to reinstall the program in which you were entering the command. You may also want to try updating your program, if able, before reinstalling it. Remember to restart the computer before reattempting to enter in the command that caused the error.
For many users, Error Code 0x80070032 appears because of a bug in one of the versions of Windows 10. If you believe that this is the case, open up your Windows Updates and check to see if there are any updates that you can install.
For users who are only seeing Error Code 0x80070032 because of the bug mentioned above, Windows released an update that should address the error code on its own. If your computer is fully updated, the error may be resolved on its own. Always remember to restart your computer after installing updates so that the necessary changes can take effect.
If the above methods did not resolve the problem successfully, you can switch to local access to your Windows Mail, rather than relying on Microsoft access. To do so, complete the following steps:
Once this is done, you can switch back to your Microsoft account, which should reset your syncing ability. Follow these steps to switch back:
Premiere Download Manager is a Browser Extension that comes bundled with Premiere Download Manager Potentially unwanted program, and other unwanted applications and extensions. This program was developed by Mindspark Interactive and offers users the ability to download files off the internet through the Download Manager provided. It also changes the home page and defaults the search engine to Myway.com.
This bundle monitors the user’s activity, and while the extension has access to your browsing activity, clicked links, visited pages, etc. the application itself has access to all the files that you downloaded, and have on your computer. This gathered data is later sent back to Mindspark’s servers where it is used to better target ads for users.
While installed, you will run into additional, sponsored links, and even pop-up ads while browsing the internet. Though it is not considered malware, it contains many behaviors disliked by users and is labeled as potentially unwanted. This bundle has been marked as a Browser Hijacker by several anti-virus applications and is therefore recommended to remove from your PC.