Symptoms of Blue Screen of Death Errors
Symptoms of a blue screen of death problem are easy to identify: if you have a blue screen error, then your computer will display a blue screen.
Also known as the infamous “Blue Screen of Death”, this screen will pop up when something goes horribly wrong with your computer. The screen displays cryptic information about the problem before automatically restarting the system.
Bluescreen Of Death Errors Solution
Download Available To Completely Repair Blue Screen of Death Errors
Recommended: Download the Automatic Repair Utility to correct this and other PC performance issues.
 Bluescreen Error Causes
Bluescreen Error Causes
This one can be a bit more complex: blue screens are caused by hundreds of different things. In fact, any miscommunication between the hardware and software of the computer can lead to the dreaded Blue Screen of Death, blue screens reference a communication problem between the Windows operating system and the hardware in your PC.
Why do computer blue screens of death errors occur?
Most computer users have experienced a blue screen of death at least once in their life. But have you ever stopped to wonder why they occur?
Blue screens of death can occur for a number of different reasons, but the most common reason is that your PC’s hardware failed to properly communicate with its software, resulting in a fatal error.
If your video card, processor, hard drive, or any other vital system component encountered a serious communication error with your operating system, then your PC may automatically display the blue screen and shut down for its own safety.
Blue screens can also occur as a self-protection mechanism if the PC is overheated.
Further Information and Manual Repair
Where do Windows blue screen errors come from?
Blue screen errors come from many different sources on your computer. However, the majority of blue screen errors seem to come from the
Windows Registry, which contains important configuration information about the programs, data, and personal files on your PC.
Windows constantly rely on the registry in order to operate normally, but since the registry is incredibly complex (it holds hundreds of thousands of files), errors naturally develop over time.
Fortunately, registry errors are fixable. They can be repaired using special
registry cleaning software. During a scan, registry cleaning software looks for any registry entries that have errors. Once these entries are found, the software automatically repairs each entry.
In many cases, this can permanently repair the blue screen error and prevent blue screens from ever appearing again.
Blue screen Windows 7
Windows 7, despite being Microsoft’s most popular operating system to date, is not immune to blue screen errors. It’s more stable than previous versions of Windows, although many users will inevitably encounter blue screen errors in Windows 7.
No matter which version of Windows you’re currently using, the error remains the same: the hardware on your computer has trouble communicating with the software, forcing the system to display the blue error message we all love to hate.
“Blue Screen of Death”
There’s a reason this error message is famously called the “blue screen of death.” Immediately after displaying a blue screen, the Windows computer will ‘die’, which means that it restarts itself.
Another reason why the error could be called the blue screen of death is that it is often displayed at the end of a PC’s life cycle. As PCs get older and their hardware starts to fail, blue screen errors become more and more common.
In real life, death isn’t reversible. In the computer world, blue screens of death certainly are. With the right software support – like Restoro – even the most novice computer technician can fix their blue screen errors and restore their PC to healthy working conditions.
Benefits Of Using Restoro, BSOD Error Codes
Restoro is one of the world’s most popular PC optimization programs. Used by professional PC technicians around the world, Restoro is a feature-rich software suite that has helped many PC users breathe new life into an old PC.
Restoro optimizes computer performance in hundreds of different ways. It looks through the registry and repairs any erroneous entries it finds. It also hunts down and eliminates malware and goes to work with the press of a button. And most importantly for you – it’s also amazingly effective at repairing blue screen errors.
Ready to experience the Restoro difference? Here are a few more advantages of our favorite software program:
- Easy for anyone to use: A few years ago, only the most tech-savvy individuals could optimize their computer’s performance. Everybody else had to pay for expensive tech support or simply buy a new computer. Thankfully, the software development community has come up with innovations like Restoro which are easy for anyone to use. Just click a button and your computer will be clean within minutes. The process could not be easier.
- Surprisingly fast: There are hundreds of thousands of files in the Windows Registry. In spite of that fact, Restoro goes to work incredibly quickly. It scans the depths of your PC in an effort to uncover whatever is causing your blue screen errors. The entire scan is complete within just a few minutes, making it easy for anyone to scan their computer on a regular basis.
- Free trial: It’s good to be skeptical. And if you don’t think Restoro will fix any of the errors your computer is experiencing, then that’s okay. However, when you download the free Restoro, you can instantly scan your computer for errors. If any errors are found during this scan, then you can repair these problems with the click of a button.
- Fixes frustrating errors: Blue screen errors are incredibly frustrating. You can’t get any work done on your computer when experiencing a blue screen problem. For that reason, Restoro helps alleviate some of the most frustrating PC problems in the world today.
- More than just blue screen repairs: Sure, blue screens are annoying. But they’re only one of many different errors that a PC can develop over time. Fortunately, Restoro does more than just fix blue screen errors. The software also identifies and repairs other problem areas on your PC, making it easy to optimize performance.
Ready to get rid of your blue screen errors – permanently?
Restoro today!
 Bluescreen Error Causes
Bluescreen Error Causes
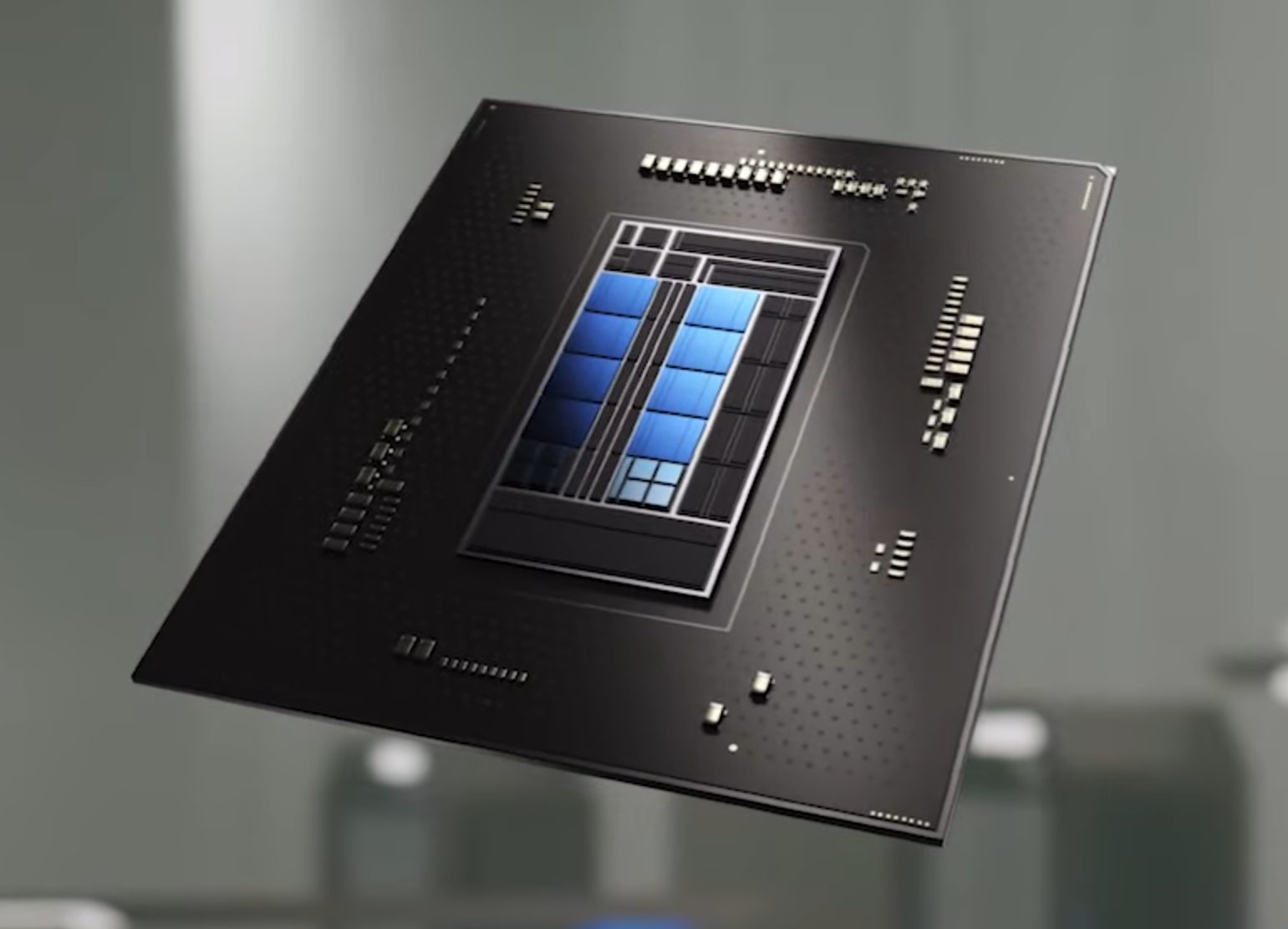 Now before you go on the bandwagon on bashing Intel itself take note that it is not Intel’s fault at all. The issue that arises is mostly due to DRM software and how it works. As you might know or not, Alder Lake has two sets of cores, standard performance cores, and power cores, and with Intel’s Thread Director on-chip right cores will be used for the right tasks, and here lies the issue.
DRM software might detect Thread Director as something suspicious and malicious, and then cut access to the game because of this. Intel, of course, has reached DRM manufacturers and places documentation about how software should be developed with this hybrid technology in mind.
Of course, newer games will be updated if needed and everything will work fine, also games on GOG will work fine because of GOG’s policy of no DRM store but some older ones might be left in limbo. They could work fine but DRM might be triggered and prevent them from loading, usually, game developer itself removes DRM protection after some time but that is not really always the case and there is a chance that some games might simply just not work on Alder Lake CPU only because of DRM protection.
Now before you go on the bandwagon on bashing Intel itself take note that it is not Intel’s fault at all. The issue that arises is mostly due to DRM software and how it works. As you might know or not, Alder Lake has two sets of cores, standard performance cores, and power cores, and with Intel’s Thread Director on-chip right cores will be used for the right tasks, and here lies the issue.
DRM software might detect Thread Director as something suspicious and malicious, and then cut access to the game because of this. Intel, of course, has reached DRM manufacturers and places documentation about how software should be developed with this hybrid technology in mind.
Of course, newer games will be updated if needed and everything will work fine, also games on GOG will work fine because of GOG’s policy of no DRM store but some older ones might be left in limbo. They could work fine but DRM might be triggered and prevent them from loading, usually, game developer itself removes DRM protection after some time but that is not really always the case and there is a chance that some games might simply just not work on Alder Lake CPU only because of DRM protection.
