Windows 10 setup is a bit complicated which is why it’s uncommon to encounter errors along the way. One of these errors you can encounter when running Windows Setup is the error code 0x80070006. If you are trying to fix this error, you’ve come to the right place as this post will guide you on how to do so.
When you get the error code 0x80070006, you will see the following error message:
“Windows cannot install required files. Network problems may be preventing Windows from accessing the file. Make sure the computer is connected to the network and restart the installation. Error code: 0x80070006.”
As stated in the error message, this kind of error in Windows Setup is due to an unstable or unreliable network connection. Such problems can also be triggered by network hardware which includes the network adapters and the network routers. To fix this error, you need to check your internet connection and router or run the built-in network troubleshooter. You could also try using a different USB port or recreate a bootable USB drive as well as get a new Windows image file.
Option 1 – Try checking your internet connection and router
As mentioned, this Windows 10 setup error could be due to an unstable internet connection. To fix it, the first thing you have to do is to check the status of your internet connection and see if it is stable and has enough speed to run the setup. If it’s slow, then it’s no wonder that the setup process failed. To fix that, you can try to reboot your router from its admin panel or you can just turn it off manually and then turn it back on after a couple of seconds. In addition, you also have to check if it’s plugged in properly.
Option 2 – Try to run the Network Adapter troubleshooter
The next thing you can do is to run the Network Adapter troubleshooter. This built-in troubleshooter can help resolve any network issues. It can reset the adapters, remove cached settings, and many more. To run it, follow these steps:
- Go to Settings > Update & security and from there select Troubleshoot.
- Next, scroll down and select the “Network Adapter” option from the right pane.
- Then click on the Run Troubleshooter” button.
- After that, your computer will check for any possible errors and will pinpoint the root cause of the problem if possible.
Option 3 – Try to use a different USB port
You might want to check the integrity of the USB port where connected the device if you are using a bootable USB storage device to run the setup for Windows 10. All you have to do is switch the USB port or try to use another bootable USB device and see if it fixes the problem.
Option 4 – Try recreating the Windows 10 installation USB
Recreating the Windows 10 installation USB might help in fixing the problem. You can use a USB drive to do so but make sure that it has a great read-write speed. Follow the steps below to recreate Windows 10 installation USB”
- Click this link and then click the Download Tool Now button.
- Next, click the “Use the tool to create installation media (USB flash drive, DVD, or ISO file)…” option and follow the next given instructions on the screen.
- Now select the ISO file option in step 5.
- After that, you should now have an ISO file.
- Next, go to the location where you’ve downloaded the ISO file.
- Then right-click on the Windows 10 ISO file and select the Open with option and then select File Explorer.
- Now click on “setup.exe” and follow the next instructions that appear on the screen. When asked, you have to select either Nothing (clean install) or Keep personal files only option. Take note that you must not select the “Keep personal files, apps, and Windows settings since it doesn’t really work.
Option 5 – Try getting a new Windows image file
If none of the four given options above worked, you might want to get a newer installation image using the Windows Media Creation tool. After that, create the bootable USB drive and once completed and then try to run the Windows 10 setup again.



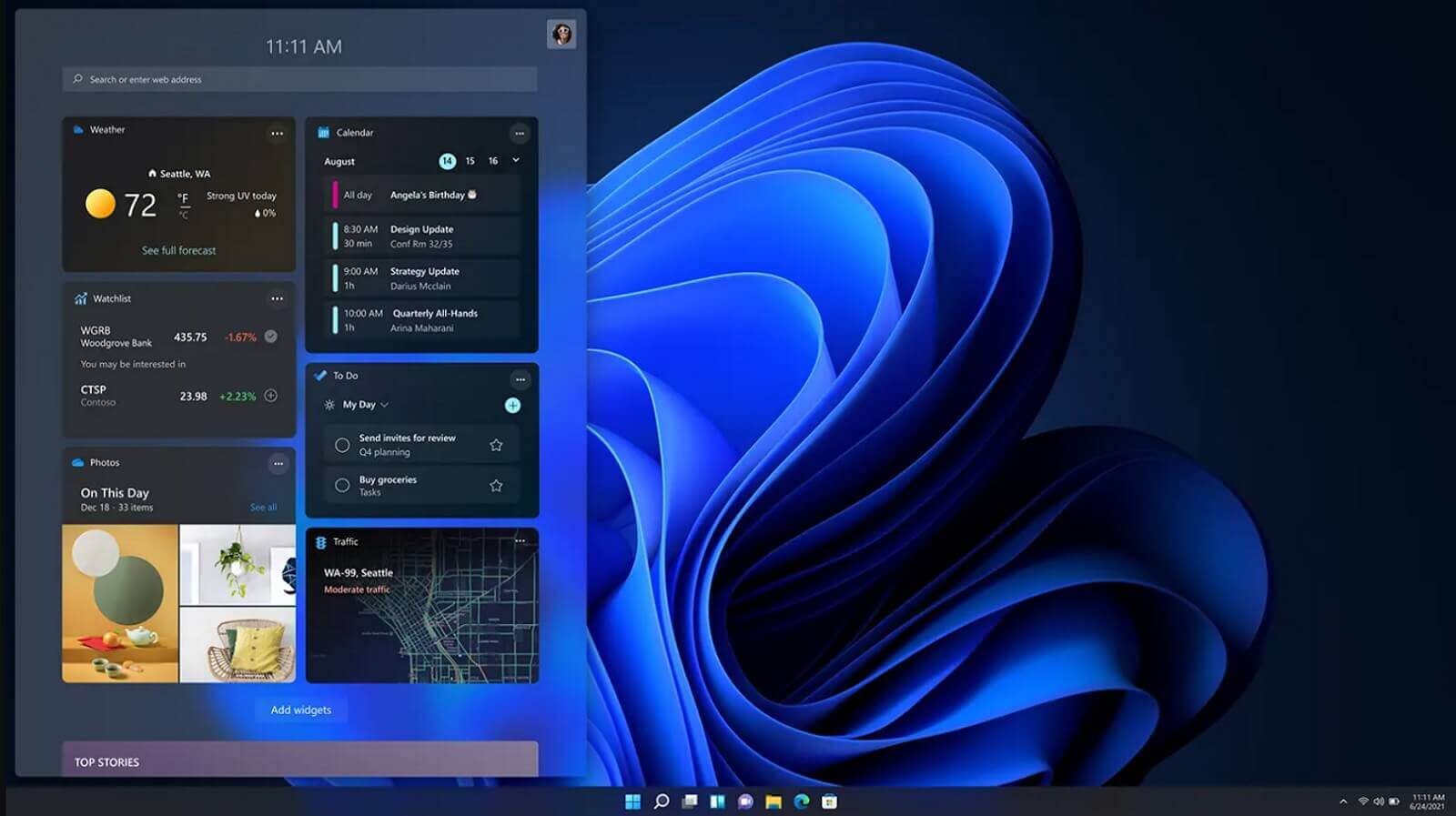 It is officially confirmed, Windows 11 release date is October 5th. Windows 11 will be released as a free upgrade to all registered Windows 10 users that have supported hardware for it.
The rest of the users will be able to install it via ISO file as a clean installation if their computer supports Windows 10 hardware requirements. The official price for the license for Windows 11 has not yet been set but I assume after release it will be set.
Priority for W11 will have users who are upgrading from W10 as stated by Microsoft.
Also, it was officially confirmed that Android apps will not be running natively in this first release of Windows 11, that feature will come in a future update, official statement below:
It is officially confirmed, Windows 11 release date is October 5th. Windows 11 will be released as a free upgrade to all registered Windows 10 users that have supported hardware for it.
The rest of the users will be able to install it via ISO file as a clean installation if their computer supports Windows 10 hardware requirements. The official price for the license for Windows 11 has not yet been set but I assume after release it will be set.
Priority for W11 will have users who are upgrading from W10 as stated by Microsoft.
Also, it was officially confirmed that Android apps will not be running natively in this first release of Windows 11, that feature will come in a future update, official statement below:

