Error Code 0xC004C4AE - What is it?
Activation errors in Windows 10 can interfere with your ability to fully use the system. When Error Code 0xC004C4AE appears on your computer, you may see a message that shows that the validation process has been stalled due to binaries that appear to have been tampered with.
While the text of this message may sound intimidating to people who are not familiar with the inner workings of the Windows 10 system, the basic meaning of the error message is that something has been introduced to the system that is not natively supported in Windows 10. During the Activation process, Windows checks to ensure that all of the Windows elements that are currently on the computer are valid and authentic to the Windows system. Usually, this particular error code refers to a language package that has been downloaded into the system using an outside application, which the Windows 10 operating system does not support.
Common symptoms include:
- An error message when the activation is attempted
- Inability to complete the Windows 10 Activation process
- Inability to fully use apps in Windows 10 until the issue is resolved
This particular error can easily be resolved with a few simple steps. However, if you are not confident in your ability to use the methods below or they do not fully remove the issue on your computer, you may want to seek the assistance of a qualified repair technician who is well versed in the Windows 10 Activation process.
Solution
 Error Causes
Error Causes
The most basic cause of Error Code 0xC004C4AE is that an unsupported language package has been enabled in the computer. This most often occurs when third-party applications have been used to introduce additional display languages to your system. While third-party applications that provide language packs are acceptable in some versions of the Windows operating system, the Windows 10 Activation process will not be able to complete if the system detects that one of these unofficial language packs exists on your machine.
Further Information and Manual Repair
There are several methods that may be helpful in resolving the basic issue in the display languages that causes Error Code 0xC004C4AE to appear:
Method 1: Restore Your System to an Earlier Point to Revert Changes
Use a backup copy to restore your computer to an earlier date, in effect undoing the changes that caused the error. When your system has been restored, you will be able to go through any language packs that are not native to the Windows operating system and remove them before re-attempting the installation and activation of the Windows 10 system.
This method is most useful if you keep a regular backup of your system and files. If you do not regularly back up the information on your computer, attempt one of the other methods instead. If you are unsure of how to use a backup to revert your changes or are not comfortable completing this step on your own, contact a certified Windows technician to assist you in the process.
Method 2: Revert to an Earlier System to Remove the Language Pack
If you are unable to restore your system using a backup, the other option to resolve Error Code 0xC004C4AE is to halt your installation of Windows 10 and go back to Windows 7 or Windows 8.1, from which you will be able to remove the language pack in question. Once the offending language pack has been completely removed from your computer, the Windows 10 Activation process should be able to proceed normally.
Several versions of windows don’t support language packages, so the best way to prevent this error from occurring is to avoid using any kind of third-party tool to install additional languages onto your Windows system. Activities Language You may be able to use third-party tools to instead complete alternative language actions without installing these languages as language packs.
If the above solutions do not help you to resolve Error Code 0xC004C4AE on your machine, get in touch with a qualified Windows repair technician, who may be able to perform the operations needed to remove the problematic language pack from your computer and allow the Windows 10 Activation process to continue to completion.

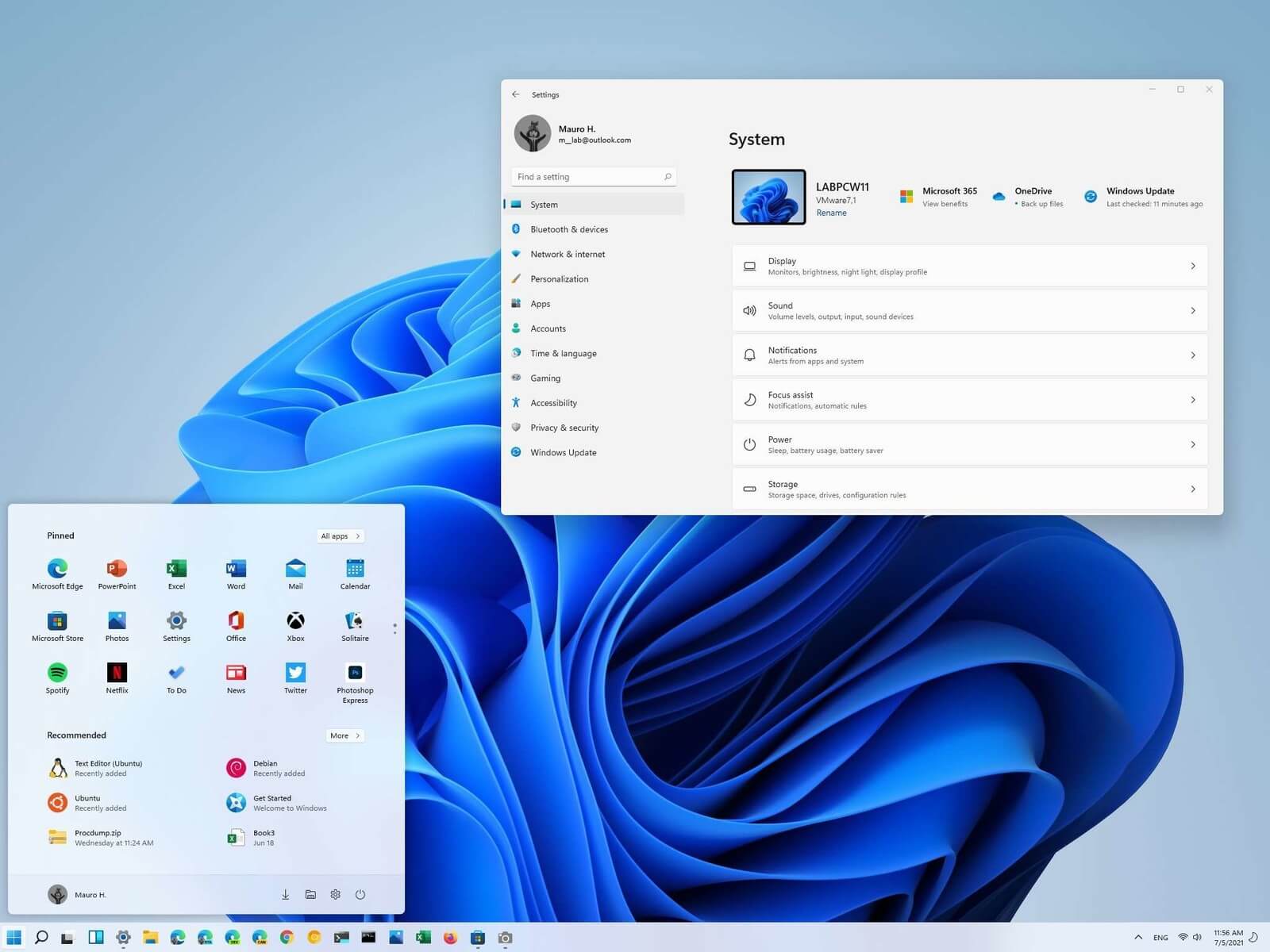 Most scrollbars are hidden by default if they are not used in Windows 11. If you are not ok with this feature and want scrollbars to be always visible and available do not worry, turning them ON is very easy.
Most scrollbars are hidden by default if they are not used in Windows 11. If you are not ok with this feature and want scrollbars to be always visible and available do not worry, turning them ON is very easy. The table itself looks very basic and it comes with a very large OLED screen between two different sizes depending on your table choice. You can choose between 65” or 77” screen sizes and OLED is mounted on the table itself so you cannot move it or adjust the angle of it that I somewhat find annoying but that comes from th4e fact I am used to adjusting my screens, but for this large screen maybe you do not need to adjust its rotation in order to get best viewing angle.
Modules themselves will offer some on-the-fly information and quick settings for the PC itself while being modular in a sense they could be mounted in different positions on the table itself providing some customization and order to suit users needs. Modules, for now, are: THX Spatial Surround Sound Controls, system monitoring, programmable hotkey module, Thunderbolt™ Powered eGPU, RAID Controller, Network Performance Module, 15W Wireless Charger, Thunderbolt™ 4 Hub, Media Controls.
Of course table, itself will have Razer chroma RGB on its surface and Razer says it will have a total of 13 different modules available on launch for a true level of personalization.
The table itself looks very basic and it comes with a very large OLED screen between two different sizes depending on your table choice. You can choose between 65” or 77” screen sizes and OLED is mounted on the table itself so you cannot move it or adjust the angle of it that I somewhat find annoying but that comes from th4e fact I am used to adjusting my screens, but for this large screen maybe you do not need to adjust its rotation in order to get best viewing angle.
Modules themselves will offer some on-the-fly information and quick settings for the PC itself while being modular in a sense they could be mounted in different positions on the table itself providing some customization and order to suit users needs. Modules, for now, are: THX Spatial Surround Sound Controls, system monitoring, programmable hotkey module, Thunderbolt™ Powered eGPU, RAID Controller, Network Performance Module, 15W Wireless Charger, Thunderbolt™ 4 Hub, Media Controls.
Of course table, itself will have Razer chroma RGB on its surface and Razer says it will have a total of 13 different modules available on launch for a true level of personalization.