Polimva is a Browser Extension for Google Chrome. This extension offers users the ability to search for any recipe on the web.
From the Author:
Polimva will help you discover new content!
You will be exposed to cool and fun content every day!
You can search and find new articles, videos, and reviews on daily basis.
-Amazing search experience.
-Access to new interesting articles and videos every hour.
-Polimva Changes the default search.
-Updated content every day.
-Follow any channel and topic that you like.
-Choose the interface and the design of the results you get every time.
This extension changes your default search engine to Yahoo, and while active it changes the displayed ads on your browser, allowing it to make revenue on every ad you click. While this is not malicious, the extension redirects your search to its servers first before forwarding it to yahoo and displaying search results. The information that is sent back to the servers contains your browsing data & visited web pages. As a result, Polimva is considered a potentially unwanted browser hijacker and if flagged for optional removal.
Browser hijackers (also known as hijackware) are a kind of malware that modifies internet browser settings without the computer owner’s knowledge or approval. These kinds of hijacks appear to be rising at an astonishing rate worldwide, and they could be truly nefarious and often harmful too. They are designed to disrupt browser functions for many different reasons. It redirects you to the sponsored websites and injects adverts on the browser which helps its developer generate ad revenue. Even though it might seem naive, all browser hijackers are damaging and therefore always regarded as security threats. What’s more, hijackers could make the entire infected system vulnerable – other destructive malware and viruses will grab these opportunities to get into your computer system effortlessly.
Here are some signs that suggest you’ve been hijacked:
1. your browser’s home page is reset to some unfamiliar webpage
2. bookmark and the new tab are also modified
3. the default web browser configurations have been changed and/or your default web engine is altered
4. you see multiple toolbars on your web browser
5. your internet browser displays endless pop-up windows
6. your internet browser starts running slowly or displays frequent errors
7. you’re disallowed access to certain websites, for example, the website of an antimalware software manufacturer like SafeBytes.
Browser hijackers can enter a PC in some way or other, including via downloads, file sharing, and email also. They can also come from any BHO, extension, add-on, toolbar, or plug-in with malicious purpose. Some internet browser hijackers spread in user’s PC by using a deceptive software distribution method called “bundling” (generally through freeware and shareware). Some of the popular hijackers are Polimva, Conduit Search, Babylon Toolbar, OneWebSearch, Sweet Page, and CoolWebSearch.
Some browser hijacking could be simply corrected by finding and removing the corresponding malware software from your control panel. Unluckily, many of the software applications used to hijack an internet browser are deliberately built to be difficult to remove or detect. You should think of doing manual fixes only if you’re a tech-savvy person since there are possible risks associated with tinkering around with the computer registry and HOSTS file.
You can opt for automatic browser hijacker removal methods by simply installing and running an efficient anti-malware program. If you need to get rid of persistent hijackers effectively, install the top-rated, award-winning anti-malware software Safebytes Anti-Malware.
Malware could cause many different types of damage to computer systems, networks, and data. Some malware variants alter browser settings by adding a proxy server or modify the PC’s DNS settings. In such cases, you will be unable to visit certain or all of the websites, and thus unable to download or install the required security software to eliminate the malware. So what to do when malicious software prevents you from downloading or installing Safebytes Anti-Malware? There are a few steps you can take to circumvent this issue.
Safe Mode is a special, simplified version of Microsoft Windows where just bare minimum services are loaded to counteract viruses and also other troublesome applications from loading. In case the malware is set to load immediately when the computer starts, shifting into this mode may well prevent it from doing so. In order to get into Safe Mode or Safe Mode with Networking, press F8 while the computer is starting up or run MSConfig and find the “Safe Boot” options in the “Boot” tab. Once you are in safe mode, you can attempt to install your anti-malware software application without the hindrance of the malicious software. Now, you could run the anti-virus scan to eliminate viruses and malware without any interference from another application.
Certain malware might target vulnerabilities of a specific web browser that block the downloading process. In case you suspect that your Internet Explorer has been hijacked by a trojan or otherwise compromised by cybercriminals, the ideal thing to do would be to switch to an alternate browser such as Mozilla Firefox, Google Chrome, or Apple Safari to download your chosen computer security software – Safebytes Anti-Malware.
To successfully eliminate the malware, you might want to approach the issue of running an anti-malware software program on the affected computer system from a different angle. Follow these steps to run the anti-malware on the infected computer.
1) Download the anti-malware on a virus-free PC.
2) Plug in the pen drive to a USB slot on the clean computer.
3) Run the setup program by double-clicking the executable file of the downloaded software, with a .exe file format.
4) Choose a USB flash drive as the location when the wizard asks you exactly where you want to install the program. Follow the instructions on the computer screen to finish off the installation process.
5) Now, plug the pen drive into the corrupted computer.
6) Double-click the EXE file to run the Safebytes software from the thumb drive.
7) Click on “Scan Now” to run a scan on the infected computer for viruses.
Want to install the very best anti-malware software for your desktop? There are numerous applications on the market that comes in free and paid versions for Microsoft Windows computers. Some of them are good, some are ok types, and some will destroy your computer themselves! You must be very careful not to choose the wrong product, particularly if you purchase a paid program. On the list of recommended software by industry experts is SafeBytes Anti-Malware, well-known security software for Windows computers.
SafeBytes anti-malware is really a powerful, highly effective protection application created to assist end-users of all levels of IT literacy in identifying and removing malicious threats out of their PC. With its outstanding protection system, this software will automatically detect and eliminate most of the security threats, including adware, viruses, browser hijackers, ransomware, trojans, worms, and PUPs.
There are plenty of wonderful features you will get with this particular security product. Listed below are a few of the great ones:
Robust, Anti-malware Protection: By using a critically acclaimed malware engine, SafeBytes gives multilayered protection that is made to catch and remove viruses and malware that are hidden deep inside your PC.
Live Protection: SafeBytes gives you round-the-clock protection for your personal computer limiting malware intrusions instantly. This software will constantly monitor your computer for suspicious activity and updates itself continuously to keep current with the constantly changing threat scenarios.
Safe Web Browsing: Through its unique safety rating, SafeBytes tells you whether a website is safe or not to visit it. This will assure that you’re always certain of your safety when browsing the internet.
Lightweight Tool: SafeBytes is a lightweight and easy-of-use anti-virus and anti-malware solution. As it utilizes very little computer resources, this application leaves the computer power exactly where it belongs to: with you.
24/7 Support: Expert technicians are at your disposal 24/7! They will quickly fix any technical issues you may be experiencing with your security software.
Put simply, SafeBytes has formulated a meaningful anti-malware solution that is aimed to protect your computer against various malware. Malware problems can become a thing of the past when you put this application to use. So if you’re searching for the very best malware removal application out there, and when you don’t mind shelling out a few bucks for it, opt for SafeBytes Anti-Malware.
To get rid of Polimva manually, navigate to the Add or Remove programs list in the Control Panel and choose the program you want to get rid of. For browser plug-ins, go to your browser’s Addon/Extension manager and select the plug-in you intend to disable or remove. You might even want to reset your home page and search engine providers, and also delete browsing history, temporary files, and internet cookies.
If you choose to manually delete the system files and Windows registry entries, use the following checklist to make sure you know exactly what files to remove before undertaking any actions. However, this can be a complicated task and only computer experts can accomplish it safely. Furthermore, certain malware keeps replicating which makes it tough to eliminate. You are advised to do this process in Windows Safe Mode.
Files:
%UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\Default\Extensions\epngjnkooalbmphkdlahcdhnfondeicc
Registry:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run

“This policy setting lets you prevent Windows from using diagnostic data to provide tailored experiences to the user. If you enable this policy setting, Windows will not use diagnostic data from this device (this data may include browser, app, and feature usage, depending on the “diagnostic data” setting value) to customize the content shown on the lock screen, Windows tips, Microsoft consumer features, and other related features. If these features are enabled, users will still see recommendations, tips, and offers, but they may be less relevant. If you disable or do not configure this policy setting, Microsoft will use diagnostic data to provide personalized recommendations, tips, and offers to tailor Windows for the user’s needs and make it work better for them. This setting does not control Cortana tailored experiences, since there are separate policies to configure it.”
 With its Rift model, Oculus set itself as a big player in VR. Now the company is slowly bowing out of the dedicated, tethered VR headset with its latest Quest 2 designed to primarily be a standalone headset.
In case you do not know, tethered headset means that the headset itself is connected to your PC and is using its power to drive your VR experience.
Now technical specifications of Quest 2 are pretty OK and it can drive stuff pretty decently and if you want you can purchase the dedicated cable to connect it to your PC for the full experience of games requiring more capable hardware.
Oculus Quest 2 is the cheapest headset on this list and with its stable performance, is highly recommended.
With its Rift model, Oculus set itself as a big player in VR. Now the company is slowly bowing out of the dedicated, tethered VR headset with its latest Quest 2 designed to primarily be a standalone headset.
In case you do not know, tethered headset means that the headset itself is connected to your PC and is using its power to drive your VR experience.
Now technical specifications of Quest 2 are pretty OK and it can drive stuff pretty decently and if you want you can purchase the dedicated cable to connect it to your PC for the full experience of games requiring more capable hardware.
Oculus Quest 2 is the cheapest headset on this list and with its stable performance, is highly recommended.
 Although the headset itself is nothing revolutionary or special its controllers are. They can track individual finger movements, making games (that take advantage of them) much more immersive than the standard trigger grips on other controllers.
The Index's higher refresh rate makes for smoother action, as well, which is another nice bonus. If you already have an HTC Vive or Vive Cosmos Elite, and their base stations (not the regular Cosmos), you can buy only the controllers.
Although the headset itself is nothing revolutionary or special its controllers are. They can track individual finger movements, making games (that take advantage of them) much more immersive than the standard trigger grips on other controllers.
The Index's higher refresh rate makes for smoother action, as well, which is another nice bonus. If you already have an HTC Vive or Vive Cosmos Elite, and their base stations (not the regular Cosmos), you can buy only the controllers.
 The PlayStation VR is compelling thanks to Sony backing its development, plus the PlayStation 4's affordability and availability compared with gaming PCs. All you need is the headset, a PlayStation 4, and a PlayStation Camera (now included with most PlayStation VR bundles).
Not really the best of the bunch but still one of the top ones for console gaming. Sony is working on a new PlayStation VR system for the PlayStation 5, with redesigned controllers. The new headset hasn't been revealed yet, but the company has released a preview of the new controllers.
The PlayStation VR is compelling thanks to Sony backing its development, plus the PlayStation 4's affordability and availability compared with gaming PCs. All you need is the headset, a PlayStation 4, and a PlayStation Camera (now included with most PlayStation VR bundles).
Not really the best of the bunch but still one of the top ones for console gaming. Sony is working on a new PlayStation VR system for the PlayStation 5, with redesigned controllers. The new headset hasn't been revealed yet, but the company has released a preview of the new controllers.
 HP headset is one which you get if you want the best image quality in VR headset, sadly controllers did not follow the same quality of headset itself. But this is still a pretty decent headset overall and worth the purchase.
HP headset is one which you get if you want the best image quality in VR headset, sadly controllers did not follow the same quality of headset itself. But this is still a pretty decent headset overall and worth the purchase.
 HTC's Vive Cosmos is the upgraded version of the Vive. It features a higher resolution and replaces the external base stations with outward-facing cameras for motion tracking. It's a comprehensive package for whole-room VR.
HTC recently released the Vive Pro 2, a high-end VR headset targeting both enterprise users and consumers. This new headset features a 2,448-by-2,448 resolution display for each eye, making it the highest-resolution headset currently available. It's also more expensive than the Cosmos Elite.
Sadly one thing that is bringing this headset down is the price.
HTC's Vive Cosmos is the upgraded version of the Vive. It features a higher resolution and replaces the external base stations with outward-facing cameras for motion tracking. It's a comprehensive package for whole-room VR.
HTC recently released the Vive Pro 2, a high-end VR headset targeting both enterprise users and consumers. This new headset features a 2,448-by-2,448 resolution display for each eye, making it the highest-resolution headset currently available. It's also more expensive than the Cosmos Elite.
Sadly one thing that is bringing this headset down is the price. Corsair is well known for RAM memory modules for PC but then it has expanded to PC peripherals and even selling some pre-build computers as well in past few years. New Corsair expansion now includes a laptop line, starting with their new gaming laptop Voyager.
Voyager laptop is packed with a mechanical keyboard and MacBook-like touch bar for your typing and pointing needs. It is built with a 16-inch QHD+ screen packing 240Hz that is run by Radeon 6800M GPU. Also inside lurks AMD 16 thread Ryzen 9 6900HS CPU, Wi-Fi 6E support, Dolby Atmos audio, and full HD 1080p WEB camera.
The keyboard has low-profile mechanical Cherry MX switches with per-key RGB lightning and above is what Corsair calls a macro bar, with 10 shortcut buttons and a small LCD in the center.
Corsair is also including a few features that tie in with its other products. Many of the company’s keyboards, mice, and other accessories use the ‘Slipstream’ USB wireless adapter, which is built into the Voyager laptop. The macro bar is also configured using the same software used for the Elgato Stream Deck, a popular product sold by Corsair.
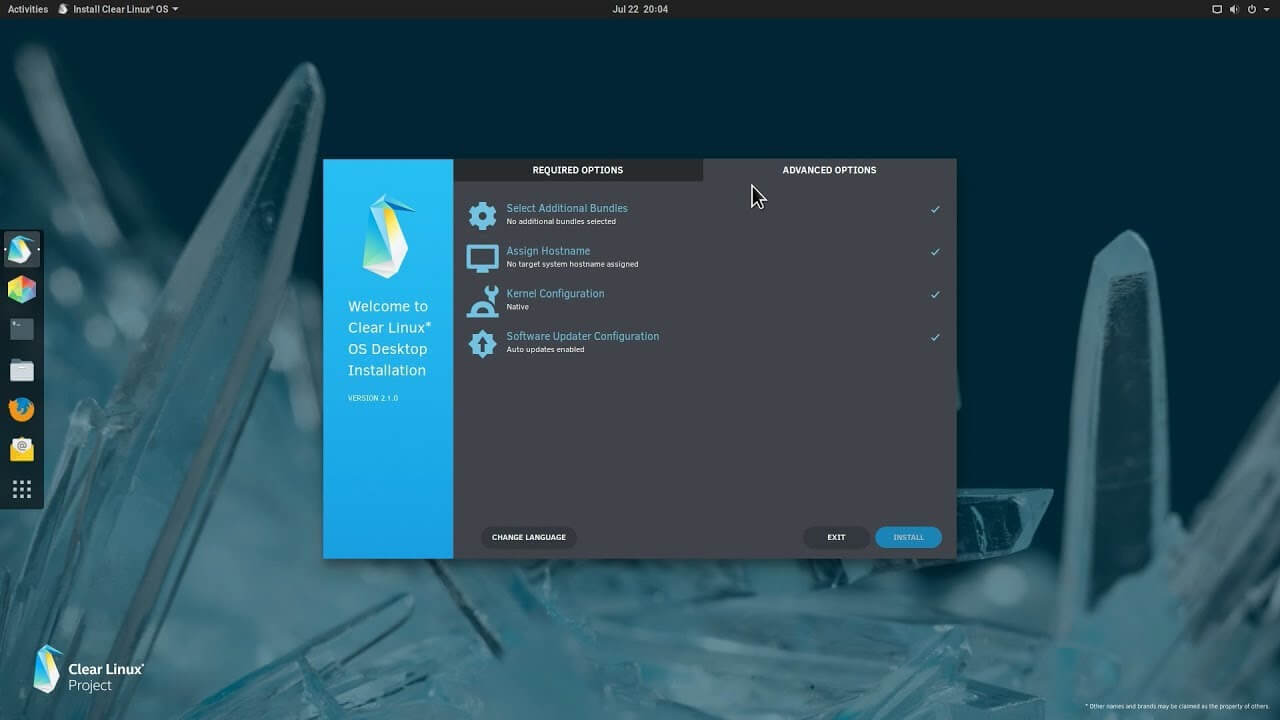 The Clear Linux Project creates an operating system and software stack that offers highly optimized performance, security, versatility, and manageability.
Clearly optimized for Intel CPUs and based on GNOME it will offer you incredible speeds if you are on Intel CPU.
The big news, though, is that Clear Linux sports the shiny new Gnome 40. This is a fresher Gnome than you'll find even on Ubuntu's more experimental 21.04 release. The only big names that let you test drive Gnome 40 are Fedora and Arch Linux.
The Clear Linux Project creates an operating system and software stack that offers highly optimized performance, security, versatility, and manageability.
Clearly optimized for Intel CPUs and based on GNOME it will offer you incredible speeds if you are on Intel CPU.
The big news, though, is that Clear Linux sports the shiny new Gnome 40. This is a fresher Gnome than you'll find even on Ubuntu's more experimental 21.04 release. The only big names that let you test drive Gnome 40 are Fedora and Arch Linux.
Code 34 is one of the several Device Manager error codes. This error code indicates that a hardware device on your PC is not properly configured.
This usually occurs when the device installed on your system is a non-plug and play. Non-plug and play devices don’t configure automatically and require manual configuration from the users end.
Error code 34 is usually displayed in the following format:
“Windows cannot determine the settings for this device. Code 34”
 Error Causes
Error CausesError code 34 may be triggered due to several reasons like:
Device Manager error codes like code 34 are easy to fix. These error codes don’t indicate any serious PC problem, nor are they fatal like blue screen of death error codes.
Nonetheless fixing it immediately is advisable to ensure the proper functioning of the plugged-in hardware device. If you don’t resolve it, you may not be able to use the device.
When PC users experience error codes like code 34, they instantly think of hiring a professional for repair especially if they lack technical understanding.
If you are not a technical whiz and you are also thinking of hiring a professional for the repair job, then don’t! Here’s why, to begin with, Device Manager error codes can be resolved easily, better yet you can fix it by yourself without spending a dime even if you are not technically sound.
To help you, below is a list of easy and effective repair solutions for error code 34. Try them to resolve the issue.
This is one of the best ways to resolve error code 34 on your system. The procedure will take 5 to 7 minutes. Simply follow the steps illustrated below to configure the problematic device on your PC.
You may not be able to configure resource settings for some devices in such an event it is advisable to consult your hardware manufacturer. Your hardware manufacturer can provide you with specific resource settings. Follow the manufacturer’s instructions to repair error code 34.
If the error continues to persist even after device configuration, then the problem may be linked to driver corruption. In that case, try method 3.
Method 3 - Download DriverFIX to Update Drivers Automatically
Whether code 34 is caused by outdated or corrupted drivers, simply download DriverFIX to resolve. DriverFIX is an advanced and user-friendly software program deployed with an intelligent programming system.
The software scans your PC to detect all problematic drivers. It finds and matches the latest and compatible versions and then updates the drivers accordingly that too automatically and on a regular basis.
Click here to download DriverFIX to repair Device Manager error code 34 on your PC automatically.