Error Code 0xC1900101, 0x30018? - What is it?
Users, when upgrading to Windows 10 from Windows 7 or Windows 8/8.1, or when upgrading to a new version, build, service pack, or major update of Windows 10, can encounter error code 0xC1900101, 0x30018. Windows 10 installation fails and stops or hangs. During the installation process, it will reach a certain maximum limit (normally at 6% or 32%) then reverts back to the previous version of the operating system and displays the following message:
We couldn’t install Windows 10. We’ve set your PC back to the way it was right before you started installing Windows 10.
0xC1900101 – 0x30018 The installation failed in the FIRST_BOOT phase with the error during the SYSPREP operation.
Solution
 Error Causes
Error Causes
In attempting to fix Error Code 0xC1900101-0x30018, it is vital to know what causes this issue. The most probable causes of this error are:
- Incompatible hardware or driver
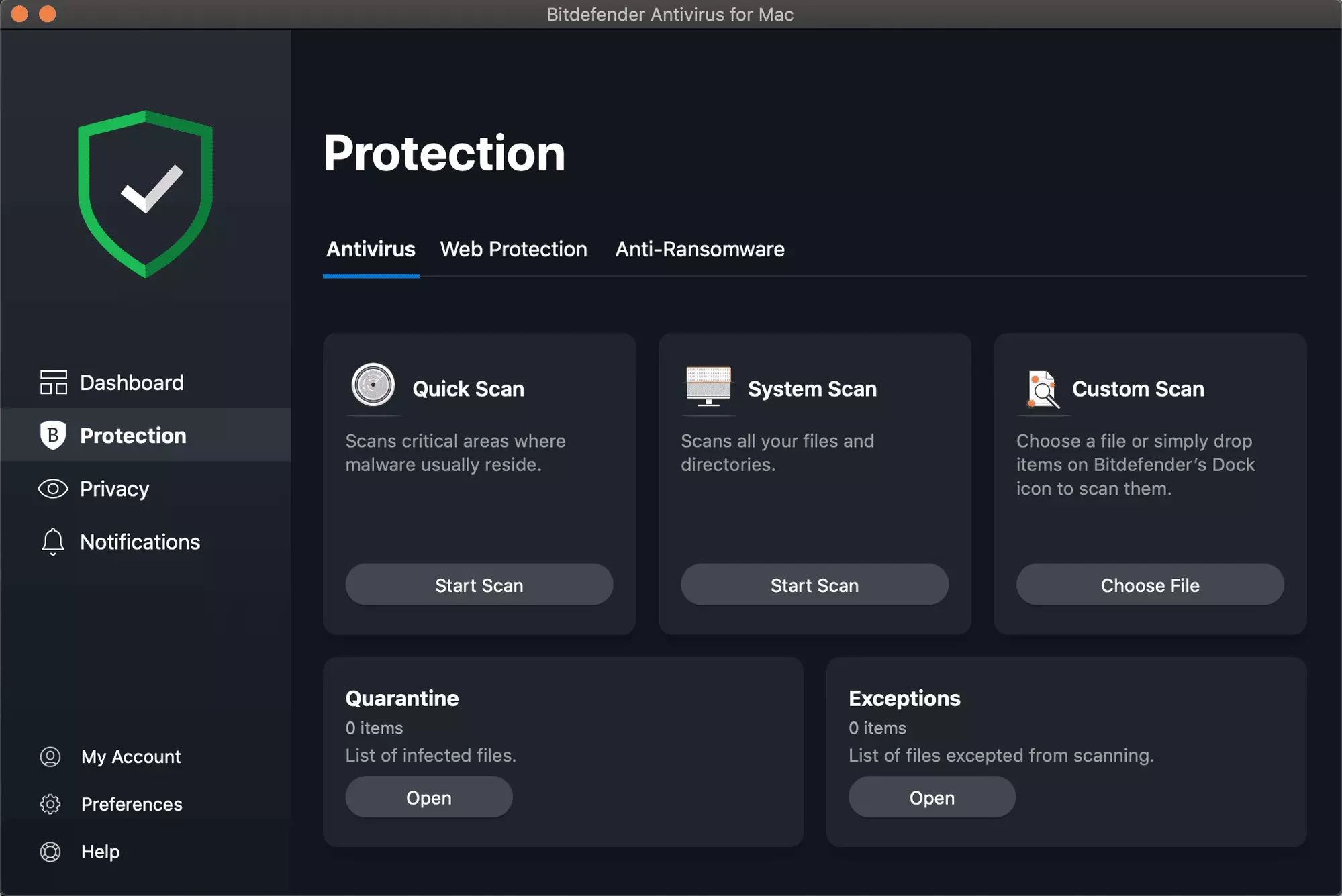
- Incompatible security programs or antivirus or incompatible utility software
- A device driver possibly stopped responding to setup.exe while on the installation process.
Further Information and Manual Repair
In fixing issues related to error codes, it is best to employ manual repair methods. Using these methods helps users pinpoint the root causes of the issue and apply solutions permanently to fix the issues. While most manual repair methods can be done by every Windows user, even those without technical abilities, there are certain cases where help from a Windows professional is needed. If you’re not up to facing risks in implementing manual methods yourself, consider getting help from a professional Windows technician or you can use a powerful automated tool. In fixing Error Code 0xC1900101-0x30018, you can repeat the same steps used for 0xc000021a (Method One) or you can try doing the following:- Disable or uninstall your Antivirus program before proceeding to upgrade the system
- Ensure that the machine name is simple (having at least 8 characters) with no special characters like hyphens or dashes.
- Restart the device a few times then try again.
- Disable General USB Devices such as the Smart Card Reader.
- If you use an SCSI hard disk, ensure that you have available drivers you can use for your storage such as a thumb drive and make sure that it is connected. During the Windows 10 setup, select the Custom Advanced Option and use the Load Driver command to be able to load the suitable driver for the SCSI drive. If this fails, try switching to an IDE-based hard disk.
- You can now perform a clean boot. Restart your device then try again.
- If you are using the .ISO file for upgrading the system, you need to disconnect from the Internet first before proceeding to the setup. If you are connected to Wi-Fi or by Ethernet (LAN), make sure to disable both connections then you can proceed to set up again.
- If you’re performing the update through Windows Update, once the download reaches 100%, disconnect from the Internet, and then proceed with the installation.
NOTE: If this fails, if possible, you can try using the .ISO file in upgrading.
- Switch to a local account if the device is connected to a domain.
- Disconnect all external devices attached to the computer such as gaming controllers, printers, or USB keys.
If you’re using Windows Update in installing Windows 10, you can implement the following:
- Open the Command Prompt window by pressing Windows Key + X. Select Command Prompt (Admin) from the menu.
- Stop the BITS, Cryptographic, MSI Installer, and the Windows Update Services. In order to do this, Type or Copy and Paste the following commands one at a time:
NOTE: Don’t forget to hit Enter after every command.
net stop wuauserv
net stop cryptSvc
net stop bits
net stop msiserver
- Rename the Catroot2 and SoftwareDistribution In order to do this, Type or Copy and Paste the following commands one at a time:
NOTE: Don’t forget to hit Enter after every command.
ren
C:WindowsSoftwareDistribution SoftwareDistribution.old
ren
C:WindowsSystem32catroot2 Catroot2.old
- Restart the BITS, Cryptographic, MSI Installer, and the Windows Update Services. In order to do this, Type or Copy and Paste the following commands one at a time:
NOTE: Don’t forget to hit Enter after every command.
net start wuauserv
net start cryptSvc
net start bits
net start msiserver
- Type Exit in the Command Prompt then close the Command Prompt window then restart the computer.

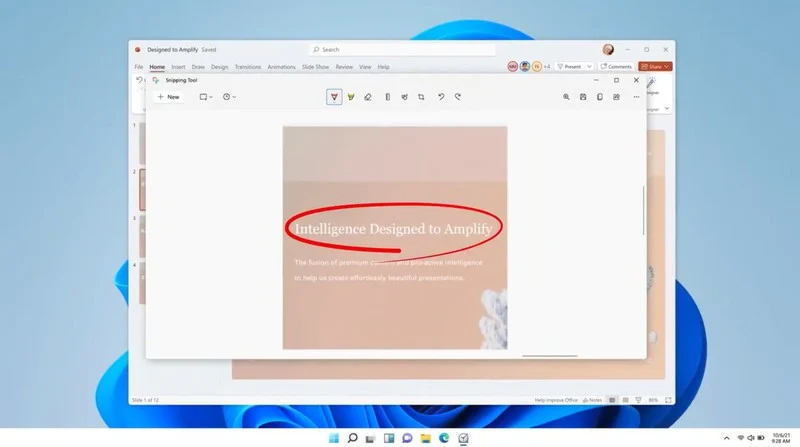 The latest update from Panos Panay on Twitter is including New and redesigned Snipping tool inside Windows 11. From the shared video, we can see that it includes modern Windows 11 UI redesign and it looks and feels like a part of Windows 11.
More things that can be seen from the shared video is that it looks like the new snipping tool is a merged version of the old with snip & sketch.
It is good to see that it is still possible to capture screen with easier way natively inside Windows 11 but some more functionality would be more welcome I guess.
Users were asking for added functions for a long time like adding simple text for example but from shared video, no new features were presented so for some users 3rd party solutions will still be the way to go.
The new and redesigned Snipping tool will roll out with the next update and we will see then about all new features inside it firsthand. Until then, take care.
The latest update from Panos Panay on Twitter is including New and redesigned Snipping tool inside Windows 11. From the shared video, we can see that it includes modern Windows 11 UI redesign and it looks and feels like a part of Windows 11.
More things that can be seen from the shared video is that it looks like the new snipping tool is a merged version of the old with snip & sketch.
It is good to see that it is still possible to capture screen with easier way natively inside Windows 11 but some more functionality would be more welcome I guess.
Users were asking for added functions for a long time like adding simple text for example but from shared video, no new features were presented so for some users 3rd party solutions will still be the way to go.
The new and redesigned Snipping tool will roll out with the next update and we will see then about all new features inside it firsthand. Until then, take care.