Since Windows 10 introduced the concept of notifications, almost any application installed on your computer sends you one. However, there are times when too many notifications can be quite annoying. Although some of them are important, most of them are not and are only getting in the way of your tasks. So if you don’t like to be flooded with tons of notifications on your Windows 10 computer, say no more as this post will help you out in disabling notifications for any apps installed.
And now with the new feature in Windows 10 called Focus Assist, you will be able to manage the level of notifications that you receive. This new feature also allows you to disable all notifications except for the ones from important or priority apps. You will just have to maintain a list of priority applications or you could also disable all the notifications except for the important ones like alarms. In addition, you could also set up some automatic rules such as the Focus Assist timings which means that you can make Focus Assist enabled for a certain period of time during the day or when you are duplicating your display or playing a game and whatnot. So if there is an application that keeps on spamming you with notifications, you can just disable the notifications for that application.
Note: You can disable notifications or just the notification banners, your choice. Aside from that, you can also control the notification sound as well as its behavior when the computer screen is locked. What’s more, is that you can also adjust the number of notifications displayed in the Action Center or select the priority applications. As stated earlier, Windows 10 gives you control that allows you to customize every nook and cranny of the notification on your Windows 10 computer. Apart from applications, there are also other notifications-related settings that you can control including disabling notifications about tips, tricks, and suggestions as well as summary notifications from Windows Defender that you get every time you use or scan your computer.

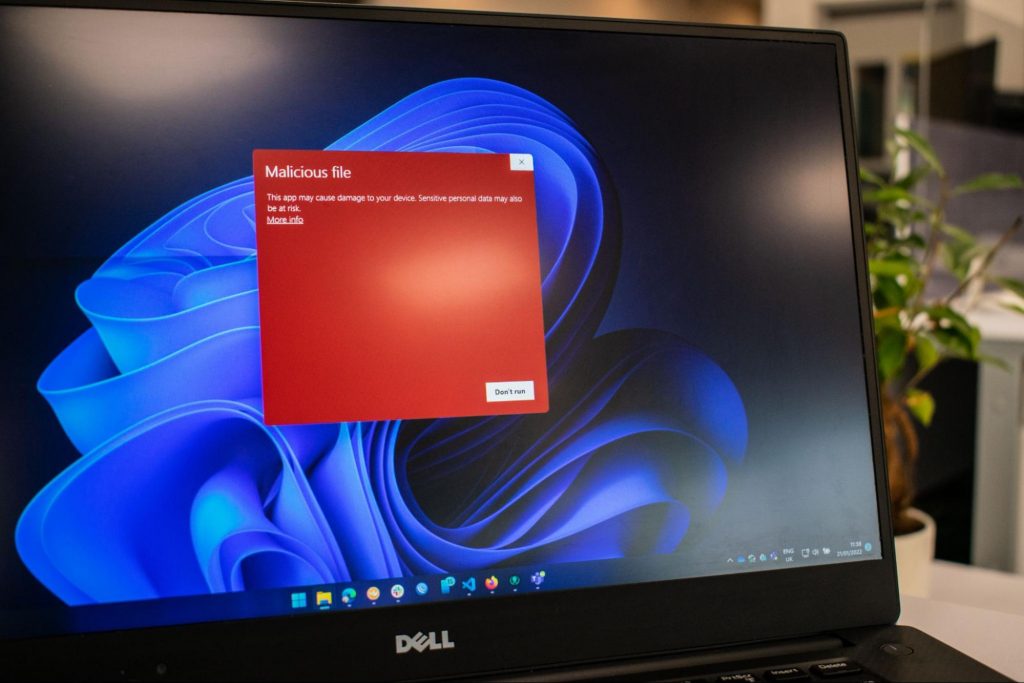
Afraid of the growing threats online? As you should be. But we’re here to show you what kinds of malware are out there and what you can do to keep them at bay.
Malware comes from the term malicious software. It’s software designed to attack and exploit devices and networks to the advantage of the hacker who made it.
Malware can be transmitted in different ways. Most commonly this happens via infected USB drives, downloadable files or malicious websites. Depending on the type and ultimate goal, the consequences of a malware attack can range from negligible to catastrophic.
A virus is typically spread via infected files, websites or links. It’s one of the oldest malware types and one of the most difficult to get rid of. That’s because, once activated, it replicates itself - hence the name.
It can perform different kinds of attacks, depending on what the creator wants to achieve. The main characteristic of a virus is that it really doesn’t show itself until you activate the host. So that’s a scary thought for sure.
Sometimes an ad blocker isn’t enough to fight off unwanted ads. And some of them can, unfortunately, be malicious. They may redirect you to infected sites or prompt downloads of risky files. Even just opening a malicious site can lead to data theft.
So, definitely be careful when clicking around. Even if an ad seems completely legitimate, you can never be too sure.
Through ransomware, cybercriminals gain access to a user’s data and use it to extort them for money. Basically, the user is threatened with data deletion or even exposure if a ransom isn’t paid by a specific deadline.
This is a particularly nerve-wracking type of malware. If it targets an individual, it preys upon their sense of anxiety, fear, guilt and even shame. If it targets a business (which is a lot more common), it preys upon not only that business’s profit but also every single one of their customers and their data.
This type of malware disguises itself very well as a legitimate-looking program. Once you download it, hackers can get full access and control of your device, data and network. They can even be hidden in games, apps and attachments. They cannot self-replicate, though, so we guess that’s… good news?
Worms can replicate, just like viruses, but you don’t need to actually activate the infected program for them to get going. They can be used for various purposes, ranging from data deletion to file encryption to support a ransomware attack.

Spyware refers to malicious software that stays hidden on your computer and monitors your activity. The best-known type is keyloggers. This can be used to steal sensitive data like passwords and banking information.
Rootkits are among the most dangerous types of malware. They allow administrative access and full control of a device, which lets hackers continue hijacking all your data and monitoring your activity without your knowledge.
Botnets are networks made up of bots - computers that cybercriminals have infected with malicious software. Bots and botnets give hackers remote access to users’ devices and allow them to spy on your camera, take screenshots, memorize passwords and launch Distributed Denial of Service attacks. This one truly makes your hair stand on end.
You know the old adage - better safe than sorry. And trust us, malware attacks are such a pain in the you-know-what that you really don’t want to be sorry.
Luckily, there are simple solutions that can shield you from most digital threats these days. What you want to be looking at is a solid antivirus program. Well, technically, you need an antimalware program, but since the latter evolved from the former, we still mostly refer to them as antivirus software.
The majority of antimalware programs these days don’t just shield you from potential risks online, but include additional features as well. For example, some Bitdefender antivirus packages also include parental control and a VPN. And Bitdefender is not just for PCs either - it offers protection for your beloved iPhone or Android as well. You can throw in a password manager in there too, for an additional layer of security.

If you aren’t too concerned about all these various threats or feel like you don’t need extra security, you can at least take a step to protect your information from being exposed to lurking cybercriminals as you’re browsing. This can be done through a good VPN like Surfshark, which hides your identity in the digital space and prevents your data from being tracked.
Choosing the right protective software is especially important if you have children with access to the Internet, since they’re unfortunately even more vulnerable to malicious attacks. If you aren’t sure what the right kind of antimalware program is right for you, you can reach out to us and we’ll be happy to help keep your entire household or office digitally secure.
The truth is that there’s no way to be 100% protected in the online world. Hackers are constantly coming up with new ways to infiltrate our devices. But malware-battling software evolves along with them and there’s still plenty you can do to keep risks away. Stay safe!
A runtime error is commonly an error that's created after the PC is operating software and encounters a problem of some form. For instance, a runtime error like run-time error code 7 reveals an "out of memory" dilemma.
Run-time errors are normally brought on by clashes with TSR (Terminate and Stay Resident) applications or additional operating applications, software problems, storage problems, or pc viruses.
First, enter the run-time error signal into a search engine to see what info you will get about the precise runtime issue you are receiving. Next, end - job all running applications and TSRs to make sure these aren't the origin of the issue. You can certainly do so by obtaining the job manager by striking Control Alt Delete.
In case your issue is regularly occurring with a unique program, go to that system programmer's site and obtain any upgrades and patches. If unavailable, try uninstalling the application involved and reinstalling it.
In the event the issue is occurring with the os, you may consider reinstalling it although it is a huge commitment. A much better idea would be to try a fix for both Windows XP or Windows 2,000. It is possible to fix and scan files by typing : sfc / scannow, heading to the Begin switch, Run, and then pushing enter. Make certain to put an area between sfc and the reduce.
You might have an equipment or storage dilemma if these measures have not resolved your run-time errors. If that is the situation, contact the support of the application under consideration for potential support accompanied by the pc or motherboard manufacturer.
Many run-time problems can be solved by upgrading the application that's creating the problem. This is only because the programmer's frequently releasing patches and improvements for their applications as insects are found and repaired.
Storage problems may frequently be fixed by rebooting the pc. Consider a reboot a short-term repair. Rebooting clears the memory but in case your COMPUTER does not have adequate memory for your applications you're operating, or sufficient hard-drive space you'll immediately run out of memory again. Something less than this sum may cause memory issues since the computer's swap file isn't in a position to expand in dimension as required.
To assess the quantity of free area, available My Computer and right-click on the HDD, generally the D: drive. Select Attributes in the menu and see the disc's ability. Perform the disk clean-up function by following prompts and pressing the Disk Clean-up button, if the room is reduced.
You may be getting run-time errors, in case your storage chip is really failing. Eliminating and changing the awful memory chip will solve the difficulty. If you're encountering other runtime-related errors, like an install runtime issue, try cleaning away the portions of the registry with some software solution.
New Apple's upscaling technology called MetalFX will place iOS and macOS devices back into the gaming world. Apple had great games back in the old days and some all-time hits like the prince of Persia have been made first for apple but along the way, it just lost it.
Same as NVIDIA's DLSS and Intel's XeSS systems, Apple MetalFX also uses AI algorithms to upscale the resolution of output game frames. So, for example, the GPU inside your MAC might render the game at 1080p, but through MetalFX and AI upscaling it will look like a 4K image but have a good frame rate since it is rendered in base resolution.

The ability to make AI strike a good balance between performance and image quality is a key to technology in today's modern gaming and having this technology will help developers a ton to be able to achieve great results on Apple hardware.
So far three official games that will use this technology and be released natively for Appl hardware are Resident Evil 8 Village, GRID legends, and No Man's Sky. All three games have been confirmed and Resident Evil 8 Village is already sent for review people are impressed since the game can run smoothly on all Apple devices, even ones with an M1 CPU.
When you say Apple gaming is probably the last thing that comes to your mind but truth be told Apple makes more money from games than Microsoft, Nintendo and Sony combined. Also, Apple itself was a big player once regarding computer games as well, Myst and Prince of Persia are games that were made and have been released for Apple first. Bungie was also founded by Apple developers and Halo was originally announced as a Mac game.
Apple has been trying and pushing gaming on its platform since it kind of died down. Today all Sony, Nintendo, and Microsoft controllers work without any issues with all Apple products. Apple also has its own gaming subscription service, Apple Arcade, and its Apple TV is packed with GPU that can rival Xbox ones.
MetalFX API ties and brings it all together, it is designed to get the most performance from the hardware by minimizing overhead.
Now, computers and laptops do not hold any large numbers if we look at the user base, and that could deter developers but if we look at iPad and iPhone things are different there, much different. How same CPU power these devices and how MetalFX is available across all products it is clear that there is a market for games there. No Man's Sky is coming to iPad using these technologies and bringing full computer experience to tablets.
Error Code 48 is a device driver error code that users can encounter on any Windows 2000 operating system and later versions.
It occurs when the connected peripheral device cannot be run as the Windows operating system’s driver required to install the programs for peripheral devices has either been corrupted or is incompatible with the system.
It prompts the user with the following message on the screen:
The software for this device has been blocked from starting because it is known to have problems with Windows. Contact the hardware vendor for a new driver. (Code 48)
 Error Causes
Error CausesLike most other Windows error codes, error code 48 is triggered by the following factors.
Identifying and removing the viruses in the system registry and in the connected devices is the easiest method to fix the corrupted registry files.
Viruses such as spyware and malware infect the registry entries and eat up the files that lead to incomplete or missing data. This creates problems for installing external devices as the driver required to install them is not complete.
You can also use system restore to eliminate the problem. Here is how you can use it:
By restoring the system via the last saved system checkpoint, you can obtain undamaged Windows system registry files that can help resolve the error code.
Since Error Code 48 is due to a missing or an out-of-date device driver, uninstalling and then reinstalling the device driver can help solve the error.
You can do this by firstly logging in as Administrator and opening Device Manager. Select the device that is causing the problem and double click it; make sure that the peripheral is connected properly to the PC.
Upon opening, click on the ‘Driver’ tab and then select ‘Update Driver’. Make sure to refer to the system documentation that you received with your PC or computer to check for the motherboard details and driver specifics.
 Error Causes
Error Causes