Why combining hard drives with storage spaces? Ok, I will admit it, I am a modern digital hamster when it comes to digital goods. I like to collect stuff and more than anything else I like to have all of that at the tip of my fingers. And how digital goods grow in size themselves (movies on Blu-ray are like 50GB each) and the collection grows in size single hard drive is starting to be completely obsolete when it comes to storage.
Sometimes we will need large storage for these kinds of personal collections, sometimes we will need it for work reasons. Whatever your reason might be Windows 10 is offering us a solution via Storage spaces.
Storage spaces is an integral part of Windows and it is meant as a tool to provide you with a RAID environment without a RAID controller. Of course, combining multiple hard drives via storage paces instead of RAID will not be so fast or stable but for home use of storing a large quantity of data is perfectly enough.
With Storage Spaces you will also have an option to reduce some space for increased security of data loss if by any chance one of your HDD fails.
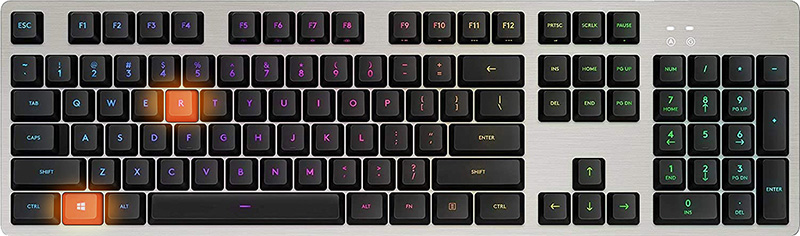
To create storage space in Windows, press ⊞ WINDOWS + R to open the run dialog.
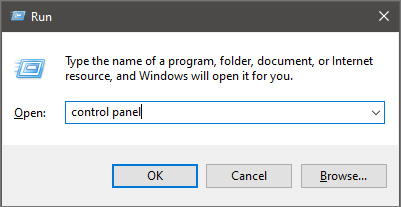
 In the run box type in Control Panel and press ENTER
In the run box type in Control Panel and press ENTER
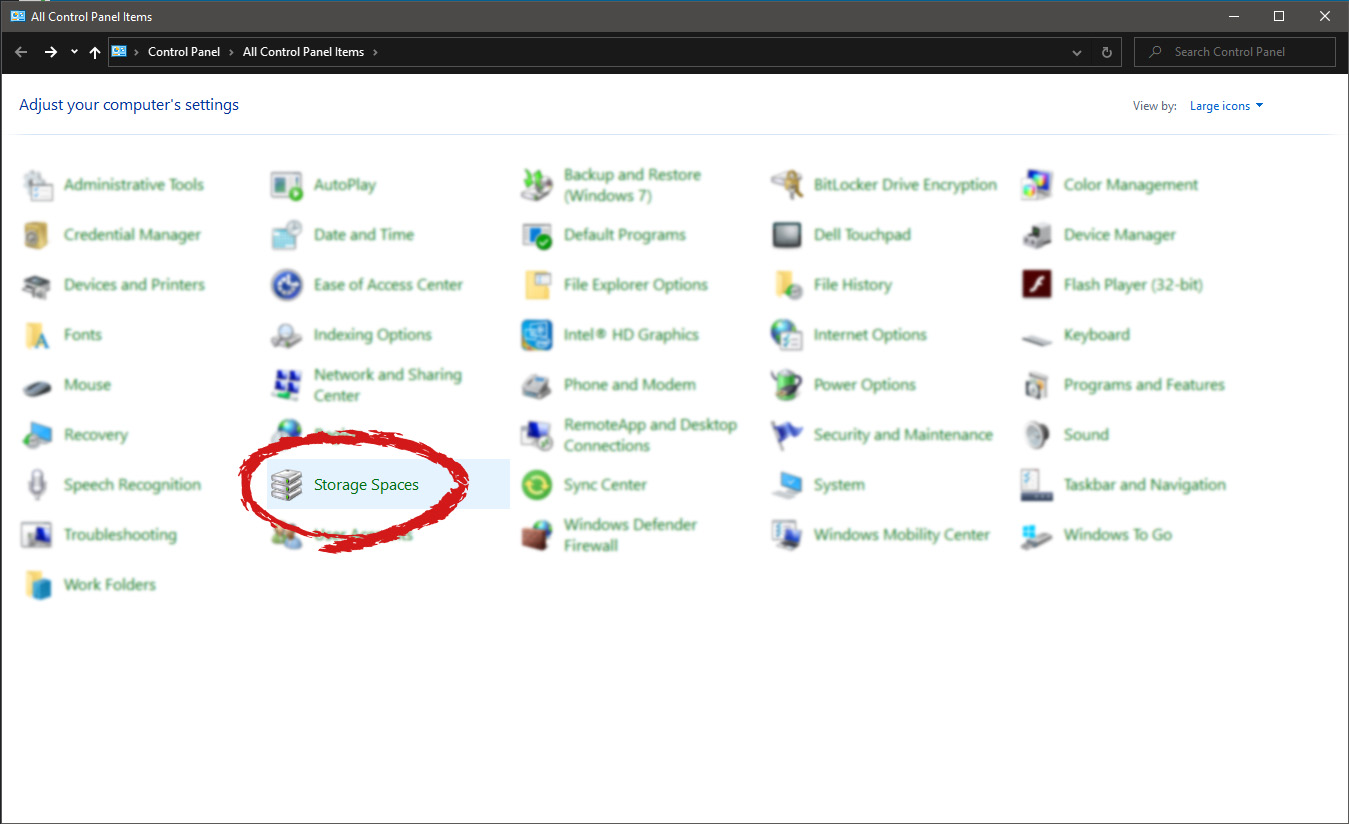
 In Control Panel find Storage Spaces and left-click on it.
In Control Panel find Storage Spaces and left-click on it.
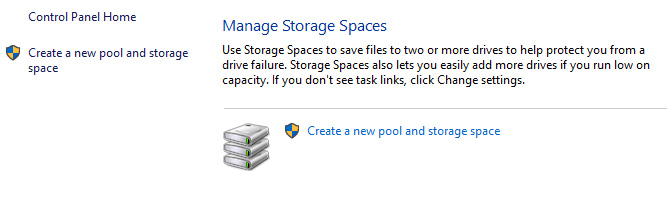
 Once storage spaces open, left-click on Create a new pool and storage space
Once storage spaces open, left-click on Create a new pool and storage space
 Once you click on create new, you will be greeted with a list of hard drives you can use for this operation.
Once you click on create new, you will be greeted with a list of hard drives you can use for this operation.
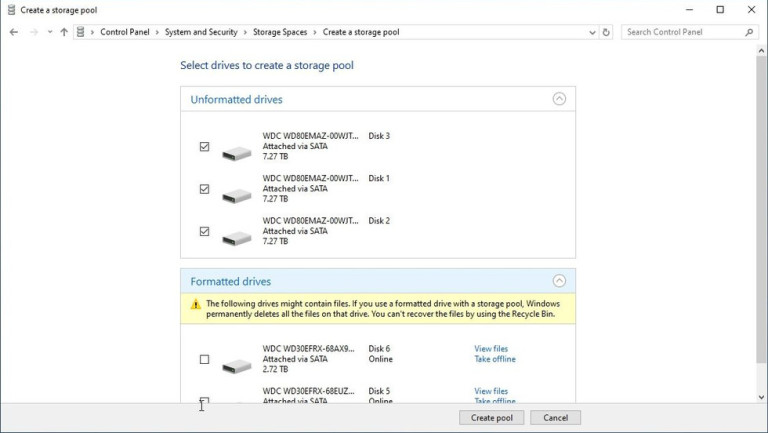 Please note that all hard drives you choose will be completely erased and formatted and then assign a single drive letter. Click on Create pool.
Please note that all hard drives you choose will be completely erased and formatted and then assign a single drive letter. Click on Create pool.
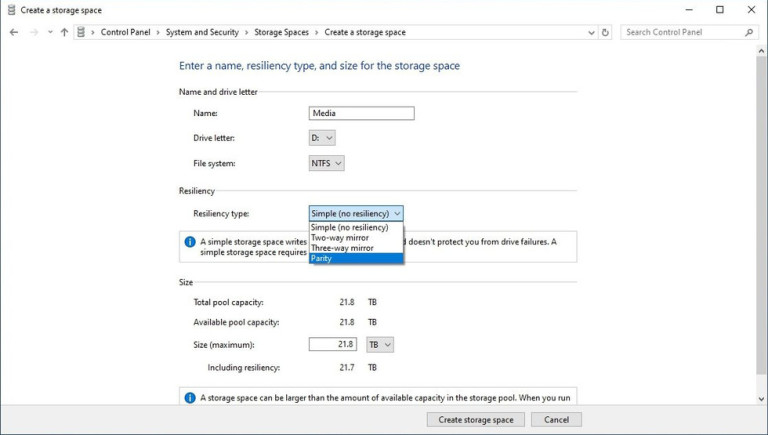 You will find yourself in new storage options where you can assign a drive letter, give storage space a name, etc.
You will find yourself in new storage options where you can assign a drive letter, give storage space a name, etc.
One thing I would like to focus on here is resiliency type, when you expand the resiliency type drop-down menu you will see 4 options inside. Simple, Two-way mirror, Three-way mirrors, and Parity.
Simple: If you choose Simple as an option, you will have maximum hard drive space but no resiliency at all, meaning that if by any chance any of your hard drives malfunction, you are losing your data from that drive completely.
Two-way mirror: This option will save your data if one of your drives fails but you need at least 2 drives and storage space will be limited since some of it will be a safe backup option for the case of a drive failure. However if one of your drives fails, you can replace it in a second and keep on working as nothing happened.
Three-way mirror: This option similar to the previous one will offer you safe data-keeping from a hard drive failure. this option will save your data even if 2 hard drives malfunction but it will require having 5 of them connected in order to be able to choose this option.
Parity: Maybe the most popular option among people who want to have 2 or 3 drives merged but do not want to lose too much space of the two-way mirror option. It offers some protection and it does not take so much space as two-way does, let us say it is a kind of win-win situation.
I personally go for simple and have an important backup on optical drives but only for reason I could use more space, know that this way is requiring from me to always have a backup in optical media and that I will need to restore all of it back if even one HDD fails which could take time. But if this way is ok with you, go for it, you will have more space to use.

“Something went wrong, Sorry, installation cannot continue because no compatible office products are detected.”When you have to work on two different languages, that’s where the language packs come in handy. You might have to work on one language but when it comes to proofreading or help, you need another language. Note that some language accessory packs offer partial localization which is why some parts of the Office might show the default language. If you are using Office 365 or Office 2019, 2016, 2013, or 2010, you need to go to the language accessory pack page from office.com and select your language. Once you see the download link, click on it to start downloading the pack. It includes the display in the chosen language, proofing tools for the selected language, as well as the Help in the selected language. Once the installation is complete, follow each one of the given options below to configure the language accessory pack properly.
 One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
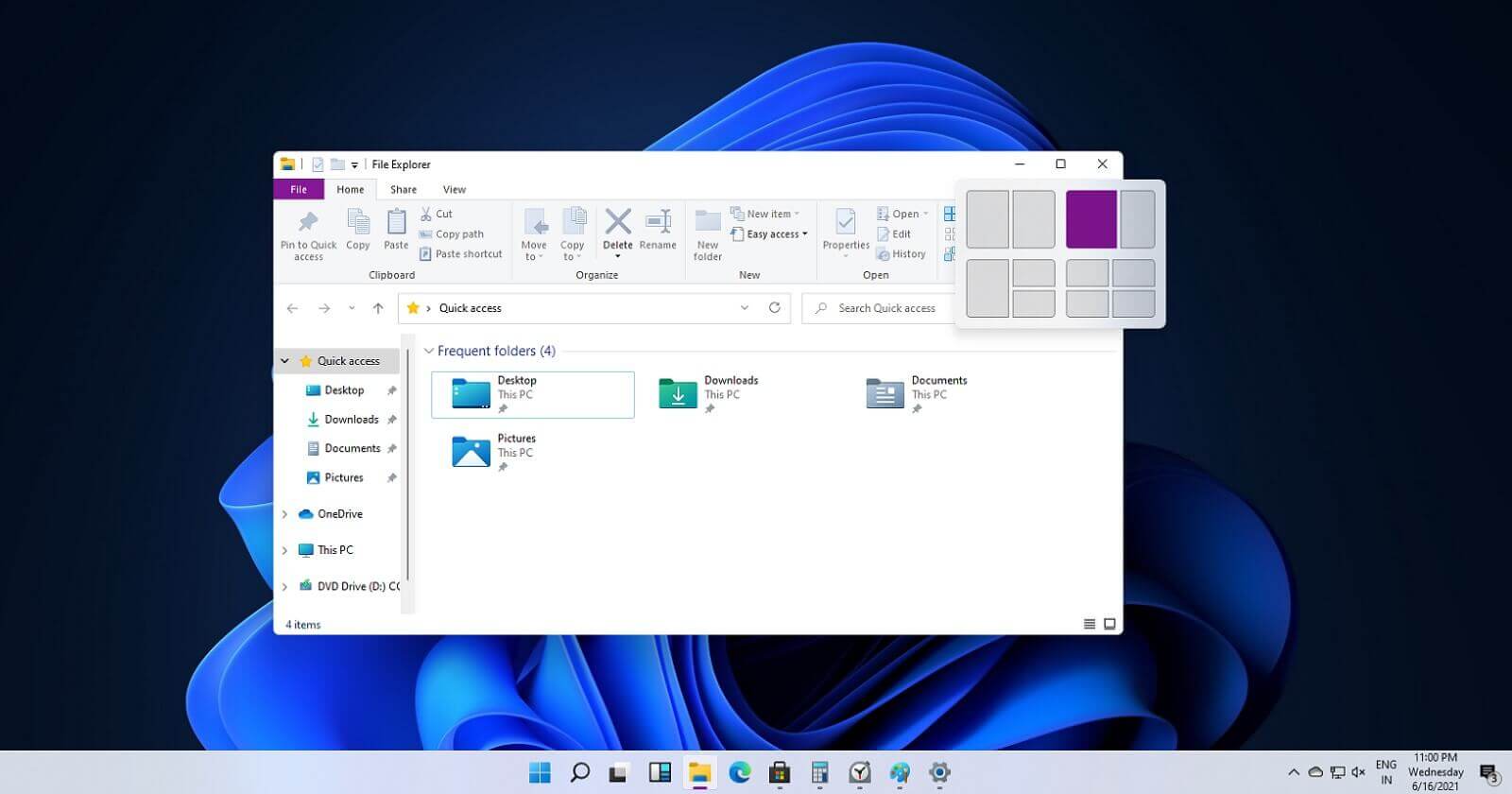 If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
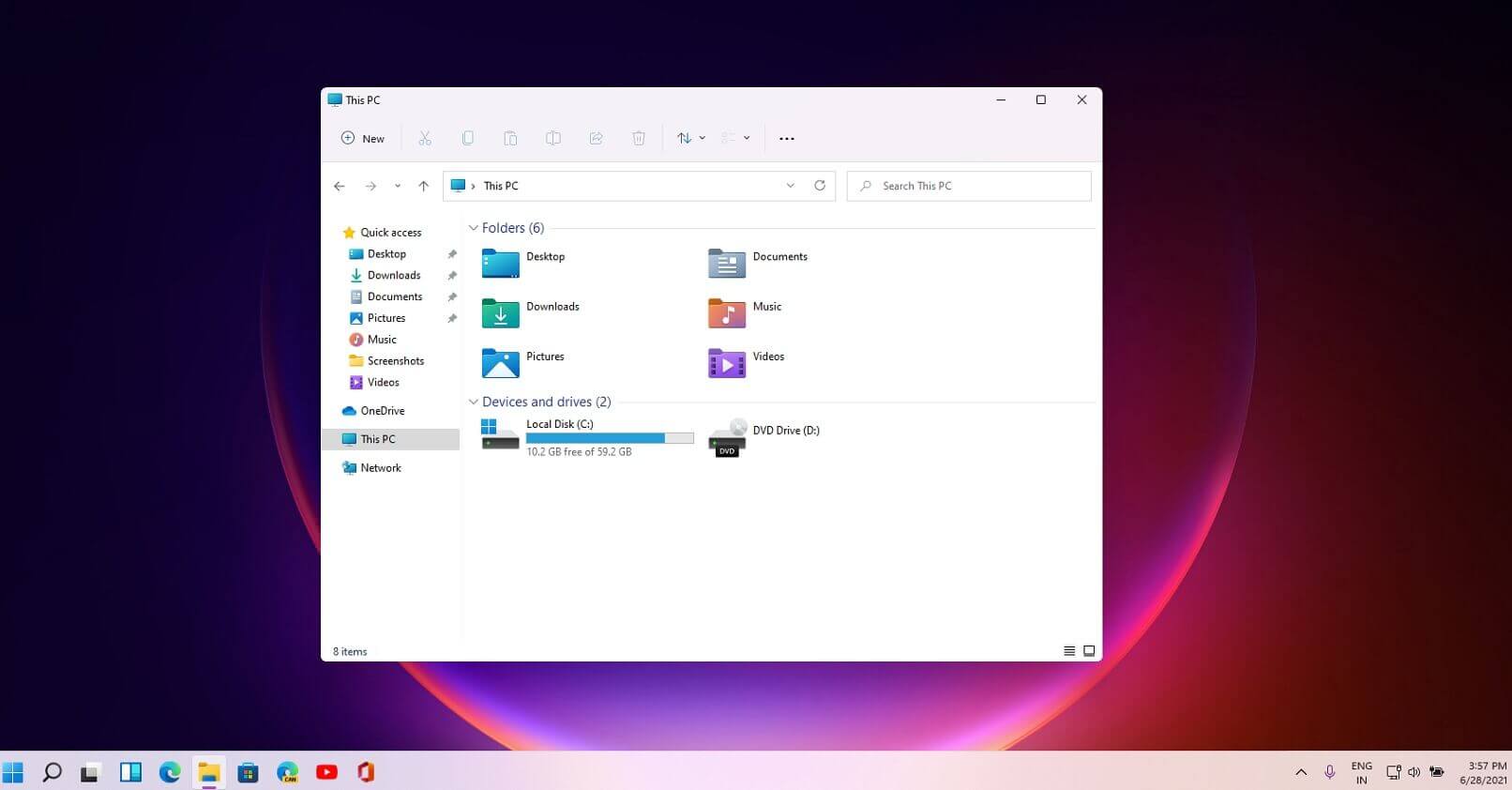 File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
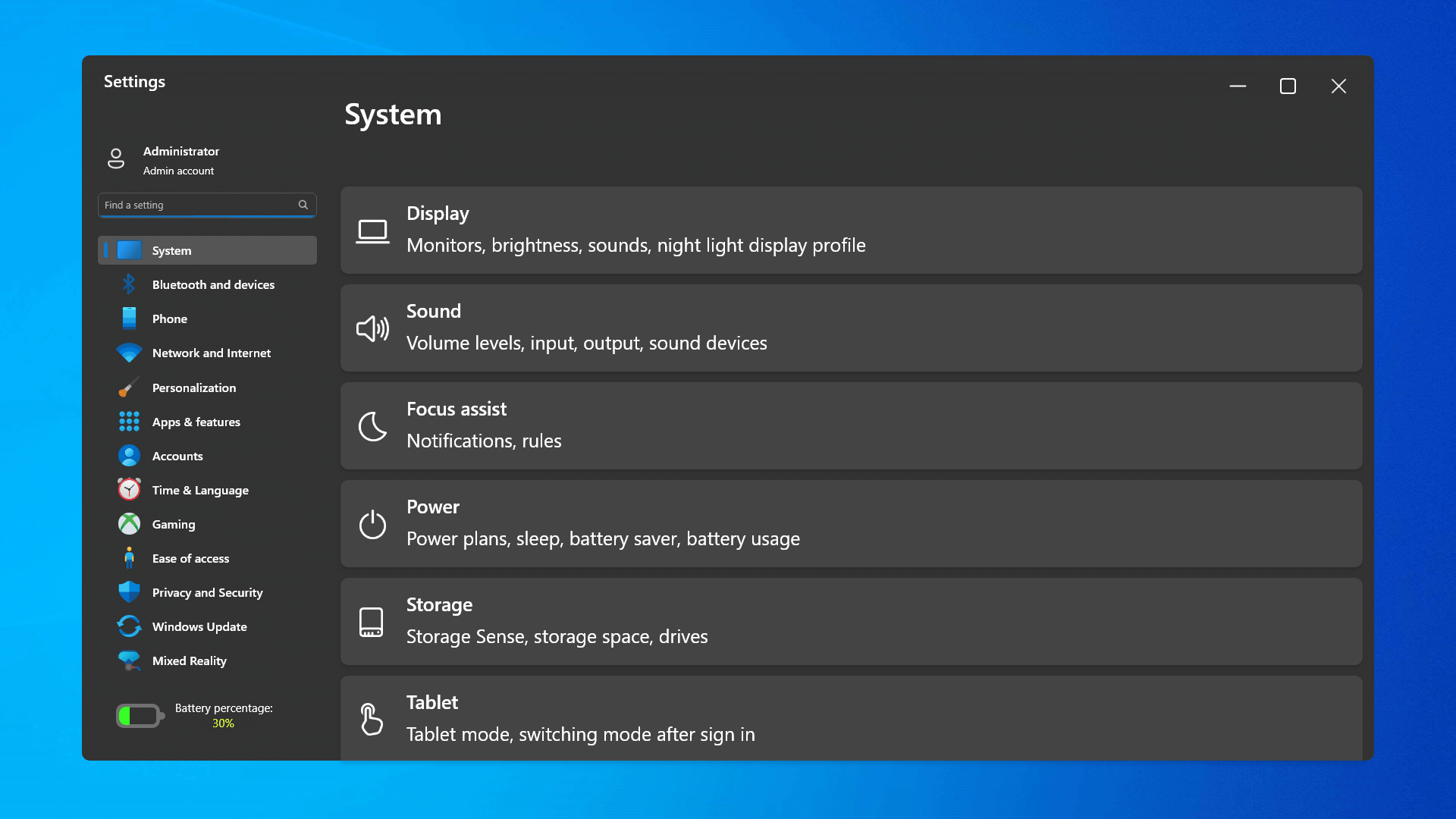 The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
 Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
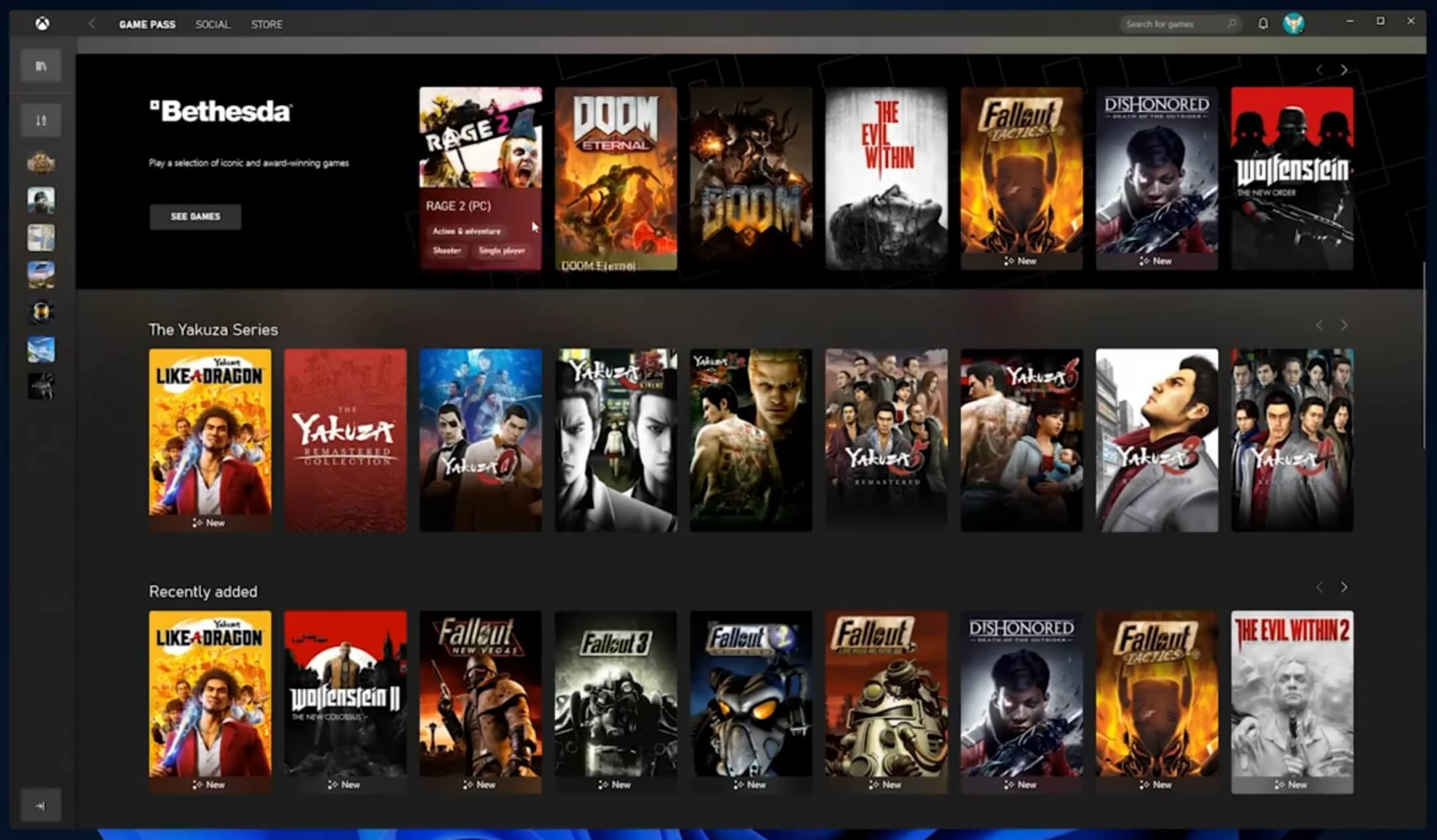 The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
 As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com
As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com Computer voice control has moved a long way from its beginning routes and in today's age controlling your PC with voice is truly a reality and fully possible. Voice control is taking up the steam in everyday life, from simple commands in cars, Alexa, smartphones, TVs, etc. to modern computers.

Windows 10 has introduced voice control into PC with Cortana even during the installation process but a lot has changed from having a virtual assistant in begging days and in today's modern Windows 11 OS. You can now freely open apps, move, copy delete files, and even dictate in order to create a word document.
However, in order to take this advantage, you will need to turn it off first since it is disabled by default. Of course, you will need a microphone and some spare time to train Windows in understanding you properly.
Just like in Windows 10, in Windows 11 voice control is also in accessibility options and the first step is to turn ON Windows Speech Recognition.
Click on the Start button and type Settings into the search bar, click on Open, or press ENTER. On the left side of the settings, window locate and click on Accessibility. On the right part once Accessibility is selected scroll down and find a section titled Interaction and click on Speech. Turn on the switch next to Windows Speech Recognition.
A pop-up will appear that will lead you through the rest of the setup and that's it.
In order to make your voice control better, if you are not satisfied with the results, you can sample more of your voice into the algorithm to tune it more to your liking. Sadly this option is still deep in Control Panel.
Click the Start button and type in Speech recognition into the search bar, look for the search result with Control Panel displayed under it, and click on Open. Click on Train Your Computer to Better Understand You and follow the instructions.
The process will probably take a few minutes. The more data you provide to the speech recognition model, the more accurate it will be when interpreting your instructions. You can train the model multiple times, and each time you do, it should improve the accuracy.
Error C00D11B1:’Windows Media Player can’t play the file.’
 Error Causes
Error CausesThe Error Code 0x802400d most often occurs when users attempt to use the Windows Update tool on their computers to move from one version of the software to another. In some cases, this error is more likely to appear on your computer during the process if you have not performed regular updates to the software as they have been available.
Common symptoms include:
While it can take additional time to deal with the issues that cause Error Code 0x802400d to appear on your computer, there are several steps that you can take to address the problem. These are fairly simple to perform and do not require advanced knowledge of the system to employ.
 Error Causes
Error CausesThe most basic cause for Error Code 0x802400d is that there is a file or a process that is causing the update process to hiccup. In many cases, this error appears when a user attempts to begin the process of updating their computer if they have several stacked updates to perform. Computers that are several updates behind where they should be will display this error more often than computers that are kept on a schedule of recommended updates.
While there are multiple reasons why the Error Code 0x802400d may appear on your computer during the Windows Update process, there are several methods that can be used to attempt to resolve the problem on your own. These are generally easy to do and do not require advanced techniques. However, if you do not feel comfortable addressing the issue on your own, contact a qualified Windows repair technician.
Here are some of the best methods that users can employ to resolve Error Code 0x802400d:
There are a number of different processes, files, and settings that could cause Error Code 0x802400d to appear on your computer during the Windows 10 Update process. For this reason, the most efficient way to determine what the culprit is for your specific issue is to download and use the System Update Readiness function.
This tool is available directly from Windows. Although there are other tools available on the Internet that claim to be able to fix the problem, these can contain viruses and malware, so be cautious if you decide to employ these instead. There are also several versions of the tool on the Windows website, so be sure to download the version that matches the operating system and version of your computer.
Once you have downloaded the Readiness tool from the Windows website, allow it to run a scan on your system. At a minimum, this process will take about fifteen minutes to complete. Although you will see a progress bar at the bottom of the window, it does not always update effectively. Some users have reported that the update appears to stop when it is two-thirds complete. Continue to let the scan run if this happens, rather than canceling it out. Even if the progress bar doesn’t update, the scan is still running.
If you have recently installed new software on your machine, it can sometimes cause problems with the update process. The best way to resolve this issue is to remove or uninstall the software, run the update process again, and then reinstall the software once the Windows system has been successfully updated.
If the above methods are not successful in resolving Error Code 0x802400d from your machine and you are still unable to complete the Windows 10 Update process or if you are not confident in your ability to complete these steps successfully on your own, get in touch with a qualified computer repair technician who is familiar with the issues surrounding Windows 10 in particular. Microsoft offers certifications for Windows repair technicians, so look for a professional who has the experience, skills, and knowledge necessary to adequately address Error Code 0x802400d on your machine.
If you wish to always have at your disposal a utility tool to fix these Windows 10 and other related issues when they do arise, download and install a powerful automated tool.
 Error Causes
Error CausesLinkury Smartbar Engine is a Brower Toolbar for Internet Explorer. Upon investigation, we discovered that this toolbar does not work with the latest versions of Internet Explorer.
From the Author:
What the Smartbar does: – Changes the default search engine in your web browser’s built-in search box. – Changes the default home page of your web browser. – Adds alternative “page not found” functionality. – Enable search from the address bar of your web browser. – Allows software updates of the application once a new version is released. – Adds, removes, or modifies components interacting with search input fields.
While installed, users may see additional unwanted ads throughout their browsing sessions.
Several anti-virus applications have marked this toolbar as a Browser Hijacker, and it is not recommended to keep it on your computer, especially if you are using a newer version of internet explorer that renders this toolbar useless.
Email Access Online is a browser extension published by Polarity Technologies Ltd. That offers users quick and easy access to emails and weather reports. While this might sound interesting and useful, there is nothing this extension offers that cannot be solved with a few simple bookmarks.
While installed Email Access Online monitors the user's browser activity and records visited websites, clicked links, and bought products, this data is later used to serve partner ads if the user looks for the covered categories, additionally, it will hijack your new tab page, changing your search engine to Yahoo to allow easier ad placement.
Browsing the internet with this extension enabled will result in additional ad placement, pop-up ads, and sponsored links throughout your browsing sessions.
Upon further investigation, it was discovered that this extension is a repack of MyEmailXP, which was a repack of Fast Email Checker. Due to its suspicious delivery methods and information gathering, several anti-virus scanners have marked this extension as a browser hijacker and it is recommended to remove it from your computer.