MovieMode is a Potentially Unwanted Program developed by GenTechnologies Apps that allegedly ads a “Lights Off” function to video streaming websites like Youtube. This feature allows a user to dim the entire background around the video, allowing for better video focus.
Although this sounds interesting and useful, upon further inspection it was discovered that this program does not work with modern browsers.
While installed, MovieMode may modify your browser settings, changing your home page, displaying additional ads, and other suspicious behavior.
From the Terms Of Use:
“Applications may be automatically enabled on your web browsers following installation. Applications or advertisements may require changing your web browser’s default home page, default page, or set of pages on startup, default search provider, and other browser settings. So that Applications can function most efficiently and with the least annoyance, Applications may modify or disable certain web browser or operating system features including, but limited to load time alerts, accelerator features, and Content Security Policy functionality. Applications may also include features to notify you when you are launching an application or visiting a web domain that may interfere with your installed Applications. “
About Potentially Unwanted Applications
What is a Potentially Unwanted Program (PUP)?
Have you ever detected an unwanted program running on your computer and wondered how the heck it got there? These unwanted programs, which are referred to as Potentially Unwanted Programs, or PUPs in short, usually tag along as a software bundle when downloading the program and could cause significant problems for users.
From the technical perspective, a PUP is not true “malware”. A basic difference between PUP and malware is distribution. Malware is normally dropped via vulnerability exploitation while PUP gets installed with the consent of the end-user, who knowingly or unintentionally approves the PUP installation on their computer system. On the other hand, it is obvious that PUPs are still bad news for computer users as they could be quite dangerous to the computer in lots of ways.
How do unwanted programs impact you?
Unwanted programs can be found in many forms. Typically, they will be found in adware bundlers that are known to use aggressive and deceptive advertising. Most bundlers install numerous adware applications from various vendors, each of which has its own EULA policy. Safebytes Anti-malware completely eradicates this threat and safeguards your PC against unwanted programs or malware infection. Additionally, most free software programs these days include a few unwanted add-ons; in many instances an internet browser toolbar or browser modification like a homepage hijacker. Not only they needlessly use up space on your screen, but toolbars may also manipulate search results, track your browsing activities, decrease your web browser’s overall performance, and slow down your web connection to a crawl.
They could seem innocent but PUPs are sometimes spyware. The worst part of setting up a PUP is the spyware, adware, and keystroke loggers that may hide inside. Most PUPs don’t have any significant value or advantages. As soon as they are installed, they could waste your valuable system resources and also drastically slow down computer performance. Many of these programs are harmful to computer systems and put your private information and perhaps your identity at stake.
The best ways to stop PUPs
• Always study the license agreement and privacy statement. Don’t agree unless you understand exactly what you’re agreeing to.
• Always pick the custom if you’re provided a choice between Recommended and Custom Installations – never ever click Next, Next, Next blindly.
• Use an ad blocker/pop-up blocker; Install anti-malware products such as Safebytes Anti-malware. These kinds of programs can establish a wall between your computer and online criminals.
• Avoid adding freeware software you simply won’t utilize. Avoid downloading and installing browser extensions and applications you aren’t familiar with.
• Always download applications from the original site. The majority of PUPs find their way to your computer is through download portals, so stay away from it entirely.
What To Do If You Cannot Install Safebytes Anti-Malware?
Malware could cause all sorts of damage after they invade your computer, from stealing your private details to deleting files on your PC. Some malware goes to great lengths to prevent you from downloading or installing anything on your computer system, especially antivirus software programs. If you’re reading this, you probably have infected by malware that prevents you from installing a computer security program like Safebytes Anti-Malware. There are a few fixes you can attempt to get around with this particular problem.
Download the software in Safe Mode with Networking
In the event the malware is set to load at Windows startup, then booting in Safe Mode should prevent it. Just bare minimum required applications and services are loaded whenever you boot your computer or laptop into Safe Mode. You will need to do the following to get rid of malware in Safe mode.
1) At power on/start-up, press the F8 key in 1-second intervals. This will invoke the Advanced Boot Options menu.
2) Use the arrow keys to choose Safe Mode with Networking and press ENTER.
3) Once you get into this mode, you should have internet access again. Now, utilize your web browser normally and go to https://safebytes.com/products/anti-malware/ to download and install Safebytes Anti-Malware.
4) Immediately after installation, do a complete scan and let the program get rid of the threats it detects.
Obtain the anti-malware program using an alternate browser
Some malware only targets certain internet browsers. If this is your situation, utilize another web browser as it might circumvent the malware. If you are not able to download the security software using Internet Explorer, this means the virus could be targeting IE’s vulnerabilities. Here, you must switch to an alternate internet browser such as Firefox or Chrome to download Safebytes Anti-malware software.
Create a portable USB antivirus for eliminating viruses
Another option is to create a portable anti-malware program on your USB stick. Follow these steps to use a thumb drive to clean your infected computer.
1) On a clean computer, install Safebytes Anti-Malware.
2) Insert the pen drive on the same system.
3) Run the setup program by double-clicking the executable file of the downloaded software, which has a .exe file extension.
4) Pick a USB flash drive as the location when the wizard asks you exactly where you want to install the software. Follow activation instructions.
5) Disconnect the USB drive. Now you can use this portable anti-malware on the infected computer system.
6) Double-click the antivirus software EXE file on the pen drive.
7) Click on “Scan Now” to run a complete scan on the affected computer for malware.
SafeBytes Anti-Malware Features
Are you looking to download the best anti-malware software for your system? There are plenty of applications in the market that comes in paid and free versions for Microsoft Windows systems. Some of them are good, some are ok types, and some will ruin your computer themselves! While looking for antimalware software, pick one which gives dependable, efficient, and total protection against all known viruses and malware. On the list of recommended software is SafeBytes AntiMalware. SafeBytes carries a really good reputation for excellent service, and customers are happy with it.
SafeBytes anti-malware is a highly effective and user-friendly protection tool that is designed for users of all levels of IT literacy. With its most advanced virus detection and repair technology, this software protects your personal computer against infections caused by various kinds of malware and similar threats, including adware, spyware, trojans horses, worms, computer viruses, keyloggers, ransomware, and potentially unwanted program (PUPs).
SafeBytes has outstanding features when compared to other anti-malware programs. Here are some of the features you might like in SafeBytes Anti-Malware.
Real-time Protection: SafeBytes gives complete and real-time security for your personal machine. It’ll monitor your computer for suspicious activity regularly and safeguards your computer from illegal access.
Most Reliable AntiMalware Protection: Built on a greatly acclaimed antivirus engine, this malware removal tool has the capacity to find and remove several obstinate malware threats like browser hijackers, potentially unwanted programs, and ransomware that other typical antivirus software will miss.
Safe Browsing: Safebytes assigns all sites a unique safety rating that helps you to have an idea of whether the webpage you are going to visit is safe to view or known to be a phishing site.
Lightweight: SafeBytes provides total protection from online threats at a fraction of the CPU load due to its advanced detection engine and algorithms.
Premium Support: You can get 24/7 technical assistance to quickly resolve any concern with your security application.
Overall, SafeBytes Anti-Malware is a solid program since it has loads of features and can identify and remove any potential threats. Malware problems can become a thing of the past once you put this application to use. If you need advanced forms of protection features and threat detections, purchasing SafeBytes Anti-Malware could be well worth the dollars!
Technical Details and Manual Removal (Advanced Users)
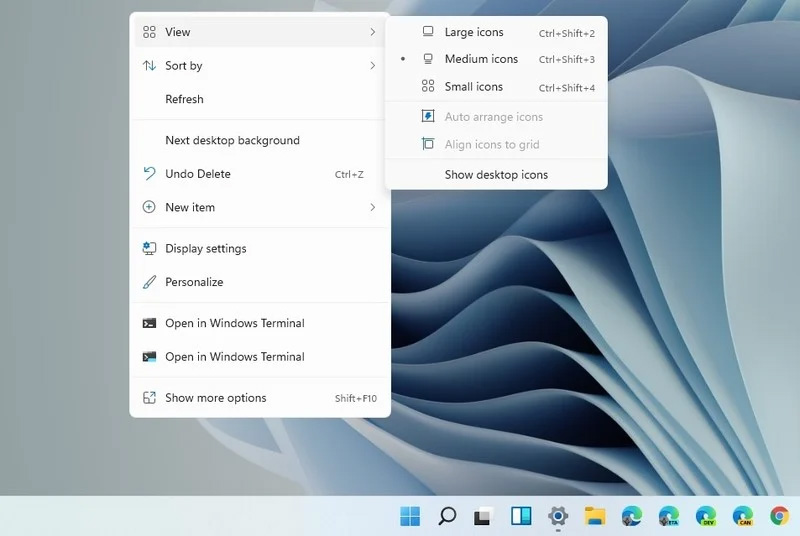
If you don’t wish to use malware removal software and like to get rid of Movie Mode manually, you could possibly accomplish this by going to the Add/Remove Programs menu in the control panel and removing the offending program; in cases of browser add-ons, you can remove it by visiting the browser’s Add-on/Extension manager. You may even want to reset your browser settings, and also clear your web browser cache and cookies.
To ensure the complete removal, manually check your hard drive and computer registry for all of the following and remove or reset the values as needed. Having said that, editing the Windows registry is often a hard task that only advanced computer users and professionals should attempt to fix it. Moreover, some malware keeps replicating which makes it difficult to get rid of. It is advisable that you carry out the removal process in Safe Mode.


 Since this requires registry tweak, please follow given solution step by step
Since this requires registry tweak, please follow given solution step by step
 Following are proven solutions that will resolve the issue and provide you with a working device.
Following are proven solutions that will resolve the issue and provide you with a working device.

 Intel announced that Pat Gelsinger (CEO) and Dr. Ann Kelleher (technology Department head) will discuss Intel’s process and packaging innovations on an upcoming webcast that will happen on July 26th.
The spokesman will talk and provide a deeper look at the process and packaging roadmaps for Intel. As we know Intel is planning to expand its production capabilities, outsource some of its technologies and offer foundry services to other chip design companies.
The strategy will also include a shift to a 7nm process and Intel’s effort to set itself again as leader of CPU performance by 2024.
There is also a chance that we will hear exact plans for Intel in the next three or four years.
Intel didn't reveal much else about what Gelsinger and Kelleher plan to discuss during the webcast. The event will be streamed on July 26 at 2 pm PT via the
Intel announced that Pat Gelsinger (CEO) and Dr. Ann Kelleher (technology Department head) will discuss Intel’s process and packaging innovations on an upcoming webcast that will happen on July 26th.
The spokesman will talk and provide a deeper look at the process and packaging roadmaps for Intel. As we know Intel is planning to expand its production capabilities, outsource some of its technologies and offer foundry services to other chip design companies.
The strategy will also include a shift to a 7nm process and Intel’s effort to set itself again as leader of CPU performance by 2024.
There is also a chance that we will hear exact plans for Intel in the next three or four years.
Intel didn't reveal much else about what Gelsinger and Kelleher plan to discuss during the webcast. The event will be streamed on July 26 at 2 pm PT via the 