The GifsGalore Toolbar from Mindspark Interactive Network, Inc. is proposed to active Web users who like to embed GIFs into their emails and share entertaining GIFs with friends via social media services. The GifsGalore software can be added to your Internet client for free but you need to be using Google Chrome, Internet Explorer or Mozilla Firefox for the GifsGalore Toolbar to be activated.
When installed it hijacks your New tab page and default search engine changing them to search.myway.com. This extension also monitors user browsing activity recording information such as: visited websites, clicked links, viewed products, etc. This information is later used to better target ads.
While browsing the internet with this extension enabled you will see additional pop-up ads, as well as sponsored links and injected ads throughout your browsing session, especially in search results.
Browser hijacking is actually a form of unwanted software program, often a browser add-on or extension, which causes modifications in web browser’s settings. There are various reasons why you may experience an internet browser hijack; however commercial, advertising, and marketing are definitely the main reasons for their creation. The idea would be to force users to visit specific sites that are aiming to improve their site visitor traffic and generate higher ad earnings. It could seem naive, but most of these sites are not legitimate and could present a serious risk to your online safety. Browser hijackers can even let other vicious programs without your knowledge further damage the computer.
When your web browser is hijacked, the following can happen: the browser’s homepage is modified; bookmark and the new tab are also changed; the default search engine has been changed and your browser security settings have been lowered without your knowledge; you see unwanted new toolbars added; unstoppable flurries of popup ads appear on your computer screen; your web browser gets sluggish, buggy, crashes very often; you are prohibited access to particular web pages, including the site of an anti-malware software developer like SafeBytes.
Browser hijackers might use drive-by downloads or file-sharing networks or perhaps an email attachment to reach a targeted computer. They may also come from any BHO, browser extension, toolbar, add-on, or plug-in with malicious purpose. Other times you might have unintentionally accepted a browser hijacker as part of an application package (usually freeware or shareware). Examples of well-known browser hijackers are Fireball, CoolWebSearch. save, Ask Toolbar, RocketTab, and Babylon Toolbar.
Some browser hijacking could be quite easily reversed by discovering and removing the corresponding malware software from your control panel. Yet, certain hijackers are far harder to find or eliminate since they might get themselves associated with some crucial computer files that enable them to operate as a necessary operating system process. Additionally, manual removals demand deep system knowledge and therefore can be a very difficult job for novices.
Installing and running an anti-malware program on the affected computer could automatically erase browser hijackers and other malicious applications. Safebytes Anti-Malware has a sophisticated anti-malware engine to help you prevent browser hijacking in the first place, and mop up any pre-existing problems. And use a PC optimizer, like Total System Care, to get rid of all related files in the registry and repair browser issues.
All malware is bad, but certain types of malware do a lot more damage to your computer than others. Some malware is created to restrict or prevent things that you want to do on your PC. It may well not let you download anything from the internet or stop you from accessing some or all websites, particularly the antivirus websites. If you’re reading this article, you may have infected by a virus that stops you from installing security software such as Safebytes Antimalware on your PC. There are some actions you can take to circumvent this problem.
The Windows OS includes a special mode known as “Safe Mode” in which just the bare minimum required programs and services are loaded. If the malware is obstructing internet access and affecting the computer, launching it in Safe Mode allows you to download anti-virus and run a scan whilst limiting possible damage. To enter into Safe Mode or Safe Mode with Networking, press the F8 key while the computer is starting up or run MSConfig and find the “Safe Boot” options in the “Boot” tab. After you restart into Safe Mode with Networking, you can download, install, as well as update the anti-malware program from there. At this point, you could run the antivirus scan to remove computer viruses and malware without any interference from another application.
Web-based viruses can be environment-specific, aiming for a particular browser or attacking specific versions of the browser. If you are not able to download the anti-malware software program using Internet Explorer, it means the virus could be targeting IE’s vulnerabilities. Here, you should switch over to a different browser like Firefox or Chrome to download the Safebytes Anti-malware program.
Another solution is to create a portable anti-malware program onto your USB stick. Adopt these measures to run the antivirus on the affected computer system.
1) Make use of another virus-free computer to download Safebytes Anti-Malware.
2) Plug the Thumb drive into the uninfected computer.
3) Double click on the executable file to run the installation wizard.
4) Select flash drive as the place when the wizard asks you where you wish to install the software. Do as instructed on the screen to finish up the installation process.
5) Now, transfer the USB drive to the infected computer system.
6) Double click the Safebytes Anti-malware icon on the thumb drive to run the software.
7) Click on “Scan Now” to run a complete scan on the affected computer for malware.
If you’re planning to purchase anti-malware for your desktop, there are plenty of brands and utilities for you to consider. A few of them are good but there are lots of scamware applications that pretend as legit anti-malware programs waiting around to wreak havoc on your computer. You need to go with a tool that has obtained a strong reputation and detects not only viruses but other kinds of malware as well. Amongst few good applications, SafeBytes Anti-Malware is the strongly recommended software program for the security-conscious individual.
SafeBytes anti-malware is a trusted tool that not only protects your PC completely but is also extremely user-friendly for people of all ability levels. With its cutting-edge technology, this application can help you remove multiples types of malware which include viruses, trojans, PUPs, worms, ransomware, adware, and browser hijackers.
Robust, Anti-malware Protection: Built upon a greatly acclaimed anti-virus engine, this malware removal tool can identify and remove several stubborn malware threats like browser hijackers, PUPs, and ransomware that other common antivirus software will miss.
Live Protection: SafeBytes gives you round-the-clock protection for your personal computer restricting malware intrusions instantly. They’re extremely effective in screening and removing numerous threats because they are regularly improved with new updates and alerts.
Web Filtering: SafeBytes inspects the links present on a web page for possible threats and alerts you whether the website is safe to browse or not, through its unique safety ranking system.
Fast Scan: SafeBytes’s virus scan engine is one of the quickest and most efficient in the industry. It's targeted scanning greatly increases the catch rate for viruses which is embedded in various computer files.
Very Low CPU and RAM Usage: SafeBytes is a lightweight and easy-of-use anti-virus and anti-malware solution. Since it uses low computer resources, this application leaves the computer power exactly where it belongs to: with you.
24/7 Premium Support: You will get 24/7 technical support to quickly resolve any issue with your security tool.
To sum it up all, SafeBytes Anti-Malware offers superb protection combined with very low system resource usage with both great malware detection and prevention. You now may realize that this particular software does more than just scan and eliminate threats from your computer. You’ll get the best all-around protection for the money you spend on SafeBytes AntiMalware subscription, there isn’t any doubt about it.
To remove GifsGalore manually, go to the Add or Remove programs list in the Windows Control Panel and select the program you want to get rid of. For internet browser extensions, go to your web browser’s Addon/Extension manager and choose the add-on you would like to remove or disable. You’ll probably also want to reset your web browser.
If you choose to manually delete the system files and registry entries, use the following list to make sure you know precisely what files to remove before undertaking any actions. However, editing the registry is usually a difficult task that only experienced users and professionals should try to fix it. Moreover, some malware is capable of replicating or preventing deletion. Carrying out this malware-removal process in Safe Mode is recommended.
Files:
%LOCALAPPDATA%\GifsGaloreTooltab
%UserProfile%\Local Settings\Application Data\GifsGaloreTooltab
%UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\Default\Sync Extension Settings\fnjgjdfhhakkbojkgmiihabbbjhgbchh
%UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\Default\Extensions\fnjgjdfhhakkbojkgmiihabbbjhgbchh
%LOCALAPPDATA%\Google\Chrome\User Data\Default\Sync Extension Settings\fnjgjdfhhakkbojkgmiihabbbjhgbchh
Registry:
HKEY_LOCAL_MACHINE\Software\[APPLICATION]\Microsoft\Windows\CurrentVersion\Uninstall..Uninstaller
GifsGaloreTooltab Uninstall Internet Explorer
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\LowRegistry\DOMStorage\gifsgalore.dl.tb.ask.com
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\LowRegistry\DOMStorage\gifsgalore.dl.myway.com
HKEY_CURRENT_USER\Software\GifsGalore

HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionSearchFlightingWhiteSearchBox
Error Code 40 is a device driver error that users encounter on any Windows 2000 and later operating systems. It occurs when the peripheral device that you connect to your PC cannot be accessed due to a change in the system registry.
This is due to the presence of invalid sub-keys of the device driver in the system registry. It is a common error that users come across and appears on your PC with either of the following messages:
“Information in the registry entry for this driver is invalid”
OR
"Windows cannot access this hardware because its service key information in the registry is missing or recorded incorrectly. (Code 40)"
 Error Causes
Error CausesAs mentioned above, the error code is triggered when the device driver’s invalid sub-keys appear in the registry, effectively changing it. This happens when the windows system files get damaged due to the following factors:
Factors such as incomplete installations or uninstallations or an improper system shut down can cause files to become damaged that threaten the health of your computer.
Removing viruses from the computer is also another factor as it removes the entries in the Windows system files which contain the viruses including spyware or malware
Fixing Error Code 40 is similar to fixing other device manager error codes. Here are a few methods you can try.
You can use system restore to eliminate the problem. Here is how you can use it:
If using system restore also does not work in removing the error code, you may have to resort to manually uninstalling and then reinstalling the device driver causing the problem.
This would be necessary since the remaining incomplete files due to a partial removal or installation of programs is what contributes to the error code. By uninstall and reinstalling the device driver program, it would lead to the completion of the files.
You can do this by firstly logging in as Administrator and open Device Manager. Select the device that is causing the problem and double click it and make sure that the peripheral is connected properly to the PC. Upon opening, click on the ‘Driver’ tab and then select ‘Update Driver’.
Make sure to refer to the system documentation that you received with your PC or computer to check for the motherboard details and driver specifics.
Manually uninstalling and reinstalling the driver will do the trick, however, it may be time-consuming especially when you would have to resort to your hardware user manual.
Therefore, using a program such as DriverFIX can save you a lot of time and frustration in having your device work properly on your computer.
DriverFIX, with its user-friendly approach to help you fix your PC issues, comes with an integrated database that detects which drivers you need to reconfigure within just a few seconds and downloads it automatically.
It further ensures that your drivers are installed in their entirety leaving no room for any incomplete files to remain that create Error Code 40.
It also has the added advantage of being able to backup and restores your files should there be the slightest possibility of system file damage.
Thus, registry damage can be averted by letting the software roll back the system files to an earlier healthy checkpoint. Driver Assist is the answer to fixing your PC error codes accurately and quickly.
Click here to download DriverFIX to fix Error Code 40 quickly and effectively!In today's modern world many households have internet access, most of the connection nowadays is done via Wi-Fi or wireless but there is a high probability that you have also a few devices connected via cable. There are of course many disadvantages and advantages between cable connection and wireless connection.
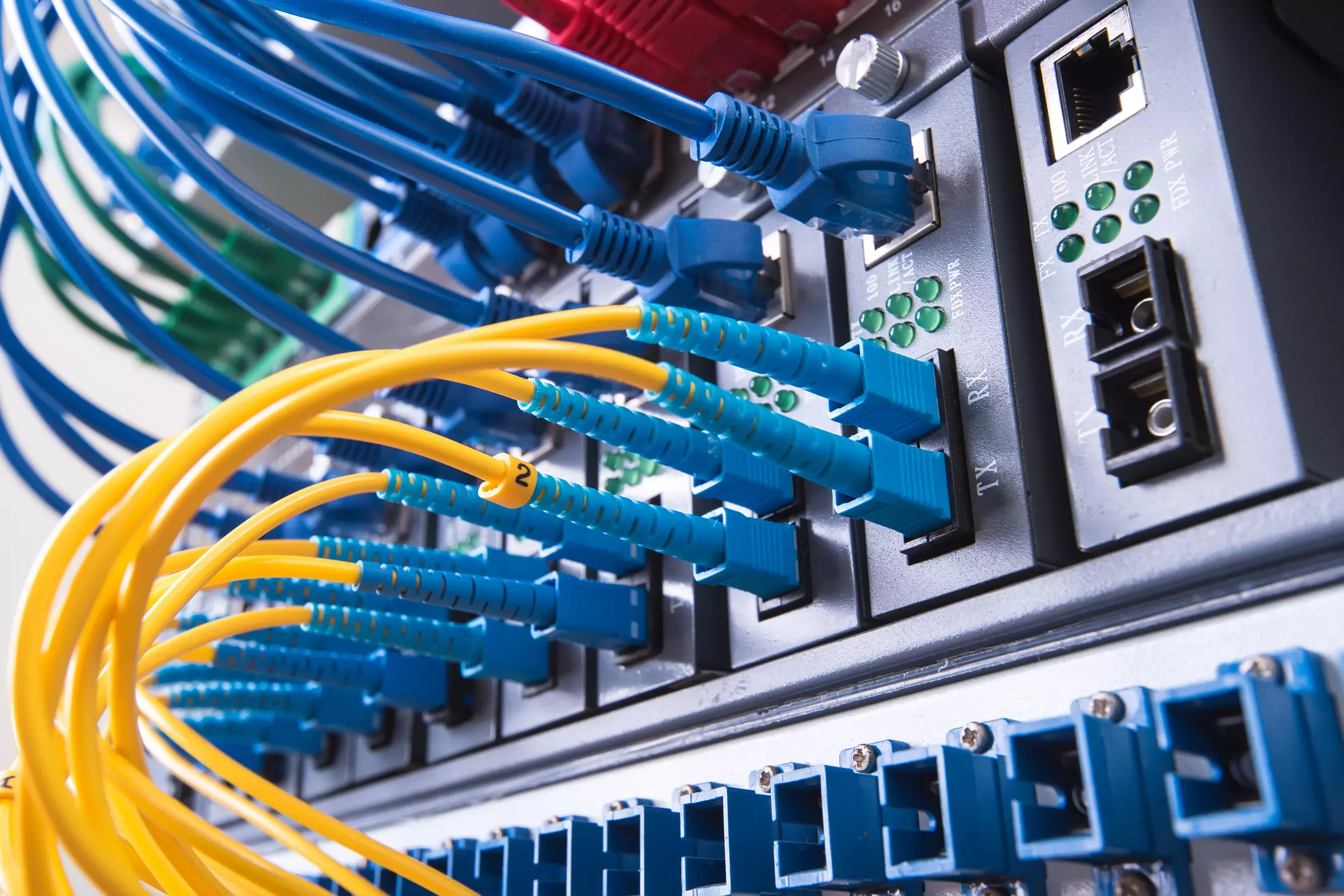
The main advantages of a hard cable connection are of course faster speed and stability compared to Wi-Fi. But if we look into the cables themselves there is also a big difference between them. Not all cables are the same and quality as well as speed vary a lot between them. Choosing the right cable is essential in order to make a maximum of your internet and we have some great tips and explanations of what cables do so you can make the right choice and enjoy your full internet potential.
Cheap cables and expensive ones are not the same no matter what everyone tells you. The old proverb you get what you pay is true and more expensive cables will be made from better materials and will have a higher transfer rate.
Quality network cables are separated into different categories with proper markings and when buying one you should always look for these markings on the cables themselves, do not buy cables that do not have markings since they will often provide lower transfer rates or will not be shielded from outside influences resulting in packet drops and instability in a network.
Unless stated, these standards are typically rated at their quoted speeds for a run of around 100 meters (around 330 ft) and use a standard RJ-45 Ethernet connector. Each generation of cable is designed to be compatible with the generations that came before it, so it’s possible (for example) to use a Cat-6a cable with a router that only supports speeds of 1Gbps.
When purchasing higher quality cable you might not be able to choose if you have shielding or not since some standards like Cat-6a, Cat-7, and Cat-8 are always shielded. But if you do not have the need for these and you are satisfied with Cat-5e for example you can choose.
Shielded cables are a little more expensive but they will provide you with a coating that will eliminate interference from outside waves making cables more reliable. Of course, if the cable will go through a room that does not have many radio waves or some other interferences then buying a shielded cable is a waste of money.
Usually, there are two types of connector platings on connectors, silver, and gold, and people usually think that gold is much better but there are major differences between silver and gold platings and truth to be told there is no better one, both are different and should be considered depending on your need.
Silver plating will provide you with faster speed since its conductivity is larger than gold, but gold is slower on the oxidation front so its life span is longer. On the other hand, if your cables are always connecting and disconnecting gold will be first to be scrubbed off from the surface since the gold coating is much thinner.
Overall if you would only connect cable once and have slower internet than cable capacity gold is the way to go, in another case if you would use the cable as always connecting and switching and your internet plan is the same as cable transfer capacity you might want to go with silver one.
Network cables are made from copper, your standard conduction material but even here there are differences in quality and therefore the chance of pocket losses over it. More quality less loss and more stable connection and this will depend on the purity of copper that is used in the cable itself. More purity in copper, more stability, simple as that.
So as you can see, there are a lot of different things that will influence your pick of proper network cable but the overall best advice is to get one that will fit well into your needs and setup. pair it up with your router and your internet plan since just simply buying something that you can not use is really a waste of money.