If you are typing inside the Search bar, Cortana, Taskbar, Windows 10 apps, etc., and then everything seems invisible then read on as this post will guide you in fixing this issue. At first, you might think that something is wrong with your keyboard but it really has nothing to do with it. The problem actually lies with the apps from Microsoft Store. Thus, if you can’t type anything in any of the apps from Microsoft Store in Windows 10, refer to the options given below to fix them.
Ctfmon.exe is a Microsoft process in Windows 10 that controls the Alternative User Input as well as the Office Language bar. In other words, it enables end-users to control the computer using on-screen keyboard inputs, speech, and even pen for various languages. It would be better if you launch the program once by going to the C:/Windows/system32 folder. Doing so will ensure that whatever API is needed for the keyboard typing to work properly again. You also have to make sure that its startup status is not disabled. In addition, you can also try the following steps, alternatively.
This will ensure that all the text boxes will start to work again. And if the task MsCtfMonitor is missing from the list of tasks, you can import it with the XML file from basics.net. Then download and create a task to run it each time you log in to your PC.
You might also try running the Windows Store Apps Troubleshooter as it can help in resolving issues with the Windows Store apps. This built-in tool can resolve most of the app-related problems. To use it, go to Settings > Update & Security > Troubleshooting > Windows Store Apps and from there, click the start the troubleshooter button. The Windows Store Apps Troubleshooter will scan the computer for any issues with the Windows store apps and will automatically fix them if it finds any.
You can also run the DISM Tool as it helps in repairing the Windows System Image as well as the Windows Component Store in Windows 10. Using this built-in tool, you have various options such as the “/ScanHealth”, “/CheckHealth”, and “/RestoreHealth” which could help in fixing the problem.
System File Checker or SFC is a built-in command utility that helps in restoring corrupted files as well as missing files. It replaces bad and corrupted system files to good system files. To run the SFC command, follow the steps given below.
The command will start a system scan which will take a few whiles before it finishes. Once it’s done, you could get the following results:

netsh int ip reset
MySearchDial is a browser hijacker that typically comes bundled with free software on the internet. This web platform designed for searching the internet and offers the installation of its software. This software injects itself into browsers and gains access to your settings, browsing data & user information. This data is distributed to the ad providers without limitation. While covered by their EULA, most users will be unaware of what they agree to with checkboxes selected by default. The software also adds a huge amount of registry keys and links throughout the operating system. Since the software injects itself into many personal files, removing the software results in a total reset of your browser settings. For these reasons MySearchDial is classified as potentially unwanted and is flagged for removal by a number of internet security utilities.
 Many times we were talking and writing here on Errortools.com about security, privacy, hacking, identity theft, etc. We tried to raise important security questions and I hope I have managed to at least shed some light and change maybe some bad behaviors for some, helping them embrace better routines about their security on their PC.
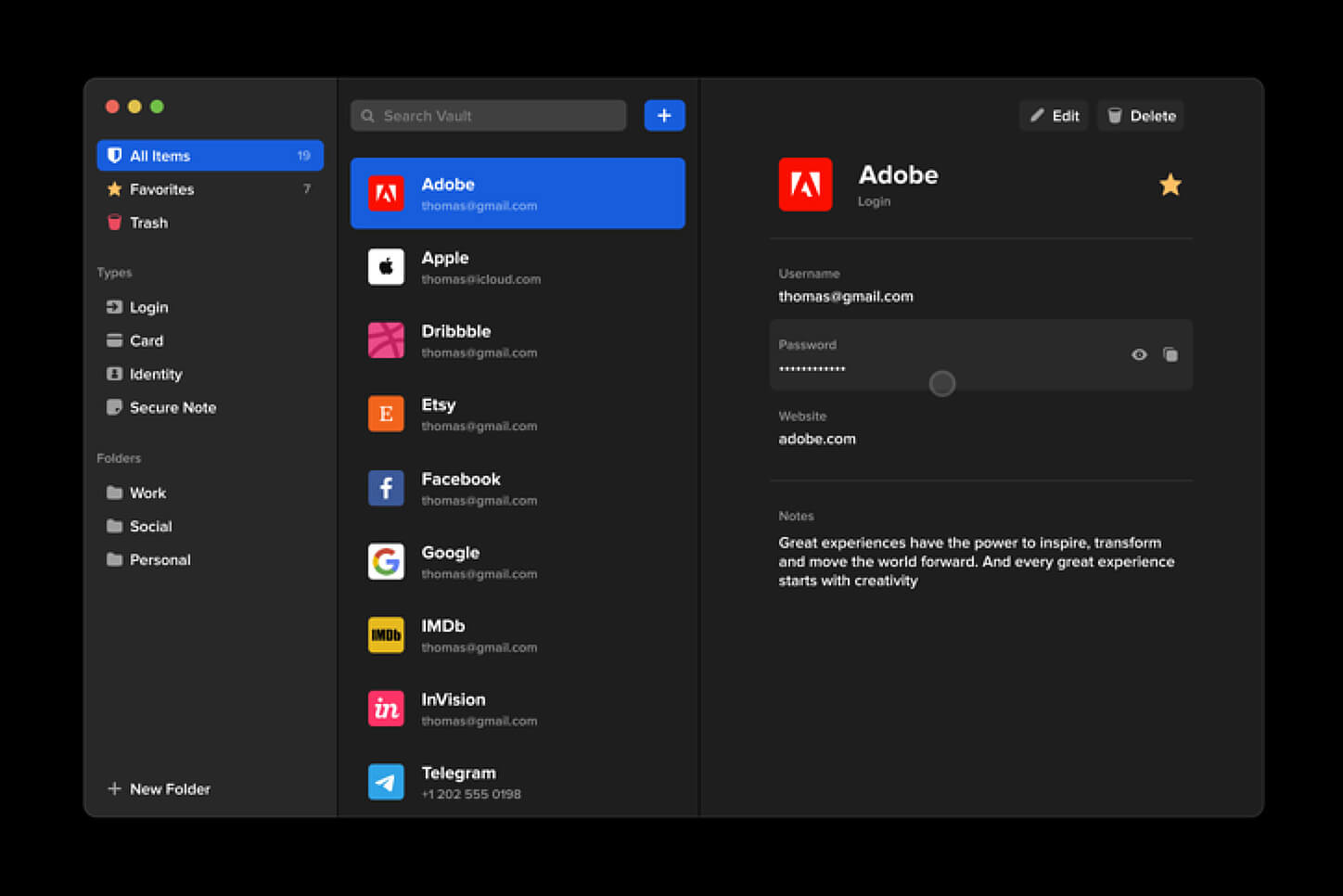
In this light, I will today present you with one neat and awesome piece of software, a password manager worth your time and money (if you want premium features): BitWarden.
Many times we were talking and writing here on Errortools.com about security, privacy, hacking, identity theft, etc. We tried to raise important security questions and I hope I have managed to at least shed some light and change maybe some bad behaviors for some, helping them embrace better routines about their security on their PC.
In this light, I will today present you with one neat and awesome piece of software, a password manager worth your time and money (if you want premium features): BitWarden.
“The exception Breakpoint, A breakpoint has been reached, (0x80000003) occurred in the application.”As you can tell, the Windows Executive STATUS message is a warning and if you are given an option, you must select one of the options from the message box. So if you are running the application in an end-user environment rather than in a development environment, you must contact the supplier of the running application regarding this error message since this shouldn’t be happening when a finished program is running. Before you get started executing the troubleshooting guide given below, make sure that you create a System Restore Point first since you will be dealing with some critical settings in Windows. Having done this, proceed to the options provided below.
chkdsk /f /r
This toolbar/web browser extension is ad/search-supported that is typically installed as an optional offer, users generally have this bundled with 3rd party software. During setup, this toolbar will modify the home page and new tab pages to the affiliate search portal MyWay.com using a primary search engine to collect shared search revenue. It will also modify the default search provider as well. While this extension is installed users will experience a display of additional ads and sponsored content throughout their browsing sessions, as well as the possibility of pop-up ads. Several anti-virus scanners have marked this extension as a Browser Hijacker and it is recommended to remove it from your computer.
 10 worst computer viruses in history
10 worst computer viruses in historyDaily Bible Guide is a browser extension developed by Mindspark Inc. for Google Chrome Browser. This extension offers users a fast and easy way to find Bible passages, view daily verses, study the Bible and view the current weather. When installed, this extension changes your default search engine and your home page to MyWay.
When installed this extension gathers user browsing information such as visited websites, search queries, clicked links, and other information. This information is later used to better target ads.
While active, you may encounter additional unwanted ads and sponsored links throughout your browsing sessions. Daily Bible Guide was marked as a Browser Hijacker by several anti-virus scanners, and due to its information mining behavior, it is considered a security risk and it is not recommended to keep on your computer; being flagged for optional removal.