Marine Aquarium Lite is a Browser Extension for Google Chrome. This extension changed your default search ending and home page to MyWebSearch.com. It is published by Mindspark Interactive and is considered a browser hijacking extension.
While installed, users will see additional ads and sponsored links in their search results. This extension also collects user website data, which allows it to better target ads. Several anti-virus scanners have marked Marine Aquarium Lite as a Browser Hijacker and are marked for removal.
From the Author:
MyWebSearch is an incredibly popular toolbar (over 20 million active users each month!), that gives you access to the web’s leading search engine Google;
includes some of the most popular products on the web for making communication easier, more expressive, and more entertaining.
The MyWebSearch toolbar platform allows you to take advantage of more than a dozen interactive features and websites.
About Browser Hijackers
Browser hijacking is a very common type of online fraud where your web browser configuration settings are altered to make it carry out things you never intend. They’re created to interfere with web browser functions for a variety of reasons. Typically, hijackers will force hits to websites of their choice either to increase traffic generating higher ad earnings, or to obtain a commission for each and every user visiting there. Even though it may seem naive, all browser hijackers are damaging and thus always classified as security risks. Once the malware attacks your PC, it begins to mess things up a whole that slows your system down to a crawl. In the worse case, you will be pushed to deal with serious malware threats too.
Major signs that your browser has been hijacked
There are many signs of browser hijacking: home-page is changed; you observe new unwanted bookmarks or favorites added, typically directed to ad-filled or porn websites; The default search page of web browser is altered; you find multiple toolbars in your browser; you’ll notice random pop-ups start showing on a regular basis; your web browser starts running slowly or displays frequent glitches; you have prohibited entry to specific web pages, for example, the site of an anti-malware software developer like SafeBytes.
How they get into your computer or laptop
Browser hijackers infect PCs by numerous means, including through a file-share, a drive-by download, or an infected e-mail. They also come from add-on software, also referred to as browser helper objects (BHO), web browser plug-ins, or toolbars. Also, some shareware and freeware can put the hijacker inside your PC through “bundling”. An example of some notorious browser hijacker includes Conduit, Anyprotect, Babylon, DefaultTab, SweetPage, RocketTab, and Delta Search, but the names are constantly changing.
Browser hijacking could lead to serious privacy issues and also identity theft, affect your web browsing experience by taking control over outbound traffic, drastically slows down your PC by deleting lots of resources, and result in system instability as well.
How you can fix a browser hijack
Some hijackers can be simply removed by uninstalling the free software they were included with or by eliminating any extension you have recently added to your computer system. But, the majority of hijacking codes are certainly not easy to get rid of manually, as they go deeper into the operating system. And there is no denying the very fact that manual fixes and removal could be a difficult job for an amateur computer user. Besides, there are several risks connected with fiddling around with the system registry files.
You can choose automatic browser hijacker removal by simply installing and running efficient anti-malware software. SafeBytes Anti-Malware discovers all types of hijackers – including Marine Aquarium Lite – and eliminates every trace quickly and efficiently. Utilize a system optimizer (such as Total System Care) together with your anti-malware software to fix various computer registry issues, eliminate computer vulnerabilities, and enhance your computer performance.
Can't Install Safebytes Anti-malware because of Malware? Try This!
Malware may cause several different types of damage to computer systems, networks, and data. Some malware sits in between your PC and the net connection and blocks a few or all websites that you want to visit. It will also prevent you from installing anything on your PC, particularly antivirus applications. If you are reading this right now, you have probably realized that virus infection is the reason behind your blocked net traffic. So what to do when you want to install an anti-malware program such as Safebytes? Even though this sort of issue will be tougher to circumvent, there are some actions you can take.
Boot your system in Safe Mode
In Safe Mode, you could adjust Windows settings, uninstall or install some programs, and eradicate hard-to-delete viruses and malware. In the event the malware is blocking access to the internet and affecting your PC, running it in Safe Mode allows you to download anti-virus and run a diagnostic scan whilst limiting potential damage. To enter into Safe Mode or Safe Mode with Networking, press the F8 key while the system is booting up or run MSConfig and find the “Safe Boot” options in the “Boot” tab. As soon as you restart the PC into Safe Mode with Networking, you may download, install, as well as update the anti-malware program from there. At this point, you could run the anti-virus scan to get rid of viruses and malware without interference from another application.
Switch over to some other internet browser
Some malware mainly targets certain web browsers. If this is your situation, use another browser as it may circumvent the computer virus. When you suspect that your Internet Explorer happens to be hijacked by a virus or otherwise compromised by cybercriminals, the best thing to do would be to switch to a different web browser such as Google Chrome, Mozilla Firefox, or Apple Safari to download your chosen security software – Safebytes Anti-Malware.
Make a bootable USB anti-virus drive
To successfully get rid of the malware, you will need to approach the issue of running an antivirus software program on the infected computer system from a different angle. Do these simple measures to clean up your affected computer by using a portable antivirus.
1) Use another virus-free computer system to download Safebytes Anti-Malware.
2) Plug the pen drive into the clean PC.
3) Double-click on the downloaded file to run the installation wizard.
4) Select the drive letter of the pen drive as the place when the wizard asks you where you want to install the anti-virus. Follow the instructions on the computer screen to finish up the installation process.
5) Now, plug the thumb drive into the infected computer.
6) Run the Safebytes Anti-malware directly from the pen drive by double-clicking the icon.
7) Click on the “Scan” button to run a full computer scan and remove viruses automatically.
SafeBytes Security Suite Benefits"]If you are looking to install an anti-malware program for your computer, there are various tools out there to consider but you just cannot trust blindly anyone, no matter whether it is a free or paid program. Some are good ones, some are decent, and some are simply just fake anti-malware programs that will harm your personal computer themselves! You must be careful not to choose the wrong product, particularly if you purchase premium software. One of the highly recommended software by industry analysts is SafeBytes Anti-Malware, a well-known security application for Microsoft Windows.
SafeBytes anti-malware is a powerful, highly effective protection software intended to assist users of all levels of IT literacy in detecting and removing harmful threats from their PC. Through its cutting-edge technology, this software protects your personal computer against infections brought on by different kinds of malware and similar internet threats, including adware, spyware, trojans horses, worms, computer viruses, keyloggers, potentially unwanted program (PUPs), and ransomware.
SafeBytes anti-malware provides an array of advanced features that sets it aside from all others. Here are a few popular features present in this computer software:
Robust Anti-malware Protection: This deep-cleaning antimalware software program goes much deeper than most antivirus tools to clean your personal computer. Its critically acclaimed virus engine locates and disables hard to remove malware that conceals deep within your PC.
Real-time Active Protection: SafeBytes offers an entirely hands-free active protection and is set to check, block, and get rid of all threats at its first encounter. This tool will constantly monitor your computer for any suspicious activity and updates itself regularly to keep abreast of the latest threats.
Web protection: SafeBytes gives an instant safety rating on the web pages you’re going to visit, automatically blocking risky sites and making sure that you are certain of your safety while browsing the web.
Lightweight Application: The program is lightweight and will work silently in the background, and will not have an effect on your computer efficiency.
Fantastic Tech Support: For any technical questions or product guidance, you can get 24/7 professional assistance through chat and e-mail.
SafeBytes has developed a fantastic anti-malware solution to help you conquer the latest malware threats and virus attacks. You can rest assured that your computer will be protected in real-time as soon as you put this software program to use. If you want sophisticated forms of protection features and threat detections, purchasing SafeBytes Anti-Malware could be worth the money!
Technical Details and Manual Removal (Advanced Users)
If you’d like to manually remove Marine Aquarium Lite without the use of an automated tool, it might be possible to do so by removing the application from the Microsoft Windows Add/Remove Programs menu, or in cases of browser plug-ins, going to the browsers AddOn/Extension manager and removing it. You’ll likely also want to reset your browser to its default configuration settings.
To be certain of complete removal, find the following Windows registry entries on your system and delete them or reset the values accordingly. Please be aware that this is for skilled users only and could be challenging, with wrong file removal resulting in additional PC errors. In addition, some malicious programs have the capability to defend against its deletion. Doing this in Safe Mode is suggested.
Files:
C:\%Documents%\%User%\Local\Temp\nst2.tmp\nsDialogs.dll
C:\%Documents%\%User%\Local\Temp\nst2.tmp\System.dll
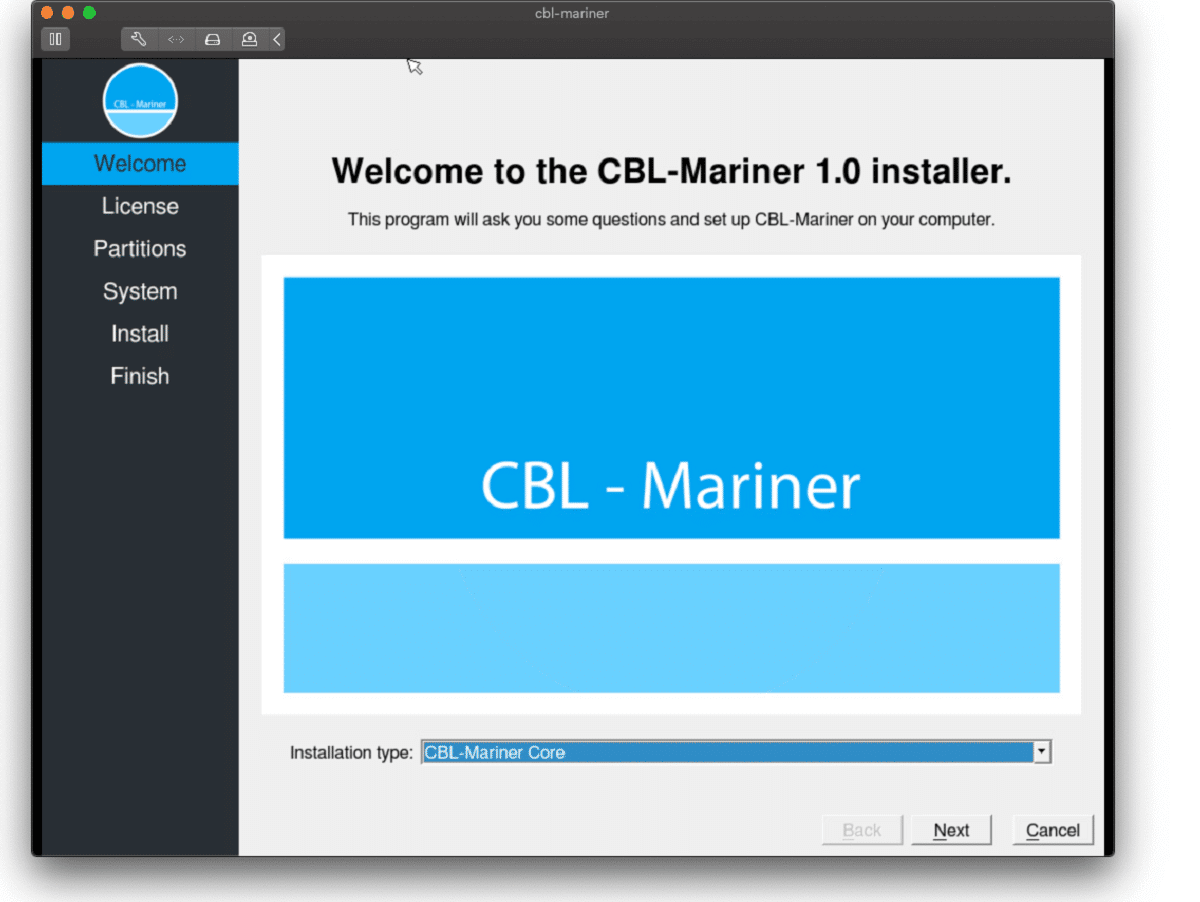 Well if anyone told me just a few years ago that I will see the day when Microsoft releases a new OS based on Linux I would be very amused, but that day has come. Mariner is the newest OS out of nowhere.
Microsoft’s new Linux Distro, dubbed Common Base Linux (CBL)-Mariner, isn’t the type of distro you’d want to install directly on any old machine. It’s primarily meant for cloud infrastructure and edge products. Specifically Microsoft’s Cloud and Edge products.
But if you are curious, it’s possible to run. Juan Manuel Rey, a Microsoft Senior Program Manager for Azure VMware, recently published a guide to ISO CBL-Mariner image. With that, you can easily get it up and running. And you can build CBL-Mariner on an Ubuntu 18.04 desktop. So you can try it out since it is free.
You can get it from here: https://github.com/microsoft/CBL-Mariner
It is obvious that Microsoft aims to set itself as a leader in enterprise server environments with this move and it is very likely that it may succeed or at least give a good shake to its competitors, mainly red hat and Suse which are two dominant distros in that field.
Many believe that they can win over by providing regular updates and package delivery via their already established system and that feature could be a turning point for some.
In any case, time will tell and we shall see.
Well if anyone told me just a few years ago that I will see the day when Microsoft releases a new OS based on Linux I would be very amused, but that day has come. Mariner is the newest OS out of nowhere.
Microsoft’s new Linux Distro, dubbed Common Base Linux (CBL)-Mariner, isn’t the type of distro you’d want to install directly on any old machine. It’s primarily meant for cloud infrastructure and edge products. Specifically Microsoft’s Cloud and Edge products.
But if you are curious, it’s possible to run. Juan Manuel Rey, a Microsoft Senior Program Manager for Azure VMware, recently published a guide to ISO CBL-Mariner image. With that, you can easily get it up and running. And you can build CBL-Mariner on an Ubuntu 18.04 desktop. So you can try it out since it is free.
You can get it from here: https://github.com/microsoft/CBL-Mariner
It is obvious that Microsoft aims to set itself as a leader in enterprise server environments with this move and it is very likely that it may succeed or at least give a good shake to its competitors, mainly red hat and Suse which are two dominant distros in that field.
Many believe that they can win over by providing regular updates and package delivery via their already established system and that feature could be a turning point for some.
In any case, time will tell and we shall see. 





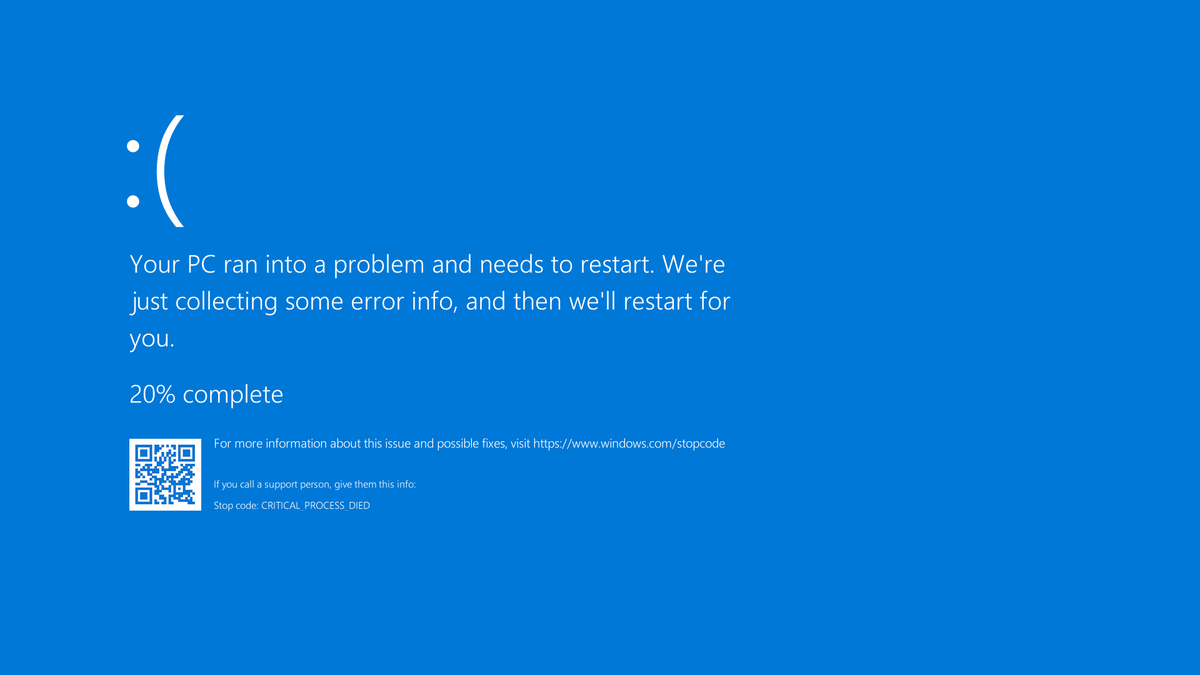 A stop error or exception error commonly called the blue screen of death (BSoD) or blue screen, is an error screen displayed on Windows computers following a fatal system error. It indicates a system crash, in which the operating system has reached a condition where it can no longer operate safely. This is caused by many different problems, such as a general hardware failure or a crucial process terminating unexpectedly.
A stop error or exception error commonly called the blue screen of death (BSoD) or blue screen, is an error screen displayed on Windows computers following a fatal system error. It indicates a system crash, in which the operating system has reached a condition where it can no longer operate safely. This is caused by many different problems, such as a general hardware failure or a crucial process terminating unexpectedly.
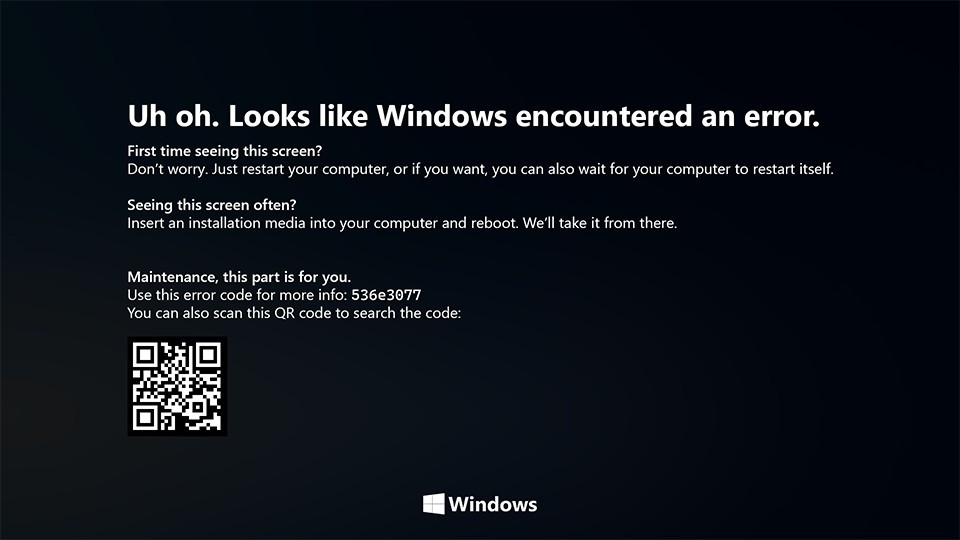 On Windows 10 systems, a Black Screen of Death can be caused by an unfinished Windows Update.
On Windows 10 systems, a Black Screen of Death can be caused by an unfinished Windows Update.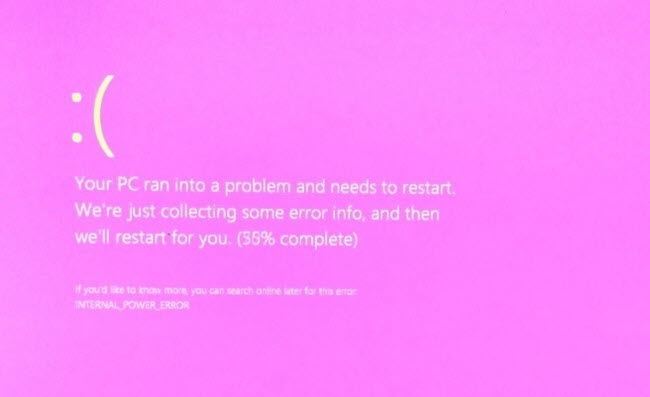 It is a diagnostic screen with a white type on a pink background. Pink Screen is mainly seen when the VMkernel of an ESX/ESXi host experiences a critical error, becomes inoperative, and terminates any virtual machines that are running. It is not fatal and generally considered more of a developer testing issue. When encountered, it can be fixed quickly by following the simple action of pressing and holding your computer’s power button to shut down the device.
It is a diagnostic screen with a white type on a pink background. Pink Screen is mainly seen when the VMkernel of an ESX/ESXi host experiences a critical error, becomes inoperative, and terminates any virtual machines that are running. It is not fatal and generally considered more of a developer testing issue. When encountered, it can be fixed quickly by following the simple action of pressing and holding your computer’s power button to shut down the device.
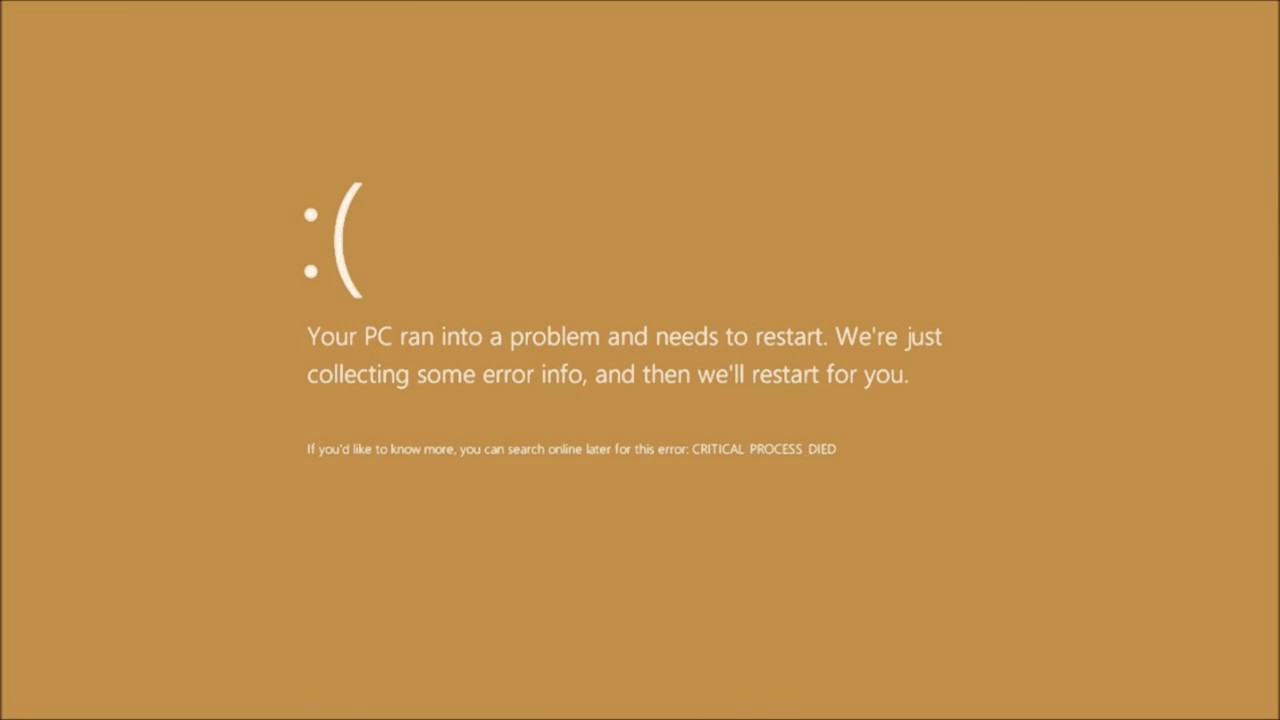 The Microsoft Windows 10 Operating System Brown Screen of Death is an on-screen fatal error notification with bug check codes which is seen when a computer crashes due to graphics hardware or software-related problems (failing graphics drivers).
The Microsoft Windows 10 Operating System Brown Screen of Death is an on-screen fatal error notification with bug check codes which is seen when a computer crashes due to graphics hardware or software-related problems (failing graphics drivers).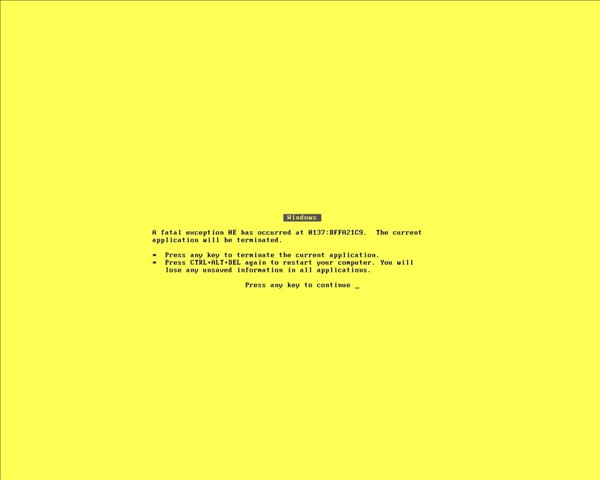 It affects the functioning of a browser, particularly Mozilla Firefox. The Yellow Screen of Death makes the appearance with a weird buzzing sound in the background when the XML parser refuses to process an XML document causing a parsing error and a weird buzzing sound. The issue persists unless the computer is manually rebooted.
It affects the functioning of a browser, particularly Mozilla Firefox. The Yellow Screen of Death makes the appearance with a weird buzzing sound in the background when the XML parser refuses to process an XML document causing a parsing error and a weird buzzing sound. The issue persists unless the computer is manually rebooted.
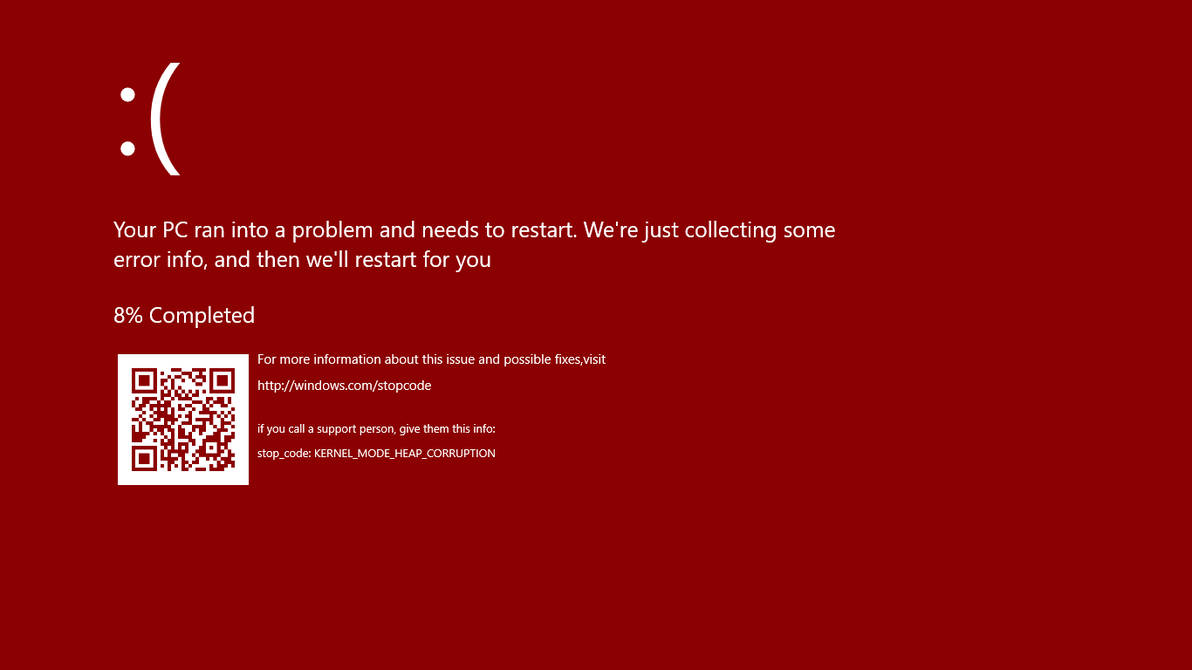 Commonly the Windows 10 red screen is caused due to the hardware error, particularly if you overclock your Windows PC/laptop. Despite this, sometimes the red screen of death is also caused by outdated or incompatible drivers or due to BIOS issues.
Commonly the Windows 10 red screen is caused due to the hardware error, particularly if you overclock your Windows PC/laptop. Despite this, sometimes the red screen of death is also caused by outdated or incompatible drivers or due to BIOS issues.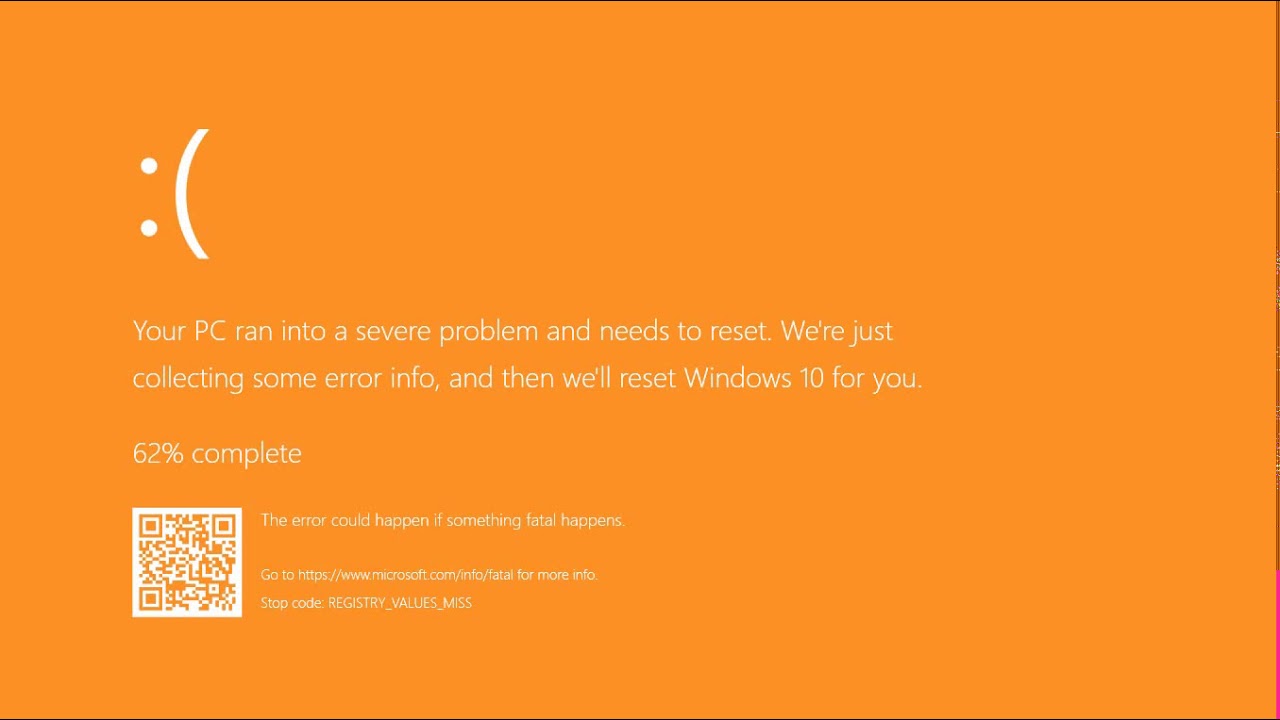 The Orange Screen of Death on Windows occurs due to fatal hardware errors. Multiple reasons have been reported for the Orange Screen of Death. Some had this issue when watching a YouTube video, some were not able to boot into Windows. It can even occur when waking up from Sleep.
The Orange Screen of Death on Windows occurs due to fatal hardware errors. Multiple reasons have been reported for the Orange Screen of Death. Some had this issue when watching a YouTube video, some were not able to boot into Windows. It can even occur when waking up from Sleep.
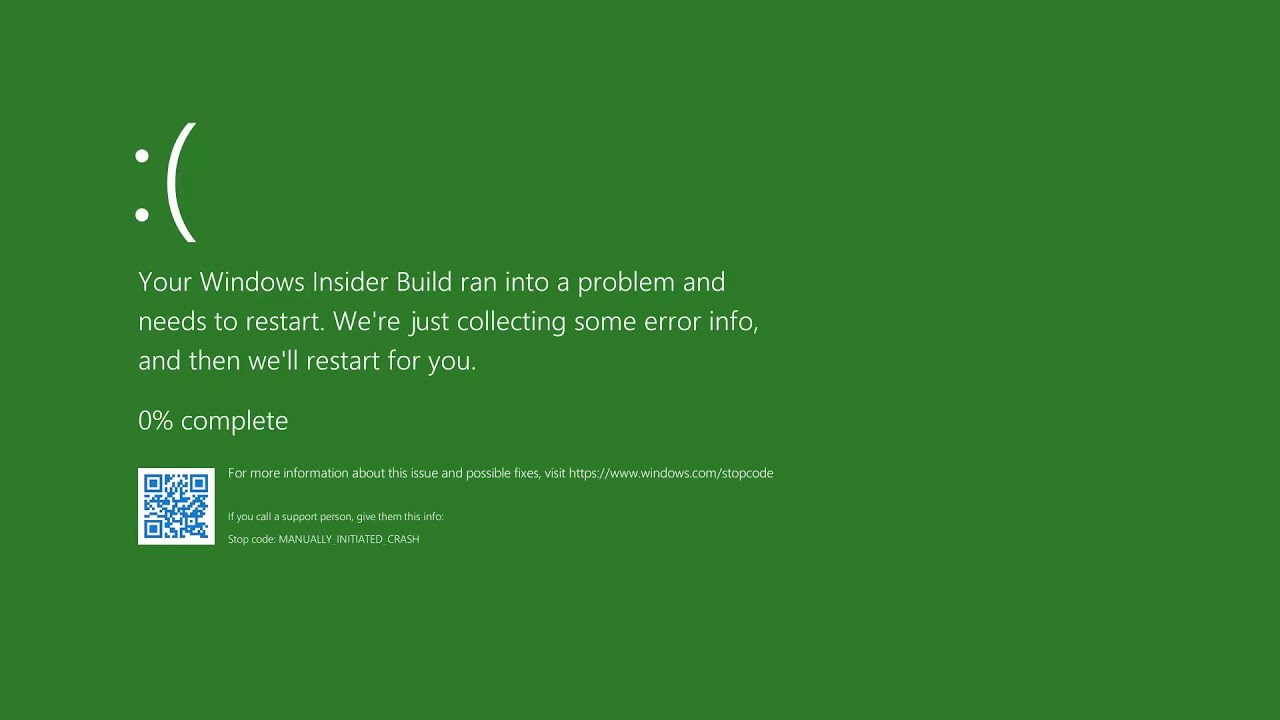 The green screen of death only appears when you're running an Insider Preview version of Windows 10. It's the same as the blue screen of death, and it will show the same error messages. ... If you see a green screen of death (GSOD) on your PC, that's a sign you're using an Insider Preview build of Windows 10.
The green screen of death only appears when you're running an Insider Preview version of Windows 10. It's the same as the blue screen of death, and it will show the same error messages. ... If you see a green screen of death (GSOD) on your PC, that's a sign you're using an Insider Preview build of Windows 10. The White Screen on Windows is also an error where the screen of the computer just turns white and freezes. There can be several things that can cause the white screen to appear on the Windows laptop monitor. But the main issue could be because of malfunctioning of the graphics hardware.
The White Screen on Windows is also an error where the screen of the computer just turns white and freezes. There can be several things that can cause the white screen to appear on the Windows laptop monitor. But the main issue could be because of malfunctioning of the graphics hardware. 
