Linkey is a potentially unwanted web browser search extension for the top browsers, designed to modify the user’s search and home pages in order to direct advertising. This extension changes your default search provider, redirects new tabs, and distributes information & statistics to the server. This extension will display unwanted ads, redirect you through unwanted search engines, and send your browsing information (potentially private information) back to its ad network.
From the publisher: Linkey is compatible with all the latest versions of Internet Explorer, Chrome, and Firefox. Linkey is a simple browser extension that allows you to get the best sites in one click in visualized & friendly interface.
About Browser Hijackers
Browser hijacking is actually a type of unwanted software, often a browser add-on or extension, which causes modifications in the browser’s settings. Browser hijackers could do many different things on your PC. Usually, hijackers will force hits to websites of their preference either to increase traffic producing higher advertisement revenue, or to obtain a commission for each and every user visiting there. Nonetheless, it’s not that harmless. Your online safety is compromised and it is also extremely annoying. Browser hijackers could also allow other malicious programs without your knowledge to further damage your computer.
How to know whether the web browser is hijacked?
The typical symptoms that suggest having this malicious software on your PC are:
1. your homepage has been reset to some unfamiliar site
2. your browser is constantly being redirected to adult sites
3. the essential web browser settings are modified and undesirable or insecure resources are put into the trusted sites listing
4. unsolicited new toolbars are added to your browser
5. you may notice endless pop-up ads on your screen
6. your web browser starts running sluggishly or exhibits frequent errors
7. You simply can’t access particular sites, particularly anti-malware websites.
How it infects your computer
Browser hijackers attack computers through malicious e-mail attachments, downloaded infected computer files, or by checking out infected internet sites. They could be included with toolbars, BHO, add-ons, plug-ins, or browser extensions. Also, certain freeware and shareware can put the hijacker in your PC through the “bundling” technique. Examples of well-known browser hijackers are Fireball, GoSave, Ask Toolbar, CoolWebSearch, Babylon Toolbar, and RocketTab.
Browser hijackers could interrupt the user’s browsing experience severely, keep track of the websites visited by users and steal financial information, cause problems in connecting to the internet, and ultimately create stability issues, making applications and computers crash.
How you can get rid of a browser hijacker
Some hijackers can be simply removed by deleting the free software they came with or by removing any extension you have recently added to your computer. Unluckily, the majority of the software products used to hijack a browser are deliberately built to be difficult to eliminate or detect. Moreover, manual removals demand in-depth system knowledge and therefore can be an extremely difficult job for novices.
What To Do When You Cannot Download Safebytes Anti-Malware?
All malware is bad and the magnitude of the damage may vary greatly in accordance with the type of infection. Certain malware variants modify internet browser settings by including a proxy server or modify the computer’s DNS configurations. When this happens, you will be unable to visit some or all of the websites, and therefore unable to download or install the necessary security software to remove the malware. If you’re reading this, you may have infected by a virus that prevents you from downloading computer security software like Safebytes Anti-Malware. There are a few options you can attempt to get around with this obstacle.
Install in Safe Mode
The Windows-based PC has a special mode called “Safe Mode” in which just the bare minimum required programs and services are loaded. If the malware is blocking internet access and affecting your PC, running it in Safe Mode will let you download antivirus and run a diagnostic scan while limiting potential damage. In order to get into Safe Mode or Safe Mode with Networking, press F8 while the system is starting up or run MSConfig and look for the “Safe Boot” options under the “Boot” tab. After you restart into Safe Mode with Networking, you could download, install, as well as update anti-malware software from there. After installation, run the malware scanner to remove most standard infections.
Use an alternate browser to download an antivirus application
Certain viruses might target vulnerabilities of a specific web browser that obstruct the downloading process. If you appear to have a virus attached to Internet Explorer, then switch over to an alternate internet browser with built-in safety features, such as Chrome or Firefox, to download your favorite antivirus program – Safebytes.
Install security software on a thumb drive
Here’s another solution which is creating a portable USB anti-malware software that can check your system for malicious software without needing installation. Do these simple actions to clean up your affected PC using portable anti-malware.
1) Download the anti-malware program on a virus-free computer.
2) Plug the Flash drive into the clean computer.
3) Double-click on the downloaded file to open the installation wizard.
4) Choose the USB flash drive as the destination for saving the software file. Follow the on-screen instructions to finish the installation.
5) Unplug the USB drive. You may now utilize this portable anti-malware on the infected computer system.
6) Double click the Safebytes Anti-malware icon on the flash drive to run the software.
7) Click on “Scan Now” to run a complete scan on the infected computer for malware.
A Look at the Best AntiMalware Program
Want to download the very best anti-malware software for your laptop? There are several applications in the market that come in paid and free versions for Microsoft Windows systems. Some of them are excellent, some are ok types, while some will destroy your PC themselves! When searching for an anti-malware tool, choose one which provides dependable, efficient, and complete protection against all known computer viruses and malware. On the list of highly recommended software programs is SafeBytes AntiMalware. SafeBytes carries a good track record of top-quality service, and customers are very happy with it.
Safebytes is one of the well-established computer solutions companies, which offer this all-inclusive anti-malware software. Using its cutting-edge technology, this application will allow you to eradicate multiples types of malware such as computer viruses, trojans, PUPs, worms, ransomware, adware, and browser hijackers.
SafeBytes has got a variety of wonderful features that can help you protect your PC from malware attacks and damage. Below are some typical features present in this tool:
Live Protection: SafeBytes offers a totally hands-free active protection that is set to observe, prevent and remove all threats at its very first encounter. This utility will always monitor your computer for any suspicious activity and updates itself regularly to keep current with the newest threats.
Most Reliable AntiMalware Protection: This deep-cleaning anti-malware software program goes much deeper than most antivirus tools to clean your computer system. Its critically acclaimed virus engine finds and disables hard-to-remove malware that conceals deep inside your PC.
Internet Security: Through its unique safety rating, SafeBytes notifies you whether a site is safe or not to access it. This will make sure that you’re always certain of your safety when browsing the net.
Lightweight Utility: The program is lightweight and can run silently in the background, and that does not have an effect on your PC efficiency.
24/7 Live Professional Support: SafeBytes provides 24/7 technical support, automatic maintenance, and upgrades for the best user experience.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove Linkey without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by Linkey
Files:
C:Users%USER%AppDataLocalTempis33084504mysearchdial.dll
C:Users%USER$AppDataLocalTempis357113909833170_stpsetup.exe
c:Users%USER$AppDataLocalTempMega Browsemegabrowse_setup.exe
C:Program Files (x86)Linkeylog.log
C:Program Files (x86)LinkeyHelper.dll
C:Program Files (x86)LinkeyChromeExtensionChromeExtension.crx
C:Program Files (x86)Linkey
C:Program Files (x86)LinkeyChromeExtension
C:Program Files (x86)LinkeyIEExtension
C:Users%USER$AppDataRoamingDigitalSitesUpdateProc
Registry:
HKLMSOFTWARECLASSESAPPID6A7CD9EC-D8BD-4340-BCD0-77C09A282921
HKLMSOFTWAREWOW6432NODECLASSESAPPID6A7CD9EC-D8BD-4340-BCD0-77C09A282921
HKLMSOFTWARECLASSESCLSID181F2C09-56DD-4F98-86D7-59BA2BC59B5A
HKLMSOFTWARECLASSESCLSID4D9101D6-5BA0-4048-BDDE-7E2DF54C8C47
HKLMSOFTWAREMICROSOFTWINDOWSCURRENTVERSIONEXPLORERBROWSER HELPER OBJECTS
HKLMSOFTWARELINKEY
HKLMSOFTWAREWOW6432NODELINKEY
HKLMSOFTWAREWOW6432NODESYSTEMKGeneral
HKUS-1-5-18-ED1FC765-E35E-4C3D-BF15-2C2B11260CE4-0SOFTWARECONDUITValueApps
HKLMSOFTWAREWOW6432NODEMICROSOFTWINDOWSCURRENTVERSIONEXPLORERBROWSER HELPER OBJECTSEF5625A3-37AB-4BDB-9875-2A3D91CD0DFD
HKLMSOFTWARELINKEY|ie_jsurl, http://app.linkeyproject.com/popup/IE/background.js
HKLMSOFTWAREWOW6432NODELINKEY|ie_jsurl, http://app.linkeyproject.com/popup/IE/background.js



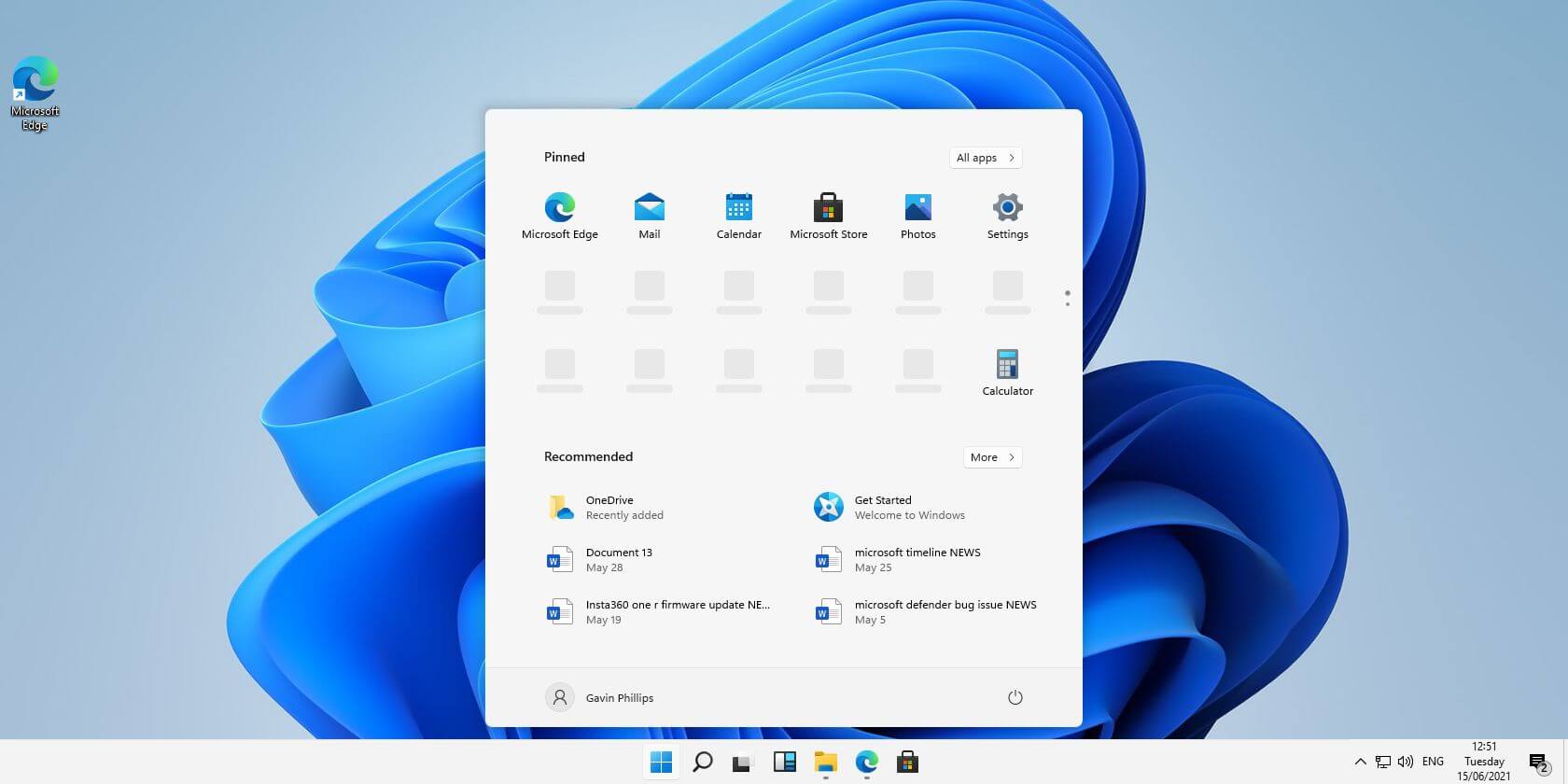 Windows 11 comes with glass and transparency effects by default once it is installed. The transparency effect looks really good but if in any case, you do not like them, you can easily turn them off very easily
Windows 11 comes with glass and transparency effects by default once it is installed. The transparency effect looks really good but if in any case, you do not like them, you can easily turn them off very easily

