Action Classic Games Toolbar is another product from Mindspark Interactive Network, Inc. that may claim to relieve users of their boredom with more than 500 online games. The Action Classic Games toolbar is available for download from its official web page and Google Web Store, though it is normally distributed via advertising directly from its website. When installed, it will change your home page and new tab to MyWay.com and start gathering user browsing information while active.
Browsing the internet with Action Classic Games enabled will result in the additional ad and sponsored content placement throughout the browsing sessions. This extension has been flagged as a Browser Hijacker by several top anti-virus applications and is therefore not recommended to keep on your computer.
About Browser Hijackers
Browser hijacking is a type of unwanted program, usually a browser add-on or extension, which causes modifications in web browser’s settings. There are plenty of reasons why you might experience an internet browser hijack; however commercial, marketing, and advertising are definitely the key reasons for their creation. The idea is to force users to visit particular websites which are looking to increase their website visitor traffic and produce higher advertisement revenue. While it might appear naive, these tools were created by vicious people who always look to take full advantage of you, so that they could make money from your naive and distraction. In a much worst case, your internet browser could be hi-jacked to download malicious software that will do a lot of damage to your computer or laptop.
Key signs that your web browser has been highjacked
Symptoms that a web browser is a hi-jacked include:
1. home-page is changed
2. your internet browser is constantly being redirected to pornography sites
3. default search engine is changed
4. you’ll see multiple toolbars in your browser
5. you find numerous ads appear on your browsers or computer screen
6. your browser has instability issues or exhibits frequent errors
7. you’ve disallowed entry to particular websites, including the website of an anti-malware software developer like SafeBytes.
How does a PC get infected with a browser hijacker
Browser hijackers infect computers via malicious email attachments, downloaded infected documents or by checking out infected internet sites. They also come from add-on software, also called browser helper objects (BHO), browser plug-ins or toolbars. Other times you might have accidentally accepted a browser hijacker as part of an application package (usually freeware or shareware). A good example of a well-known browser hijacker is the latest Chinese malware known as “Fireball”, which has attacked 250 million computer systems around the world. It works as a hijacker but can be changed into a full-functioning malware downloader afterward.
The presence of any browser hijacker malware on your computer might considerably diminish the web browsing experience, monitor your online activities that result in major privacy issues, create system stability issues and eventually cause your computer to slow down or to a practically unusable condition.
Browser hijacker removal
The one thing you can try to get rid of a browser hijacker is to find the malicious software inside the “Add or Remove Programs” list in the Microsoft Windows Control Panel. It may or may not be there. If it is, try and uninstall it. However, many browser hijackers are hard to get rid of manually. No matter how much you attempt to remove it, it may keep coming back again and again. Besides, browser hijackers could modify Windows registry so it could be very difficult to restore all the values manually, particularly when you’re not very tech-savvy individual.
You might opt for automatic browser hijacker removal by just installing and running a reliable anti-malware application. To eradicate any type of browser hijacker from your personal computer, you should download the following professional malware removal tool – SafeBytes Anti-Malware. Together with the anti-malware tool, a PC optimizer, such as SafeBytes Total System Care, will help you in removing all related files and modifications in the Windows registry automatically.
Learn How to Remove a Virus that is Blocking Websites or Preventing Downloads
Malware could potentially cause all sorts of damage after they invade your computer, from stealing your personal information to deleting data files on your PC. Certain malware types modify web browser settings by adding a proxy server or modify the PC’s DNS configurations. In these instances, you will be unable to visit some or all of the sites, and therefore unable to download or install the necessary security software to remove the computer virus. If you are reading this article right now, you might have probably recognized that a malware infection is a reason behind your blocked web traffic. So what to do if you need to download and install an anti-malware application like Safebytes? There are a few steps you can take to circumvent this issue.
Boot your PC in Safe Mode
If the virus is set to run automatically when Microsoft Windows starts, stepping into Safe Mode may block the attempt. Just bare minimum required applications and services are loaded when you boot your computer into Safe Mode. To launch your Windows XP, Vista, or 7 computers in Safe Mode with Networking, follow the instructions below.
1) At power on, hit the F8 key before the Windows splash screen starts to load. This should bring up the Advanced Boot Options menu.
2) Make use of the arrow keys to choose Safe Mode with Networking and hit ENTER.
3) When you are into this mode, you should have online access once again. Now, utilize your browser normally and navigate to https://safebytes.com/products/anti-malware/ to download and install Safebytes Anti-Malware.
4) After installation, do a full scan and let the software program delete the threats it discovers.
Download the security program using an alternate browser
Some malware may target vulnerabilities of a specific browser that block the downloading process. If you are not able to download the anti-malware software program using Internet Explorer, this means the virus may be targeting IE’s vulnerabilities. Here, you should switch over to an alternative internet browser such as Chrome or Firefox to download the Safebytes program.
Make a bootable USB antivirus drive
Another option would be to make a portable antivirus program on your USB stick. Try these simple actions to clean up your affected PC using portable anti-malware.
1) On a virus-free PC, install Safebytes Anti-Malware.
2) Put the pen drive into the clean computer.
3) Double-click on the downloaded file to run the installation wizard.
4) When asked, choose the location of the pen drive as the place where you want to store the software files. Follow the instructions on the computer screen to finish up the installation process.
5) Now, plug the pen drive into the corrupted PC.
6) Double-click the EXE file to open the Safebytes tool right from the thumb drive.
7) Hit the “Scan Now” button to begin the malware scan.
Features and Benefits of SafeBytes Anti-Malware
Would you like to install the very best anti-malware program for your computer? There are various applications in the market that comes in paid and free versions for Windows computers. A few of them are good but there are numerous scamware applications that pretend as genuine anti-malware software waiting to wreak havoc on your computer. You should pick a product that has gained a strong reputation and detects not just computer viruses but other kinds of malware too. While thinking about reliable programs, Safebytes Anti-Malware is certainly the highly recommended one.
SafeBytes anti-malware is a trusted software that not only protects your computer completely but is also very easy to use for people of all ability levels. Using its outstanding protection system, this utility will instantly detect and remove the majority of the security threats, including browser hijackers, viruses, adware, ransomware, trojans, worms, and PUPs.
There are numerous amazing features you’ll get with this security product. Listed below are some of the highlighted features included in the application.
Active Protection: SafeBytes gives real-time active checking and protection against all known viruses and malware. They’re highly efficient in screening and eliminating various threats because they’re regularly revised with the latest updates and safety measures.
Best AntiMalware Protection: Safebytes is made on the best virus engine within the industry. These engines will detect and remove threats even during the early stages of a malware outbreak.
Safe Web Browsing: Safebytes allots all sites a unique safety ranking that helps you to have an idea of whether the webpage you’re going to visit is safe to browse or known to be a phishing site.
Light-weight: SafeBytes is renowned for its minimal influence on computer resources and great detection rate of various threats. It works silently and efficiently in the background so you are free to utilize your computer at full power all of the time.
24/7 Customer Support: Support service is accessible 24 x 7 x 365 days via email and chats to answer your questions.
To sum it up, SafeBytes Anti-Malware is really great for securing your laptop or computer against all sorts of malware threats. There is no doubt that your PC will be protected in real-time once you put this software program to use. So if you’re searching for the very best malware removal tool out there, and when you don’t mind shelling out some dollars for it, opt for SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
To remove Action Classic Games manually, go to the Add or Remove programs list in the Windows Control Panel and select the program you want to get rid of. For web browser plug-ins, go to your web browser’s Addon/Extension manager and select the plug-in you intend to disable or remove. Additionally, it is advised to factory reset your web browser settings to their default state.
To be certain of complete removal, find the following Windows registry entries on your system and remove it or reset the values accordingly. Please keep in mind that only advanced users should try to manually edit the registry because removing any single vital system file results in a major problem or even a system crash. Moreover, some malware keeps replicating which makes it tough to get rid of. Doing this malware-removal process in Safe Mode is suggested.
Files:
%LOCALAPPDATA%\Action Classic GamesTooltab
%UserProfile%\Local Settings\Application Data\Action Classic GamesTooltab
%LOCALAPPDATA%\Google\Chrome\User Data\Default\Extensions\dbkmigdeafonnkpjndllhadgclnkamdm
%UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\Default\Extensions\dbkmigdeafonnkpjndllhadgclnkamdm
%PROGRAMFILES(x86)%\ActionClassicGames_e1
%PROGRAMFILES%\ActionClassicGames_e1
%USERPROFILE%\Application Data\ActionClassicGames_e1
%USERPROFILE%\AppData\LocalLow\ActionClassicGames_e1
%UserProfile%\Local Settings\Application Data\ActionClassicGames_e1
Registry:
HKEY_CURRENT_USER\Software\AppDataLow\Software\ActionClassicGames_e1
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\4f521f8c-b472-4fad-be00-340c2803ed56
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\6ff6226a-4c91-44e5-b2cb-93c96033f842
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\8fed6e71-aaf0-4fd9-a25d-ccd01216caef
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\f134110e-125c-4df0-a36f-e29d6dc48bf8
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\3e8810b8-21bc-4567-9d53-21a575f0aa4e
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\4f521f8c-b472-4fad-be00-340c2803ed56
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\6ff6226a-4c91-44e5-b2cb-93c96033f842
HKEY_CURRENT_USER\Software\Action Classic Games



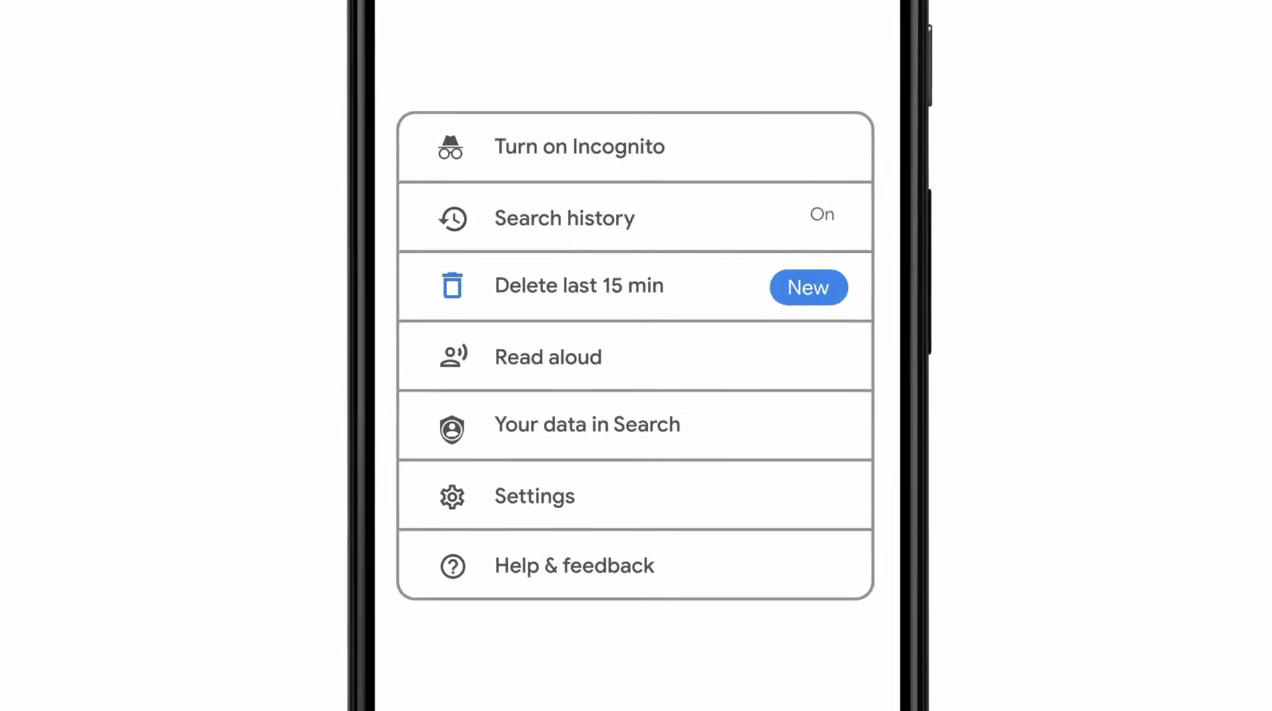 As previously announced by Google feature to quickly delete the last 15min of browsing history via one button is rolling out now.
For now, only Apple users will be available to use this feature but the Android update is scheduled for later this year, a strange move by Google but it is what it is.
For anyone who is unfamiliar with this feature, basically, Google wants a quick way to remove the last 15min of browsing history as a supposedly stated request to make deleting browsing history much easier.
Google came up with this idea so you can keep the previous history intact but remove just 15min time frame, no additional explanation was given on why 15 but I presume it is some round number that came up as the middle one with research, read telemetry info.
Using quick delete requires being signed into Search with a Google account. Users can access the option by simply tapping on the avatar icon to access the settings then choosing "Delete last 15 minutes."
As previously announced by Google feature to quickly delete the last 15min of browsing history via one button is rolling out now.
For now, only Apple users will be available to use this feature but the Android update is scheduled for later this year, a strange move by Google but it is what it is.
For anyone who is unfamiliar with this feature, basically, Google wants a quick way to remove the last 15min of browsing history as a supposedly stated request to make deleting browsing history much easier.
Google came up with this idea so you can keep the previous history intact but remove just 15min time frame, no additional explanation was given on why 15 but I presume it is some round number that came up as the middle one with research, read telemetry info.
Using quick delete requires being signed into Search with a Google account. Users can access the option by simply tapping on the avatar icon to access the settings then choosing "Delete last 15 minutes."