HPQTRA08.exe - What is it?
HPQTRA08.exe (Hewlett Packard Tray 08) is the Hewlett Packard Digital Imaging Monitor task. It is installed with the drivers of HP imaging products like PhotoSmart Printers.
It incessantly monitors and indicates the connectivity status with any recognizable HP product.
Simply put, HPQTRA08.exe is an exe (executable) file that contains step-by-step instructions that a computer follows to carry out a function.
HPQTRA08.exe error code is displayed in any of the following formats:
- "Hpqtra08.exe Application Error."
- "Cannot find hpqtra08.exe."
- "Hpqtra08.exe not found."
- "Error starting program: hpqtra08.exe."
- "Hpqtra08.exe is not a valid Win32 application."
- "Hpqtra08.exe failed."
- "Faulting Application Path: hpqtra08.exe."
- "Hpqtra08.exe has encountered a problem and needs to close. We are sorry for the inconvenience."
- "Hpqtra08.exe is not running."
Solution
 Error Causes
Error Causes
Error code HPQTRA08.exe can be triggered for several reasons. However, some of the most common causes include:
- Corrupt Windows registry keys
- Virus infection
- Deleted, damaged, or corrupted HPQTRA08.exe file
- HPQTRA08.exe file conflict
- Corrupt or incomplete installation of Hp Digital Imaging
It is advisable to repair the error code HPQTRA08.exe on your PC immediately. Delays can lead to serious problems especially if the underlying cause of the error is related to registry corruption.
Further Information and Manual Repair
To resolve this error on your PC, you don’t need to hire a professional and pay hundreds of dollars for the repair. Simply try the DIY methods listed below to fix the problem right away.
Method 1 - Download and Install HPQTRA08.exe File
If the error cause is related to deleted, corrupted, or damaged HPQTRA08.exe file, then the best way to fix the problem is to install the HPQTRA08.exe file on your PC.
However, first, make sure the site you select to download the file from is reliable and trusted.
By downloading from an unreliable website you can expose your PC to potential malicious programs and risk your data security.
Method 2 - Remove all Viruses
Sometimes viruses and malware tend to disguise in the form of exe files such as the HPQTRA08.exe file.
In such a situation scan your entire PC for viruses and malware using a powerful antivirus. Remove all the malicious programs found to fix the issue.
Method 3 - Clean and Repair the Registry
The registry saves all PC-related activities and information including both important and obsolete files such as cookies, bad registry entries, invalid keys, internet history, and junk files.
If these files are not removed from the registry frequently, these accumulate in the registry and corrupt thereby triggering error codes. Error code HPQTRA08.exe is generated when the corrupt Windows registry keys are associated with the HPQTRA08.exe file.
To resolve, clean the registry and repair it. Although this can be done manually it can be time-consuming and tricky especially if you are not technically sound, therefore it is advisable to download Restoro.
Click here to download Restoro and resolve error HPQTRA08.exe.
Method 4 - Locate and Install the Driver
As was pointed out, you might need to reinstall the printer driver again. Using
DriverFIX, you’ll be able to automatically update your computer system and install the drivers your computer needs to operate smoothly.
 With its Rift model, Oculus set itself as a big player in VR. Now the company is slowly bowing out of the dedicated, tethered VR headset with its latest Quest 2 designed to primarily be a standalone headset.
In case you do not know, tethered headset means that the headset itself is connected to your PC and is using its power to drive your VR experience.
Now technical specifications of Quest 2 are pretty OK and it can drive stuff pretty decently and if you want you can purchase the dedicated cable to connect it to your PC for the full experience of games requiring more capable hardware.
Oculus Quest 2 is the cheapest headset on this list and with its stable performance, is highly recommended.
With its Rift model, Oculus set itself as a big player in VR. Now the company is slowly bowing out of the dedicated, tethered VR headset with its latest Quest 2 designed to primarily be a standalone headset.
In case you do not know, tethered headset means that the headset itself is connected to your PC and is using its power to drive your VR experience.
Now technical specifications of Quest 2 are pretty OK and it can drive stuff pretty decently and if you want you can purchase the dedicated cable to connect it to your PC for the full experience of games requiring more capable hardware.
Oculus Quest 2 is the cheapest headset on this list and with its stable performance, is highly recommended.
 Although the headset itself is nothing revolutionary or special its controllers are. They can track individual finger movements, making games (that take advantage of them) much more immersive than the standard trigger grips on other controllers.
The Index's higher refresh rate makes for smoother action, as well, which is another nice bonus. If you already have an HTC Vive or Vive Cosmos Elite, and their base stations (not the regular Cosmos), you can buy only the controllers.
Although the headset itself is nothing revolutionary or special its controllers are. They can track individual finger movements, making games (that take advantage of them) much more immersive than the standard trigger grips on other controllers.
The Index's higher refresh rate makes for smoother action, as well, which is another nice bonus. If you already have an HTC Vive or Vive Cosmos Elite, and their base stations (not the regular Cosmos), you can buy only the controllers.
 The PlayStation VR is compelling thanks to Sony backing its development, plus the PlayStation 4's affordability and availability compared with gaming PCs. All you need is the headset, a PlayStation 4, and a PlayStation Camera (now included with most PlayStation VR bundles).
Not really the best of the bunch but still one of the top ones for console gaming. Sony is working on a new PlayStation VR system for the PlayStation 5, with redesigned controllers. The new headset hasn't been revealed yet, but the company has released a preview of the new controllers.
The PlayStation VR is compelling thanks to Sony backing its development, plus the PlayStation 4's affordability and availability compared with gaming PCs. All you need is the headset, a PlayStation 4, and a PlayStation Camera (now included with most PlayStation VR bundles).
Not really the best of the bunch but still one of the top ones for console gaming. Sony is working on a new PlayStation VR system for the PlayStation 5, with redesigned controllers. The new headset hasn't been revealed yet, but the company has released a preview of the new controllers.
 HP headset is one which you get if you want the best image quality in VR headset, sadly controllers did not follow the same quality of headset itself. But this is still a pretty decent headset overall and worth the purchase.
HP headset is one which you get if you want the best image quality in VR headset, sadly controllers did not follow the same quality of headset itself. But this is still a pretty decent headset overall and worth the purchase.
 HTC's Vive Cosmos is the upgraded version of the Vive. It features a higher resolution and replaces the external base stations with outward-facing cameras for motion tracking. It's a comprehensive package for whole-room VR.
HTC recently released the Vive Pro 2, a high-end VR headset targeting both enterprise users and consumers. This new headset features a 2,448-by-2,448 resolution display for each eye, making it the highest-resolution headset currently available. It's also more expensive than the Cosmos Elite.
Sadly one thing that is bringing this headset down is the price.
HTC's Vive Cosmos is the upgraded version of the Vive. It features a higher resolution and replaces the external base stations with outward-facing cameras for motion tracking. It's a comprehensive package for whole-room VR.
HTC recently released the Vive Pro 2, a high-end VR headset targeting both enterprise users and consumers. This new headset features a 2,448-by-2,448 resolution display for each eye, making it the highest-resolution headset currently available. It's also more expensive than the Cosmos Elite.
Sadly one thing that is bringing this headset down is the price.  The application settings screen will open, in upper tabs locate Compatibility and left-click on it.
The application settings screen will open, in upper tabs locate Compatibility and left-click on it. After the click, you will find yourself in application compatibility settings.
After the click, you will find yourself in application compatibility settings.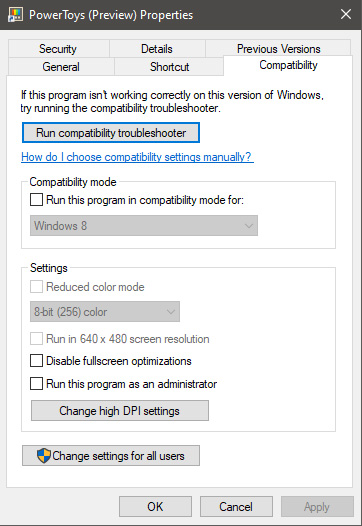 In this window, you will face different options to run the chosen application in various modes in order to make it run. How settings are self-explanatory and different applications will need different settings sadly we can not cover them all but your safest bet is to run them in an environment where they have worked.
In this window, you will face different options to run the chosen application in various modes in order to make it run. How settings are self-explanatory and different applications will need different settings sadly we can not cover them all but your safest bet is to run them in an environment where they have worked.


