Microsoft Visual C++ Runtime Library Error
Fix Microsoft Visual C++ Runtime Library Error, Microsoft Windows operating system supports a form of shared libraries that are known as DLL (Dynamic-link libraries). These are also known as code libraries that are used by multiple processes while one copy is loaded into memory.
Runtimes are also code libraries that are loaded by applications when the application is called to run on the system. The most common runtime libraries that are used today are Visual C++ Runtime Library and Java Runtime Environment.
These libraries are practically used for nearly every single application you run on your system. Therefore it is very important that these libraries are in good working order.
Microsoft Visual C++ Runtime Library Error occurs when this runtime library becomes corrupted.
When Microsoft Visual C++ Runtime Library Error occurs, the applications powered by this runtime library fail to run smoothly, resulting in locking you out of those applications and hampering your ability to work on them.
Generally speaking, this error indicates system instability and poor PC maintenance. If this error is not fixed timely it can expose your system to serious PC damages like system freeze, crashes, and data loss.
Solution
 Error Causes
Error Causes
Microsoft Visual C++ Runtime Library Error is triggered for numerous reasons. These include:
- Poor program installation
- Disk fragmentation
- Missing and damaged .dll files
- Registry corruption
- Malware invasion
In a nutshell, it can be said that the deep-rooted cause of the Microsoft Visual C++ Runtime Library Error is the registry. All the causes listed above are associated with the registry.
For simplification, the registry is the main database of your system that stores all the activities executed on the computer in the RAM, the hard disk.
This includes both the important data and junk files such as temporary files, internet history, bad registry keys, invalid registry entries, and also the files from the uninstalled programs.
If these files are not removed from the registry frequently, it overloads the hard disk and leads to obscure error message displays on your system like the Microsoft Visual C++ Runtime Library Error as warning signs.
Sometimes, rebooting the system may fix the Microsoft Visual C++ Runtime Library Error. However, this is temporary. Error message pops again after some time. So, instead of seeking out a temporary solution, it is advisable to look for a solution that can repair this error for the longest time.
Further Information and Manual Repair
There are two ways to fix the Microsoft Visual C++ Runtime Library Error code. One is to reinstall the Visual C++ runtime libraries. This can be a complex task if you are not a computer programmer or technically sound.
However, the second way, or let’s just say the best and easiest way to resolve this problem is to download Restoro.
This is truly an easy way as it requires no technical expertise or programming knowledge to repair the Microsoft Visual C++ Runtime Library Error.
Restoro is an advanced, user-friendly, and multi-functional repair tool integrated with profound powerful utilities like an intuitive registry cleaner, system stability scanner, and anti-virus.
It has a smooth interface, easy navigation, and a simple layout making it easy for users and even novices to operate it to resolve the Microsoft Visual C++ Error in seconds.
The registry cleaner scans your entire PC for registry issues. It wipes out all the invalid, unnecessary, and obsolete files clearing up your disk space. In addition to this, it repairs fragmented disks, damaged .dll files (runtime code library), and repairs the registry.
Along with these benefits, Restoro also functions as a system optimizer thus boosting the performance of your system. It can be downloaded by all PC Windows users as it is compatible with all Windows versions.
Click here to download Restoro on your PC to resolve the Microsoft Visual C++ Runtime Library Error code and to ensure optimum PC performance and health.
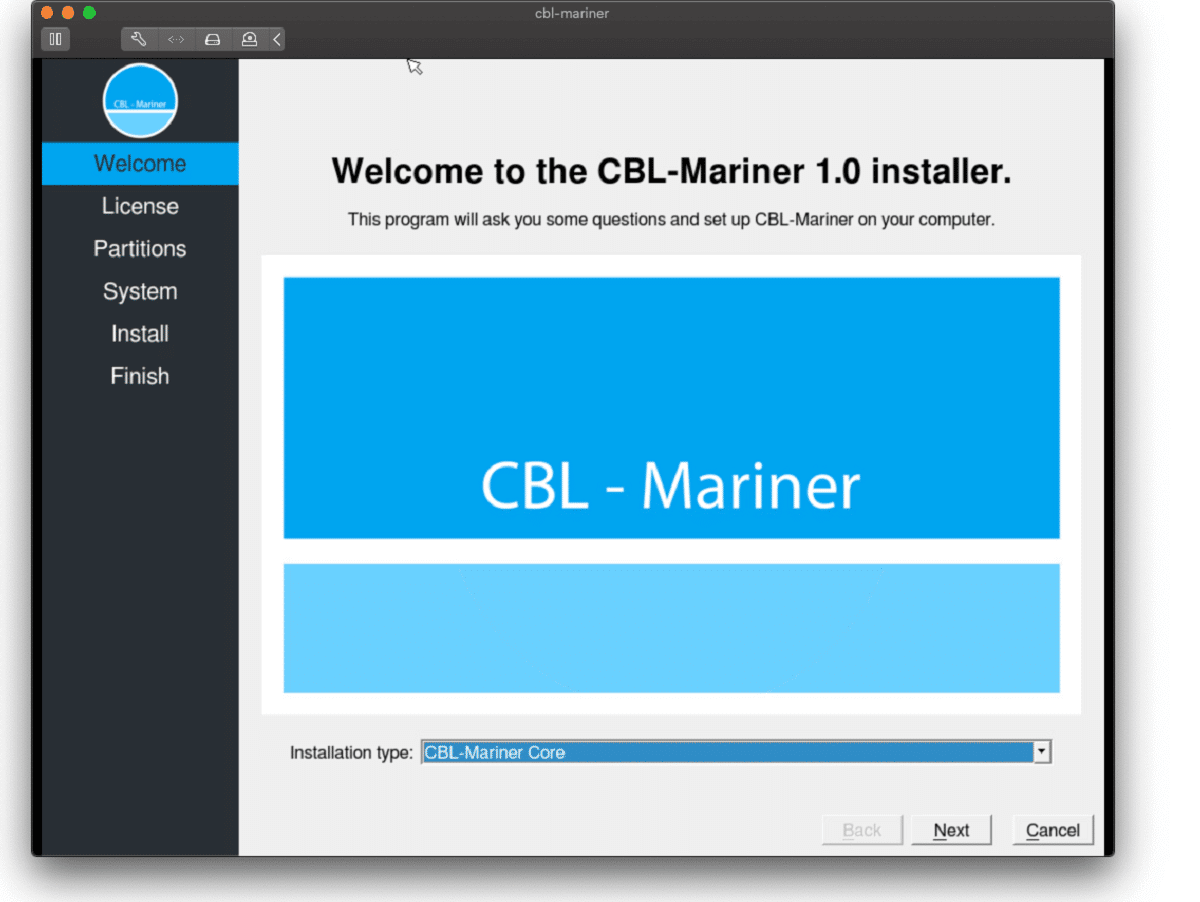 Well if anyone told me just a few years ago that I will see the day when Microsoft releases a new OS based on Linux I would be very amused, but that day has come. Mariner is the newest OS out of nowhere.
Microsoft’s new Linux Distro, dubbed Common Base Linux (CBL)-Mariner, isn’t the type of distro you’d want to install directly on any old machine. It’s primarily meant for cloud infrastructure and edge products. Specifically Microsoft’s Cloud and Edge products.
But if you are curious, it’s possible to run. Juan Manuel Rey, a Microsoft Senior Program Manager for Azure VMware, recently published a guide to ISO CBL-Mariner image. With that, you can easily get it up and running. And you can build CBL-Mariner on an Ubuntu 18.04 desktop. So you can try it out since it is free.
You can get it from here: https://github.com/microsoft/CBL-Mariner
It is obvious that Microsoft aims to set itself as a leader in enterprise server environments with this move and it is very likely that it may succeed or at least give a good shake to its competitors, mainly red hat and Suse which are two dominant distros in that field.
Many believe that they can win over by providing regular updates and package delivery via their already established system and that feature could be a turning point for some.
In any case, time will tell and we shall see.
Well if anyone told me just a few years ago that I will see the day when Microsoft releases a new OS based on Linux I would be very amused, but that day has come. Mariner is the newest OS out of nowhere.
Microsoft’s new Linux Distro, dubbed Common Base Linux (CBL)-Mariner, isn’t the type of distro you’d want to install directly on any old machine. It’s primarily meant for cloud infrastructure and edge products. Specifically Microsoft’s Cloud and Edge products.
But if you are curious, it’s possible to run. Juan Manuel Rey, a Microsoft Senior Program Manager for Azure VMware, recently published a guide to ISO CBL-Mariner image. With that, you can easily get it up and running. And you can build CBL-Mariner on an Ubuntu 18.04 desktop. So you can try it out since it is free.
You can get it from here: https://github.com/microsoft/CBL-Mariner
It is obvious that Microsoft aims to set itself as a leader in enterprise server environments with this move and it is very likely that it may succeed or at least give a good shake to its competitors, mainly red hat and Suse which are two dominant distros in that field.
Many believe that they can win over by providing regular updates and package delivery via their already established system and that feature could be a turning point for some.
In any case, time will tell and we shall see. 

 Microsoft has not published a solution to this issue, but users point out two potential problems. The first is a security mechanism based on disk virtualization, which is supposed to slow down the performance of SSDs.
The second, in turn, is related to the place of installation of Windows 11 – users indicate that if the performance test is performed on a medium with no files associated with the system, its performance results are similar to the parameters given by the manufacturer.
Transfer speeds were to be slightly improved with the latest Windows 11 update 22000.348. However, users are still waiting for a solution to the problem that significantly reduces the efficiency of SSD media.
Microsoft has not published a solution to this issue, but users point out two potential problems. The first is a security mechanism based on disk virtualization, which is supposed to slow down the performance of SSDs.
The second, in turn, is related to the place of installation of Windows 11 – users indicate that if the performance test is performed on a medium with no files associated with the system, its performance results are similar to the parameters given by the manufacturer.
Transfer speeds were to be slightly improved with the latest Windows 11 update 22000.348. However, users are still waiting for a solution to the problem that significantly reduces the efficiency of SSD media.
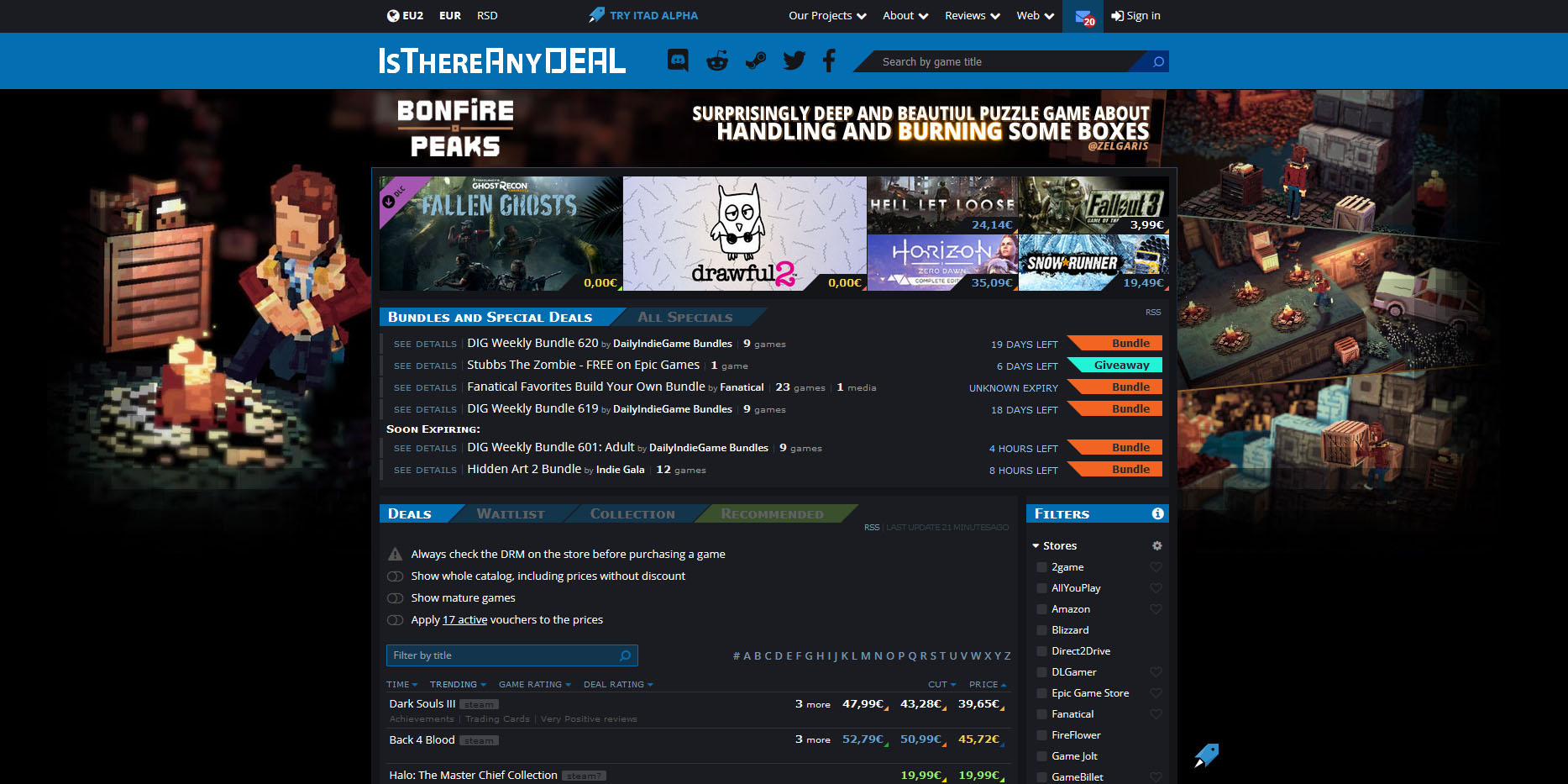 Is There Any Deal
Is There Any Deal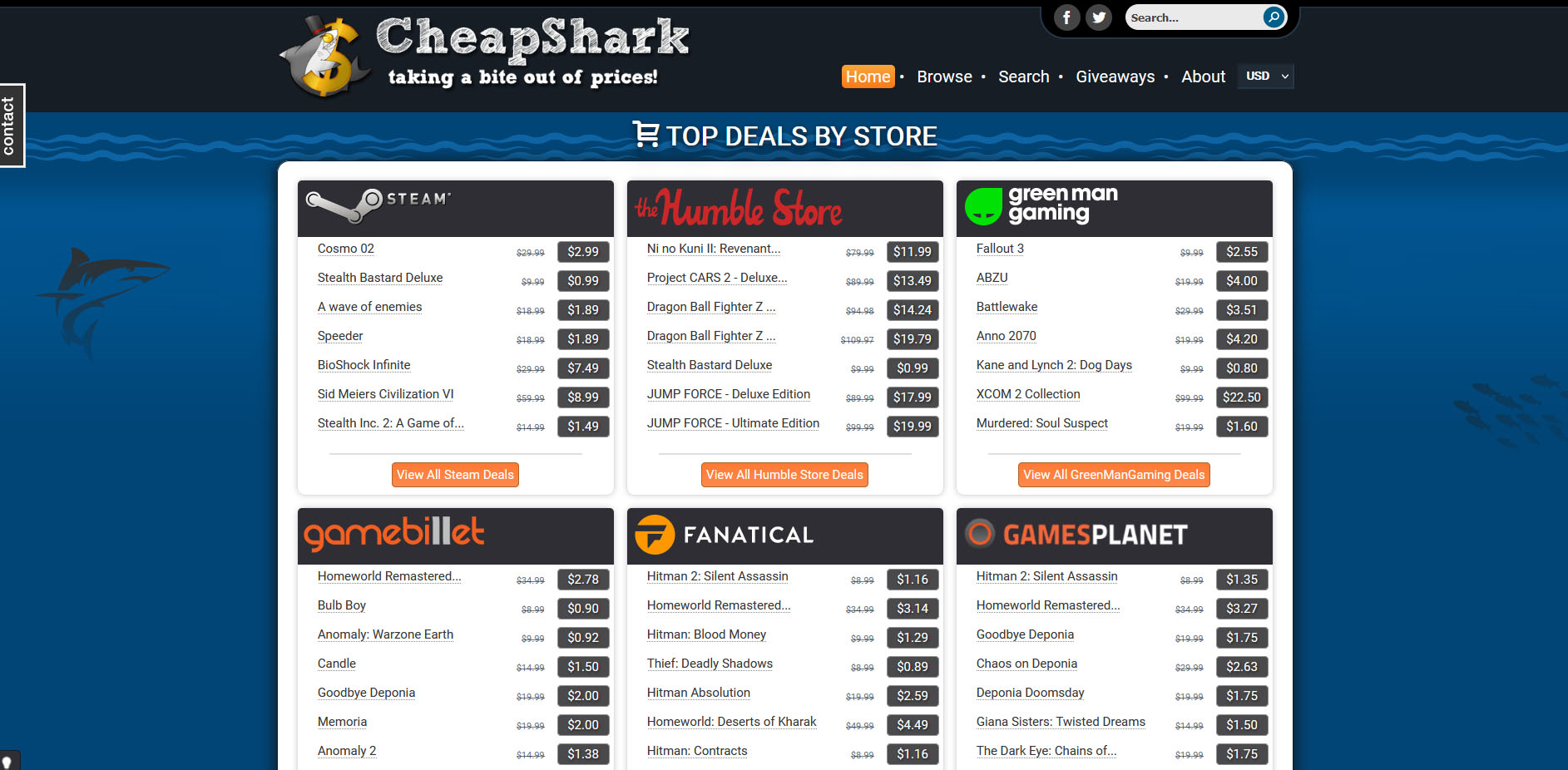 Cheap Shark
Cheap Shark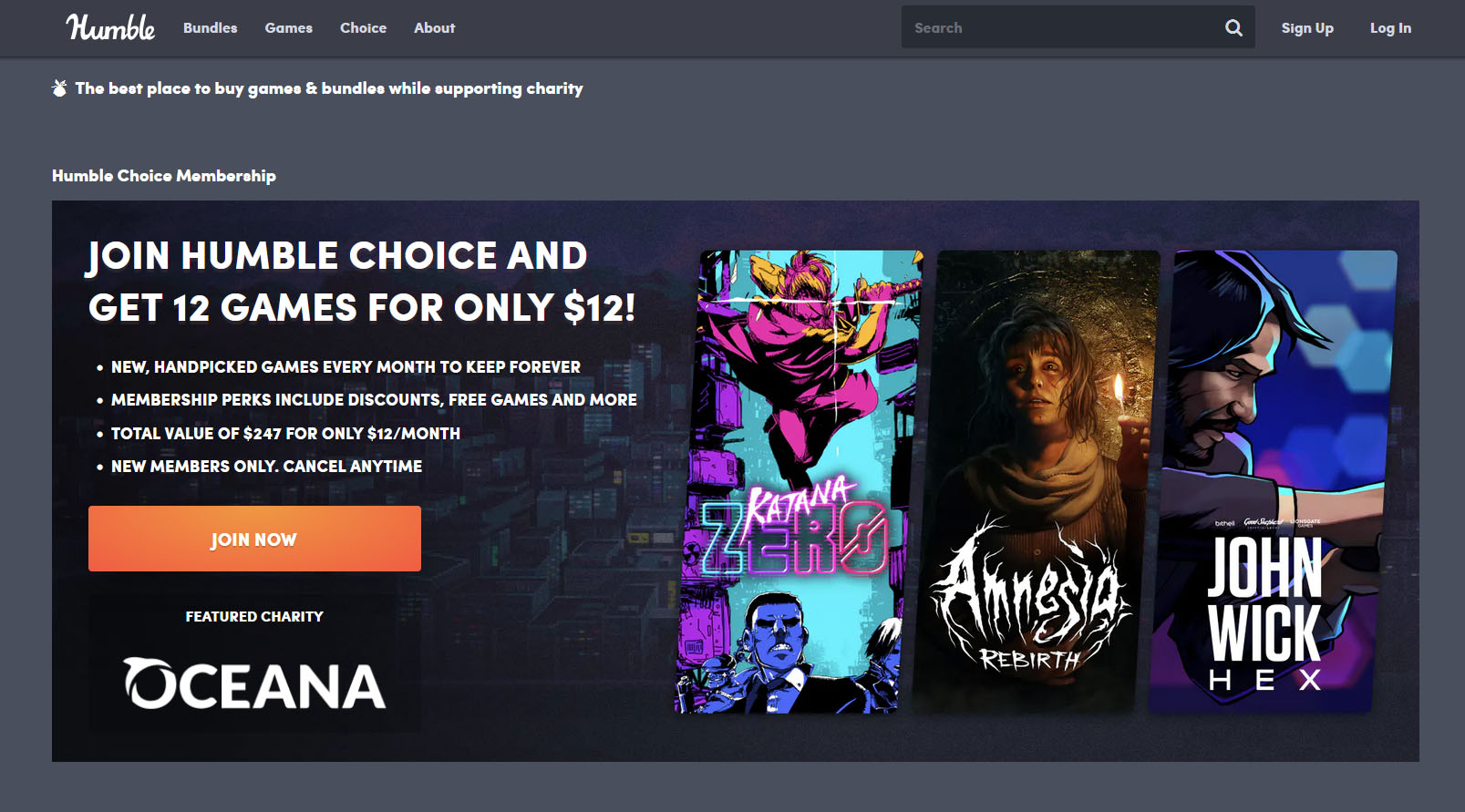 Humble Bundle
Humble Bundle Fanatical
Fanatical Slick Deals
Slick Deals Green Man Gaming
Green Man Gaming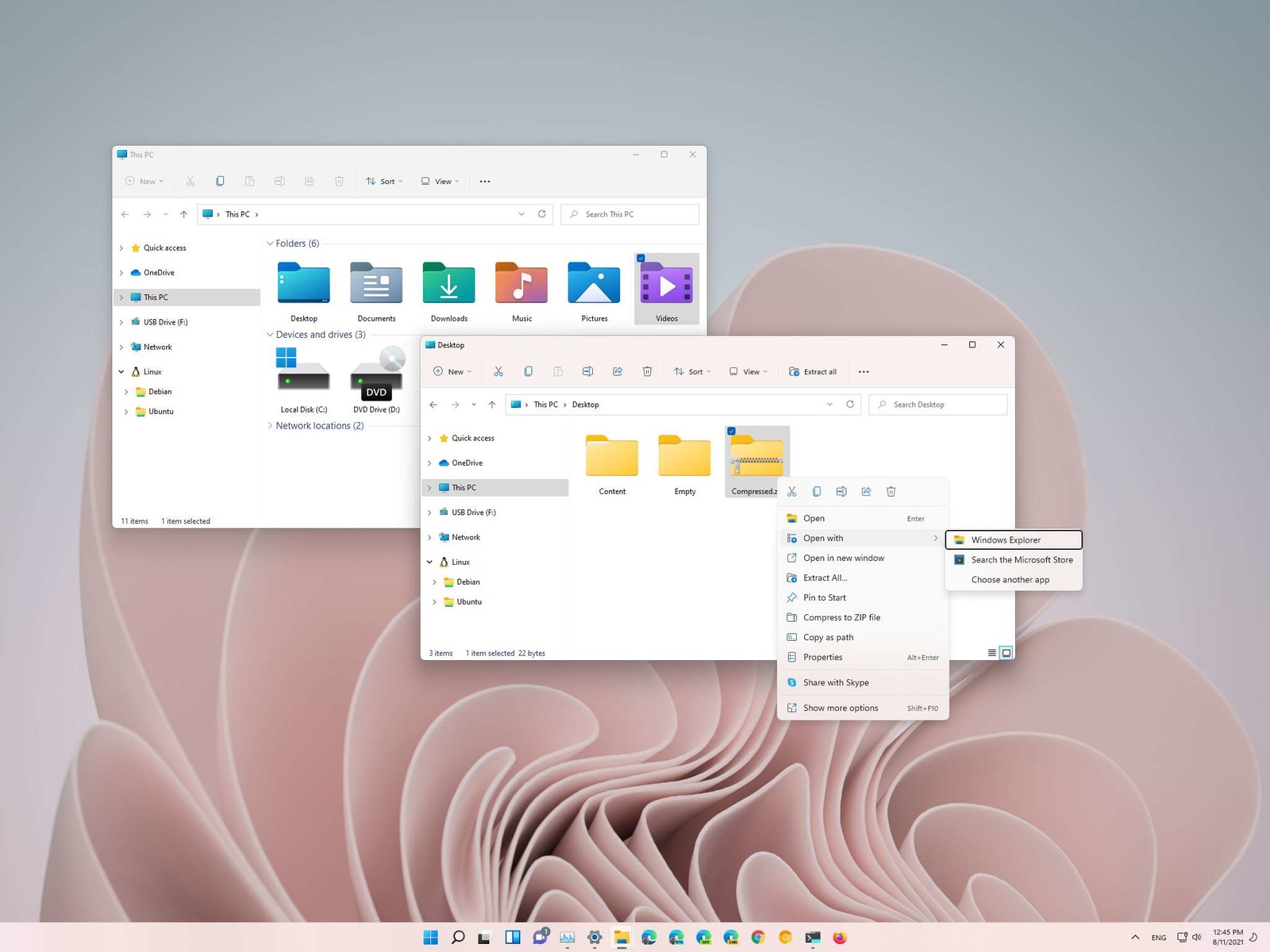 How this is the case we have decided to put a little tutorial on how to accomplish this very task and run file explorer with administrator privileges.
How this is the case we have decided to put a little tutorial on how to accomplish this very task and run file explorer with administrator privileges.

