EasyDocMerge Toolbar is a Browser Hijacker for Google Chrome. Usually, such browser extensions are installed without your knowledge. These types of Browser Hijackers are often the cause of many problems while surfing the Internet. The most common problems are unwanted pop-ups, underlined words, additional ads, sponsored links, to generate web traffic and earn revenue of the advertising networks by gathering the users browsing data and sending it back to the Mindspark ads network.
When installed this extension will hijack your home page setting it to MyWay.com, it will also change your new tab page to EasyDocMerge (Powered by MyWay.com Search).
About Browser Hijackers
Browser hijacking is a form of an unwanted program, commonly a web browser add-on or extension, which then causes modifications in the browser’s settings. Browser hijacker malware is developed for a variety of reasons. It redirects you to the sponsored internet sites and inserts adverts on your browser that assist its creator to generate earnings. A lot of people think that the browser hijacker is only a harmless website but that is not the case. Nearly every browser hijacker poses an existent threat to your online safety and it’s important to classify them under privacy dangers. They don’t just mess up your browsers, but browser hijackers can even modify the computer registry, leaving your computer susceptible to various other types of attacks.
Key symptoms that your web browser has been hijacked
There are various signs of web browser hijacking: the home page of the web browser is changed unexpectedly; new bookmarks pointing to porn websites are added to your favorite pages; the essential web browser settings are modified and unwanted or insecure resources are added to the trusted sites list; you’ll see many toolbars on your web browser; you see a lot of pop-up ads on your computer screen; your web browser has become unstable or starts running sluggishly; Inability to navigate to particular sites, particularly anti-malware and other computer security software sites.
How they infect computers
Browser hijackers infect computer systems by numerous means, including via a file-share, a drive-by download, or an infected e-mail attachment. They can also originate from any BHO, extension, add-on, toolbar, or plug-in with malicious intent. A browser hijacker may also come bundled up with some free software that you unintentionally download to your computer, compromising your internet security. Typical examples of browser hijackers include CoolWebSearch, Conduit, Coupon Server, OneWebSearch, RocketTab, Searchult.com, Snap.do, and Delta Search.
Browser hijackers may record user keystrokes to gather potentially important information that leads to privacy issues, cause instability on computers, drastically disrupt user’s browsing experience, and finally slow down the system to a point where it will become unusable.
Removal
Certain browser hijacking could be simply reversed by discovering and eliminating the corresponding malware software from your control panel. In some cases, it can be a difficult job to identify and eliminate the malicious component because the associated file might be running as part of the operating system process. You should consider carrying out manual fixes only if you are a tech-savvy person, as potential risks are associated with tinkering with the system registry and HOSTS file.
Installing and running antivirus programs on the affected computer could automatically erase browser hijackers and other malicious applications. Safebytes Anti-Malware contains a state-of-the-art anti-malware engine to help you prevent browser hijacking in the first place, and clean up any pre-existing issues
What you can do if Virus Prevents You From Downloading Or Installing Anything?
Practically all malware is bad, but certain kinds of malware do a lot more damage to your computer than others. Some malware sits in between your computer and the internet connection and blocks a few or all internet sites that you would like to visit. It will also prevent you from adding anything to your PC, especially antivirus software. If you’re reading this now, you might have probably recognized that a malware infection is the real cause of your blocked web connectivity. So how to proceed if you need to install an antivirus application such as Safebytes? Although this kind of problem can be difficult to get around, there are a few steps you can take.
Eliminate viruses in Safe Mode
If any virus is set to run automatically when Microsoft Windows starts, stepping into Safe Mode could block this attempt. Only minimal required programs and services are loaded when you boot your laptop or computer in Safe Mode. You will need to do the following to eliminate malware in Safe mode.
1) At power on/start-up, hit the F8 key in 1-second intervals. This should bring up the Advanced Boot Options menu.
2) Select Safe Mode with Networking using arrow keys and press ENTER.
3) When this mode loads, you should have the internet. Now, utilize your browser normally and navigate to https://safebytes.com/products/anti-malware/ to download and install Safebytes Anti-Malware.
4) Once the software is installed, allow the diagnostic scan to run to eliminate viruses and other threats automatically.
Obtain the security program using an alternate web browser
Some malware might target vulnerabilities of a specific web browser that obstruct the downloading process. The best way to avoid this problem is to pick a web browser that is renowned for its security features. Firefox has built-in Phishing and Malware Protection to help keep you secure online.
Run anti-malware from your USB drive
To effectively get rid of the malware, you need to approach the problem of running antivirus software on the infected computer from a different angle. Abide by these steps to run the anti-virus on the affected computer.
1) On a virus-free PC, download and install Safebytes Anti-Malware.
2) Plug the Flash drive into the clean computer.
3) Double-click the Setup icon of the antivirus program to run the Installation Wizard.
4) Choose the flash drive as the destination for saving the file. Follow the on-screen instructions to finish the installation process.
5) Remove the pen drive. You can now utilize this portable anti-virus on the infected computer system.
6) Double-click the antivirus program EXE file on the USB flash drive.
7) Simply click “Scan Now” to run a complete scan on the affected computer for viruses.
Protect Your Computer Against Viruses and Malware With SafeBytes Security Suite
Today an anti-malware program can protect your laptop or computer from different types of internet threats. But how to select the best one amongst countless malware protection software that is available out there? As you might be aware, there are several anti-malware companies and tools for you to consider. A few are really worth your money, but many aren’t. You need to choose one that is dependable, practical, and has a strong reputation for its malware source protection. Among few good applications, SafeBytes Anti-Malware is the strongly recommended software program for the security-conscious user.
SafeBytes anti-malware is a powerful, highly effective protection application made to help end-users of all levels of computer literacy in detecting and removing harmful threats from their computer. After you have installed this software, SafeByte's sophisticated protection system will ensure that no viruses or malicious software can seep through your personal computer.
SafeBytes has fantastic features when compared to various other anti-malware programs. Listed below are some of the great features included in the software.
Real-time Active Protection: SafeBytes gives you round-the-clock protection for your personal computer limiting malware intrusions instantly. It will examine your PC for suspicious activity at all times and safeguards your PC from illegal access.
Antimalware Protection: Safebytes is made on the best virus engine in the industry. These engines can identify and get rid of threats even during the initial phases of a malware outbreak.
“Fast Scan” Features: SafeBytes’s high-speed malware scanning engine minimizes scanning times and extends the life of the battery. Simultaneously, it will effectively find and get rid of infected files or any internet threat.
Web Protection: SafeBytes checks and gives a unique safety rating to every website you visit and block access to webpages known to be phishing sites, thus protecting you against identity theft, or known to contain malicious software.
Low CPU Usage: SafeBytes is a lightweight application. It consumes an extremely small amount of processing power as it runs in the background so you are free to use your Windows-based computer the way you want.
24/7 Premium Support: Professional technicians are at your disposal 24/7! They will immediately fix any technical issues you may be encountering with your security software.
Simply put, SafeBytes has formulated a meaningful anti-malware solution that is aimed to protect your computer against various malware. Malware trouble will become a thing of the past once you put this software to use. For top protection and the best value for money, you can’t get better than SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
If you want to manually remove EasyDocMerge without using an automated tool, it may be possible to do so by removing the application from the Microsoft Windows Add/Remove Programs menu, or in cases of browser plug-ins, going to the browsers AddOn/Extension manager and removing it. You’ll likely also want to totally reset your browser to its default configuration settings.
To be certain of complete removal, find the following registry entries on your computer and remove them or reset the values appropriately. However, this is a tricky task and only computer experts can perform it safely. Moreover, some malicious programs are capable to defend against its removal. It is highly recommended that you do the removal process in Windows Safe Mode.
Files:
%UserProfile%\Local Settings\Application Data\EasyDocMergeTooltab
%LOCALAPPDATA%\Google\Chrome\User Data\Default\Extensions\mabloidgodmbnmnhoenmhlcjkfelomgp
%UserProfile%\Local Settings\Application Data\Google\Chrome\User Data\Default\Extensions\mabloidgodmbnmnhoenmhlcjkfelomgp
%PROGRAMFILES(x86)%\EasyDocMerge_ex
%PROGRAMFILES%\EasyDocMerge_ex
%USERPROFILE%\Application Data\EasyDocMerge_ex
%USERPROFILE%\AppData\LocalLow\EasyDocMerge_ex
%UserProfile%\Local Settings\Application Data\EasyDocMerge_ex
Registry:
HKEY_CURRENT_USER\Software\AppDataLow\Software\EasyDocMerge_ex
HKEY_CURRENT_USER\Software\EasyDocMerge_ex
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\5e3ee57e-7d53-458f-a124-16aab06de2d6
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\64366ff9-336f-4002-a665-406a1d259cd3
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\87008eb3-6282-4075-9889-62f381451926
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\96107269-cd2e-4175-a61a-5c2e8540e8a5
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\2741d16e-6298-4345-8988-7979ffd45266
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\5e3ee57e-7d53-458f-a124-16aab06de2d6
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\64366ff9-336f-4002-a665-406a1d259cd3
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\87008eb3-6282-4075-9889-62f381451926
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\DOMStorage\easydocmerge.dl.tb.ask.com
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\SearchScopes\8bf0dd5e-ea06-48db-97a4-df286e054079
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Approved Extensions, value: 389672DB-CD13-4CF2-AED1-3170BC0DD6EC
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Internet Explorer\SearchScopes\8bf0dd5e-ea06-48db-97a4-df286e054079
HKEY_CURRENT_USER\Software\EasyDocMerge
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\LowRegistry\DOMStorage\easydocmerge.dl.myway.com
 Error Causes
Error Causes
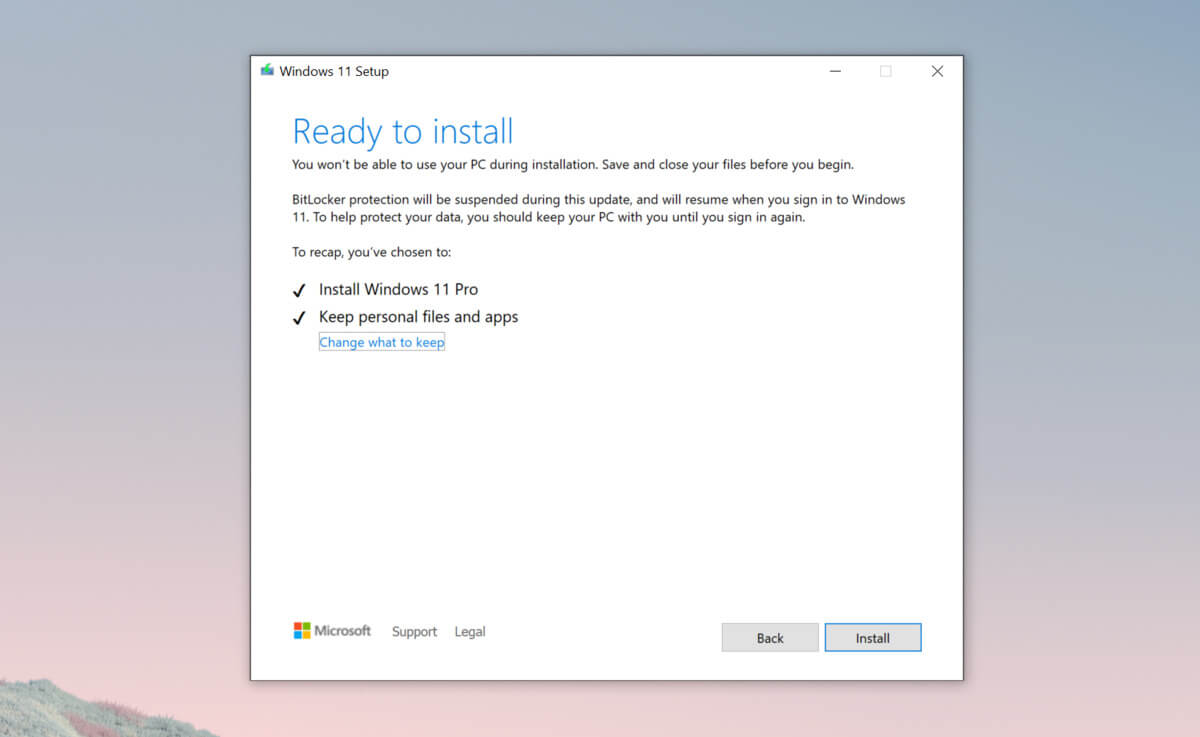 Bypass TPM with changing installation media
Bypass TPM with changing installation media