Error Code 0x80073afc - What is it?
Error code 0x80073afc deals with an antivirus program first built into Windows 8/8.1 This error occurs when Windows Defender, the built-in anti-virus software in Windows 8/8.1 and higher, does not start automatically and users attempt to manually start the program. During the initialization period of the program start-up, something goes wrong and users get a 0x80073afc Error message. The error message states there was a problem with the initialization of the program. Windows Defender provides protection of your computer and it is advised by the Microsoft Corporation that you ensure it starts up automatically on every start-up.
Solution
 Further Information and Manual Repair
Further Information and Manual Repair
Users have found several manual repairs that have fixed the problem without needing to contact technicians for extra help. While the methods below should solve your problem easily, if this is the first time you have encountered the issue you may want to do a simple restart. This has fixed the problem for some users and is the easiest first troubleshooting move. If it doesn’t work move on to the methods listed below, which are easily completed without extra help.
Before trying any of these methods, please make sure that you are logged into a profile that is listed as the administrator of the computer of his administrative powers enabled. If this is not the case you will not be able to complete the following methods. Please log out and log back in on the administrator profile.
Method 1:
First, check to see if you have a third-party anti-virus program installed on your computer. Some users believe that the built-in Windows Defender program is not powerful enough to handle the safety of their computer so they usually download a third-party program. However, that program may have caused a conflict with Windows Defender and may not allow it to open. If you do have a third-party program installed, try uninstalling it then manually starting Windows Defender.
Method 2:
If method one does not work, you may be infected by malware or a virus that has tampered with the settings on your computer and will not allow Windows Defender to start automatically or manually.
First, open Run by holding the “Win” key and pressing the “R” key. Then type “Regedit”. The program will ask for permission to follow through with this action. Click on “Yes” and the Open Registry Editor will open.
Find the HKEY_LOCAL_MACHINESoftwareMicrosoftWindows NTCurrentVersionImage File Execution Option and check to see if there are any files similar to MSASCui.exe or MpCmdRun.exe. If there are any file entries that resemble that, you will want to right-click on them before selecting the “Delete” option. If you do not see any entries that match, this is not the issue with your Windows Defender and you will want to try another method.
The Registry on your computer is very important. It helps tell your computer what programs are safe to run, what programs should be run, and what programs should not be run. If it is tampered with by a virus or Malware, multiple system operations can be affected.
However, if you did find similar file names, and you deleted them, try to start Windows Defender manually. If it does not work again, move on to the next method.
Method 3:
If the first two methods do not work for your issue, and you are still receiving error code 0x80073afc when attempting to start Windows Defender, this step should solve the problem if you have Restore Point installed on your computer, which you most likely do.
For this method, we will be restoring your computer to a previous Restore Point. First, just like in method two, hold the “Win” key and press the “R” key. This will open run. Next type “Rstrui.exe” and click “ok”. After some time, you will see System Restore Windows. Click “Next” and select the restore point that you would like to go back to. After your computer has restored to the point you selected, check to ensure that Windows Defender has started correctly.
If the above methods aren't able to rectify the issue, you might have to download and install a powerful automated tool to get the job done.

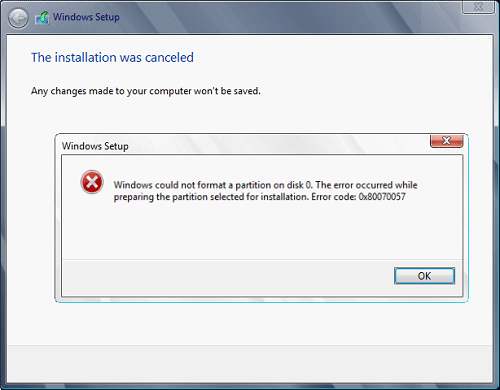 This error is very frustrating and it annoys pretty much anyone who encountered it but do not worry we have a solution for you.
First thing is to confirm the error prompt, Click on the OK button and then on X to exit Windows 10 installation wizard. Click on yes to confirm that you want to exit the setup.
You will find yourself in original installation windows.
On that screen choose and click on Repair your computer. Choose an option screen that will pop up, click on Troubleshoot. In the advanced options, click on the command prompt.
Once you are in command prompts type DISKPART and hit ENTER
In the diskpart prompt type LIST DISK and hit ENTER again.
type SELECT DISK #, where # is listed disk number where you would like to install Windows.
type LIST VOLUME in order to list volumes in the selected disk and hit ENTER
You need to select the volume on which you would like to place your WINDOWS, to do this type in SELECT VOLUME #, where # is the listed number of the volume
Finally, type FORMAT FS=NTFS and hit ENTER
You have successfully formated a given volume, you can now exit DISKPART and return to setup, to exit DISKPART simply type exit and hit ENTER.
Leave command prompt as well by again typing exit and hitting ENTER
You will be returned to Choose an option screen, click on Turn off your PC.
Your drive has been successfully formatted and it is ready for clean Windows installation, you can now restart your Windows 10 installation and the process will complete without errors.
This error is very frustrating and it annoys pretty much anyone who encountered it but do not worry we have a solution for you.
First thing is to confirm the error prompt, Click on the OK button and then on X to exit Windows 10 installation wizard. Click on yes to confirm that you want to exit the setup.
You will find yourself in original installation windows.
On that screen choose and click on Repair your computer. Choose an option screen that will pop up, click on Troubleshoot. In the advanced options, click on the command prompt.
Once you are in command prompts type DISKPART and hit ENTER
In the diskpart prompt type LIST DISK and hit ENTER again.
type SELECT DISK #, where # is listed disk number where you would like to install Windows.
type LIST VOLUME in order to list volumes in the selected disk and hit ENTER
You need to select the volume on which you would like to place your WINDOWS, to do this type in SELECT VOLUME #, where # is the listed number of the volume
Finally, type FORMAT FS=NTFS and hit ENTER
You have successfully formated a given volume, you can now exit DISKPART and return to setup, to exit DISKPART simply type exit and hit ENTER.
Leave command prompt as well by again typing exit and hitting ENTER
You will be returned to Choose an option screen, click on Turn off your PC.
Your drive has been successfully formatted and it is ready for clean Windows installation, you can now restart your Windows 10 installation and the process will complete without errors.  I going to admit right here that I am a big fan of Cooler Master PC cases, I like them and they are always one of the things that I consider when building a new PC, overall I like their ideas and quality so personal for me it was quite a surprise to see that they are one that is making a new generation gaming chair.
Now truth to be told Orb X is not your typical gaming chair as you can clearly see from the pictures. The chair itself will come in two colors: white or black and RGB lighting looks to be prominently featured throughout.
I going to admit right here that I am a big fan of Cooler Master PC cases, I like them and they are always one of the things that I consider when building a new PC, overall I like their ideas and quality so personal for me it was quite a surprise to see that they are one that is making a new generation gaming chair.
Now truth to be told Orb X is not your typical gaming chair as you can clearly see from the pictures. The chair itself will come in two colors: white or black and RGB lighting looks to be prominently featured throughout.
 The chair itself is advertised as both meant and aimed for professional and gaming crowds but I believe the gaming crowd is in general more interested in this hardware piece.
Hardware is enclosed in a fully motorized shuttle dome which aims to maximize your privacy, it supports a single 49inch display or three 27inch monitors along with surround speakers if you do not wish to use headphones.
The chair itself is advertised as both meant and aimed for professional and gaming crowds but I believe the gaming crowd is in general more interested in this hardware piece.
Hardware is enclosed in a fully motorized shuttle dome which aims to maximize your privacy, it supports a single 49inch display or three 27inch monitors along with surround speakers if you do not wish to use headphones.
 It offers an adjustable headrest, lumbar support, and footrest so you can spend some time in it and be comfortable. Controls on the chair itself allow you to raise or lower the dome for easier getting in and out of it.
Orb X also has a compartment in its backside, it folds out and has a sliding tray designed to hold your PC or console. Everything is enclosed so wiring is not the issue.
Overall Orb X seems really like the computer chair of the future, Cooler Master expects to release the Orb X by December 2021, priced around $12,000-$14,000.
It offers an adjustable headrest, lumbar support, and footrest so you can spend some time in it and be comfortable. Controls on the chair itself allow you to raise or lower the dome for easier getting in and out of it.
Orb X also has a compartment in its backside, it folds out and has a sliding tray designed to hold your PC or console. Everything is enclosed so wiring is not the issue.
Overall Orb X seems really like the computer chair of the future, Cooler Master expects to release the Orb X by December 2021, priced around $12,000-$14,000.  Once it opens, click on Device Manager to open it,
If you have a driver device error inside Windows, you should see it immediately when entering the Device Manager, it will have a yellow exclamation mark beside it. Right-click on it and choose update driver.
Once it opens, click on Device Manager to open it,
If you have a driver device error inside Windows, you should see it immediately when entering the Device Manager, it will have a yellow exclamation mark beside it. Right-click on it and choose update driver.
