Error Code 16 - What is it?
Code 16 is a type of Device Manager error code. Windows XP users are most likely to encounter it. This error pops on XP systems that are running legacy or not plug-and-play hardware.
Error code 16 is displayed in the following format:
‘Windows cannot identify all the resources this device uses. (Code 16)’
Solution
 Error Causes
Error Causes
Error code 16 occurs when you use a peripheral device such as an external drive or a printer and that device is not properly or completely configured. Though the device may have been recognized before Windows fails to verify its configuration. Simply put, error code 16 appears when devices are partially configured.
In addition to this, another cause of error 16 is outdated or corrupt device drivers. Devices often fail to run successfully because of driver problems.
Device drivers are programs that provide instructions to control different devices attached to the computer system such as audio devices and printers to name a few.
Though error code 16 is not fatal like other PC error codes such as BSoD; however, it may hamper your ability to use certain devices installed on your system and lower your work productivity.
To avoid inconvenience, it is advisable to resolve the error immediately to avoid inconvenience.
Further Information and Manual Repair
PC error codes are often considered technical and difficult to resolve which is why many prefer to hire a professional for the repair job rather than doing it themselves.
Small repair jobs like fixing error code 16 by a professional computer programmer may cost you hundreds of dollars.
So, why incur so much cost when you can repair it easily by yourself even if you are not a technical whiz.
Error code 16 is easy to repair.
Here are some effective DIY methods that you can use for resolving error code 16 on your PC. These methods require no technical background, knowledge or expertise for that matter. Just simply follow the instructions and resolve the error code 16 issue.
Let’s get started…
Method 1 - Setup from the Disk that Came with the Hardware Device
Run setup from the disk that came with the hardware device, or you can simply copy the setup software file to your hard drive/flash drive. Refer to the vendor’s direction to set up.
If for any reason you’re unable to find the directions, simply uninstall the device. Then go to the start menu, Control Panel, and select ‘Add New Hardware’.
Now pick the appropriate hardware and follow the steps that the Wizard suggests. This is most likely to resolve the error code.
Nonetheless, if the error code still persists, then try method 2.
Method 2 - Allocate More PC Resources
Another alternative method to resolve error code 16 is to allocate more PC resources to the device. To specify additional resources:
- Go to the start menu
- Type Device Manager
- Then go to the Device properties and click the resources
- Here specify the device in the Device Manager
- If you see a resource with a question mark, assign that resource to the device
- However, if for any reason the resource is unable to change, then simply click ‘Change Setting’.
- If Change Settings is not available, then click the box to the ‘Use Automatic Settings’ box. This will make the option available.
Method 3 - Install DriverFIX
As previously stated above, device manager error codes like error code 16 may also occur due to driver problems. If this is the underlying reason for error code 16 on your system, then the best way to resolve it is to install DriverFIX.
DriverFIX is user-friendly, advanced, and feature-filled software deployed with an intelligent programming system, which detects all problematic device drivers automatically in seconds.
It matches these drivers with their latest versions and updates them smoothly without any hassle, resolving error code 16 right away.
And furthermore, once you install this software on your PC, you don’t have to worry about driver problems anymore typically because it updates drivers on a regular basis with compatible and new versions, ensuring that your computer functions properly. It is easy to install and is compatible with all Windows versions.
Click here to download DriverFIX to repair error code 16
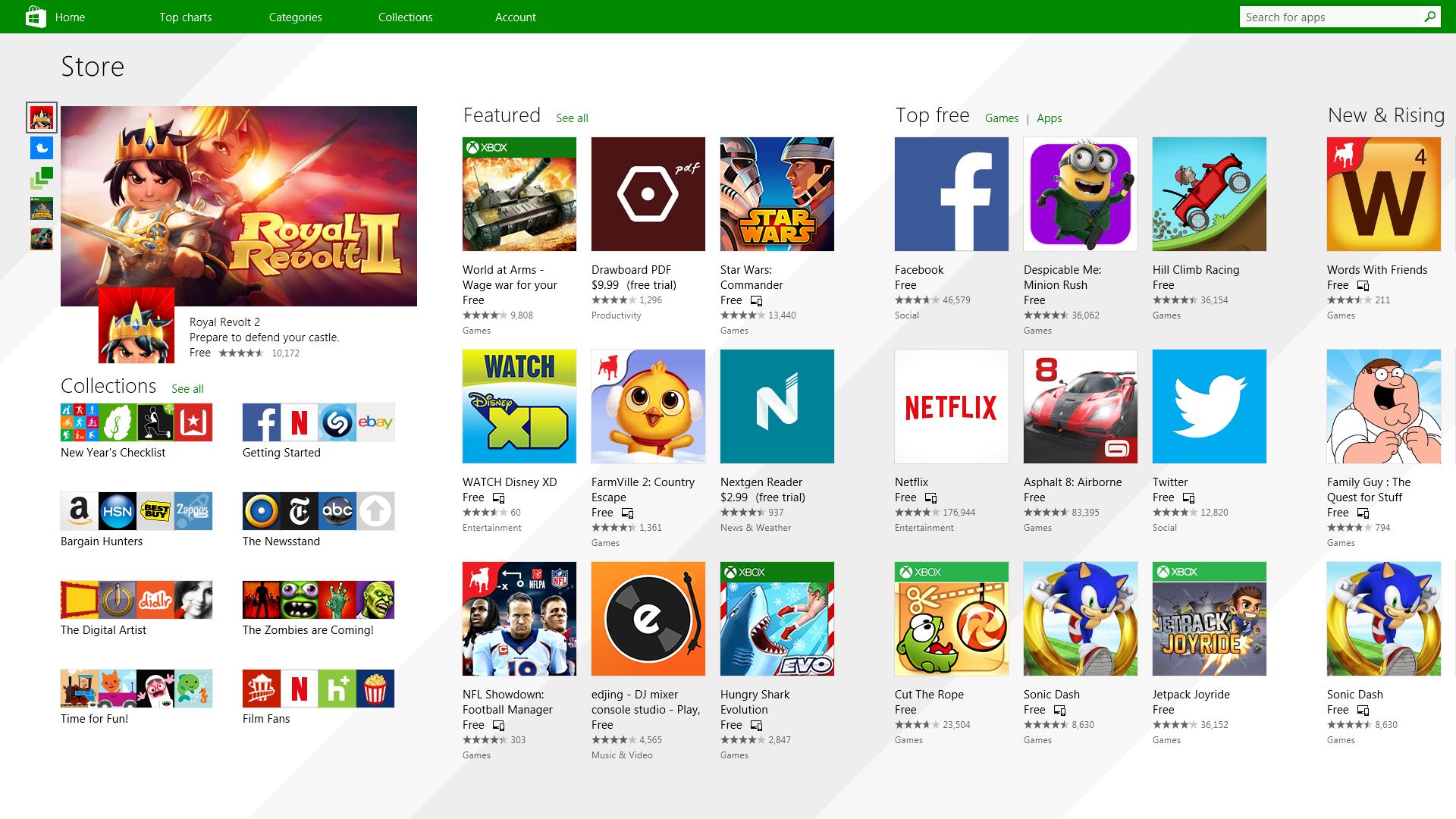 It has officially confirmed that many open source and free applications will be in it like Opera, VLC, discord, Libre office, etc. It seems that Microsoft wants to place its store as one place to go for all of your software needs.
Another great surprise is the coming of Epic games store implementation. It was officially confirmed but not explained in detail, will we have Epic store opened in Windows store or we will only get installer as a package we will see but this is some great news.
As for how it states now, it seems that the Windows store aims to eliminate searching the web for applications and bring them all into one environment with reviews and ratings so you know which one to install and use. It also features a great search engine to find proper applications for your needs.
The new store will come to Windows 10 as well but after all Windows 11 has been mostly released and adopted. So expect it via update in two or three months' time.
It would be great if some larger companies decide to join MS stores like Autodesk, Adobe, the Foundry, etc so you can install everything you need from it but one can only hope.
It has officially confirmed that many open source and free applications will be in it like Opera, VLC, discord, Libre office, etc. It seems that Microsoft wants to place its store as one place to go for all of your software needs.
Another great surprise is the coming of Epic games store implementation. It was officially confirmed but not explained in detail, will we have Epic store opened in Windows store or we will only get installer as a package we will see but this is some great news.
As for how it states now, it seems that the Windows store aims to eliminate searching the web for applications and bring them all into one environment with reviews and ratings so you know which one to install and use. It also features a great search engine to find proper applications for your needs.
The new store will come to Windows 10 as well but after all Windows 11 has been mostly released and adopted. So expect it via update in two or three months' time.
It would be great if some larger companies decide to join MS stores like Autodesk, Adobe, the Foundry, etc so you can install everything you need from it but one can only hope. 


 Changes and features
Changes and features