Error Code 0x80070057 – What is it?
Error code 0x80070057 occurs when Windows users are having problems installing updates on their machines. The error code may result due to issues affecting Windows Update, for instance, problems with system files or settings that can be accessed or modified using the registry in Windows. Error code 0x80070057 affects multiple versions of the Windows operating system including Windows 10. Common symptoms manifested when this error code and other update error codes occur include the following:
- Inability to complete the installation of updates via Windows Update
- Presence of error code message box
Error Causes
Update error codes like error code 0x80070057 occur when there are issues related to system files, programs or malicious software is present on one’s machine. To combat these issues, users may need to implement manual repair procedures, depending on the specific error code present on their device.
Solution
 Further Information and Manual Repair
Further Information and Manual Repair
Windows users can fix error code 0x80070057 by manually repairing or deleting subkeys and values within the Windows registry. This enables Windows Update to function as the proper modification of settings and other information present in the registry can fix problems associated with certain error codes.
The manual repair procedures also enable users to address specific problems on the devices that may not be fixed through the use of other methods.
Method One: Back-Up Registry in Windows
The Windows registry contains information regarding applications installed on the version of Windows you use on your device. This information as well as settings related to hardware are all accessible to users and can be useful when combating problems like error code 0x80070057.
However, users will need to be very careful when making modifications within the registry in Windows. This is due to the fact that errors made while accessing the registry can lead to serious issues on your PC. Backing up your registry before you modify it is crucial since it will provide protection against any problems that may arise if you make an error. This is the first step in resolving error code 0x80070057. Follow the steps below to back up your registry properly.
- Step one: Type regedit.exe in the search box near the Start button.
- Step two: Type the appropriate password or provide confirmation if you are prompted to do so
- Step three: Locate Registry Editor
- Step four: Select registry key or subkey that you want to back up
- Step five: Click File > Export
- Step six: In the Export Registry File dialog box, choose a location where you will save the backup copy
- Step seven: Name the backup file then select Save.
In the case of fixing error code 0x80070057, the registry file or subkey you will need to back up relates to this: HKEY_LOCAL_MACHINE. This contains configuration details or information related to your machine regardless of the user. Also note that the registry, once you have created a backup file, will be protected, thus enabling you to move to the manual method mentioned below.
Method Two: Make Changes to the Windows Registry
The execution of modifications to the registry can be a complex procedure, especially if you are an average Windows 10 user who lacks technical knowledge. Thankfully, even non-technical users can access the solutions they need by simply following the instructions provided in this article.
You may also contact a Windows repair technician as well, in case you have trouble implementing the steps mentioned for modifying your Windows registry or if other problems arise while you are proceeding with these instructions.
Step one: Access the Windows Registry Editor by typing regedit.exe in the search box near the Start button.
Step two: Type the appropriate password or provide confirmation if you are prompted to do so
Step three: Locate Registry Editor
Step four: Enter the following:
[HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsUpdateUX] "IsConvergedUpdateStackEnabled"=dword:00000000
[HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsUpdateUXSettings] "UxOption"=dword:00000000
After making these modifications in the Windows registry, restart your machine. You can then check Windows Update to see if the problem has been resolved. If the modifications to the registry have proven successful, you will no longer see the error code 0x80070057 message box. You will also be able to complete all updates via Windows Update.
Method Three: Download an Automated Tool
If you wish to always have at your disposal a utility tool to fix these Windows 8 and other related issues when they do arise, download and install a powerful automated tool.
 I do not know about you, but I prefer to set my Windows to be more to my liking and not how Microsoft thinks it should be. Let’s face it, not all users feel comfortable whit Microsoft settings and idea how things should be.
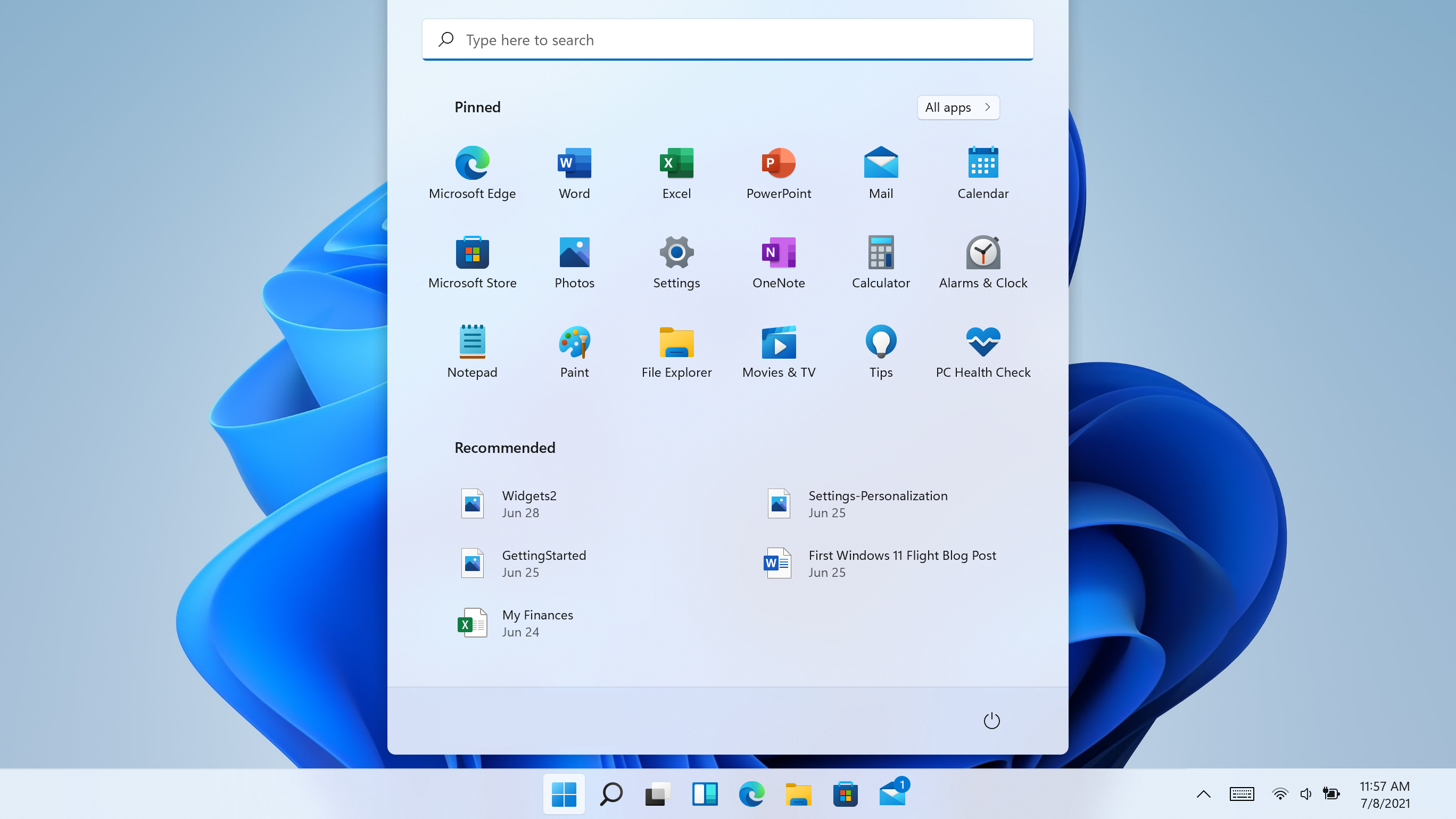
One of the things I particularly did not like even in Windows 10 is icons that come by default on my taskbar, now so far, well until the latest Windows 11 update you could remove default taskbar icons the same way as in Windows 10, just right-click on them and unpin, sadly with latest update build on Windows 11 this option has been removed.
In order to remove default icons from the taskbar, one must go now to Windows 11 settings and choose from there which one you would like to be placed on it. Of course, this is nothing game-breaking but it still feels strange why the standard option has been removed, it just makes no sense but lately not many things that come from Microsoft do.
I do not know about you, but I prefer to set my Windows to be more to my liking and not how Microsoft thinks it should be. Let’s face it, not all users feel comfortable whit Microsoft settings and idea how things should be.
One of the things I particularly did not like even in Windows 10 is icons that come by default on my taskbar, now so far, well until the latest Windows 11 update you could remove default taskbar icons the same way as in Windows 10, just right-click on them and unpin, sadly with latest update build on Windows 11 this option has been removed.
In order to remove default icons from the taskbar, one must go now to Windows 11 settings and choose from there which one you would like to be placed on it. Of course, this is nothing game-breaking but it still feels strange why the standard option has been removed, it just makes no sense but lately not many things that come from Microsoft do.
I do not know about you, but I prefer to set my Windows to be more to my liking and not how Microsoft thinks it should be. Let’s face it, not all users feel comfortable whit Microsoft settings and idea how things should be.
One of the things I particularly did not like even in Windows 10 is icons that come by default on my taskbar, now so far, well until the latest Windows 11 update you could remove default taskbar icons the same way as in Windows 10, just right-click on them and unpin, sadly with latest update build on Windows 11 this option has been removed.
In order to remove default icons from the taskbar, one must go now to Windows 11 settings and choose from there which one you would like to be placed on it. Of course, this is nothing game-breaking but it still feels strange why the standard option has been removed, it just makes no sense but lately not many things that come from Microsoft do.
I do not know about you, but I prefer to set my Windows to be more to my liking and not how Microsoft thinks it should be. Let’s face it, not all users feel comfortable whit Microsoft settings and idea how things should be.
One of the things I particularly did not like even in Windows 10 is icons that come by default on my taskbar, now so far, well until the latest Windows 11 update you could remove default taskbar icons the same way as in Windows 10, just right-click on them and unpin, sadly with latest update build on Windows 11 this option has been removed.
In order to remove default icons from the taskbar, one must go now to Windows 11 settings and choose from there which one you would like to be placed on it. Of course, this is nothing game-breaking but it still feels strange why the standard option has been removed, it just makes no sense but lately not many things that come from Microsoft do. 

 Fear not because we had this issue and tried several things in order to overcome the problem and after some time here is a list of what can you do if you are facing this exact issue. The list is written from most simple solutions to more complex ones and it is advisable to follow it as presented. That being said, let's dive into solving the problem.
Fear not because we had this issue and tried several things in order to overcome the problem and after some time here is a list of what can you do if you are facing this exact issue. The list is written from most simple solutions to more complex ones and it is advisable to follow it as presented. That being said, let's dive into solving the problem.
