Not a Valid Win32 Application Error - What is it?
Not a Valid Win32 Application error code that indicates either the file or the program you are attempting to run missing or corrupt. And because of this error, Windows is unable to open your desired file or run the program successfully.
Error Causes
The ‘Not a Valid Win32 Application’ is triggered due to multiple reasons such as:
- Unsuccessful program installation due to damaged disc/CD
- Corrupted or incompatible file
- The hard drive is loaded with bad and invalid entries
- Malware invasion or viral infection
When you come across this error code on your PC, it is advisable to resolve it as it will cause you a great deal of inconvenience hampering program and file accessibility.
Furthermore, if the error code occurs due to malware or viruses, then it can lead to severe data security threats and privacy issues.
Further Information and Manual Repair
To resolve the Not a Valid Win32 Application error on your PC, you don’t need to be a technical expert or hire a professional. Though this error might be crucial it is easy to fix.
Here are some of the many methods that you can try to resolve this error code on your PC:
- Check for File Compatibility
If you downloaded a file that is not compatible with your Windows version then you will come across this error. In this case, it is advisable to download the file version that is compatible and can run easily on the
Windows version installed on your system.
Nonetheless, if the file is compatible but still doesn’t run on your PC, then it’s possible that the file became corrupt during the download.
Try downloading the file again.
You may also come across the Not a valid Win32 application error code if the program installation from the CD is unsuccessful.
This happens when the CD is dirty or it is scratched. The program does not copy properly onto the computer from the damaged CD. So, if the CD is scratched and dirty, buy a new CD and try installing the program again.
- Verify the Program You Want to Run is Still on the Computer
If you are running the program from a shortcut, then verify that the program is still installed on your PC. This error may occur if the program is no longer installed on the computer.
If you find the program is not installed on your system, then reinstall and try running the program again.
Make sure the program or the file you are attempting to run on your system does not contain the same name as the long filename directory it is saved in. For example, running a file named ‘program’ in the ‘program files’ directory can cause errors in some Windows versions.
If this is the issue, then try installing the program in a different directory.
If the hard drive is bad or corrupted, it can also generate the not a valid Win32 application. And because of this error files and programs fail to execute successfully as not all data can be read from the hard drive.
To repair this issue first you need to run defrag and ScanDisk Microsoft built-in tools. These tools check for errors on the hard drive.
If the error code occurs due to a viral infection or malware attack on your system, then you must download an antivirus, scan, and remove such malicious software. However, antivirus may slow down the speed of your PC.
So, to resolve speed issues and boost the performance of your system, you may have to download a system optimizer.


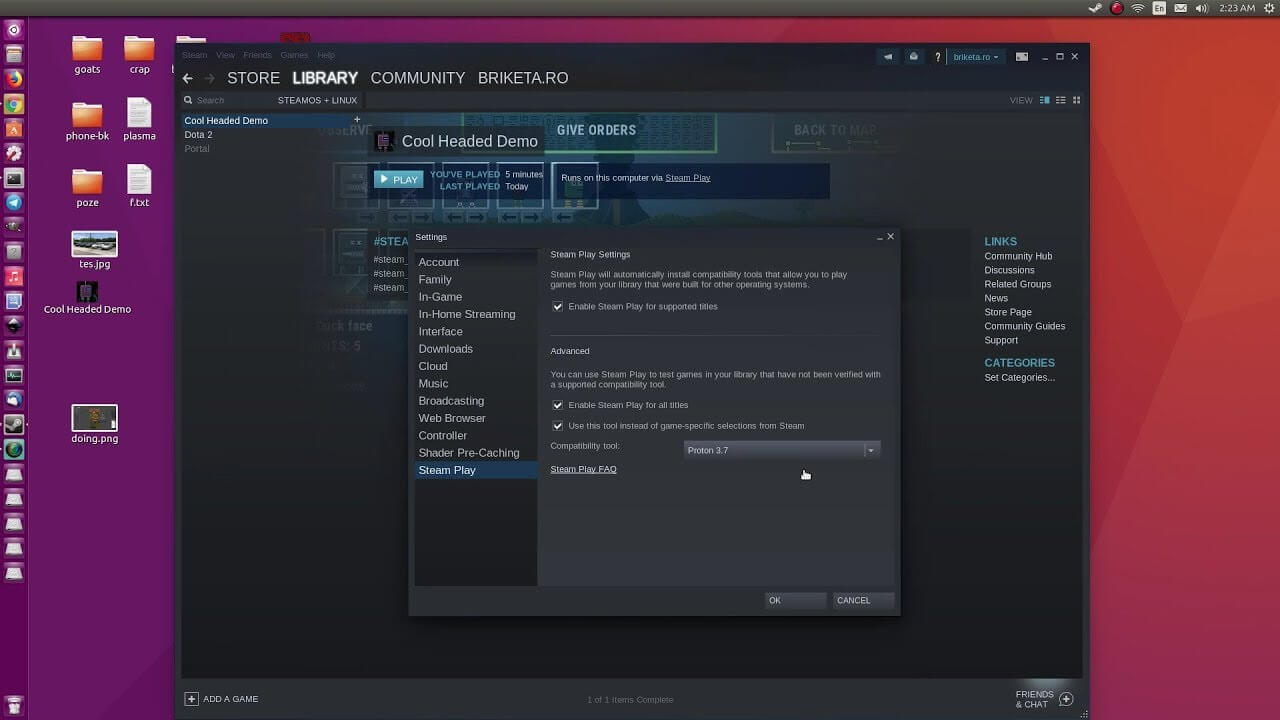 Despite popular belief, there are a lot of users running Linux OS. Linux offers great security and working environment and 96.3% of the world's top 1 million servers run on Linux. 90% of all cloud infrastructure operates on Linux and practically all the best cloud hosts use it. But gaming on Linux is limited, enter Steam proton a Valve’s gaming solution.
Despite popular belief, there are a lot of users running Linux OS. Linux offers great security and working environment and 96.3% of the world's top 1 million servers run on Linux. 90% of all cloud infrastructure operates on Linux and practically all the best cloud hosts use it. But gaming on Linux is limited, enter Steam proton a Valve’s gaming solution.
