What is the Error Code 0x6d9?
If you have a firewall installed on your system, you may come across the error code 0x6d9. This error occurs when opening Windows Firewall with advanced security. The error code 0x9d9 is displayed as:
“There was an error opening the Windows Firewall with Advanced Security snap-in.
The Windows Firewall with Advanced Security snap-in failed to load. Restart the Windows Firewall service on the computer you are managing. Error code: 0x6D9”
This occurs when the Windows Firewall service is missing. The service doesn’t start due to permission errors on various registry keys. It is a critical blue screen of death error code that turns the computer screen blue and causes the Windows to shut down.
If this error code is not fixed it may start appearing more and more frequently resulting in total system corruption.
Solution
 Error Causes
Error Causes
Virtually, the underlying cause for Windows Firewall error code 0x6d9 is a damaged registry. The registry is the database of the system that saves all the activities including web browsing and programs installed and uninstalled and junk files on the PC.
The registry saves all the information in the RAM, your hard disk. As the disk gets filled with files, it then requires more power to run which impacts the performance of the PC and slows it down.
Simultaneously, since the hard disk is overloaded with data, it exposes the registry to file damages, fragmentation, and corruption which then eventually causes hindrance in running calling programs and running them on your system because files are either corrupt or missing.
Other than cluttered disk issues, registry errors also occur due to viral and malware attacks. If the Firewall is inaccessible, your system is prone to malware.
Further Information and Manual Repair
To fix the error code 0x6d9 on your system, you don’t have to be a computer programmer or hire a professional. You can fix it all by yourself with Restoro.
Restoro is an advanced, intuitive, user-friendly, and multi-functional repair tool with a comprehensive suite of powerful PC fixing utilities, all in one.
From registry errors like the blue screen of death error codes including 0x6d9 to viral infection and system slowdowns, Restoro is your one-stop solution for all PC errors.
With this software, you don’t need any technical expertise. You don’t have to get into the nitty-gritty of finding the deep-rooted cause for the error code 0x6d9 and then searching and installing a PC tool designed to solve that specific cause for the error.
Restoro has an intuitive and sophisticated interface combined with an automated algorithm that enables it to detect, scan and identify all the underlying and deep-rooted causes for errors on your PC in seconds and resolves them all. All you have to do is hit the scan button and the
Restoro takes care of the rest.
Restoro features
Restoro is also easy to use and has simple navigation making it easy for all levels of users including beginners and intermediates to use.
This PC Fixer is both a high-functional registry cleaner and a powerful anti-virus. This means whether the error code 0x6d9 occurs due to disk overload or viral infection this helper can be used to fix the error in both scenarios.
Its in-built registry cleaner cleans and clears up the hard disk in a few seconds. It removes all the unnecessary and obsolete files cluttering the system and repairs the damaged registry.
For data safety during repair, it has a built-in back feature. This feature allows you to save and create backup copies of all your files.
Its smart privacy error detector feature checks for viruses, spyware, adware, and malware invasion on your system. Such malicious software if not removed from your PC can expose you to data security risks. Such software allows easy access to hackers.
And since error code 0x6d9 hampers you in using Firewall, your system will have higher chances of getting infected by viruses and data security dangers. Nonetheless, by running Restoro on your system, you can easily remove this malicious software and resolve the error code 0x6d9.
Unlike other repair tools, Restoro is compatible with all Windows versions.
How to get Restoro
So, what are you waiting for? It will take just 3 steps. To get started all you need to do is:
- Click here to install Restoro
- Run it to Scan for errors
- Hit the repair button to resolve
To prevent the error code 0x6d9 from reoccurring on your PC for a while proper PC maintenance is advisable to run Restoro on a weekly basis on your system so that the registry is not cluttered and your system is not exposed to viruses.
Timely detection of errors and repair is the best way to keep your system performing smoothly and at its optimum speed.



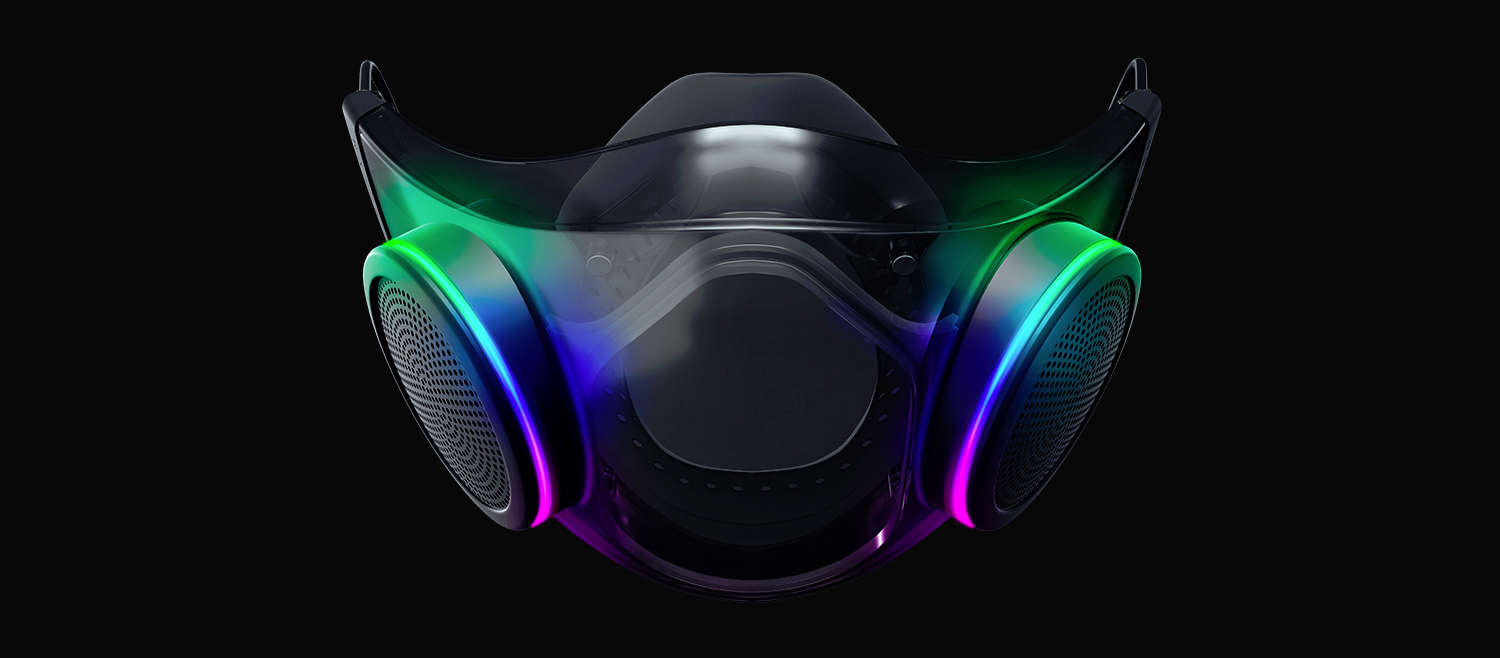 The world today is still sadly under pandemic and by the looks of it, COVID-19 is here to stay, well at least for some time in the near future. Razer seems to think so as well since their upcoming gear is not really what you would expect.
Enter Hazel, a new and upcoming Razer smart mask.
The world today is still sadly under pandemic and by the looks of it, COVID-19 is here to stay, well at least for some time in the near future. Razer seems to think so as well since their upcoming gear is not really what you would expect.
Enter Hazel, a new and upcoming Razer smart mask.
