PriceGong is a browser add-in for Internet Explorer, Chrome and Firefox that analyzes web sites your browser visits and attempts to find coupons and other deals associated with the merchant’s product offerings or services. If PriceGoing sees a corresponding deal, it will attempt to inject an affiliate ‘code’ in order to collect various affiliate based commissions if a purchase is made while trying to offer you the best price of that particular product, or, in many cases try and show you an alternative product that is similar even if it is sold by a different merchant. Upon further inspection it was found that PriceGong failed to function in our testing.
While installed, this extension might display additional ads, inject sponsored content into webpages, even if the sponsored content is of lower quality than the original ones.
About Browser Hijackers
Browser hijackers (sometimes known as hijackware) are a kind of malicious software that alters web browser settings without the computer owner’s knowledge or consent. These types of hijacks are increasing at an alarming rate around the globe, and it could be really nefarious and often dangerous too. They’re created to disrupt browser programs for various purposes. In most cases, hijackers are designed for the benefit of online hackers usually through income generation from forced advert mouse clicks and site visits. Though it might seem naive, all browser hijackers are damaging and thus always regarded as security risks. In a much worst case, your browser could be hi-jacked to download malware that will do a great deal of damage to your computer or laptop.
Major symptoms that an internet browser has been hijacked
Signs that an internet browser is hijacked include:
1. home page is changed
2. bookmark and the new tab are also modified
3. the essential web browser settings are modified and unwanted or insecure sites are put into the trusted websites list
4. discover new toolbars that you didn’t add
5. never-ending pop-up ads appear and/or your web browser popup blocker is disabled
6. your web browser has become unstable or starts running sluggishly
7. you’re disallowed access to specific web pages, for example, the website of an antivirus software manufacturer like SafeBytes.
Precisely how browser hijacker infects computers
A browser hijacker can be installed on your computer if you visit an infected website, click an email attachment, or download something from a file-sharing site. They are usually included with toolbars, add-ons, BHO, plug-ins or browser extensions. Other times you may have accidentally accepted a browser hijacker as part of a software program bundle (usually freeware or shareware). An example of some well-known browser hijacker includes Anyprotect, Conduit, Babylon, SweetPage, DefaultTab, RocketTab, and Delta Search, but the names are regularly changing.
The existence of any browser hijacker on your computer can substantially diminish the web browsing experience, record your internet activities that result in troublesome privacy issues, create system stability problems and finally cause your computer to slow down or to a practically unusable state.
Browser Hijacker Malware – Removal
Some hijackers can be removed by uninstalling the freeware they were included with or by removing any extension you have recently added to your system. However, most browser hijackers are hard to get rid of manually. No matter how much you try to eliminate it, it might come back over and over. You should think about performing manual repairs only if you are a tech-savvy individual, as there are potential risks associated with messing around with the system registry and HOSTS file.
Installing and running antivirus application on the affected computer could automatically erase browser hijackers and other malicious programs. SafeBytes Anti-Malware discovers all kinds of hijackers – including PriceGong – and eliminates every trace quickly and efficiently. Use a system optimizer along with your antivirus software to solve various computer registry issues, remove system vulnerabilities, and improve your computer's overall performance.
Tips on How to Remove Malware that is Blocking Websites or Preventing Downloads
Practically all malware is bad, but certain kinds of malware do much more damage to your PC than others. Some malware variants alter browser settings by including a proxy server or modify the PC’s DNS configuration settings. In these cases, you’ll be unable to visit some or all of the websites, and therefore unable to download or install the required security software to eliminate the infection. If you are reading this now, you may have perhaps recognized that a virus infection is the real cause of your blocked web traffic. So how to proceed if you want to install an anti-malware application like Safebytes? There are a few fixes you can attempt to get around with this particular issue.
Use Safe Mode to resolve the problem
Safe Mode is actually a unique, simplified version of Windows where just bare minimum services are loaded to counteract viruses as well as other troublesome programs from loading. In case the malware is set to load automatically when computer boots, switching into this particular mode could prevent it from doing so. To boot into Safe Mode, hit “F8” key on the keyboard right before Windows boot screen shows up; Or after normal Windows boot up, run MSCONFIG, look over “Safe Boot” under Boot tab, and click Apply. Once you’re in Safe Mode, you can attempt to download and install your antivirus program without the hindrance of the virus. At this point, you could run the antivirus scan to eliminate viruses and malware without any hindrance from another malicious application.
Download the anti-malware program in an alternate web browser
Malicious program code may exploit vulnerabilities in a specific internet browser and block access to all anti-malware software websites. If you appear to have a virus attached to Internet Explorer, then switch to an alternate web browser with built-in security features, such as Firefox or Chrome, to download your favorite anti-malware program – Safebytes.
Create a bootable USB antivirus drive
Another option is to save and operate an anti-malware software program entirely from a Flash drive. Follow these steps to use a flash drive to clean your infected PC.
1) On a virus-free computer, install Safebytes Anti-Malware.
2) Plug in the USB drive to a USB port on the uninfected computer.
3) Double-click on the downloaded file to open the installation wizard.
4) Choose the flash drive as the location for saving the software file. Follow activation instructions.
5) Transfer the flash drive from the clean computer to the infected PC.
6) Double-click the anti-malware software EXE file on the pen drive.
7) Run Full System Scan to detect and clean-up up all sorts of malware.
SafeBytes Anti-Malware: Light-weight Malware Protection for Windows Computer
If you’re looking to buy anti-malware for your laptop or computer, there are lots of brands and packages for you to consider. A few of them do a great job in eliminating threats while some will harm your computer by themselves. You should select a company that builds industry-best anti-malware and has earned a reputation as trustworthy. On the list of highly recommended application by industry analysts is SafeBytes Anti-Malware, a popular security application for Microsoft Windows.
SafeBytes antimalware is a very effective and easy to use protection tool which is ideal for users of all levels of IT literacy. This software could easily detect, eliminate, and protect your computer from the most advanced malware intrusions such as spyware, adware, trojan horses, ransomware, PUPs, worms, parasites as well as other potentially harmful software applications.
SafeBytes possesses a plethora of wonderful features that can help you protect your computer from malware attack and damage. Let’s check out some of them below:
Robust, Anti-malware Protection: Using a critically acclaimed malware engine, SafeBytes provides multilayered protection which is designed to find and remove threats which are hidden deep inside your computer’s operating system.
Real-time Threat Response: SafeBytes provides a totally hands-free live protection that is set to observe, block, and remove all threats at its very first encounter. It will constantly monitor your laptop or computer for hacker activity and also provides users with advanced firewall protection.
Web Filtering: SafeBytes inspects the hyperlinks present on a webpage for possible threats and notifies you if the website is safe to browse or not, through its unique safety ranking system.
Fast Scan: Safebytes Anti-Malware, with its enhanced scanning engine, offers ultra-fast scanning which will immediately target any active on-line threat.
Lightweight: SafeBytes is a light-weight and user friendly anti-virus and antimalware solution. Since it utilizes very little computer resources, this application leaves the computer’s power exactly where it belongs: with you.
24/7 Guidance: Support service is readily available for 24 x 7 x 365 days through chat and email to answer your queries.
SafeBytes can keep your PC protected from most advanced malware threats automatically, thus keeping your internet experience secure and safe. You can rest assured that your computer will be protected in real-time as soon as you put this software to use. So if you are looking for the best anti-malware subscription for your Windows-based PC, we highly recommend SafeBytes Anti-Malware program.
Technical Details and Manual Removal (Advanced Users)
To eliminate PriceGong manually, navigate to the Add/Remove programs list in the Control Panel and choose the offending program you want to remove. For web browser extensions, go to your web browser’s Addon/Extension manager and choose the add-on you want to disable or remove. You might even want to reset your home page and search engine providers, and also clear your web browser cache and cookies.
Finally, check your hard disk for all of the following and clean your registry manually to remove leftover application entries following uninstalls. However, editing the Windows registry is actually a complicated job that only advanced computer users and professionals should attempt to fix the problem. In addition to that, certain malware is capable of replicating or preventing deletion. You’re advised to do this procedure in Windows Safe Mode.
Folders:
C:\Documents and Settings\Lynn\Application Data\PriceGong
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data
Files:
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\a.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\b.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\c.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\d.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\e.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\f.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\g.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\h.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\i.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\J.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\k.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\l.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\m.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\mru.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\n.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\o.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\p.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\q.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\r.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\s.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\t.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\u.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\v.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\w.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\x.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\y.xml
C:\Documents and Settings\Lynn\Application Data\PriceGong\Data\z.xml
Registry:
HKEY_CURRENT_USER\Software\PriceGong


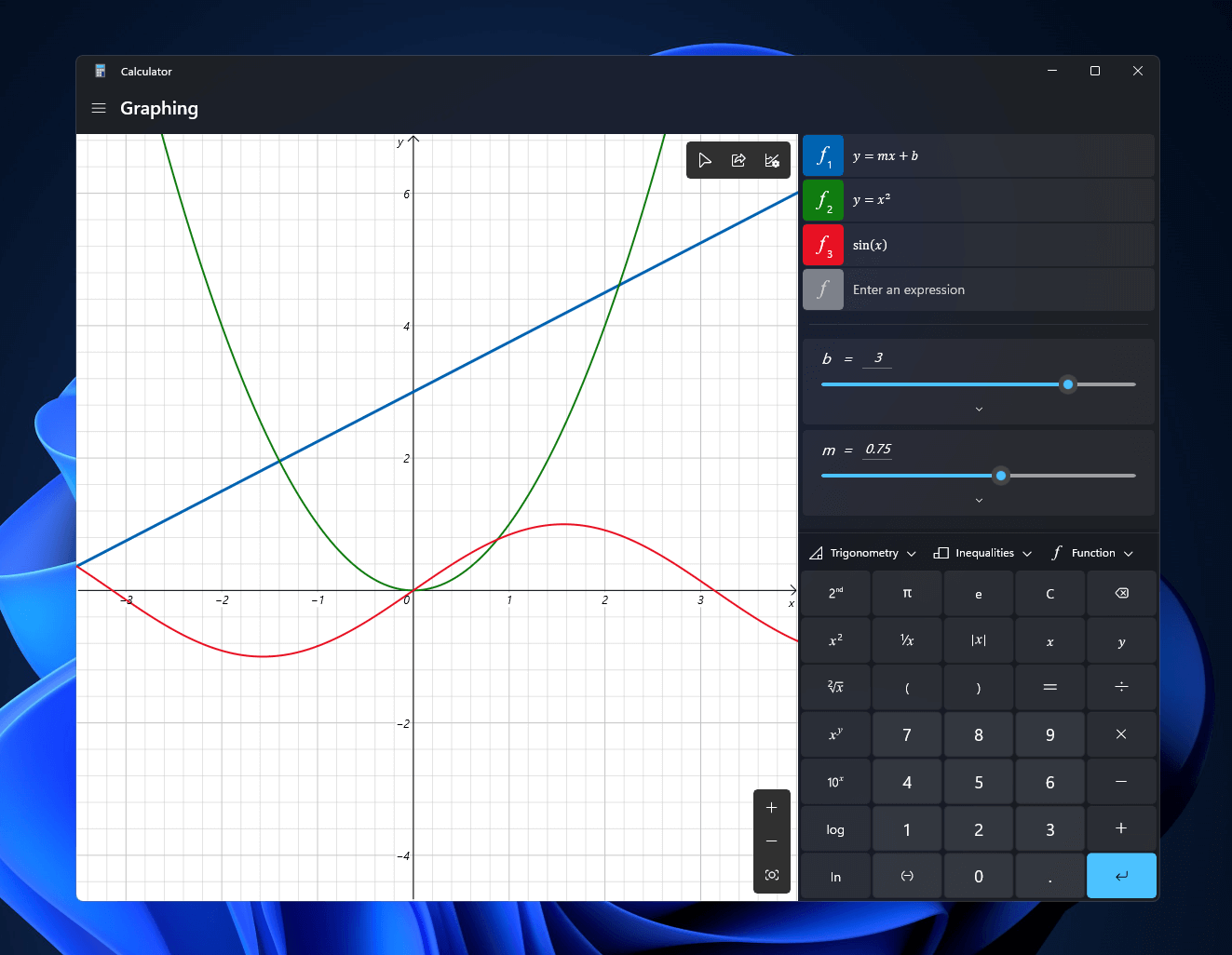 Windows 11 will bring some old applications in new looks and some will get additional features as well. One of the old apps that will get new stuff is a calculator.
The calculator was always a way to go application for quick calculations but Microsoft aims to expand on that and make the calculator a little more useful.
The first thing that you will notice is the calculator look, the calculator has now an application theme setting that allows you to change the look of the application. It comes in standard and professional mode as usual but this time calculator will come with features that will enable it to handle some programming and engineering tasks.
The new calculator features a full graphing mode that lets you visually analyze a graph to identify key features. It also packs a deep converter that can switch between more than 100 units and currencies.
Windows 11 will bring some old applications in new looks and some will get additional features as well. One of the old apps that will get new stuff is a calculator.
The calculator was always a way to go application for quick calculations but Microsoft aims to expand on that and make the calculator a little more useful.
The first thing that you will notice is the calculator look, the calculator has now an application theme setting that allows you to change the look of the application. It comes in standard and professional mode as usual but this time calculator will come with features that will enable it to handle some programming and engineering tasks.
The new calculator features a full graphing mode that lets you visually analyze a graph to identify key features. It also packs a deep converter that can switch between more than 100 units and currencies.
