What is this particular error?
One common issue when trying to upgrade to Windows 10 from Windows 7 or 8 is incompatible software. Any installed software or app that isn’t compatible with Windows 10 will prevent you from continuing with the set-up. Normally, you’ll get an error message “What needs your attention” and it will ask you to uninstall a list of apps manually. Unfortunately, some users reported that they couldn’t find the app it asks to uninstall. In some cases, users said they’ve already uninstalled the app but it still won’t start the Windows 10 Setup.
Solution
 Error Causes
Error Causes
This type of issue normally occurs because of the following:
- Incompatible software/apps
- Corrupted software/apps
- Incomplete uninstallation
Further Information and Manual Repair
Here are some steps you can take whenever you encounter this error.
Note: Before taking any steps, make sure that you’re highly equipped to do so. Some steps might affect the system and even do more damage to your computer. You might also want to consider using an automated tool instead.
Method 1 – Perform a clean boot, then retry upgrading
A clean boot is normally done to start Windows using the least set of drivers and startup programs available. By doing this, it eliminates possible software issues that happen when installing or uninstalling a program in Windows 10.
Before performing a clean boot, make sure to take note of the following:
- You need administrative privileges in order to perform this action.
- When doing this, your computer might lose temporarily functionality. However, it will return after start-up.
- It is highly advisable to not use the System Configuration to change advanced boot options.
Here are the steps to perform a clean boot.
- Step 1 – Go to Start and search for msconfig
- Step 2 – Go to System Configuration
- Step 3 – Under Services tab, click on the “Hide all Microsoft services” checkbox. Then, choose to Disable all
- Step 4 – Go to the System Configuration’s Startup tab. Then, click on “Open Task Manager”
- Step 5 – In the Task Manager dialog box, you will see a Startup tab. Choose items that you want to disable and then click the Disable button
- Step 6 – Close the Task Manager dialog box.
- Step 7 – Go back to the Startup tab of the System Configuration box. Click “Ok” then proceed with restarting.
Method 2 – Manually uninstall programs from the Program Files folders
Instead of using the “add or remove programs” feature in Windows, you might need to manually install the program directly from the C drive. To do this, follow the steps below:
- Step 1 – Go to the C drive, and look for the Program Files folders. For 32-bit users, you can find it at C:\Program Files. If you’re using the 64-bit version of Windows, go to C:\Program Files (x86) folder.
- Step 2 – Find the “uninstall” application file
- Step 3 – Right-click, and run the file as administrator. Wait for the uninstallation to finish. In some software, you need to restart your system before the uninstallation will take effect.
Note: In some cases, you may also need to search for files related to the program. You can use the search bar under Drive C to do this. Delete those files as well.
Method 3 – Create a new user account
Before upgrading to Windows 10, create a new user account. Make sure it has administrative privileges. From there, run the upgrade.
Method 4 – Use third-party uninstaller services
If you still can’t run Windows 10 Setup after the above methods, you might need to rely on a third-party service. Microsoft recommends Revouninstaller that can help you.
Before using this software, reinstall the application or utility that Windows 10 wants you to install. Then, use Revouninstaller to delete the program completely.
Method 5 – Disable third-party antivirus software
Some users who experienced this issue reported that it was solved after disabling or completely uninstalling the anti-virus software installed in their system.
Method 6 – Use a trusted automated tool
If after trying the above methods, the problem still persists, it might be best to use a trusted automated tool to fix the issue.



 Once disguised it will wait patiently for a user's click and once that happens it will replicate itself and further infect the system. This rapid spread can lead to stolen personal data, some system hick-ups, and other system-related issues.
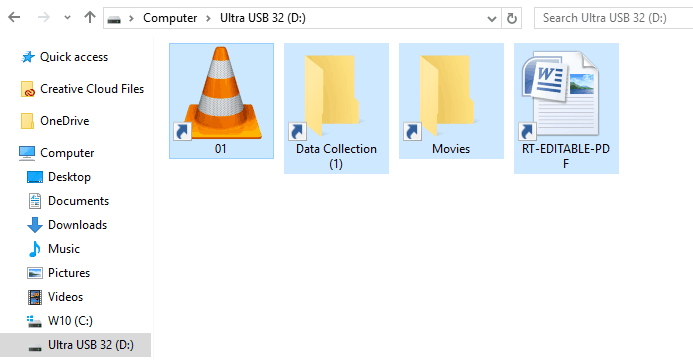
This malware mainly affects physical file transfer devices like for example and most USB drives, hard drives, and SD memory cards and it can easily transfer itself to the computer.
The advantage of this shortcut virus comparing it to others is that it is mostly undetected by a vast variety of antivirus software. So running just anti-virus software maybe not be enough to remove it from your system. Luckily for all unfortunate users that have caught this annoyance, it can be easily removed fully manually in a short time.
Once disguised it will wait patiently for a user's click and once that happens it will replicate itself and further infect the system. This rapid spread can lead to stolen personal data, some system hick-ups, and other system-related issues.
This malware mainly affects physical file transfer devices like for example and most USB drives, hard drives, and SD memory cards and it can easily transfer itself to the computer.
The advantage of this shortcut virus comparing it to others is that it is mostly undetected by a vast variety of antivirus software. So running just anti-virus software maybe not be enough to remove it from your system. Luckily for all unfortunate users that have caught this annoyance, it can be easily removed fully manually in a short time.
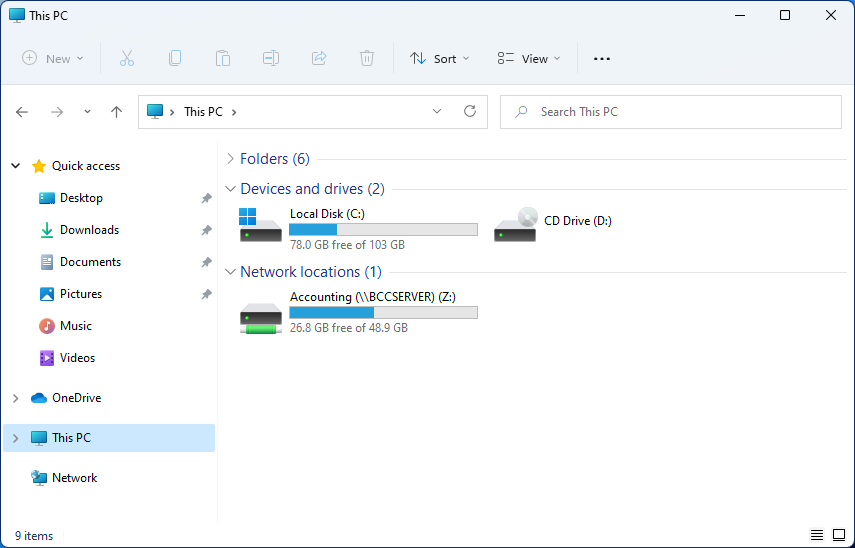 Mapping network drive has many benefits in terms of speed and ease of access of files via network. It lets you access the hard drive over the whole network like it was the hard drive inside your PC case. In order to easily and quickly map a folder as a network drive follow the guide below.
Mapping network drive has many benefits in terms of speed and ease of access of files via network. It lets you access the hard drive over the whole network like it was the hard drive inside your PC case. In order to easily and quickly map a folder as a network drive follow the guide below.
