RegClean Pro is a program developed by Systweak Inc. RegClean Pro cleans such invalid registry errors using its advanced scan engine. It not only fixes invalid registry entries, it also defragments the registry, keeping it streamlined for smoother system performance.
RegClean Pro defines auto-start registry entities that allow the program to run each time the system is restarted, it also adds various Scheduled tasks in Windows Task Manager in order to launch the application at various times. This application has been found bundled up with various other potentially unwanted applications, also several anti-virus programs have detected this application for optional removal.
About Potentially Unwanted Applications
What is a Potentially Unwanted Program (PUP)?
Have you ever detected an unwanted program on your computer system and pondered how it got there since you’re confident that you didn’t consciously download or never gave authorization to be installed? Potentially Unwanted Programs (PUP), also known as Potentially Unwanted Applications (PUA), are programs that you never wanted in the first place and sometimes come bundled with freeware software. Once installed, the majority of these applications can be hard to eliminate and become much more of a nuisance rather than a benefit.
The term PUP was coined to outline this crapware as something other than malicious software. Similar to malicious software, PUPs cause problems when downloaded and placed on your PC, but what makes a PUP different is you grant consent to download it – the fact is very different – the software installation bundle actually tricks you into accepting the installation. No matter whether it is viewed as malware or otherwise, PUPs are nearly always harmful to a computer owner as they will bring on spyware, adware, keystroke logging, along with other nasty “crapware” features on the PC.
What do PUPs do on your PC, precisely?
PUPs come in many forms. Commonly, they will be seen in adware bundlers which are known to use aggressive and misleading advertising. Most bundlers install multiple adware applications from various vendors, each of which has its own EULA policy. Safebytes Anti-Malware totally eliminates this threat and safeguards the computer against unwanted programs or adware infection. They will also come in the form of web browser extension add-ons and toolbars. They may keep track of your online movements, redirect your search results to risky sites where spyware and adware can be downloaded, hijack your search page, and slow your web-browser down to a crawl.
PUPs lie in the gray part of the software spectrum. Also in the large majority of the cases, people won’t be aware that they are installing an unwanted program. Even if the PUPs really aren’t inherently malicious, these software programs still do practically nothing good on your computer system – they will take valuable resources, slow your PC, weaken your computer security, making your PC more vulnerable to viruses.
How you can stop PUPs
• Read carefully before accepting the license agreement as it might have a clause about PUPs.
• Do not accept standard, express, default, or any other installation settings which are recommended. Always select “custom” installation.
• Install an advert blocker/pop-up blocker; Deploy anti-malware products like Safebytes Anti-Malware. These types of software programs could establish a wall between the computer and online criminals.
• Be alert if you download and install freeware, open-source software, or shareware. Never install applications that seem suspicious or malicious.
• Use official product websites for downloading software. Stay away from download portals altogether as most websites compel users to download the software using their own download manager, which is often bundled with some sort of unwanted programs.
Can't Install Safebytes Anti-malware due to the presence of Malware? Do This!
Practically all malware is bad, but certain types of malicious software do more damage to your computer or laptop than others. Some malware sits in between the computer and the internet connection and blocks a few or all websites which you want to check out. It might also prevent you from the installation of anything on your PC, particularly anti-virus programs. If you’re reading this article right now, you’ve perhaps recognized that virus infection is a reason for your blocked internet traffic. So what to do when you want to install an anti-malware application like Safebytes? There are a few actions you can take to circumvent this issue.
Download the software in Safe Mode with Networking
In Safe Mode, you are able to change Windows settings, uninstall or install some software, and remove hard-to-delete viruses and malware. If the virus is set to load immediately when the computer boots, switching to this mode may prevent it from doing so. To get into Safe Mode or Safe Mode with Networking, press the F8 key while the computer is booting up or run MSConfig and look for the “Safe Boot” options under the “Boot” tab. After you restart into Safe Mode with Networking, you can download, install, as well as update anti-malware software from there. Following installation, run the malware scanner to eliminate most standard infections.
Switch to an alternate web browser
Certain viruses might target vulnerabilities of a particular web browser that block the downloading process. If you seem to have a trojan attached to Internet Explorer, then switch to an alternate web browser with built-in security features, such as Chrome or Firefox, to download your preferred anti-malware program – Safebytes.
Install and run anti-malware from a USB drive
Another method is to download and transfer an anti-malware application from a clean PC to run a virus scan on the infected system. Follow these steps to run the antivirus on the infected computer.
1) On a clean PC, download and install Safebytes Anti-Malware.
2) Plug in the USB drive into the uninfected PC.
3) Double click on the downloaded file to open the installation wizard.
4) Choose a USB flash drive as the place when the wizard asks you where you wish to install the application. Follow activation instructions.
5) Remove the USB drive. You may now use this portable antivirus on the infected computer.
6) Double-click the antivirus software EXE file on the pen drive.
7) Run Full System Scan to identify and clean-up up all types of malware.
A Look at the Best Anti-Malware Program
These days, anti-malware software can protect your PC from different types of internet threats. But exactly how to decide on the right one among various malware protection application that is available out there? As you might be aware, there are numerous anti-malware companies and products for you to consider. Some are worth your money, but most aren’t. You have to purchase a product that has obtained a good reputation and detects not only viruses but other sorts of malware too. Amongst few good programs, SafeBytes Anti-Malware is the highly recommended program for the security-conscious end user.
Safebytes is among the well-established computer solutions firms, which provide this all-inclusive anti-malware software program. With its cutting-edge technology, this application will let you eliminate several types of malware like computer viruses, trojans, PUPs, worms, adware, ransomware, and browser hijackers.
SafeBytes has great features when compared to other anti-malware programs. The following are some of the features you will like in SafeBytes.
Real-time Protection: Malware programs trying to enter the computer are identified and stopped as and when detected by the SafeBytes active protection shields. They are very efficient in screening and getting rid of various threats because they’re constantly revised with new updates and alerts.
World-class AntiMalware Protection: This deep-cleaning anti-malware software goes much deeper than most anti-virus tools to clean out your computer. Its critically acclaimed virus engine locates and disables hard-to-remove malware that conceals deep within your personal computer.
Internet Security: SafeBytes checks and gives a unique safety ranking to each and every site you visit and block access to web pages known to be phishing sites, thus protecting you against identity theft, or known to contain malware.
Fast Scan: Safebytes Anti-Malware, with its advanced scanning engine, offers ultra-fast scanning which can immediately target any active on-line threat.
Lightweight: This program is not “heavy” on your computer’s resources, so you will not notice any performance problems when SafeBytes is operating in the background.
Premium Support: For any technical issues or product support, you can get 24/7 professional assistance via chat and email.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove RegCleanPro without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by RegCleanPro
Files:
File %APPDATASystweakRegClean ProVersion 6.1ExcludeList.rcp.
File %APPDATASystweakRegClean ProVersion 6.1German_rcp.dat.
File %APPDATASystweakRegClean ProVersion 6.1log_06-13-2013.log.
File %APPDATASystweakRegClean ProVersion 6.1results.rcp.
File %APPDATASystweakRegClean ProVersion 6.1TempHLList.rcp.
File %COMMONDESKTOPRegClean Pro.lnk.
File %COMMONPROGRAMSRegClean ProRegClean Pro entfernen.lnk.
File %COMMONPROGRAMSRegClean ProRegClean Pro.lnk.
File %COMMONPROGRAMSRegClean ProRegister RegClean Pro.lnk.
File %PROGRAMFILESRegClean ProChinese_rcp.ini.
File %PROGRAMFILESRegClean ProCleanSchedule.exe.
File %PROGRAMFILESRegClean ProCloud_Backup_Setup.exe.
File %PROGRAMFILESRegClean ProCloud_Backup_Setup_Intl.exe.
File %PROGRAMFILESRegClean Proisxdl.dll.
File %PROGRAMFILESRegClean ProRCPUninstall.exe.
File %PROGRAMFILESRegClean ProRegCleanPro.dll.
File %PROGRAMFILESRegClean ProRegCleanPro.exe.
File %PROGRAMFILESRegClean Prosystweakasp.exe.
File %PROGRAMFILESRegClean Proxmllite.dll.
File %WINDIRTasksRegClean Pro_DEFAULT.job.
File %WINDIRTasksRegClean Pro_UPDATES.job.
Directory %APPDATASystweakRegClean ProVersion 6.1.
Directory %APPDATASystweakRegClean Pro.
Directory %COMMONPROGRAMSRegClean Pro.
Directory %PROGRAMFILESRegClean Pro.
Registry:
Key Distromatic at HKEY_CURRENT_USERSoftware.
Key Systweak at HKEY_CURRENT_USERSoftware.
Key Systweak at HKEY_LOCAL_MACHINESOFTWARE.
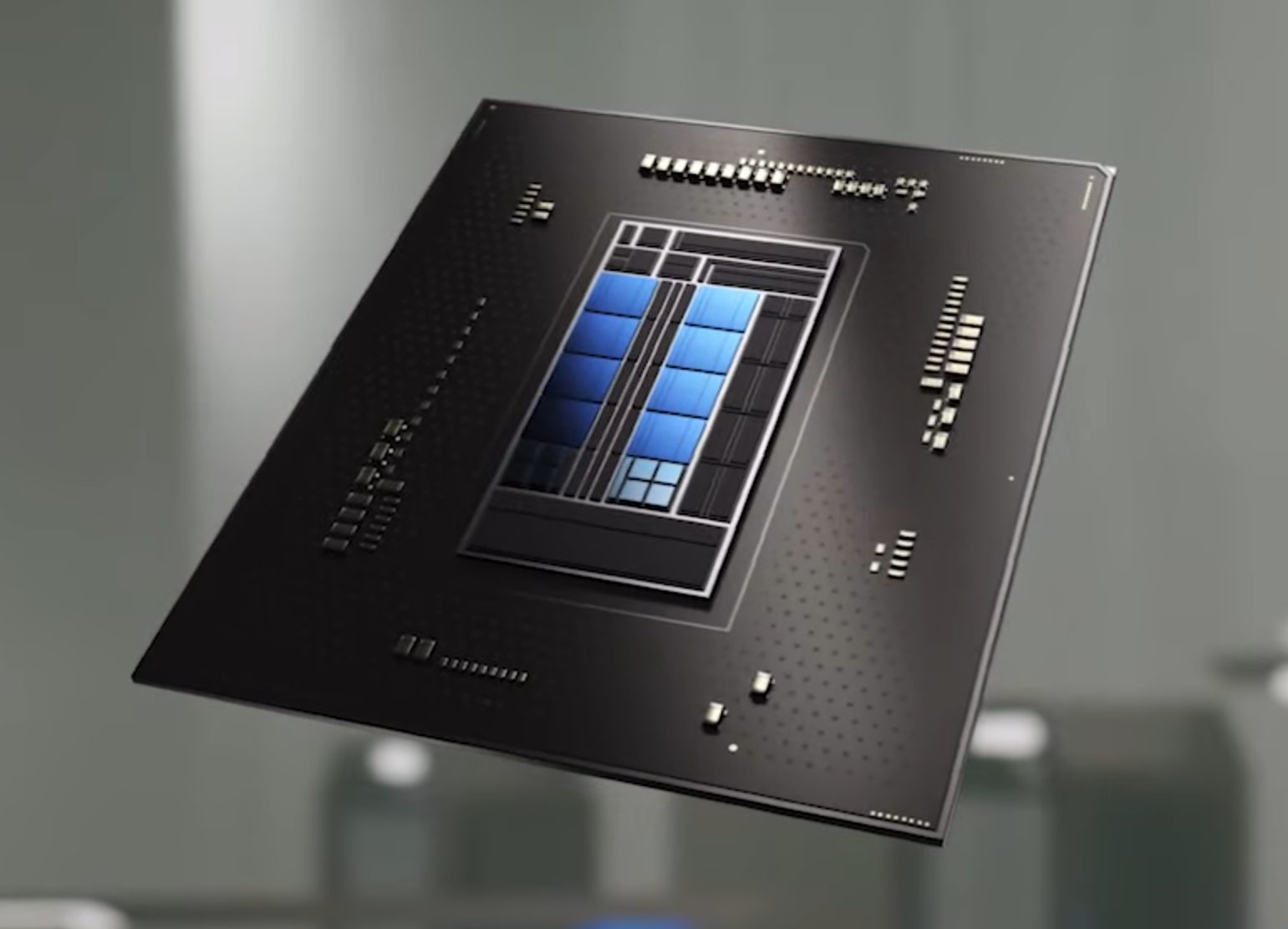 Now before you go on the bandwagon on bashing Intel itself take note that it is not Intel’s fault at all. The issue that arises is mostly due to DRM software and how it works. As you might know or not, Alder Lake has two sets of cores, standard performance cores, and power cores, and with Intel’s Thread Director on-chip right cores will be used for the right tasks, and here lies the issue.
DRM software might detect Thread Director as something suspicious and malicious, and then cut access to the game because of this. Intel, of course, has reached DRM manufacturers and places documentation about how software should be developed with this hybrid technology in mind.
Of course, newer games will be updated if needed and everything will work fine, also games on GOG will work fine because of GOG’s policy of no DRM store but some older ones might be left in limbo. They could work fine but DRM might be triggered and prevent them from loading, usually, game developer itself removes DRM protection after some time but that is not really always the case and there is a chance that some games might simply just not work on Alder Lake CPU only because of DRM protection.
Now before you go on the bandwagon on bashing Intel itself take note that it is not Intel’s fault at all. The issue that arises is mostly due to DRM software and how it works. As you might know or not, Alder Lake has two sets of cores, standard performance cores, and power cores, and with Intel’s Thread Director on-chip right cores will be used for the right tasks, and here lies the issue.
DRM software might detect Thread Director as something suspicious and malicious, and then cut access to the game because of this. Intel, of course, has reached DRM manufacturers and places documentation about how software should be developed with this hybrid technology in mind.
Of course, newer games will be updated if needed and everything will work fine, also games on GOG will work fine because of GOG’s policy of no DRM store but some older ones might be left in limbo. They could work fine but DRM might be triggered and prevent them from loading, usually, game developer itself removes DRM protection after some time but that is not really always the case and there is a chance that some games might simply just not work on Alder Lake CPU only because of DRM protection.


 In order to make a keyboard shortcut for the desired folder know that it is available only when you have a shortcut of the desired folder, it cannot be done on the folder itself, only on its shortcut. Now folder shortcut does not need to reside on desktop, you can place it anywhere you like, but it must be a shortcut.
So the first step is of course to make a shortcut of the folder that you wish to have access via keyboard key combination and place it where you wish.
Once you have done this step, right-click on it and choose properties. Inside properties at the top click on the Shortcut tab and then inside Shortcut Key, press the key combination that you wish to associate with this folder. Confirm with OK and start using fast folder access with your desired key combination.
In order to make a keyboard shortcut for the desired folder know that it is available only when you have a shortcut of the desired folder, it cannot be done on the folder itself, only on its shortcut. Now folder shortcut does not need to reside on desktop, you can place it anywhere you like, but it must be a shortcut.
So the first step is of course to make a shortcut of the folder that you wish to have access via keyboard key combination and place it where you wish.
Once you have done this step, right-click on it and choose properties. Inside properties at the top click on the Shortcut tab and then inside Shortcut Key, press the key combination that you wish to associate with this folder. Confirm with OK and start using fast folder access with your desired key combination.  Microsoft wants to escalate the situation from Australia to the EU, what a surprise.
Hello all and welcome to another news article, this time we are focusing on Microsoft pushing the EU to accept law proposition from Australia.
For all of you who are not familiar with the given situation let me quickly explain. The feud began when the Australian government proposed a new law that targeted Facebook and Google specifically. The government said that it believed that both of the tech giants were using content from news outlets without paying.
Have you ever seen the little news snippets that Google or Facebook sometimes show its users to keep them up to date? These are lifted directly from news websites, and the Australian government claimed that this practice meant that people didn't bother visiting the news website. This then staved news websites of revenue.
As such, the government put forward a new law that would mean Google and Facebook would have to pay the source website for every time they displayed a news snippet. Facebook responded by removing its Australian news coverage in light of the law.
Google, however, put up a fight. It argued that its snippets encouraged people to click on it to read more, thus driving more traffic to the news website. It also said that such a law would be too expensive to maintain in the long run.
As such, Google threatened to remove itself from Australia if the law passed. This was likely a scare tactic, as 95 percent of Australian web users use Google; however, it actually opened the door for its rival, Microsoft.
Microsoft saw how it could push its own search engine BING to replace google. It of course went and reached the Australian government to assure them that BING is more than capable to fulfill its needs and fully abide by the proposed law.
Now Microsoft knows that if this law passes it could see a similar situation happening in Europe and it is pushing it. US News reported on how Microsoft plans to encourage EU countries to adopt this new law too. The company has teamed up with the European Publishers Council and News Media Europe to make the following statement:
Publishers might not have the economic strength to negotiate fair and balanced agreements with these gatekeeper tech companies, who might otherwise threaten to walk away from negotiations or exit markets entirely
Microsoft wants to escalate the situation from Australia to the EU, what a surprise.
Hello all and welcome to another news article, this time we are focusing on Microsoft pushing the EU to accept law proposition from Australia.
For all of you who are not familiar with the given situation let me quickly explain. The feud began when the Australian government proposed a new law that targeted Facebook and Google specifically. The government said that it believed that both of the tech giants were using content from news outlets without paying.
Have you ever seen the little news snippets that Google or Facebook sometimes show its users to keep them up to date? These are lifted directly from news websites, and the Australian government claimed that this practice meant that people didn't bother visiting the news website. This then staved news websites of revenue.
As such, the government put forward a new law that would mean Google and Facebook would have to pay the source website for every time they displayed a news snippet. Facebook responded by removing its Australian news coverage in light of the law.
Google, however, put up a fight. It argued that its snippets encouraged people to click on it to read more, thus driving more traffic to the news website. It also said that such a law would be too expensive to maintain in the long run.
As such, Google threatened to remove itself from Australia if the law passed. This was likely a scare tactic, as 95 percent of Australian web users use Google; however, it actually opened the door for its rival, Microsoft.
Microsoft saw how it could push its own search engine BING to replace google. It of course went and reached the Australian government to assure them that BING is more than capable to fulfill its needs and fully abide by the proposed law.
Now Microsoft knows that if this law passes it could see a similar situation happening in Europe and it is pushing it. US News reported on how Microsoft plans to encourage EU countries to adopt this new law too. The company has teamed up with the European Publishers Council and News Media Europe to make the following statement:
Publishers might not have the economic strength to negotiate fair and balanced agreements with these gatekeeper tech companies, who might otherwise threaten to walk away from negotiations or exit markets entirely 