Portable small Bluetooth speakers are nothing new on the market, most of the time they have given the opportunity for music listening during picnics and walks in nature and also replaced some car speaker systems. The latest star in small portable speakers in JBL Clip 4, small in size, waterproof, and with an incredible high-quality sound.

Performance and quality
Out of the box and after first look speaker looks great, it has excellent design and is very intuitive to work with. Everything is laid out logically and you can start using it right away without reading instructions.
The sound quality is surprisingly very good and clear. I must say I have not expected this clarity and power from a speaker of this size. The volume range is also incredibly good and will fill most needs even on small picnics outdoors where you can hear it loud enough. One thing to mention is that even on their loudness levels sound is still clear without distortion which, to be honest, is to be expected from someone like JBL.
Where you can take JBL Clip 4
You can take it where ever you want, Its size and clip make it perfect for beach and pool trips. Speaker is waterproof and gas IP67 rating, meaning that sand and dirt will not affect it either. Do not take this speaker to your diving adventures since that will break it but a depth around 1 meter underwater should be safe. After your trip do not forget to wash Clip 4 with clean water so all dirt, salt, and other stuff are properly cleaned for longer life of the device.
How long it will play?
JBL claims that the battery will last 10 hours of continuous play. Note that this is meant probably on the largest volume setting so when you use it on lower settings battery is lasting longer. Playing of course on low volumes will extend playback time even longer but here we come at one feature that I do not like, there is no indication of any kind how much battery is left in the speaker, the only indication is a red light when the battery is almost empty which means you could be outside at that point and did not know that low battery was there in the first place when you were packing. Some battery indication would be a great addon.
More stability for JBL Clip 4
The clip itself has been improved from the previous Clip 3 model, it is wider, it goes all the way around the casing, and feels overall better and more stable. Since the clip is now all around casing this means a wider opening can be made making it fit around stuff Clip 3 was not able to.
Conclusion
All in all, Clip 4 is an incredible speaker and one that would highly recommend, the price goes around 79 USD but it can be found even as low as 50 USD on discounts and promotions and if you manage to get one at that price it is a great buy. Sound is good, portability is great, dirt and waterproof are excellent and battery life is really good.



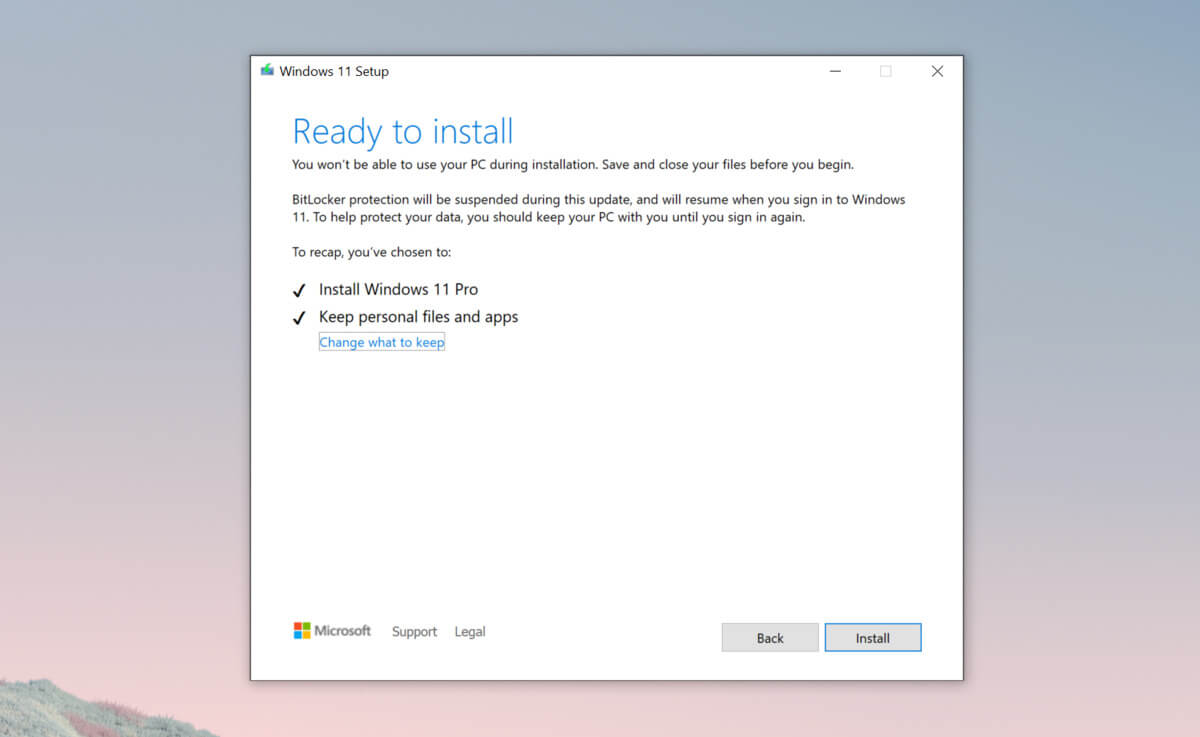 Bypass TPM with changing installation media
Bypass TPM with changing installation media