This toolbar/web browser extension is ad/search-supported that is typically installed as an optional offer, users generally have this bundled with 3rd party software. During setup, this toolbar will modify the home page and new tab pages to the affiliate search portal MyWay.com using a primary search engine to collect shared search revenue. It will also modify the default search provider as well.
While this extension is installed users will experience a display of additional ads and sponsored content throughout their browsing sessions, as well as the possibility of pop-up ads.
Several anti-virus scanners have marked this extension as a Browser Hijacker and it is recommended to remove it from your computer.
About Browser Hijackers
Browser hijacking means that a malicious code has taken control over and altered the settings of your internet browser, without your consent. They are designed to interfere with browser programs for a variety of purposes. Usually, it’ll drive users to predetermined websites that are looking to increase their advertising campaign income. Though it may seem naive, all browser hijackers are damaging and thus always regarded as security risks. In a worst-case scenario, your internet browser can be hijacked to download malicious software that can do a great deal of damage to your laptop or computer.
How to know if your internet browser has been hijacked
The common symptoms that indicate having this malicious software on your PC are:
1. home page is modified
2. bookmark and the new tab are likewise modified
3. default online search engine is changed
4. you’re getting new toolbars you have never found before
5. your internet browser displays endless pop-up ads
6. your web browser has become unstable or starts running slowly
7. you can’t visit certain websites like homepages of anti-malware software.
Exactly how browser hijacker finds its way onto your computer system
Browser hijackers can enter a computer by some means or other, including via downloads, file sharing, and e-mail also. They may also come from any BHO, extension, add-on, toolbar, or plug-in with malicious intent. Browser hijackers sneak into your pc in addition to free software application downloads that you unintentionally install alongside the original. Some of the most popular hijackers are MyImageConverter, Conduit Search, Babylon Toolbar, Sweet Page, OneWebSearch, and CoolWebSearch.
Learn how to get rid of browser hijackers
Certain hijackers could be removed by just uninstalling the related freeware or add-ons through the Add or Remove Programs in the Windows control panel. In some cases, it could be a difficult job to find and remove the malicious piece because the associated file could be running as part of the operating system process. Besides, browser hijackers can modify the Windows registry so it can be quite tough to restore all the values manually, especially when you are not a very tech-savvy person.
You can choose automatic browser hijacker removal by just installing and running an efficient anti-malware program. SafeBytes Anti-Malware detects all types of hijackers – including MyImageConverter – and eliminates every trace quickly and efficiently. In addition to anti-virus software, a PC optimizer program, like Total System Care, can help you fix Windows registry errors, remove unwanted toolbars, secure your internet privacy, and boost overall computer performance.
What to Do if Virus Stops You From Downloading Or Installing Antivirus?
Practically all malware is bad, but certain types of malware do much more damage to your PC than others. Some malware variants alter web browser settings by adding a proxy server or change the PC’s DNS configuration settings. In such cases, you’ll be unable to visit some or all of the websites, and therefore not able to download or install the required security software to clear out the computer virus. If you are reading this now, you might have perhaps realized that virus infection is a reason behind your blocked net connectivity. So how to proceed if you need to install an anti-virus software like Safebytes? Follow the instructions below to remove malware by alternate methods.
Download the software in Safe Mode with Networking
The Windows operating system comes with a special mode referred to as “Safe Mode” in which only the minimum required programs and services are loaded. In the event the malware is blocking internet connection and affecting your computer, running it in Safe Mode enables you to download anti-virus and run a diagnostic scan whilst limiting potential damage. To get into Safe Mode or Safe Mode with Networking, press F8 while the system is booting up or run MSCONFIG and locate the “Safe Boot” options in the “Boot” tab. Once you are in safe mode, you can try to install your anti-malware application without the hindrance of the malware. Now, you can run the antivirus scan to get rid of viruses and malware without hindrance from another malicious application.
Download the security software using an alternate internet browser
Some malware only targets particular web browsers. If this sounds like your situation, utilize another web browser as it might circumvent the virus. If you seem to have a trojan attached to Internet Explorer, then switch to an alternate web browser with built-in safety features, such as Firefox or Chrome, to download your preferred anti-malware program – Safebytes.
Install anti-malware on a USB drive
Another option would be to make a portable antivirus program on your USB flash drive. To run anti-malware from a USB pen drive, follow these simple measures:
1) On a virus-free computer, download and install Safebytes Anti-Malware.
2) Plug the USB drive into the clean computer.
3) Double-click on the downloaded file to open the installation wizard.
4) Select the drive letter of the flash drive as the location when the wizard asks you exactly where you want to install the antivirus. Follow the on-screen instructions to finish the installation process.
5) Transfer the flash drive from the uninfected computer to the infected computer.
6) Double-click the Safebytes Anti-malware icon on the USB drive to run the software.
7) Hit the “Scan” button to run a full computer scan and remove viruses automatically.
Protect Your PC and Privacy With SafeBytes Anti-Malware
Are you looking to install the best anti-malware software program for your PC? You can find many applications on the market which come in free and paid versions for Windows systems. A few of them do a great job in eradicating malware threats while some will affect your PC themselves. You should look for a product that has obtained a good reputation and detects not only viruses but other types of malware as well. While considering the highly regarded applications, Safebytes AntiMalware is certainly the highly recommended one.
SafeBytes anti-malware is trustworthy software that not only secures your PC completely but is also quite user-friendly for people of all ability levels. Through its cutting-edge technology, this software will help you protect your computer against infections caused by various kinds of malware and similar internet threats, including adware, spyware, viruses, worms, trojans, keyloggers, ransomware, and potentially unwanted program (PUPs).
SafeBytes anti-malware offers an array of advanced features which sets it aside from all others. Let’s take a look at a few of them below:
Real-time Threat Response: SafeBytes provides real-time active supervision and protection from all known computer viruses and malware. It’ll inspect your personal computer for suspicious activity regularly and its unrivaled firewall protects your computer from illegal access by the outside world.
World-class AntiMalware Protection: Using a critically acclaimed anti-malware engine, SafeBytes offers multilayered protection which is designed to catch and get rid of viruses and malware that are hidden deep inside your computer’s operating system.
Web protection: SafeBytes inspects the hyperlinks present on a webpage for possible threats and notifies you if the site is safe to visit or not, through its unique safety ranking system.
Light-weight: This application is not “heavy” on the computer’s resources, so you’ll not see any performance troubles when SafeBytes is working in the background.
24/7 Customer Support: Support service is readily available 24 x 7 x 365 days through email and chats to answer your concerns.
SafeBytes has developed a great anti-malware solution to help you conquer the latest malware threats and virus attacks. You can be sure that your computer will be protected in real-time once you put this tool to use. So if you’re looking for the absolute best malware removal application out there, and if you don’t mind paying out a few bucks for it, opt for SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
To get rid of MyImageConverter manually, navigate to the Add or Remove programs list in the Control Panel and choose the program you want to get rid of. For web browser extensions, go to your browser’s Addon/Extension manager and choose the plug-in you intend to disable or remove. You may also want to reset your home page and search engine providers, and also delete temporary files, browsing history, and cookies.
If you opt to manually delete the system files and Windows registry entries, utilize the following checklist to make sure you know precisely what files to remove before performing any actions. But bear in mind, editing the Windows registry is usually a difficult task that only advanced users and professionals should attempt to fix the problem. In addition, some malware is capable of replicating or preventing removal. It is highly recommended that you carry out the removal procedure in Windows Safe Mode.
 Valve has announced the first gaming PC handheld console: Steam Deck. At its core, Stead Deck is just a portable, small PC in little casing. It uses AMD Zen 2 CPU and RDNA 2 GPU architecture, has 16GB of RAM, Wi-Fi, and Bluetooth.
It is a portable device with both a touchpad and joystick packing a seven-inch screen with a resolution of 1280x800 (16:10 aspect ratio). The screen has an ambient light sensor for automatic light adjustments same as your modern mobile device.
Stating to Valve battery will hold up from two to eight hours depending on the activity of the user and what exactly he is doing. The handheld comes also with a carrying case.
Valve has announced the first gaming PC handheld console: Steam Deck. At its core, Stead Deck is just a portable, small PC in little casing. It uses AMD Zen 2 CPU and RDNA 2 GPU architecture, has 16GB of RAM, Wi-Fi, and Bluetooth.
It is a portable device with both a touchpad and joystick packing a seven-inch screen with a resolution of 1280x800 (16:10 aspect ratio). The screen has an ambient light sensor for automatic light adjustments same as your modern mobile device.
Stating to Valve battery will hold up from two to eight hours depending on the activity of the user and what exactly he is doing. The handheld comes also with a carrying case.

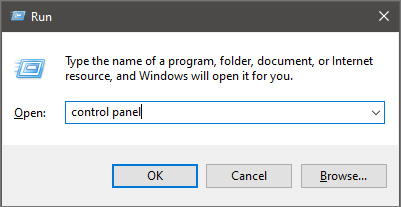
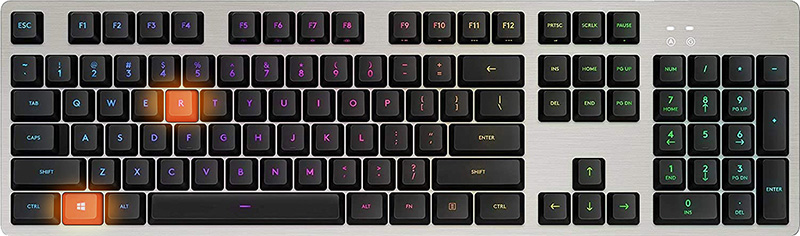 Once run dialog is shown type in it control panel as shown in the picture and press OK
Once run dialog is shown type in it control panel as shown in the picture and press OK
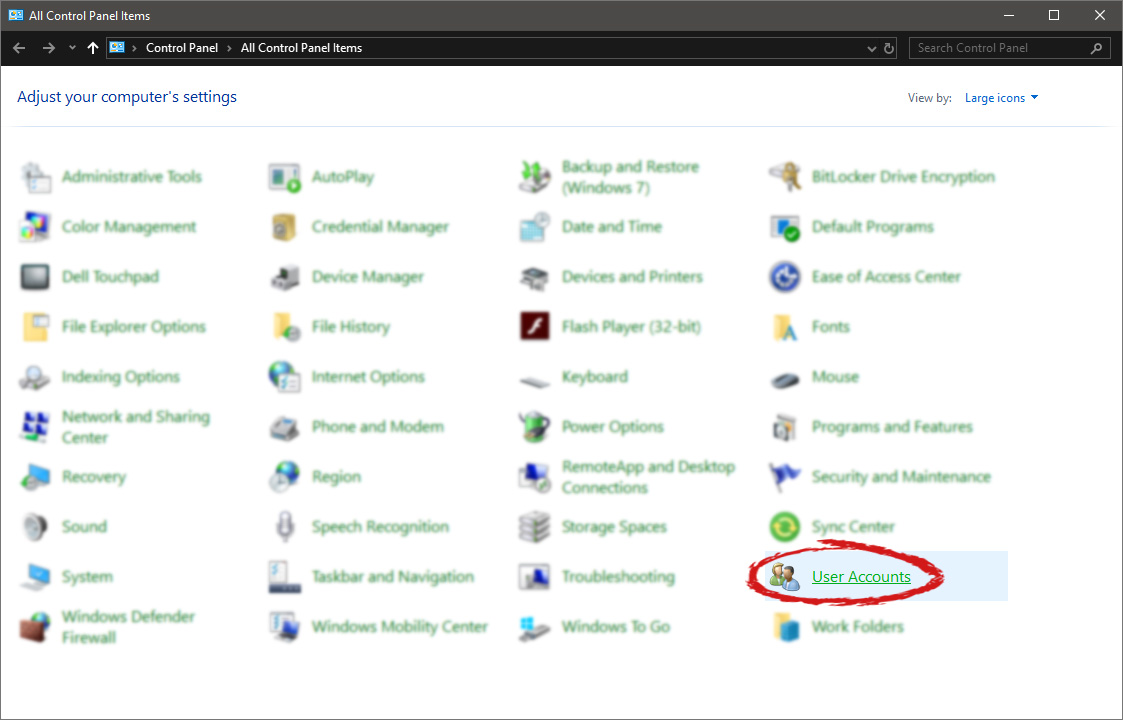
 If you have followed the steps precisely, you should be now in the control panel of Windows 10. Click on the top-right view and choose large icons. The Control panel will switch to a grid-like view, in the current view go to the far-right and almost bottom icon where it says User Accounts and click on it.
If you have followed the steps precisely, you should be now in the control panel of Windows 10. Click on the top-right view and choose large icons. The Control panel will switch to a grid-like view, in the current view go to the far-right and almost bottom icon where it says User Accounts and click on it.
 User account settings
User account settings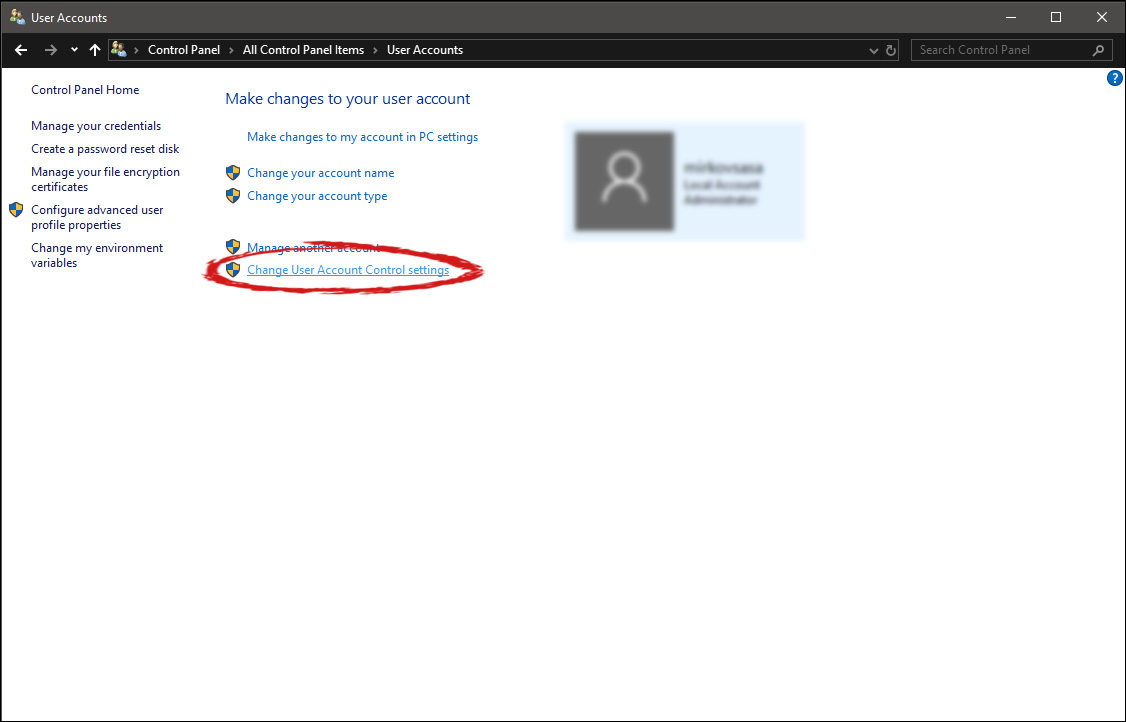 Once you click on the link you will be presented with a User account control slider on the left and a brief explanation on the right
Once you click on the link you will be presented with a User account control slider on the left and a brief explanation on the right
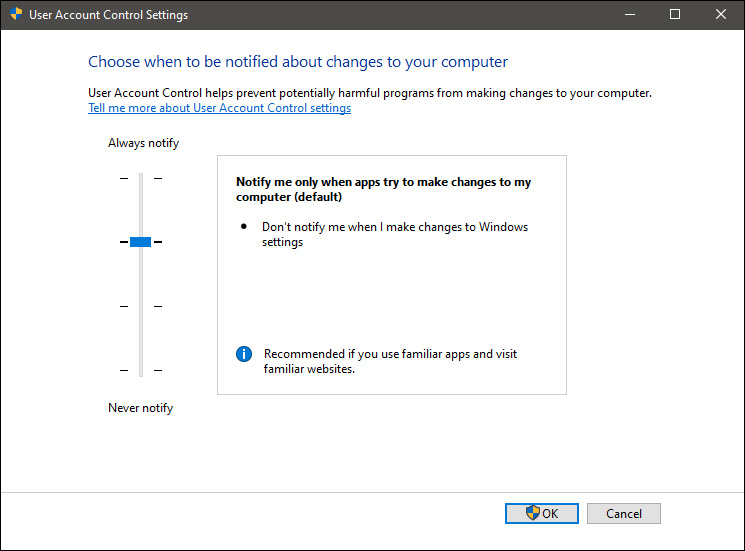 Here in the picture, we see Windows default setting and an explanation of when and how he will notify you. If you wish to turn all notifications linked to programs changing computer or you making windows changes, click on the left slider and bring it all the way to the bottom where it says never notify me. If you prefer some notifications try to find which of the remaining 3 settings best suit your needs. Once you are done and satisfied with your choice click on OK.
Here in the picture, we see Windows default setting and an explanation of when and how he will notify you. If you wish to turn all notifications linked to programs changing computer or you making windows changes, click on the left slider and bring it all the way to the bottom where it says never notify me. If you prefer some notifications try to find which of the remaining 3 settings best suit your needs. Once you are done and satisfied with your choice click on OK.  The true cause is that there is no working Border Gateway Protocol (BGP) routes into Facebook's sites. BGP is the standardized exterior gateway protocol used to exchange routing and reachability information between the internet top-level autonomous systems (AS). Most people, indeed most network administrators, never need to deal with BGP.
Cloudflare VP Dane Knecht was the first to report the underlying BGP problem. This meant, as Kevin Beaumont, former Microsoft's Head of Security Operations Centre, tweeted,
"By not having BGP announcements for your DNS name servers, DNS falls apart = nobody can find you on the internet. Same with WhatsApp btw. Facebook has basically de-platformed themselves from their own platform."
Many people are very annoyed by this and with the fact that they cannot use their social media platforms but it seems that Facebook employees are in even bigger annoyance as it was reported that Facebook employees can't enter their buildings because their "smart" badges and doors were also disabled by this network failure. If true, Facebook's people literally can't enter the building to fix things.
Reddit user u/ramenporn, who claimed to be a Facebook employee working on bringing the social network back from the dead, reported, before he deleted his account and his messages:
"DNS for FB services has been affected and this is likely a symptom of the actual issue, and that's that BGP peering with Facebook peering routers has gone down, very likely due to a configuration change that went into effect shortly before the outages happened (started roughly 1540 UTC). There are people now trying to gain access to the peering routers to implement fixes, but the people with physical access is separate from the people with knowledge of how to actually authenticate to the systems and people who know what to actually do, so there is now a logistical challenge with getting all that knowledge unified. Part of this is also due to lower staffing in data centers due to pandemic measures."
Ramenporn also stated that it wasn't an attack, but a mistaken configuration change made via a web interface.
Both BGP and DNS are down, the "connection to the outside world is down, remote access to those tools don't exist anymore, so the emergency procedure is to gain physical access to the peering routers and do all the configuration locally."
Technicians on site don't know how to do that and senior network administrators aren't on site.
It seems that it will all be down for a couple of more hours before the issue is resolved.
The true cause is that there is no working Border Gateway Protocol (BGP) routes into Facebook's sites. BGP is the standardized exterior gateway protocol used to exchange routing and reachability information between the internet top-level autonomous systems (AS). Most people, indeed most network administrators, never need to deal with BGP.
Cloudflare VP Dane Knecht was the first to report the underlying BGP problem. This meant, as Kevin Beaumont, former Microsoft's Head of Security Operations Centre, tweeted,
"By not having BGP announcements for your DNS name servers, DNS falls apart = nobody can find you on the internet. Same with WhatsApp btw. Facebook has basically de-platformed themselves from their own platform."
Many people are very annoyed by this and with the fact that they cannot use their social media platforms but it seems that Facebook employees are in even bigger annoyance as it was reported that Facebook employees can't enter their buildings because their "smart" badges and doors were also disabled by this network failure. If true, Facebook's people literally can't enter the building to fix things.
Reddit user u/ramenporn, who claimed to be a Facebook employee working on bringing the social network back from the dead, reported, before he deleted his account and his messages:
"DNS for FB services has been affected and this is likely a symptom of the actual issue, and that's that BGP peering with Facebook peering routers has gone down, very likely due to a configuration change that went into effect shortly before the outages happened (started roughly 1540 UTC). There are people now trying to gain access to the peering routers to implement fixes, but the people with physical access is separate from the people with knowledge of how to actually authenticate to the systems and people who know what to actually do, so there is now a logistical challenge with getting all that knowledge unified. Part of this is also due to lower staffing in data centers due to pandemic measures."
Ramenporn also stated that it wasn't an attack, but a mistaken configuration change made via a web interface.
Both BGP and DNS are down, the "connection to the outside world is down, remote access to those tools don't exist anymore, so the emergency procedure is to gain physical access to the peering routers and do all the configuration locally."
Technicians on site don't know how to do that and senior network administrators aren't on site.
It seems that it will all be down for a couple of more hours before the issue is resolved. 