The Motitags toolbar browser add-on was created by Mindspark Inc. and is compatible with Internet Explorer and Mozilla Firefox. It claims to enhance users’ Internet browsing experience by enabling smileys within popular email clients such as Gmail, Yahoo!, AOL, and Outlook Live. While such added functionality may seem useful, Internet users should be aware that this browser plugin is categorized as a Browser Hijacker due to its behavior.
When installed this extension changes your default search engine, the home page, and new tab to MyWay.com, and while installed it gathers user browsing data and sends it back to Mindspark servers. This data is later used to inject additional unwanted ads into the user’s browser search results.
About Browser Hijackers
Browser hijacking is actually a type of unwanted software program, often a web browser add-on or extension, which then causes modifications in the web browser’s settings. Browser hijacker malware is developed for a number of reasons. These are generally used to force hits to a specific website, manipulating web traffic to generate ad revenue. It could seem harmless, but the majority of these websites aren’t legitimate and could pose a serious threat to your online safety. In a much worst case, your internet browser could be hi-jacked to open up your computer to a host of additional computer infections.
How one can identify a browser hijack
There are several signs of browser hijacking. Here are a few of them: the home page of your browser is changed unexpectedly; you get re-directed to websites you never intended to visit; the essential web browser settings are altered and unwanted or unsafe resources are added to the trusted websites list; discover new toolbars that you didn’t add; endless pop-up adverts show up and/or your web browser popup blocker is disabled; your browser gets sluggish, buggy, crashes frequently; you can’t navigate to certain internet pages, for example, security software related websites.
So how does a browser hijacker infect a computer?
Browser hijackers infect computers via malicious email attachments, downloaded infected files, or by going to infected sites. Many internet browser hijackings come from add-on software, i.e., toolbars, browser helper objects (BHO), or plug-ins added to browsers to provide them extra capabilities. Browser hijackers sneak into your pc in addition to free software application downloads that you unwittingly install along with the original. An example of some infamous browser hijacker includes Babylon, Anyprotect, Conduit, SweetPage, DefaultTab, RocketTab, and Delta Search, but the names are often changing.
Browser hijacking can bring about severe privacy problems and also identity theft, affect your browsing experience by taking control over outgoing traffic, drastically slows down your PC by consuming lots of resources, and result in system instability also.
Getting rid of browser hijackers
Some browser hijacking could be easily stopped by discovering and eliminating the corresponding malware program through your control panel. But, most browser hijackers are difficult to eliminate manually. No matter how much you try to eliminate it, it can return over and over. Rookie PC users should not try for the manual form of removal, since it needs thorough computer knowledge to perform fixes on the system registry and HOSTS file.
Professionals always recommend users to remove any malware including browser hijacker with an automatic removal tool, which is easier, safer, and quicker than the manual removal technique. Safebytes Anti-Malware has a state-of-the-art anti-malware engine that will help you stop browser hijacking in the first place, and clean up any existing issues.
What To Do If You Cannot Download Safebytes Anti-Malware?
Malware could potentially cause all sorts of damage once they invade your computer, starting from stealing your private details to erasing data files on your computer system. Some malware sits in between your computer and your internet connection and blocks some or all sites that you would like to visit. It might also prevent you from installing anything on your PC, particularly anti-virus programs. If you’re reading this, you probably have infected by malware that prevents you from downloading a computer security program such as Safebytes Antimalware on your PC. There are a few options you could try to get around with this particular obstacle.
Install in Safe Mode
If the malware is set to load automatically when Windows starts, entering Safe Mode could block this attempt. Only minimal required programs and services are loaded whenever you start your personal computer in Safe Mode. To start your Windows XP, Vista, or 7 computers in Safe Mode with Networking, please do as instructed below.
1) At power on/start-up, press the F8 key in 1-second intervals. This would conjure up the Advanced Boot Options menu.
2) Choose Safe Mode with Networking with arrow keys and press Enter.
3) When you are into this mode, you will have online access again. Now, get the virus removal application you want by using the web browser. To install the program, follow the directions within the setup wizard.
4) Right after the software is installed, allow the scan run to eliminate viruses and other threats automatically.
Use an alternate web browser to download security software
Malicious code could exploit vulnerabilities on a particular internet browser and block access to all anti-virus software sites. The most effective way to avoid this issue is to choose a web browser that is renowned for its security features. Firefox contains built-in Malware and Phishing Protection to keep you safe online.
Install security software on a USB drive
To effectively eliminate the malware, you need to approach the problem of installing an anti-virus software program on the infected PC from a different angle. Follow these steps to run the antivirus on the affected computer.
1) Download Safebytes Anti-Malware or Microsoft Windows Defender Offline onto a virus-free computer system.
2) Plug the pen drive into the uninfected computer.
3) Double click on the downloaded file to open the installation wizard.
4) Choose the USB stick as the destination for saving the software file. Follow the instructions on the screen to finish up the installation process.
5) Disconnect the flash drive. You may now use this portable anti-malware on the infected computer.
6) Double-click the anti-malware program EXE file on the USB flash drive.
7) Run Full System Scan to detect and get rid of all sorts of malware.
Benefits and Features of SafeBytes Security Suite
To protect your laptop or computer from many different internet-based threats, it is very important to install an anti-malware program on your PC. However, with so many anti-malware companies in the marketplace, nowadays it’s difficult to decide which one you should obtain for your laptop. A few are very good ones, some are ok types, and some are simply just fake anti-malware applications that could damage your computer themselves! When looking for an anti-malware program, pick one which gives reliable, efficient, and total protection against all known viruses and malware. One of the highly recommended software by industry analysts is SafeBytes Anti-Malware, a popular security application for Microsoft Windows.
Safebytes is one of the well-established computer solutions companies, which provide this complete anti-malware software. Using its cutting-edge technology, this application can assist you to eliminate multiples types of malware such as viruses, PUPs, trojans, worms, ransomware, adware, and browser hijackers.
SafeBytes possesses a variety of wonderful features that can help you protect your laptop or computer from malware attack and damage. Below are some typical features found in this application:
World-class AntiMalware Protection: Built upon a greatly acclaimed anti-virus engine, this malware removal application can find and remove numerous stubborn malware threats like browser hijackers, PUPs, and ransomware that other typical anti-virus applications will miss.
Real-time Threat Response: SafeBytes gives complete and real-time security for your computer. They’re extremely effective in screening and getting rid of numerous threats since they’re regularly improved with the latest updates and alerts.
“Fast Scan” Features: Safebytes Anti-Malware, using its enhanced scanning engine, provides ultra-fast scanning which can quickly target any active online threat.
Website Filtering: Through its unique safety ranking, SafeBytes notifies you whether a site is safe or not to visit it. This will ensure that you’re always certain of your online safety when browsing the internet.
Light-weight: The program is lightweight and can run silently in the background, and will not have an effect on your PC efficiency.
24/7 Premium Support: SafeBytes provides you with 24/7 technical support, automatic maintenance, and software upgrades for the best user experience.
Simply put, SafeBytes has developed a meaningful anti-malware solution that is aimed to protect you against various malware. Malware issues can become a thing of the past when you put this tool to use. So if you’re seeking the very best malware removal application out there, and when you don’t mind shelling out a few bucks for it, go for SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove Motitags without using an automated tool, it may be possible to do so by removing the application from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. Additionally, it is advised to factory reset your web browser to its default state to fix corrupt settings.
Finally, check your hard drive for all of the following and clean your computer registry manually to get rid of leftover application entries after uninstalls. Please remember that only advanced users should try to manually edit the system files simply because removing any single vital registry entry leads to a serious issue or even a PC crash. Moreover, certain malicious programs have the capability to defend against its removal. Carrying out this in Safe Mode is recommended.


 The euphoria around Windows 11 is not dying and reveal that Android apps will work natively inside Windows 11 has raised many emotions and questions.
So, Microsoft has announced that Android apps will run natively inside Windows 11 OS and that they will reside alongside your other installed ones as icons, etc.
It is no secret that many users have been using emulation software to run Android apps inside Windows so far, so what is the difference?
The euphoria around Windows 11 is not dying and reveal that Android apps will work natively inside Windows 11 has raised many emotions and questions.
So, Microsoft has announced that Android apps will run natively inside Windows 11 OS and that they will reside alongside your other installed ones as icons, etc.
It is no secret that many users have been using emulation software to run Android apps inside Windows so far, so what is the difference?
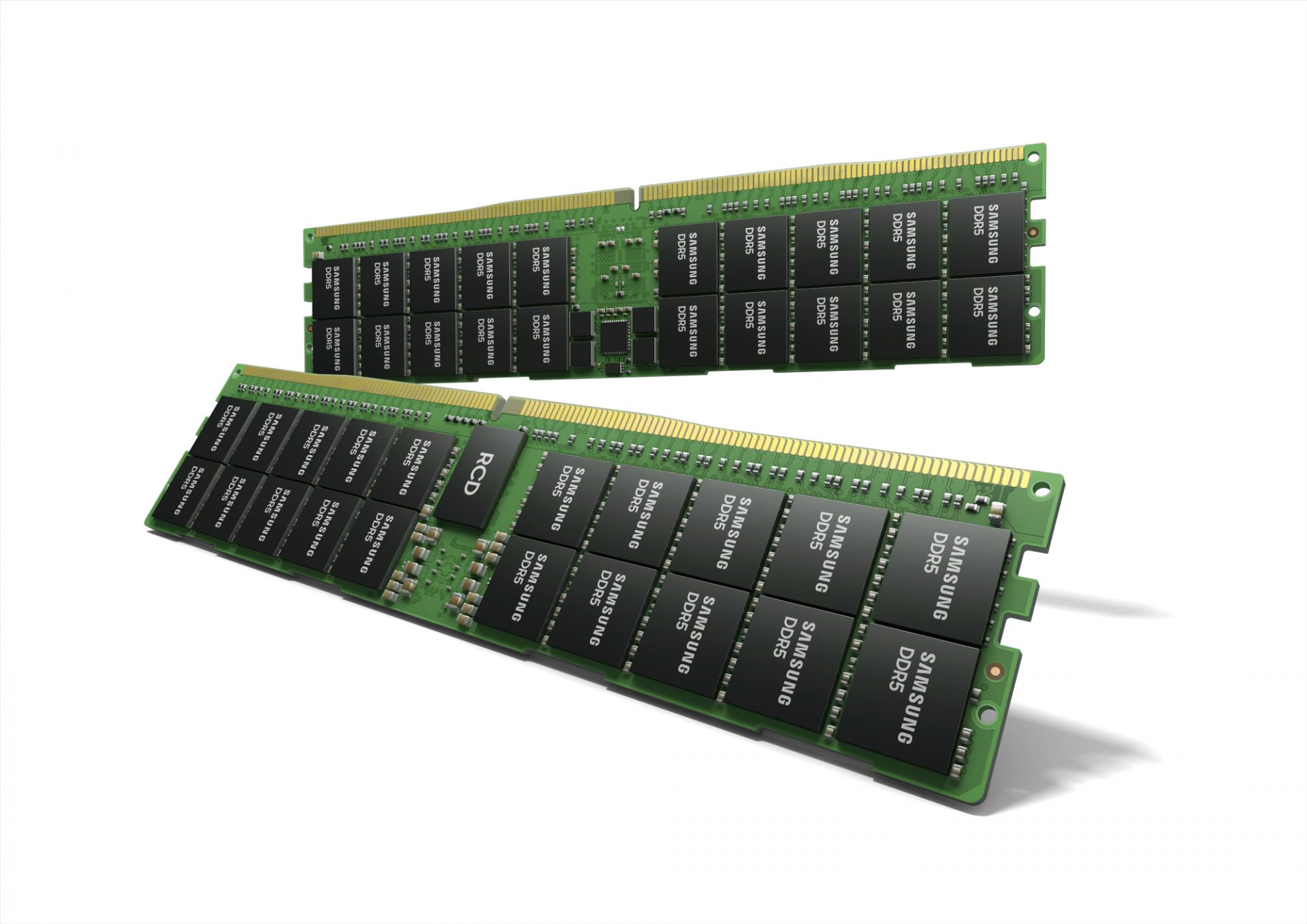 Next-generation of RAM, DDR5 supposed to hit shelves around late summer or fall in 2021if everything goes as planned.
Its goal is to increase speed and efficiency, wants to pack more memory in a single stick, and have better power management.
Next-generation of RAM, DDR5 supposed to hit shelves around late summer or fall in 2021if everything goes as planned.
Its goal is to increase speed and efficiency, wants to pack more memory in a single stick, and have better power management.
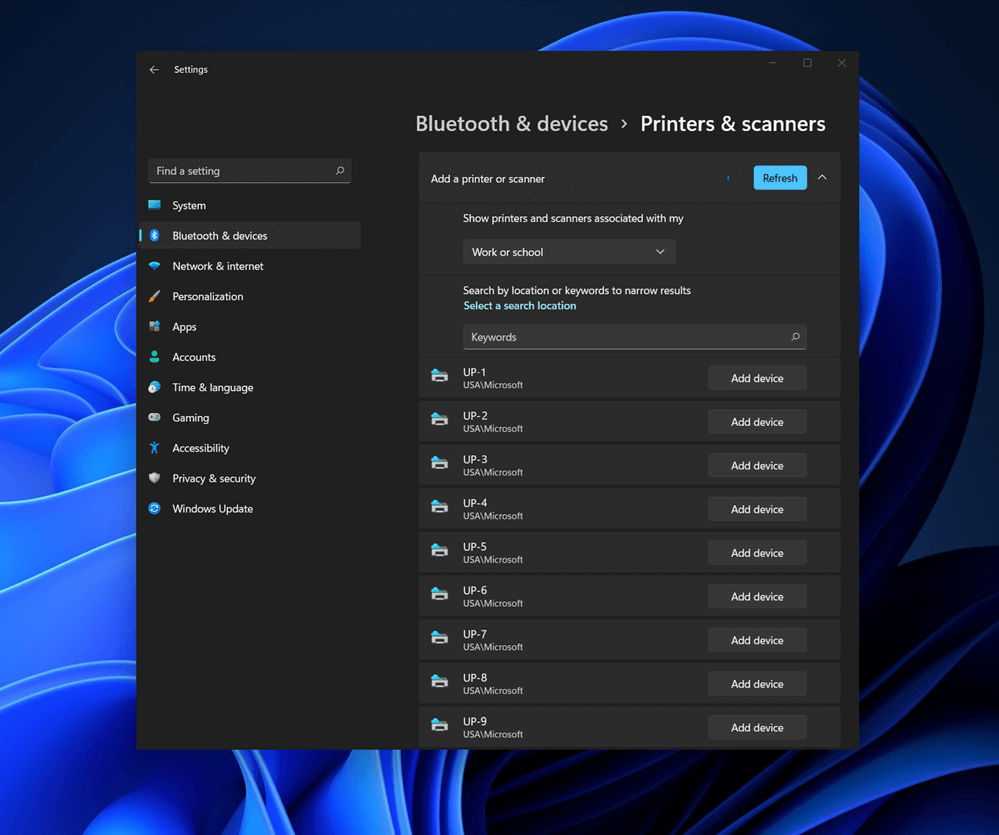 Bluetooth perhaps is slowly becoming an outdated feature but sometimes you can really used it and need it.
By default, in Windows 11 Bluetooth is turned OFF so if you need it, you will need to turn it ON first. Luckily turning it ON is easy and we will guide you through the process
Bluetooth perhaps is slowly becoming an outdated feature but sometimes you can really used it and need it.
By default, in Windows 11 Bluetooth is turned OFF so if you need it, you will need to turn it ON first. Luckily turning it ON is easy and we will guide you through the process
