Code 33 - What is it?
Code 33 is a typical Device Manager error. This error code occurs when Windows is unable to start a device that you are trying to use on your PC. The error code 33 is usually displayed in the following format:
“Windows cannot determine which resources are required for this device. Code 33”
Solution
 Error Causes
Error Causes
Error code 33 may be triggered due to two reasons. One reason can be the translator's failure to find the correct resource for the device driver.
And since this error code is associated with the Device Manager, another reason can be an outdated or corrupted device driver. In most cases, the underlying problem for Device Manager error code is outdated/corrupted drivers.
The good news is that Device Manager error code 33 is not detrimental. However, if the error is not resolved timely, it can lower the functionality and the performance of your PC. You may not be able to use the hardware device.
Further Information and Manual Repair
To resolve code 33, you don’t need to be technically sound or hire a professional computer programmer. Just like any other Device Manager error code, code 33 is also easy to repair.
To help you fix this issue on your system, below are some of the best, easy, and effective DIY solutions.
Method 1 - Configure Hardware Device
Properly configure the problematic hardware device to fix error code 33. It is important to understand that when you install a device that is not plug-and-play, the resource settings are not configured automatically.
This means for such devices you will have to perform device configuration manually.
For device configuration, here’s what you should do:
- Go to the start menu
- Click Control Panel, then click Performance and Maintenance, and then System
- Now on the hardware tab, click on Device Manager and then double click the device you wish to configure
- Click the resources tab and then click on the check box next to the Use Automatic Setting
- After that click, the ‘Setting Based On’ and then click the hardware configuration you wish to change
- Press the ‘Resource Type’ you will like to configure in the ‘Resource Settings’ box
- Now go to the Change Settings tab and type a new value for the Resource Type
Method 2 - Update the Problematic Drivers
Code 33 can also be generated due to driver problems. In such a scenario, it is recommended to update the outdated or corrupted drivers.
Identifying all problematic drivers and updating them individually can be frustrating and time-consuming. Therefore to save time and avoid the hassle involved in updating drivers manually, it is advisable to download DriverFIX.
Method 3 - Download DriverFIX to Update Drivers Automatically
DriverFIX is a next-generation and user-friendly program compatible with all Windows versions.
This software is exclusively designed to repair and resolve device driver-related problems and error codes.
Once installed, its intelligent and intuitive programming system detects all outdated, corrupted, and misconfigured device drivers on your PC. It automatically updates all the problematic drivers in a few seconds. It makes sure that the driver versions are the latest and compatible with your operating system.
Furthermore, it also ensures that drivers are continuously updated whenever new versions are available. So, you don’t have to worry about keeping device drivers up to date.
Click here to download DriverFIX to resolve Device Manager error code 33 today!
 Microsoft office has two major packages, an online one, and an offline version. The online version of the course is Office 365 that requires a monthly subscription and it is always regularly updated and maintained. Another version is more of a typical old school application, install it and use it, no constant internet connection is required and no monthly subscription is required, buy once and use it.
The last version of buying it once and use it was Office 2019 and after two years we are going to receive a new version soon. Microsoft has set its release date for October 5th of this year and as always it will feature the current latest version of office applications and one-time purchase.
The new office will support dark mode and other improvements tied to the new Windows 11 and some specific features tied to Office itself.
Microsoft office has two major packages, an online one, and an offline version. The online version of the course is Office 365 that requires a monthly subscription and it is always regularly updated and maintained. Another version is more of a typical old school application, install it and use it, no constant internet connection is required and no monthly subscription is required, buy once and use it.
The last version of buying it once and use it was Office 2019 and after two years we are going to receive a new version soon. Microsoft has set its release date for October 5th of this year and as always it will feature the current latest version of office applications and one-time purchase.
The new office will support dark mode and other improvements tied to the new Windows 11 and some specific features tied to Office itself. 







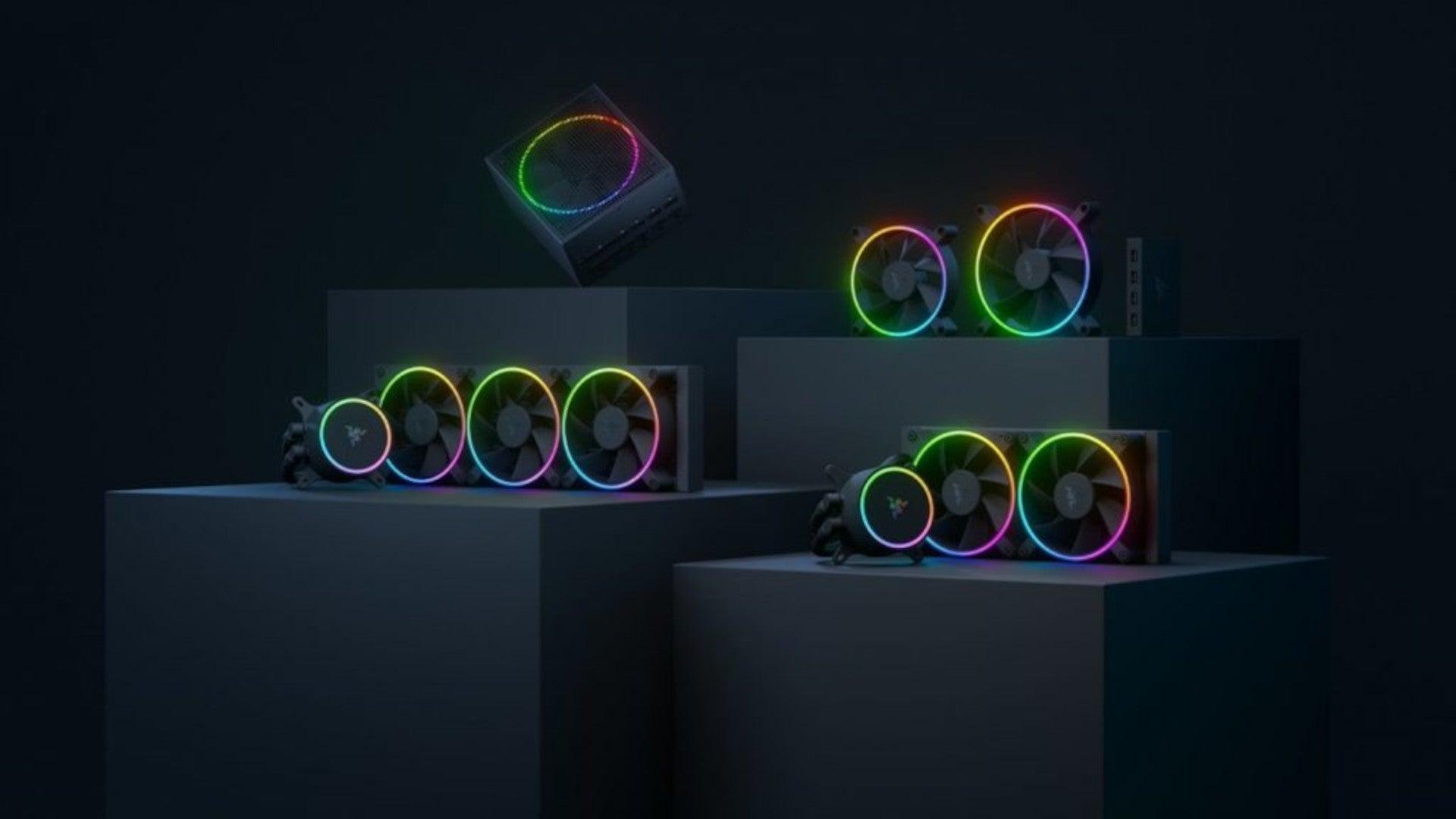 Razer is a well-known brand among PC gamers and users, it started as a peripheral manufacturer focused on keyboards and mouse but after years passed Razer expanded its inventory offerings. It soon started offering headphones and lately has branched into wider product lines like gaming chairs and protection masks.
It is not a big surprise that Razer is expanding into other branches of the PC industry. This time, however, it has revealed not one but three new hardware for your PC. Case fans, all in one liquid cooler and power supply.
There are not many details about the products themselves but one thing is one hundred percent confirmed, they come with Razer Chroma, all of them, even the fans.
Razer is a well-known brand among PC gamers and users, it started as a peripheral manufacturer focused on keyboards and mouse but after years passed Razer expanded its inventory offerings. It soon started offering headphones and lately has branched into wider product lines like gaming chairs and protection masks.
It is not a big surprise that Razer is expanding into other branches of the PC industry. This time, however, it has revealed not one but three new hardware for your PC. Case fans, all in one liquid cooler and power supply.
There are not many details about the products themselves but one thing is one hundred percent confirmed, they come with Razer Chroma, all of them, even the fans.
 Most interesting for me personally is Razers Katana, the power supply unit. It is a modular power supply ranging from 750W to 1200W with the additional option of Titanium rated one with an impressive 1600W of power. Power supply will start shipping in early 2022 and at the time of writing this article no price range has been released.
Most interesting for me personally is Razers Katana, the power supply unit. It is a modular power supply ranging from 750W to 1200W with the additional option of Titanium rated one with an impressive 1600W of power. Power supply will start shipping in early 2022 and at the time of writing this article no price range has been released.
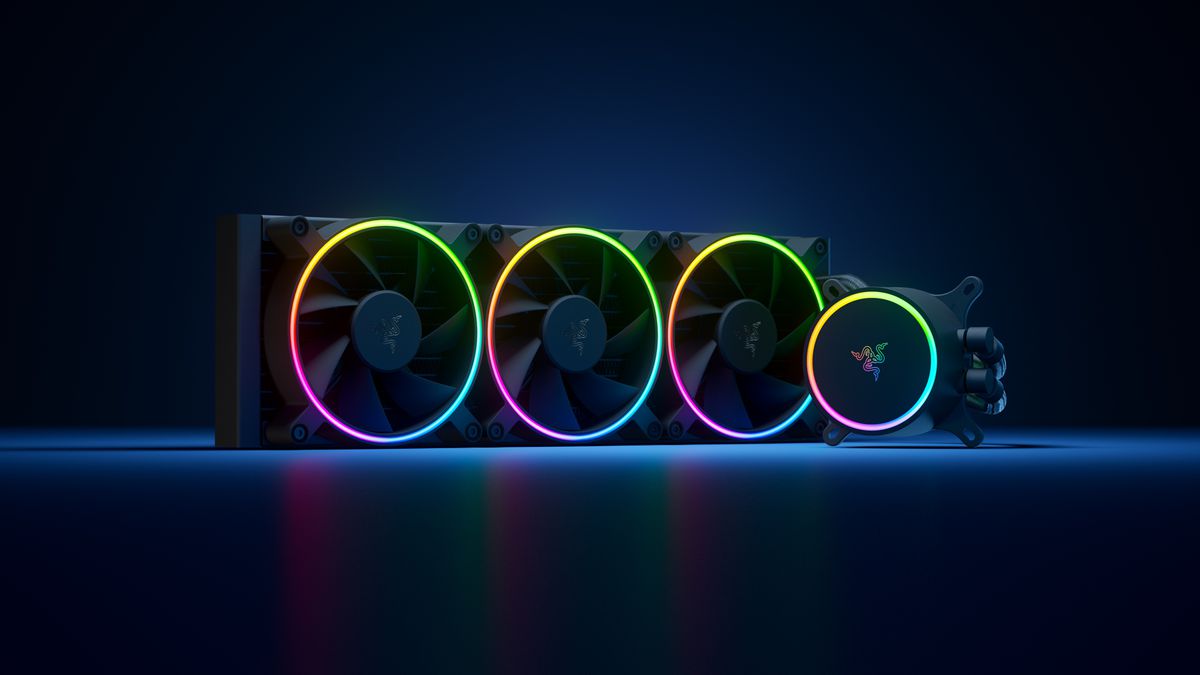 Hanbo liquid cooler will feature an optimized intake design so it can ensure greater heat transfer and fluid dynamic for improved reliability and silent operation. Radiator comes in 240mm size with two fans and a larger one of 360mm with three fans. The pump will be able to rotate in any direction of full 360 degrees so it can fit in any case. Hanbo will be released in November this year but no pricing has been released so far.
Hanbo liquid cooler will feature an optimized intake design so it can ensure greater heat transfer and fluid dynamic for improved reliability and silent operation. Radiator comes in 240mm size with two fans and a larger one of 360mm with three fans. The pump will be able to rotate in any direction of full 360 degrees so it can fit in any case. Hanbo will be released in November this year but no pricing has been released so far.
 Kunai fans will boast high static pressure performance with lowered noise. They will go as far as 2200rpm for the 120mm version where the 140mm version will go up to 1600rpm. They will come with addressable LEDs and up to eight fans will be able to be connected to Razer’s PWM fan controller that will come with a magnet at the back for easy attachment to any steel part of PC casing.
PWM will use Razer’s Synapse software to customize pulse width modulation in order to improve airflow and noise. PWM will be priced at $49.99 in the Razer Store and it is available for preorder. Fans are priced at $44.99 for one 120mm or $129.99 for a three-pack of 120mm. One 140mm will go for $49.99 and a three-pack will be $129.99.
Kunai fans will boast high static pressure performance with lowered noise. They will go as far as 2200rpm for the 120mm version where the 140mm version will go up to 1600rpm. They will come with addressable LEDs and up to eight fans will be able to be connected to Razer’s PWM fan controller that will come with a magnet at the back for easy attachment to any steel part of PC casing.
PWM will use Razer’s Synapse software to customize pulse width modulation in order to improve airflow and noise. PWM will be priced at $49.99 in the Razer Store and it is available for preorder. Fans are priced at $44.99 for one 120mm or $129.99 for a three-pack of 120mm. One 140mm will go for $49.99 and a three-pack will be $129.99. 
