MyWebFace is a browser extension developed by Mindspark. This extension claims to allow users to easily access websites that allow them to make a cartoon portrait of themselves. While this may seem interesting in the beginning, all this extension does is to add links to already popular websites that are easy to find.
When installed MyWebFace changes your default search engine and your home page to MyWay.com.
While the extension is running it gathers user browsing information, allowing it to mine data and better server unwanted ads throughout your browsing sessions.
MyWebFace has been marked as a Browser Hijacker by many anti-virus programs, and while not considered malware, it is not recommended to keep it on your computer.
About Browser Hijackers
Browser hijackers (sometimes referred to as hijackware) are a type of malicious software that alters web-browser configurations without the user’s knowledge or consent. These hijacks happen to be rising at a worrying rate worldwide, and it could be really nefarious and sometimes harmful too. Browser hijackers are capable of doing a variety of things on your PC. In general, hijackers are made for the benefit of online hackers often through revenue generation that comes from forced ad clicks and website visits. Although it may seem naive, all browser hijackers are harmful and thus always classified as security risks. Browser hijackers could also let other destructive programs without your knowledge further damage the computer.
Indications of browser hijack
There are numerous signs that indicate the browser is highjacked:
1. the browser’s home page is changed
2. if you enter a URL, you find yourself constantly directed to a different web page than the one you intended
3. the default web engine has been changed and your web browser security settings have been lowered without your knowledge
4. unsolicited new toolbars are added to your web browser
5. you observe numerous ads pop up on the web browsers or computer screen
6. your browser gets sluggish, buggy crashes often
7. you can’t go to certain websites like home pages of anti-malware software.
How does a browser hijacker infect a PC
Browser hijackers can get into a PC in some way or other, for instance via downloads, file sharing, and e-mail also. They also come from add-on applications, also known as browser helper objects (BHO), web browser extensions, or toolbars. Also, some shareware and freeware can put the hijacker within your computer through “bundling”. Typical examples of browser hijackers include Conduit, CoolWebSearch, OneWebSearch, Coupon Server, RocketTab, Snap.do, Delta Search, and Searchult.com.
Browser hijacking can cause severe privacy problems and even identity theft, disrupt your browsing experience by taking control over outgoing traffic, substantially slows down your PC by deleting lots of system resources, and lead to system instability at the same time.
Browser Hijacker Malware – Removal
Certain hijackers can be removed simply by uninstalling the corresponding freeware or add-ons from the Add or Remove Programs in the Windows control panel. In some cases, it can be a difficult task to discover and get rid of the malicious piece because the associated file will be running as part of the operating system process. Moreover, manual removal requires you to execute several time-consuming and complex procedures that are tough to conduct for inexperienced computer users.
Browser hijackers could be effectively removed by installing the anti-malware application on the affected system. To get rid of any type of browser hijacker from your computer, you could download this particular top-notch malware removal program – SafeBytes Anti-Malware. And use a system optimizer, such as Total System Care, to eliminate all related files from the registry and repair browser issues.
Tips on How to Eliminate a Virus that is Blocking Websites or Preventing Downloads
Malware may cause several different types of damage to PCs, networks, and data. Some malware is meant to restrict or block things that you wish to do on your personal computer. It may well not permit you to download anything from the internet or stop you from accessing some or all sites, in particular the anti-virus sites. If you’re reading this, chances are you’re stuck with a malware infection that is preventing you to download or install the Safebytes Anti-Malware program on your system. Even though this type of problem can be tougher to get around, there are a few actions you can take.
Start Windows in Safe Mode
The Windows OS includes a special mode known as “Safe Mode” where just the bare minimum required programs and services are loaded. In case the virus is set to load immediately when the PC starts, switching to this mode may prevent it from doing so. To start the computer into Safe Mode, press the “F8” key on the keyboard right before the Windows boot screen appears; Or after normal Windows boot up, run MSCONFIG, look over “Safe Boot” under the Boot tab, and click Apply. Once you’re in safe mode, you can attempt to install your antivirus software application without the hindrance of the malicious software. Following installation, run the malware scanner to eliminate standard infections.
Switch over to an alternate internet browser
Some malware only targets certain internet browsers. If this is your case, utilize another web browser as it might circumvent the computer virus. If you suspect that your Internet Explorer has been hijacked by malware or otherwise compromised by hackers, the best course of action is to switch to an alternate browser like Chrome, Firefox, or Safari to download your favorite computer security software – Safebytes Anti-Malware.
Install and run anti-virus from a USB drive
To effectively get rid of the malware, you should approach the problem of running an anti-malware software program on the affected computer from a different angle. To run anti-virus using a USB flash drive, follow these simple steps:
1) Use another virus-free computer system to download Safebytes Anti-Malware.
2) Insert the USB drive into the uninfected PC.
3) Double-click the Setup icon of the anti-malware software package to run the Installation Wizard.
4) When asked, select the location of the USB drive as the place in which you would like to store the software files. Do as instructed on the screen to complete the installation process.
5) Transfer the thumb drive from the clean computer to the infected computer.
6) Double-click the anti-malware software EXE file on the USB flash drive.
7) Click the “Scan Now” button to start the virus scan.
Highlights of SafeBytes Anti-Malware
If you are looking to install an anti-malware program for your PC, there are numerous tools on the market to consider nonetheless, you just cannot trust blindly anyone, irrespective of whether it is a free or paid program. A few of them do a good job in removing threats while some will harm your computer by themselves. You should choose one that is efficient, practical, and has a strong reputation for its malware source protection. On the list of strongly recommended software is SafeBytes Anti-Malware. SafeBytes has a superb history of top-quality service, and customers appear to be very happy with it.
SafeBytes anti-malware is a reliable tool that not only secures your PC permanently but is also quite easy to use for people of all ability levels. With its outstanding protection system, this utility will quickly detect and remove the majority of the security threats, including browser hijackers, viruses, adware, ransomware, trojans, worms, and PUPs.
There are many amazing features you will get with this particular security product. Listed below are a few of the great ones:
Antimalware Protection: Using its enhanced and sophisticated algorithm, this malware elimination tool can identify and remove the malware threats hiding in your PC effectively.
Real-time Threat Response: Malware programs looking to enter the computer are discovered and stopped as and when detected by the SafeBytes real-time protection shields. This tool will continuously monitor your PC for any suspicious activity and updates itself continuously to keep abreast of the constantly changing threat scenarios.
Faster Scanning: This software has one of the fastest and most powerful virus scanning engines in the industry. The scans are extremely accurate and take a little time to complete.
Safe Web Browsing: Through its unique safety ranking, SafeBytes notifies you whether a site is safe or not to visit it. This will assure that you’re always certain of your online safety when browsing the net.
Minimal CPU Usage: SafeBytes is a lightweight and user-friendly anti-virus and anti-malware solution. As it uses very low computer resources, this program leaves the computer’s power exactly where it belongs: with you actually.
24/7 Guidance: You can obtain absolutely free 24/7 technical assistance from their computer experts on any product queries or PC security issues.
To conclude, SafeBytes Anti-Malware is really great for securing your computer against all kinds of malware threats. You now may understand that this particular software does more than just scan and eliminate threats in your PC. You will get the best all-around protection for the money you spend on SafeBytes Anti-Malware subscription, there isn’t any doubt about it.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove MyWebFace without the use of an automated tool, it might be actually possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser plug-ins, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
Lastly, check your hard disk for all of the following and clean your computer registry manually to remove leftover application entries after uninstallation. However, editing the registry can be a difficult job that only advanced users and professionals should try to fix it. Moreover, certain malicious programs are capable to defend against its deletion. You’re advised to do this process in Safe Mode.
Files:
%PROGRAMFILES%\MyWebFace_5aEI\Installr.binaEZSETP.dll
%PROGRAMFILES%\MyWebFace_5aEI\Installr.bin\NP5aEISb.dll
Search and Delete:
5aauxstb.dll
5abar.dll
5abarsvc.exe
5abrmon.exe
5abrstub.dll
5adatact.dll
5adlghk.dll
5adyn.dll
5afeedmg.dll
5ahighin.exe
5ahkstub.dll
5ahtmlmu.dll
5ahttpct.dll
5aidle.dll
5aieovr.dll
5aimpipe.exe
5amedint.exe
5amlbtn.dll
5amsg.dll
5aPlugin.dll
5aradio.dll
5aregfft.dll
5areghk.dll
5aregiet.dll
5ascript.dll
5askin.dll
5asknlcr.dll
5askplay.exe
5aSrcAs.dll
5aSrchMn.exe
5atpinst.dll
5auabtn.dll
CREXT.DLL
CrExtP5a.exe
NP5aStub.dll
T8EXTEX.DLL
T8EXTPEX.DLL
T8HTML.DLL
T8RES.DLL
T8TICKER.DLL
Folders:
C:\Documents and Settings\username\Application Data\Mozilla\Firefox\Profiles\gb5e8gtn.default\extensionsaffxtbr@MyWebFace_5a.com
C:\Documents and Settings\username\Application Data\MyWebFace_5a
C:\Program Files\MyWebFace_5a
Registry:
Key HKLM\SOFTWARE\MyWebFace_5a
Key HKLM\SOFTWARE\MozillaPlugins\@MyWebFace_5a.com/Plugin
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MyWebFace_5abar Uninstall
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\b1df253a-9e7a-480d-b6a5-7a435b520dbb
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\14d02517-c8be-4735-a344-3c8366c77aa0
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.ThirdPartyInstaller
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.SkinLauncherSettings
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.SkinLauncher
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.ScriptButton
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.SettingsPlugin
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.RadioSettings
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.Radio
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.PseudoTransparentPlugin
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.MultipleButton
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.HTMLPanel
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.HTMLMenu
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.FeedManager
Key HKLM\SOFTWARE\Classes\MyWebFace_5a.DynamicBarButton
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ Value: MyWebFace_5a Browser Plugin Loader Data: 5aPlugin.dll
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ Value: MyWebFace Search Scope Monitor Data: 5abrmon.exe
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ Value: MyWebFace Data: MyWebFace.dll
 Error Causes
Error Causes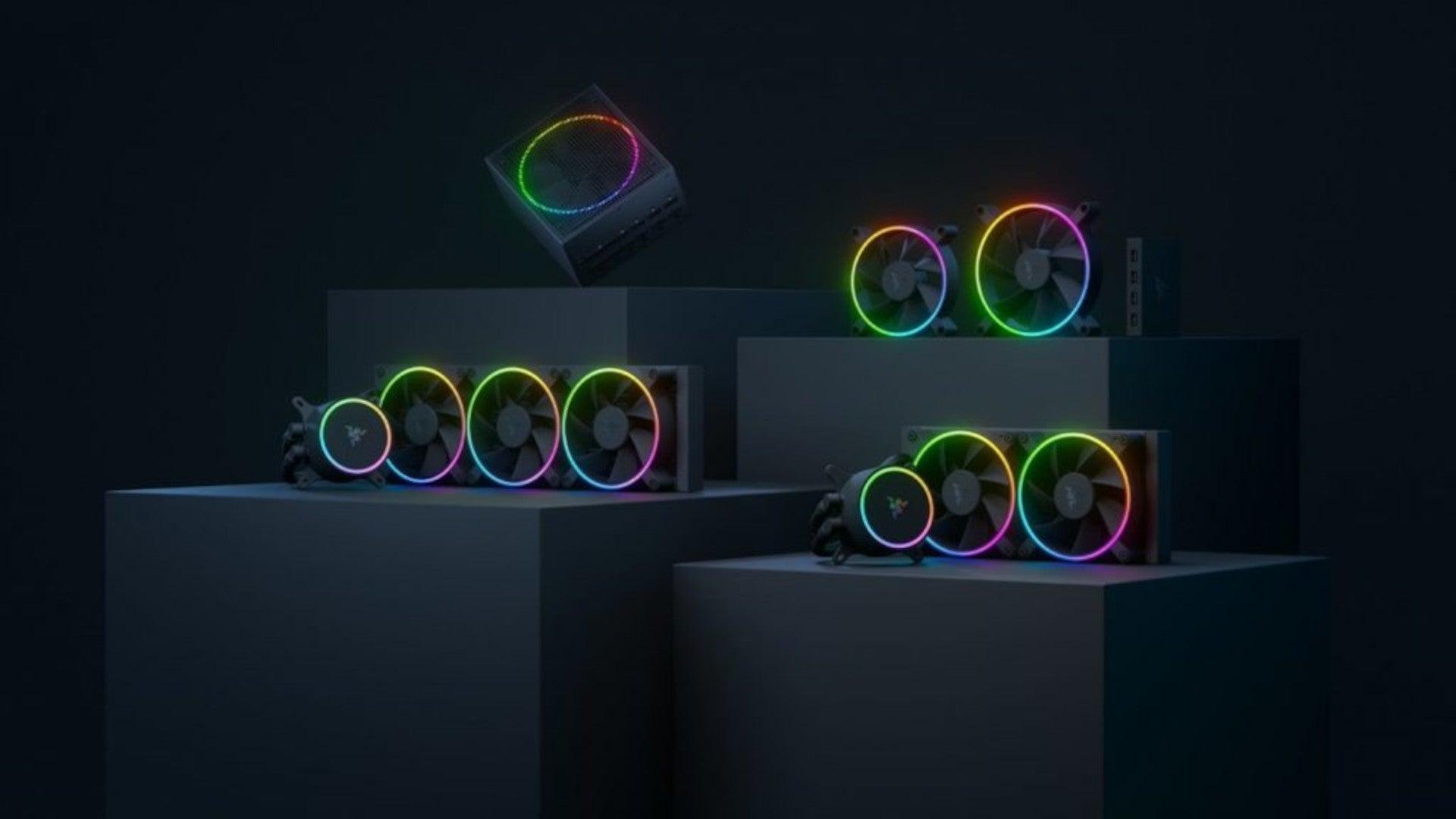 Razer is a well-known brand among PC gamers and users, it started as a peripheral manufacturer focused on keyboards and mouse but after years passed Razer expanded its inventory offerings. It soon started offering headphones and lately has branched into wider product lines like gaming chairs and protection masks.
Razer is a well-known brand among PC gamers and users, it started as a peripheral manufacturer focused on keyboards and mouse but after years passed Razer expanded its inventory offerings. It soon started offering headphones and lately has branched into wider product lines like gaming chairs and protection masks. Most interesting for me personally is Razers Katana, the power supply unit. It is a modular power supply ranging from 750W to 1200W with the additional option of Titanium rated one with an impressive 1600W of power. Power supply will start shipping in early 2022 and at the time of writing this article no price range has been released.
Most interesting for me personally is Razers Katana, the power supply unit. It is a modular power supply ranging from 750W to 1200W with the additional option of Titanium rated one with an impressive 1600W of power. Power supply will start shipping in early 2022 and at the time of writing this article no price range has been released.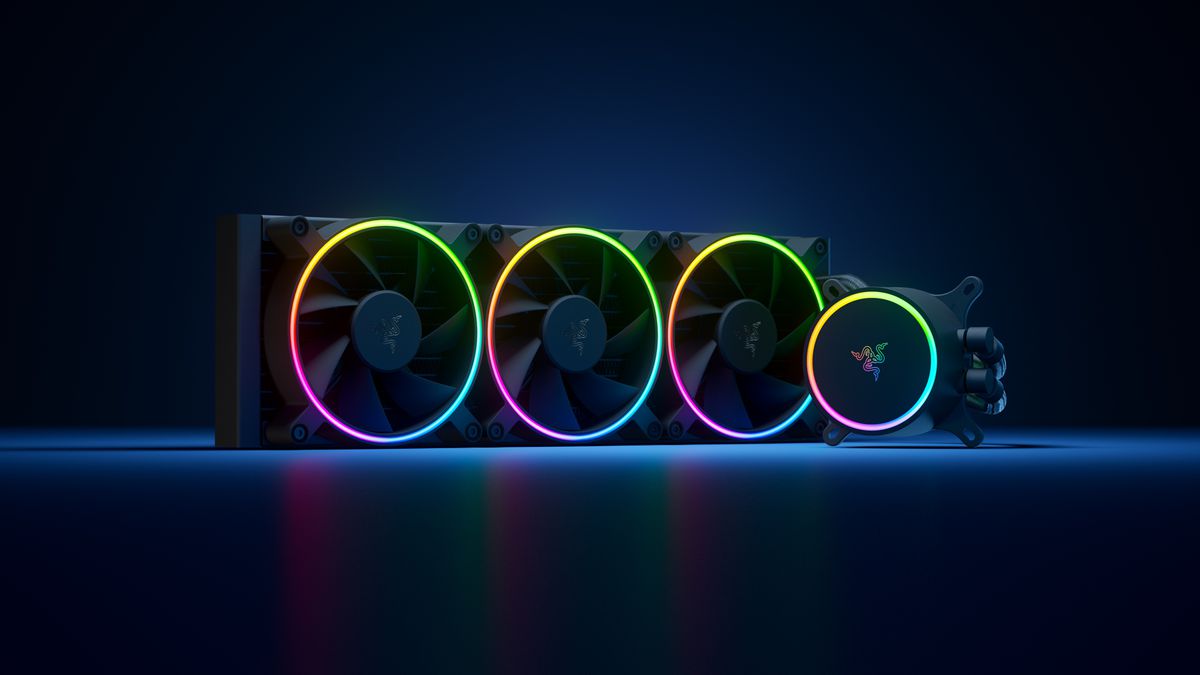 Hanbo liquid cooler will feature an optimized intake design so it can ensure greater heat transfer and fluid dynamic for improved reliability and silent operation. Radiator comes in 240mm size with two fans and a larger one of 360mm with three fans. The pump will be able to rotate in any direction of full 360 degrees so it can fit in any case. Hanbo will be released in November this year but no pricing has been released so far.
Hanbo liquid cooler will feature an optimized intake design so it can ensure greater heat transfer and fluid dynamic for improved reliability and silent operation. Radiator comes in 240mm size with two fans and a larger one of 360mm with three fans. The pump will be able to rotate in any direction of full 360 degrees so it can fit in any case. Hanbo will be released in November this year but no pricing has been released so far. Kunai fans will boast high static pressure performance with lowered noise. They will go as far as 2200rpm for the 120mm version where the 140mm version will go up to 1600rpm. They will come with addressable LEDs and up to eight fans will be able to be connected to Razer’s PWM fan controller that will come with a magnet at the back for easy attachment to any steel part of PC casing.
Kunai fans will boast high static pressure performance with lowered noise. They will go as far as 2200rpm for the 120mm version where the 140mm version will go up to 1600rpm. They will come with addressable LEDs and up to eight fans will be able to be connected to Razer’s PWM fan controller that will come with a magnet at the back for easy attachment to any steel part of PC casing.
 One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
One of the first things that everyone saw when Microsoft has unveiled Windows 11 is its Start menu. Funny enough this is what has caused most of the divide among users, some find it interesting, and some do not like it. Truth is, it is different, and it is centered in the middle instead of the lower left part of the screen.
It has been confirmed however that the Start menu can be moved to any part of the screen so if you want, you could place it on the lower left as it has always been.
Live tiles do not longer exist in the Start menu, instead, we have styled simple icons.
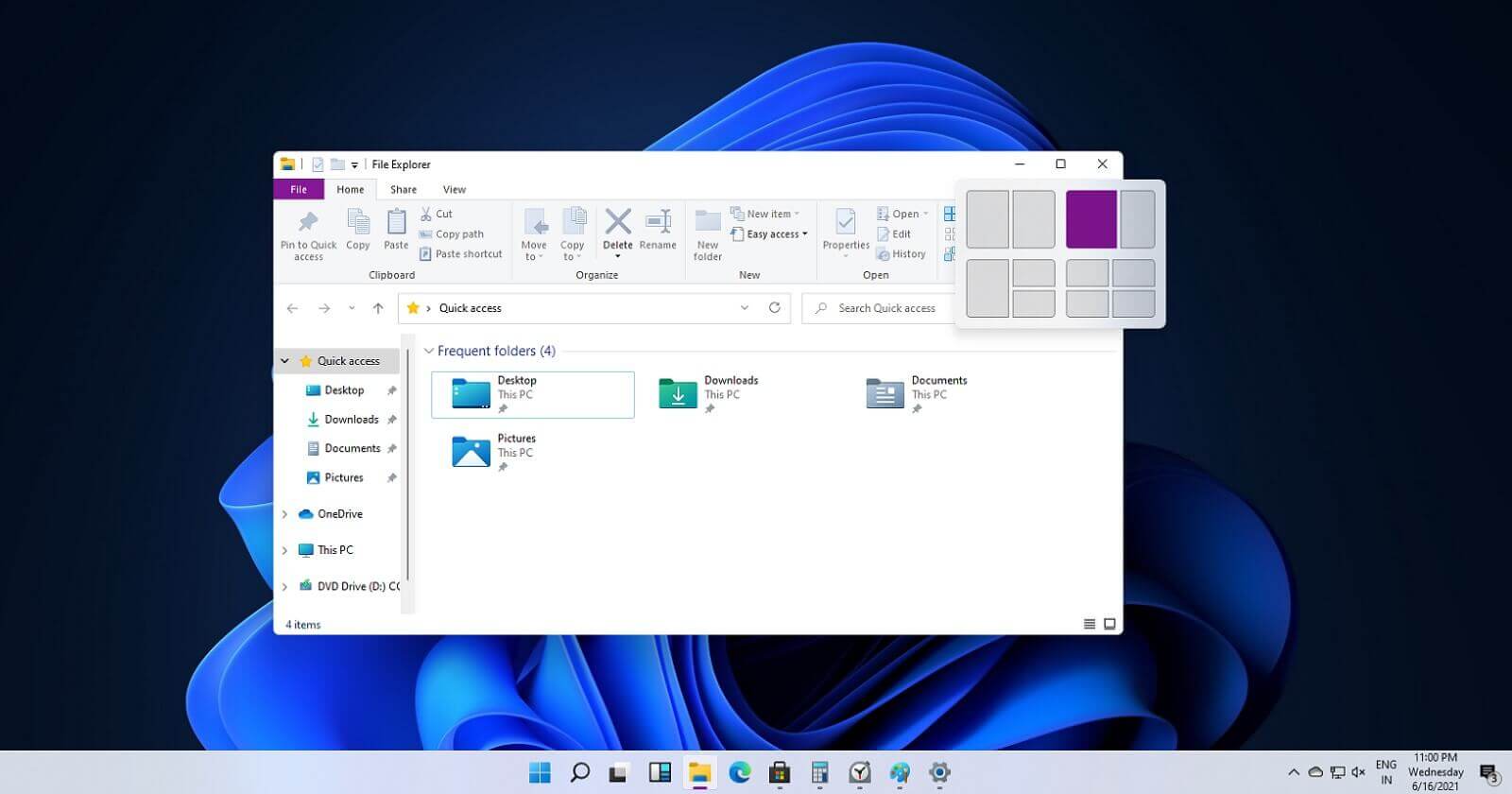 If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
If you have used the cascade option in previous Windows versions then it is most likely that you will like the new Snap controls.
You can quickly snap windows side by side, or arrange them in sections on your desktop just by hovering over maximize button on the title bar.
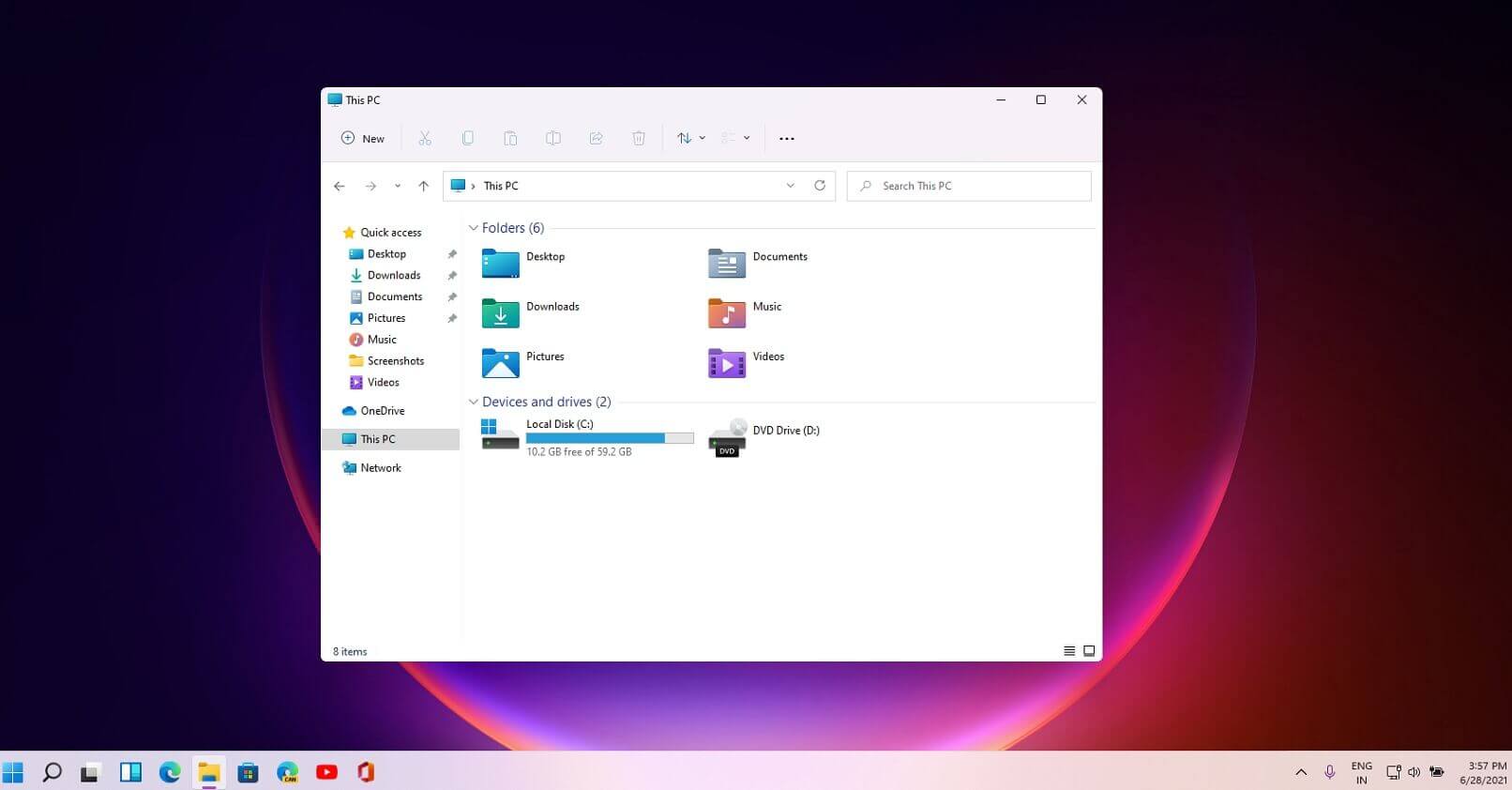 File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
File explorer has gone through some visual and design changes, the ribbon on top has been completely removed and replaced with a header-like feature with a slick and clean design.
The header contains a nice organized and designed single row of icons like cut, paste, copy, rename, delete, and new folder icons.
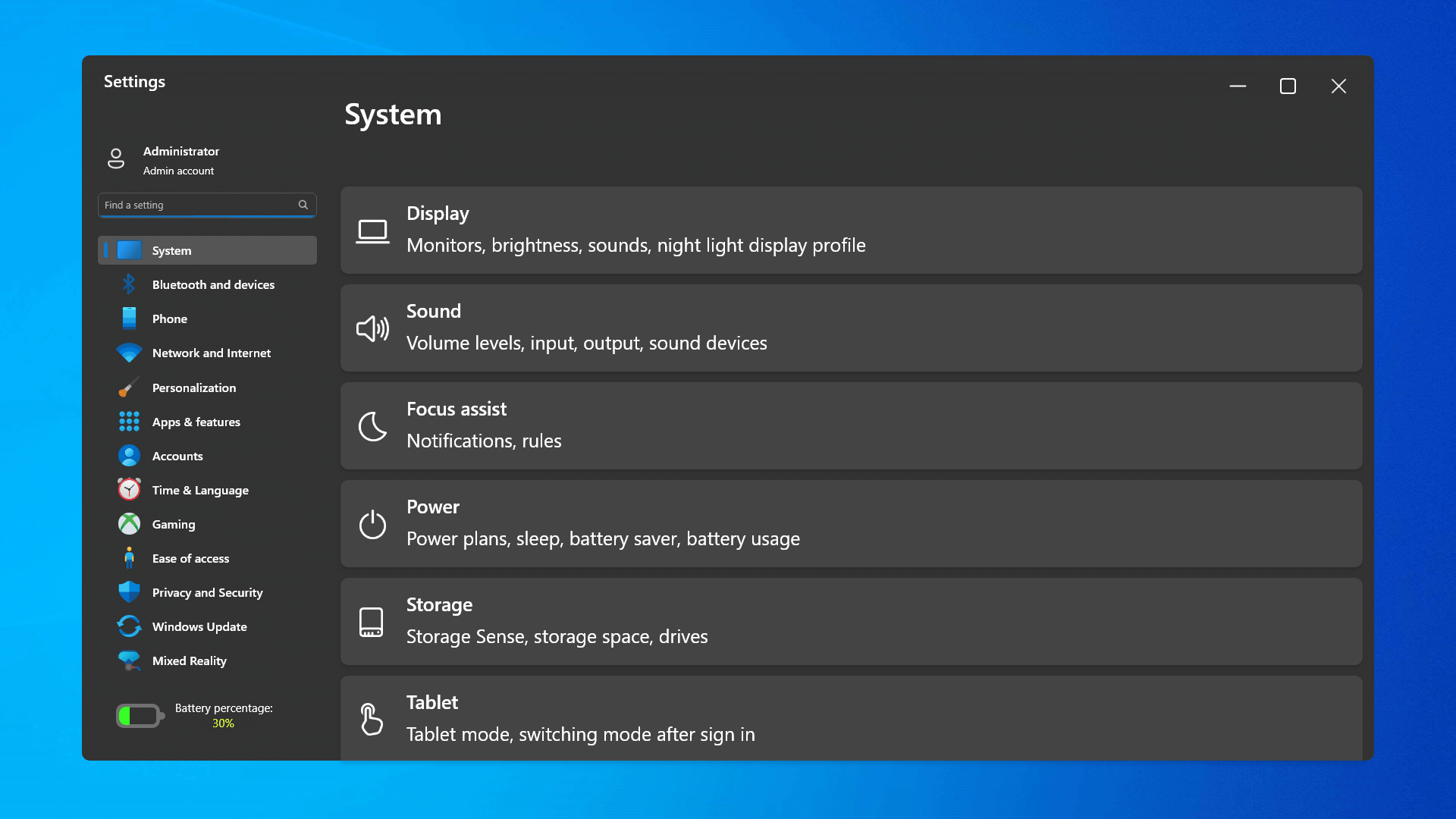 The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
The settings app also has gone through visual and design changes. It has a new design that is very visually appealing and navigation has been simplified and more organized. Finding the right and desired setting is much faster and clearer now.
 Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
Yes, widgets are back but not like you remember them.
Instead of being all-time present at your desktop like once they used to be, now there is a button on the taskbar which brings the widget bar up that contains desired widgets. This way they are easily accessible and do not clutter desktops.
So far we have weather, news, calendar, and stocks widget but we will see how development on these goes. I expect to have community-made widgets like in old days for all of our needs.
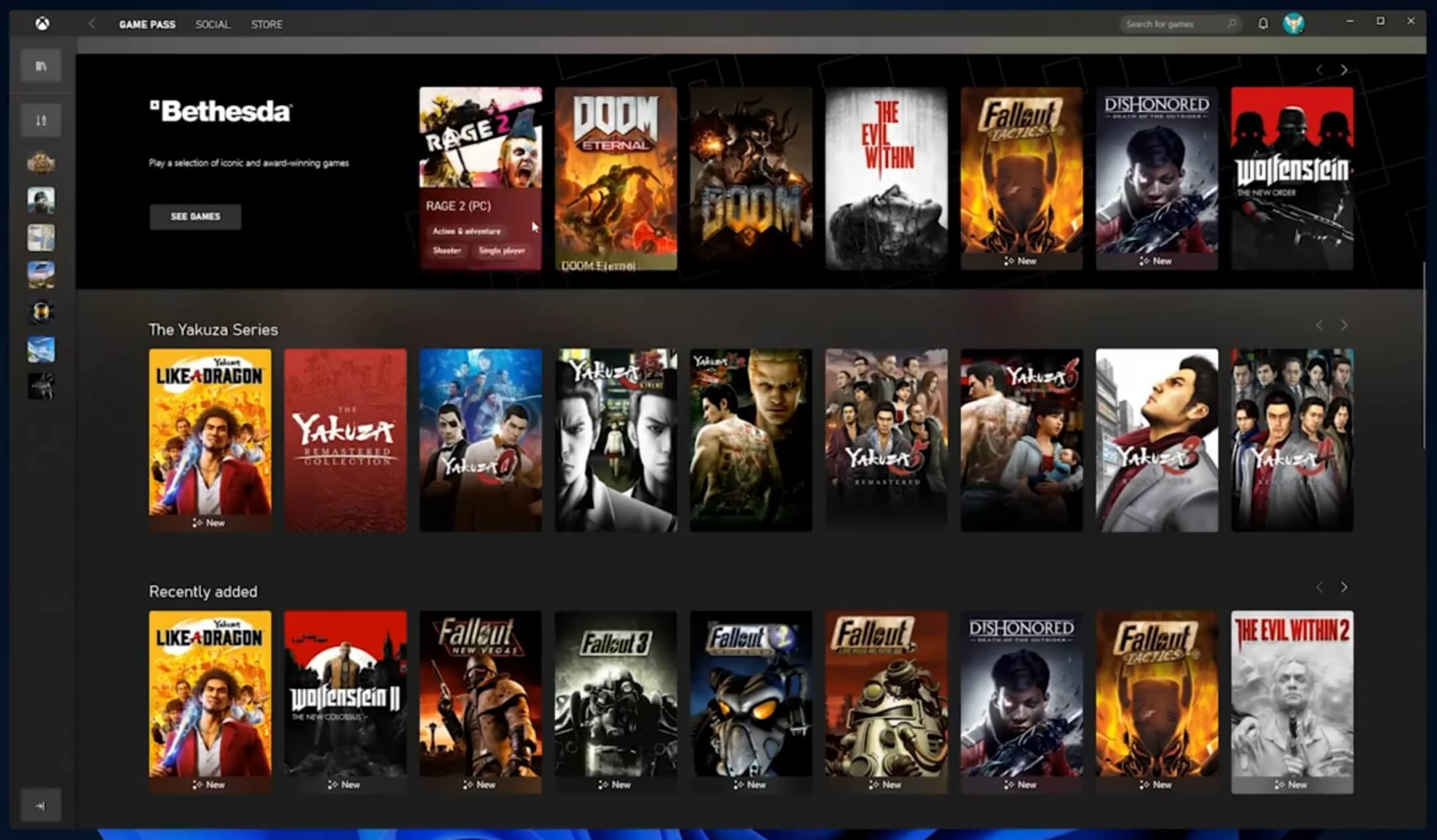 The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
The new Xbox app is now integrated into Windows 11, offering quick access to Xbox Game Pass games, the social parts of the Xbox network, and the Xbox store.
 As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com
As widely known by now Windows 11 will require you to have a TPM 2.0 module capable CPU in order to install it.
This system requirement has caused a lot of controversies but essentially it seems that MS's goal is to protect your personal data by using this module.
The upside of course is that your data will be protected much more than in previous Windows versions, the downside, of course, will be that you will need newer hardware to run OS on it.
and that is essentially it, keep on tuned on more Windows 11 information and overall articles tied to PC and technology here at errortools.com 

