MovieGoat is a browser extension that allegedly lets you search for your favorite videos using its simple search engine.
From the author:
Search for your favorite movies online, stay updated with the latest news and trends, and keep an eye on what’s up and coming in the world of cinema.
Simply type goat+ SpaceTab + query at the chrome search bar.
MovieGoat hijacks your browser, replacing your default search engine, displaying sponsored videos when you use its search and will display pop-up ads during your browsing experience. This extension has been detected as a Browser Hijacker by several anti-virus scanners and is not recommended to keep on your computer, especially because it serves no other purpose than to display pop-up ads and negatively impact your browsing experience.
About Browser Hijackers
Browser hijack is a common type of internet fraud where your internet browser configuration settings are modified to make it carry out things you never intend. There are numerous reasons why you may have an internet browser hijack; however commercial, advertising, and marketing are definitely the primary reasons for their creation. Usually, hijackers are made for the benefit of cyber hackers usually through income generation from forced ad clicks and site visits. Most people assume that these types of websites are legitimate and harmless but that is incorrect. Almost every browser hijacker poses an actual threat to your online safety and it’s important to categorize them under privacy risks. Some browser hijackers are designed to make particular modifications beyond the web browsers, like altering entries on the system registry and permitting other types of malware to further damage your PC.
How you can recognize a browser hijack
When your browser is hijacked, the following could happen: your homepage has been reset to some unfamiliar webpage; you find yourself regularly directed to some other site than the one you meant; The default search page of web browser is altered; you are finding new toolbars you have never witnessed before; you’ll notice random pop-ups start showing regularly; websites load very slowly and sometimes incomplete; Inability to navigate to particular websites, particularly anti-malware as well as other computer security software websites.
How it infects your computer
Browser hijackers can get into a computer in some way or other, for example via downloads, file sharing, and email too. They may also be deployed through the installation of a web browser toolbar, add-on, or extension. A browser hijacker can also come bundled up with some freeware which you unwittingly download and install the browser hijack, compromising your computer security. A good example of some infamous browser hijackers includes Anyprotect, Conduit, Babylon, SweetPage, DefaultTab, Delta Search, and RocketTab, however, the names are constantly changing.
Browser hijacking can bring about severe privacy problems and even identity theft, affect your browsing experience by taking control over outbound traffic, substantially slows down your computer by consuming lots of resources, and cause system instability also.
Removal
One thing you could try to eliminate a browser hijacker is to locate the malicious software within the “Add or Remove Programs” list of the Windows Control Panel. It might or might not be there. If it is, uninstall it. But, most browser hijackers are hard to eliminate manually. Irrespective of how much you attempt to get rid of it, it could come back again and again. On top of that, manual removal demands you to carry out several time-consuming and complicated procedures which are very hard to complete for new computer users.
What you can do if Virus Prevents You From Downloading Or Installing Antivirus?
Malware can cause all sorts of damage if they invade your PC, ranging from stealing your personal information to erasing files on your computer. Some malware is created to restrict or block things that you want to do on your PC. It may not allow you to download anything from the net or it will prevent you from accessing a few or all of the internet sites, particularly the antivirus sites. If you’re reading this article, odds are you’re stuck with a virus infection that is preventing you to download or install Safebytes Anti-Malware software on your computer system. There are a few solutions you can attempt to get around with this particular obstacle.
Boot your computer in Safe Mode
If the malware is set to load automatically when Microsoft Windows starts, entering safe mode could block this attempt. Just the minimum required applications and services are loaded whenever you boot your computer or laptop in Safe Mode. Here are the steps you need to follow to boot into the Safe Mode of your Windows XP, Vista, or 7 computers (visit Microsoft site for directions on Windows 8 and 10 PCs).
1) At power on, hit the F8 key before the Windows splash screen begins to load. This would conjure up the Advanced Boot Options menu.
2) Select Safe Mode with Networking using arrow keys and hit Enter.
3) Once you get into this mode, you will have internet access once again. Now, obtain the malware removal program you want by using the internet browser. To install the software, follow the directions in the installation wizard.
4) Following installation, do a complete scan and allow the program to remove the threats it detects.
Use an alternate web browser to download security software
Malicious code could exploit vulnerabilities in a particular browser and block access to all antivirus software websites. If you are not able to download the anti-virus software program using Internet Explorer, it means malware may be targeting IE’s vulnerabilities. Here, you need to switch over to another web browser such as Chrome or Firefox to download Safebytes Anti-malware software.
Install and run anti-malware from a USB drive
Here’s yet another solution which is utilizing a portable USB antivirus software package that can check your computer for viruses without the need for installation. Follow these steps to use a USB flash drive to clean your corrupted computer system.
1) Download Safebytes Anti-Malware or Windows Defender Offline onto a clean PC.
2) Insert the USB drive into the clean computer.
3) Double-click the exe file to run the installation wizard.
4) When asked, choose the location of the USB drive as the place in which you would like to store the software files. Follow the on-screen instructions to complete the installation.
5) Disconnect the flash drive. You can now utilize this portable anti-malware on the affected computer system.
6) Double-click the antivirus program EXE file on the USB flash drive.
7) Hit the “Scan” button to run a full computer scan and remove viruses automatically.
Protect your PC from Malware With SafeBytes Security Suite
If you are looking to install anti-malware software for your computer, there are plenty of tools on the market to consider nonetheless, you should not trust blindly anyone, no matter whether it is a paid or free software. A few are good ones, some are ok types, and some are simply just bogus anti-malware applications that can damage your personal computer themselves! You need to pick one that is efficient, practical, and has a strong reputation for its malware protection. On the list of strongly recommended software by industry analysts is SafeBytes Anti-Malware, the safest program for Microsoft Windows.
SafeBytes anti-malware is a trusted software that not only secures your computer permanently but is also very user-friendly for people of all ability levels. With its outstanding protection system, this tool will automatically detect and remove most of the security threats, including browser hijackers, viruses, adware, ransomware, PUPs, and trojans.
SafeBytes possesses a plethora of amazing features that can help you protect your PC from malware attack and damage. Here are a few of the best ones:
Most effective AntiMalware Protection: Using its enhanced and sophisticated algorithm, this malware removal tool can identify and eliminate the malware threats hiding within your computer system effectively.
Active Protection: Malware programs trying to get into the system are identified and stopped as and when detected by the SafeBytes active protection shields. It will constantly monitor your laptop or computer for hacker activity and also gives users advanced firewall protection.
Web Protection: SafeBytes checks and provides a unique safety rating to every single website you visit and block access to web pages considered to be phishing sites, thus safeguarding you against identity theft, or known to contain malware.
High-Speed Malware Scanning Engine: This tool has got one of the fastest and most efficient virus scanning engines in the industry. The scans are very accurate and take a little time to complete.
Lowest CPU and Memory Usage: SafeBytes is a lightweight tool. It consumes a very small amount of processing power as it operates in the background so you are free to use your Windows-based PC the way you really want.
24/7 Online Support: For any technical queries or product support, you can get 24/7 expert assistance through chat and e-mail.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove MovieGoat without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by MovieGoat
Files:
%Documents and Settings%All UsersApplication DataMovie Goat virus
%program files %internet explorer Movie Goat[random].mof
%program files (x86)%common filesspeechengines
%programData%suspicious folders
%windows%system32drivermessy code.dll
%AppData%[malware program name]toolbar uninstallStatIE.dat
%app data% Movie Goat virus
Registry:
[HKEY_LOCAL_MACHINESOFTWAREMicrosoftMATSWindowsInstallerEAF386F0-7205-40F2-8DA6-1BABEEFCBE8914.07.30.07.52.18]”ProductName”=”Movie Goat”
[HKEY_LOCAL_MACHINESOFTWAREWow6432NodeMicrosoftTracingMuvic_RASAPI32]
[HKEY_LOCAL_MACHINESOFTWAREWow6432NodeMicrosoftTracingMuvic_RASMANCS]
[HKEY_LOCAL_MACHINESOFTWAREWow6432NodeMicrosoftWindowsCurrentVersionUninstallEAF386F0-7205-40F2-8DA6-1BABEEFCBE89]
“DisplayName”=”Movie Goat”
[HKEY_USERSS-1-5-21-3825580999-3780825030-779906692-1001SoftwareMicrosoftWindowsCurrentVersionUninstall50f25211-852e-4d10-b6f5-50b1338a9271]
“DisplayName”=”Movie Goat”


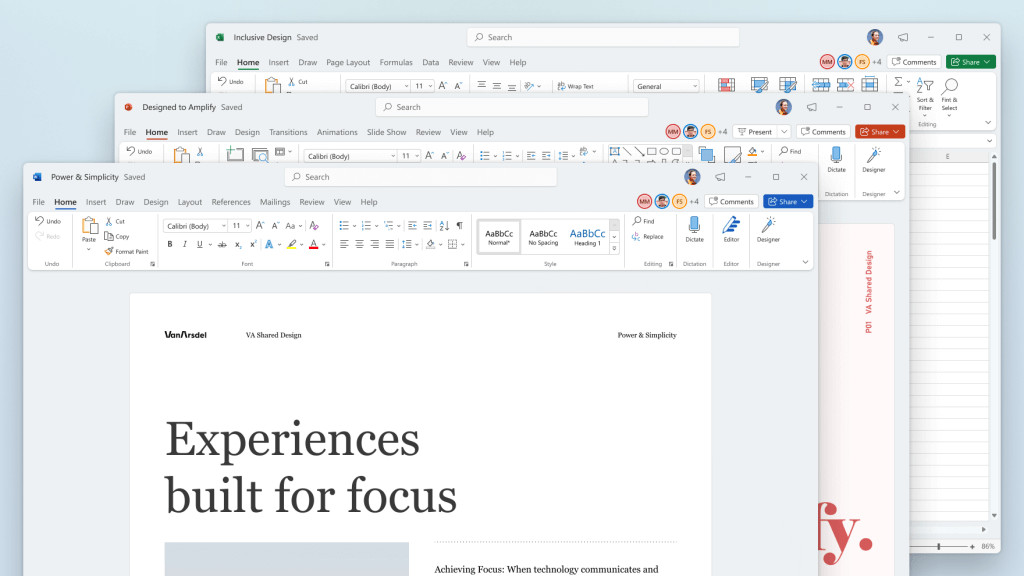
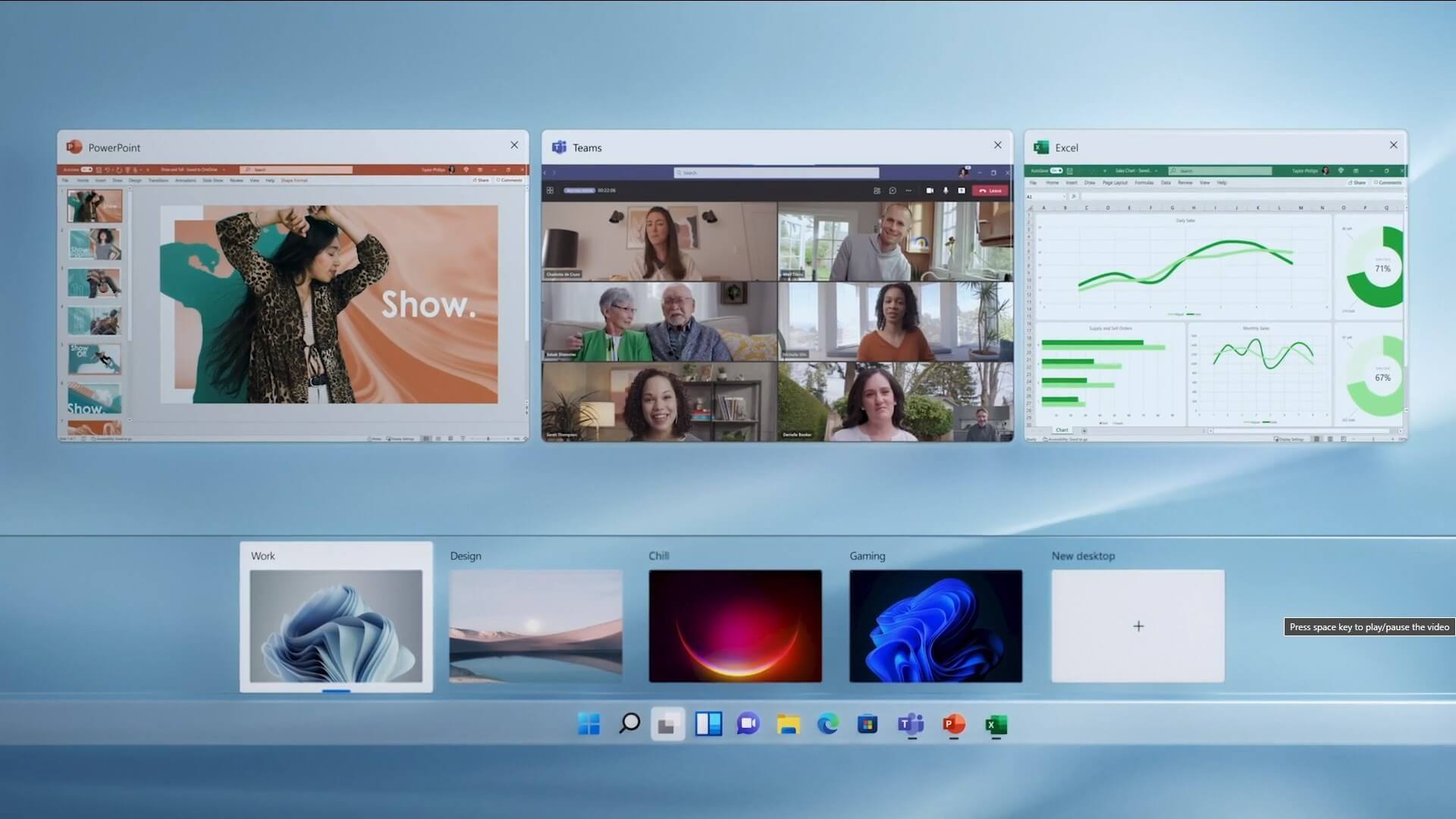 The feature that was originally planned for now scrapped Windows 10X is included in Windows 11. You will be able to customize your Virtual desktop with different wallpapers for each screen.
In order to fully customize your virtual desktops with different wallpapers follow this easy step-by-step guide.
The feature that was originally planned for now scrapped Windows 10X is included in Windows 11. You will be able to customize your Virtual desktop with different wallpapers for each screen.
In order to fully customize your virtual desktops with different wallpapers follow this easy step-by-step guide.
 How to switch
How to switch Conclusion
Conclusion