SearchApp by Blpsearch is a Browser Hijacker that is presently targeting Google Chrome browsers. It is offered as a tool gives user enhanced online search experience. Search App also has other amazing tools that let you quickly search the web from a new tab window.
This extension changed your home page and new tab search to blpsearch. While installing you will see additional ads and sponsored links displaying throughout your browsing sessions. It collects user browsing information and uses it to better serve sponsored content.
About Browser Hijackers
Browser hijacking means a malicious code has control over and altered the settings of your web browser, without your approval. There are numerous reasons why you might experience an internet browser hijack; however commercial, marketing, and advertising are the key reasons for their creation. Generally, hijackers will force hits to websites of their preference either to increase web traffic generating higher ad earnings, or to obtain a commission for every user visiting there. Nonetheless, it is not that naive. Your internet safety is jeopardized and it is also very annoying. In a much worst case, your browser could be hi-jacked to download malicious software that will do a lot of damage to your computer or laptop.
Find out how to identify a browser hijack
Symptoms that your internet browser is hijacked include: your web browser’s homepage is suddenly different; bookmark and the new tab are also modified; the default browser configurations have been changed and/or your default web engine is altered; unsolicited new toolbars are added to your web browser; you observe numerous ads appear on your web browsers or display screen; your browser has instability issues or displays frequent errors; Inability to navigate to certain sites, especially anti-malware and other computer security software sites.
How it infects your personal computer
Browser hijackers can enter a PC by some means or other, for example via file sharing, downloads, and email too. Many internet browser hijackings come from add-on applications, i.e., toolbars, browser helper objects (BHO), or extensions added to web browsers to provide them extra capabilities. Some browser hijackers spread in user’s computers by using a deceptive software distribution strategy known as “bundling” (generally through shareware and freeware). Examples of popular browser hijackers are Fireball, GoSave, Ask Toolbar, CoolWebSearch, RocketTab, and Babylon Toolbar.
Browser hijackers may record user keystrokes to gather potentially important information leading to privacy issues, cause instability on systems, drastically disrupt the user experience, and ultimately slow down the system to a stage where it becomes unusable.
How to repair a browser hijack
The one thing you could try to remove a browser hijacker is to discover the malicious software within the “Add or Remove Programs” list of the Windows Control Panel. It might or might not be there. When it is, uninstall it. Yet, some hijackers will be more difficult to locate or remove since they might get themselves associated with certain important computer files that enable it to operate as a necessary operating-system process. You should think about carrying out manual fixes only if you’re a tech-savvy individual because there are negative consequences associated with messing around with the system registry and HOSTS file.
Installing and running antivirus software on the affected computer could automatically erase browser hijackers and other malicious programs. Safebytes Anti-Malware features a cutting-edge anti-malware engine to help you prevent browser hijacker infection in the first place, and clean up any existing issues. Together with the anti-malware tool, a PC optimizer, can help you in getting rid of all linked files and modifications in the computer registry automatically.
What To Do If You Cannot Install Any Anti-Malware?
Malware can cause plenty of damage to your personal computer. Some malware goes to great lengths to stop you from downloading or installing anything on your computer, particularly anti-virus software programs. If you are reading this now, you’ve perhaps realized that a malware infection is a reason behind your blocked net traffic. So how to proceed if you need to download and install an antivirus application such as Safebytes? There are a few steps you can take to circumvent this problem.
Install anti-virus in Safe Mode with Networking
In Safe Mode, you can actually change Windows settings, uninstall or install some program, and eradicate hard-to-delete malware. In the event the malware is obstructing the internet connection and affecting your computer, running it in Safe Mode allows you to download antivirus and run a scan whilst limiting potential damage. To boot into Safe Mode, hit the “F8” key on the keyboard right before the Windows boot screen shows up; Or right after normal Windows boot up, run MSConfig, check Safe Boot under Boot tab, and click Apply. Once you’re in Safe Mode, you can attempt to install your antivirus software program without the hindrance of the malware. Following installation, run the malware scanner to eliminate most standard infections.
Use an alternate browser to download security software
Some malware only targets particular web browsers. If this is your situation, use another web browser as it could circumvent the virus. In the event you suspect that your Internet Explorer happens to be hijacked by a virus or otherwise compromised by cybercriminals, the most effective thing to do is to switch to an alternate web browser such as Google Chrome, Mozilla Firefox, or Apple Safari to download your chosen security program – Safebytes Anti-Malware.
Install antivirus on a flash drive
Here’s yet another solution which is utilizing a portable USB anti-virus software that can scan your system for malware without needing installation. Do these simple steps to clear up your affected computer using a portable antivirus.
1) On a clean PC, download and install Safebytes Anti-Malware.
2) Connect the flash drive to a USB port on the clean computer.
3) Run the setup program by double-clicking the executable file of the downloaded application, which has a .exe file extension.
4) Select thumb drive as the place when the wizard asks you where you want to install the application. Follow the directions to finish the installation process.
5) Transfer the USB drive from the clean computer to the infected computer.
6) Run the Safebytes Anti-malware directly from the pen drive by double-clicking the icon.
7) Click “Scan Now” to run a scan on the affected computer for viruses.
Protect your Computer against Malware With SafeBytes Security Suite
If you’re looking to download the anti-malware program for your PC, there are various tools in the market to consider but you just cannot trust blindly anyone, irrespective of whether it is paid or free program. Some of them are excellent, some are ok types, and some will ruin your computer themselves! When searching for anti-malware software, pick one that offers reliable, efficient, and complete protection against all known computer viruses and malware. In terms of commercial tool options, most people go with well-known brands, like SafeBytes, and are quite happy with it.
SafeBytes anti-malware is a powerful, highly effective protection tool created to help users of all levels of computer literacy in identifying and eliminating harmful threats out of their computer. Through its cutting-edge technology, this software protects your personal computer against infections brought on by different types of malware and other threats, including spyware, adware, computer viruses, worms, trojan horses, keyloggers, potentially unwanted programs (PUPs), and ransomware.
SafeBytes anti-malware offers a myriad of enhanced features that sets it apart from all others. Listed below are some of the features you might like in SafeBytes.
World-class AntiMalware Protection: Using its enhanced and sophisticated algorithm, this malware elimination tool can identify and eliminate the malware threats hiding in your PC effectively.
Active Protection: SafeBytes gives round-the-clock protection for your computer restricting malware attacks in real-time. This software will always keep track of your PC for suspicious activity and updates itself regularly to keep abreast of the latest threats.
Website Filtering: SafeBytes checks and gives a unique safety rating to every single website you visit and block access to web pages considered to be phishing sites, thus safeguarding you against identity theft, or known to contain malware.
Light-weight: SafeBytes is a lightweight and user-friendly antivirus and anti-malware solution. As it utilizes minimal computer resources, this program leaves the computer’s power exactly where it belongs to: with you.
Fantastic Tech Support: You can get high levels of support round the clock if you’re using their paid software.
To sum it up all, SafeBytes Anti-Malware gives you outstanding protection combined with very low system resource usage with both great malware detection and prevention. Once you’ve installed SafeBytes Anti-Malware, you no longer need to worry about malware or any other security concerns. So when you need advanced forms of protection features and threat detections, purchasing SafeBytes Anti-Malware could be worth the dollars!
Technical Details and Manual Removal (Advanced Users)
If you don’t wish to use an automated tool and prefer to remove SearchApp manually, you could possibly do so by going to the Windows Add/Remove Programs menu in the control panel and deleting the offending program; in cases of browser extensions, you can uninstall it by going to the browser’s Add-on/Extension manager. You’ll probably also want to totally reset your internet browser to its default configuration settings.
In order to ensure the complete removal, manually examine your hard drive and registry for all the following and eliminate or reset the values as needed. But bear in mind, this is often a difficult task and only computer professionals can perform it safely. In addition, some malware is capable of replicating or preventing deletion. It is advisable that you carry out the removal procedure in Safe Mode.
Files:
%Documents and Settings%\All Users\Application Data\Blpsearch.com
%program files %\internet explorer\Blpsearch.com\random.mof
%program files (x86)%\common files\speechengines\
%programData%\suspicious folders\
%windows%\system32\driver\messy code.dll
%AppData%\blpsearch.com\toolbar uninstallStatIE.dat
%app data%\Blpsearch.comn Blpsearch.com
Registry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MATS\WindowsInstaller\EAF386F0-7205-40F2-8DA6-1BABEEFCBE8914.07.30.07.52.18 ProductName=Blpsearch.com
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\Muvic_RASAPI32
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\Muvic_RASMANCS
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\EAF386F0-7205-40F2-8DA6-1BABEEFCBE89\DisplayName=Blpsearch.com
HKEY_USERS\S-1-5-21-3825580999-3780825030-779906692-1001\Software\Microsoft\Windows\CurrentVersion\Uninstallf25211-852e-4d10-b6f5-50b1338a9271\DisplayName=Blpsearch.com
 in the command prompt you need to type the next command:
in the command prompt you need to type the next command:



 This is a very interesting decision by Microsoft and I fully support it, this time users will be able to pay less and to choose only applications that they need instead of paying for the whole package and not using it.
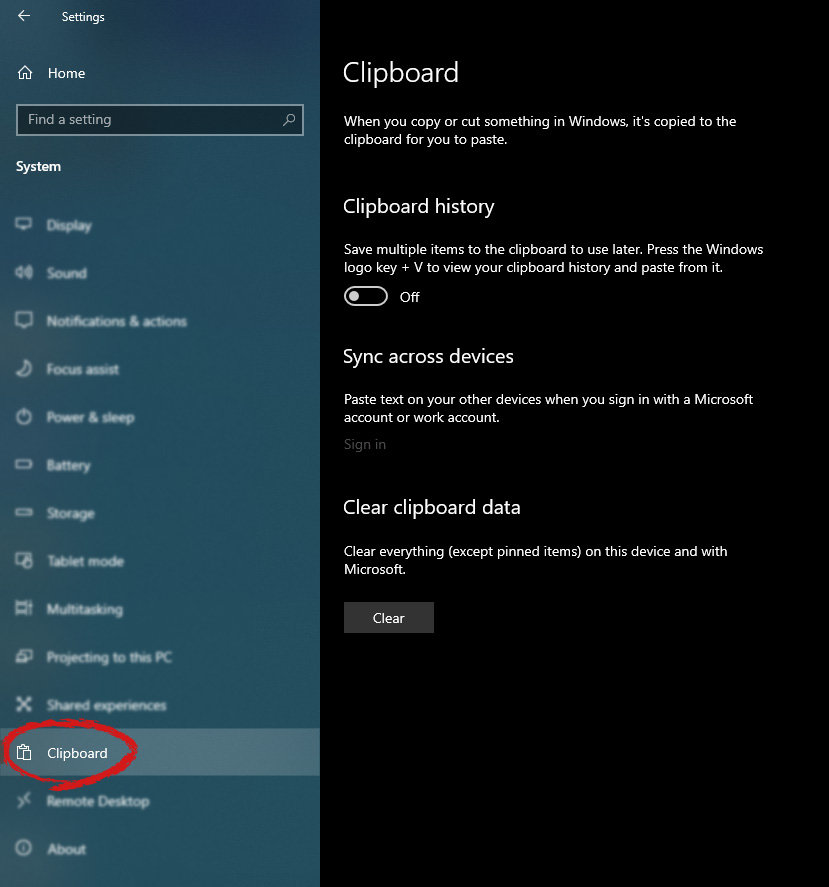
This is a very interesting decision by Microsoft and I fully support it, this time users will be able to pay less and to choose only applications that they need instead of paying for the whole package and not using it.  in system dialog click on the clipboard and on the right screen turn ON CLipboard history.
in system dialog click on the clipboard and on the right screen turn ON CLipboard history.