Code 0x80070070 – 0x50011 – What is it?
If you’ve recently tried installing Windows 10, you might have encountered error code 0x80070070 – 0x50011 or its alternatives (error code 0x80070070 – 0x50012 and 0x80070070 – 0x60000). Whatever formats this error code presents itself in, it's usually accompanied by a barrage of other errors, as underscored on Microsoft’s official site. If you’ve encountered this error code, it simply means that your computer system might not have the required or required space to install the upgrade.
Likely, if you’ve experienced error code 0x80070070 – 0x50011, it’ll likely appear in the formats highlighted below:
- 0x80070070 – 0x50011
- 0x80070070 – 0x50012
- 0x80070070 – 0x60000
Solution
 Error Causes
Error Causes
At present, this Windows 10 upgrade error is triggered or caused by various factors:
- Lack of computer resources or space
- Virus/malware infestation
- A clogged registry
Further Information and Manual Repair
Whilst new, not much information has been propagated regarding this error. However, there are some manual / practical steps you can take to have your Windows 10 upgrade up and running. Since the primary aspect of solving this problem is to make space on your computer system, here are some ways in which you can do so manually.
Method 1: Get more space
- Check the current space on your computer
Before making attempts to create space on your computer, it’s vital that you check to decipher how much free space you have available.
- Make use of Disk Clean-up
Since there’s a free service available on your computer to create space, why not use it and save time? If the Disk Cleanup tool is employed regularly, this will free up hard drive space and optimize your computer to work better.
- Remove unwanted desktop apps
There are several apps lying around on your computer that you simply don’t use, uninstall those and make space to elude error code 0x80070070 – 0x50011 or its alternatives (Code 0x80070070 – 0x50012, Code 0x80070070 – 0x60000)
- Remove or archive files
If you have lots of photos, media, documents (files), videos, etc, that you don’t use or will only need in the future, try cloud storage. You’ll still have those files within your possession but just not in a physical location. However, they’re still accessible. Another suggestion: If you use programs such as One Drive or Google Drive for desktop, limit your use to only the online application.
- Add more storage
If you’re not able to implement the above steps to clear some space to accommodate your Windows 10 upgrade due to error code 0x80070070 – 0x50011, acquire more storage. This can be expanded by incorporating storage devices such as USB flash drives, CDs, cloud storage, and SD Cards.
Method 2: Scan your computer for virus/malware
If you regularly download stuff, especially software on the Internet from ‘not so secured’ sites, you might have picked up something. You might have downloaded malware or virus (along with other legit programs).
To resolve this issue, it’s advised and very important that you download a powerful antivirus and perform a complete scan of your computer system. After you’ve detected and removed the suspected malware/virus, you’ll then be able to eliminate error code 0x80070070 – 0x50011 and resume with your Windows 10 upgrade.
Method 3: Clean up your computer’s registry
If you do not clean your computer’s registry often, it could become congested or clogged by .XML files, junk files, and cookies. To resolve this problem, clean your registry by using a powerful and user-friendly tool to clean up the problem.
Click here to download Restoro.


 For many people that are playing online games, this is not such a big deal since they always must have the latest version in order to play their games but for other ones, this has arrived as a bit of a problem. Many people preferred older game versions since often updates can change certain mechanics inside the game making it different as an experience or introduce some elements that not everyone likes.
So far, people could use the steamDB site to find depo of the game versions you would like to play and download it but if this beta code goes live that will not be an option anymore. Now, playing old games without updates could also be used for nostalgic reasons and these people have also been cut off with this update.
It is important to point that update is still in beta client only but users have already started to voice their opinions asking Valve not to place it live. In the end, it will all depend on Valve’s decision will they listen to their customers or decide to push updates on live service.
For many people that are playing online games, this is not such a big deal since they always must have the latest version in order to play their games but for other ones, this has arrived as a bit of a problem. Many people preferred older game versions since often updates can change certain mechanics inside the game making it different as an experience or introduce some elements that not everyone likes.
So far, people could use the steamDB site to find depo of the game versions you would like to play and download it but if this beta code goes live that will not be an option anymore. Now, playing old games without updates could also be used for nostalgic reasons and these people have also been cut off with this update.
It is important to point that update is still in beta client only but users have already started to voice their opinions asking Valve not to place it live. In the end, it will all depend on Valve’s decision will they listen to their customers or decide to push updates on live service. 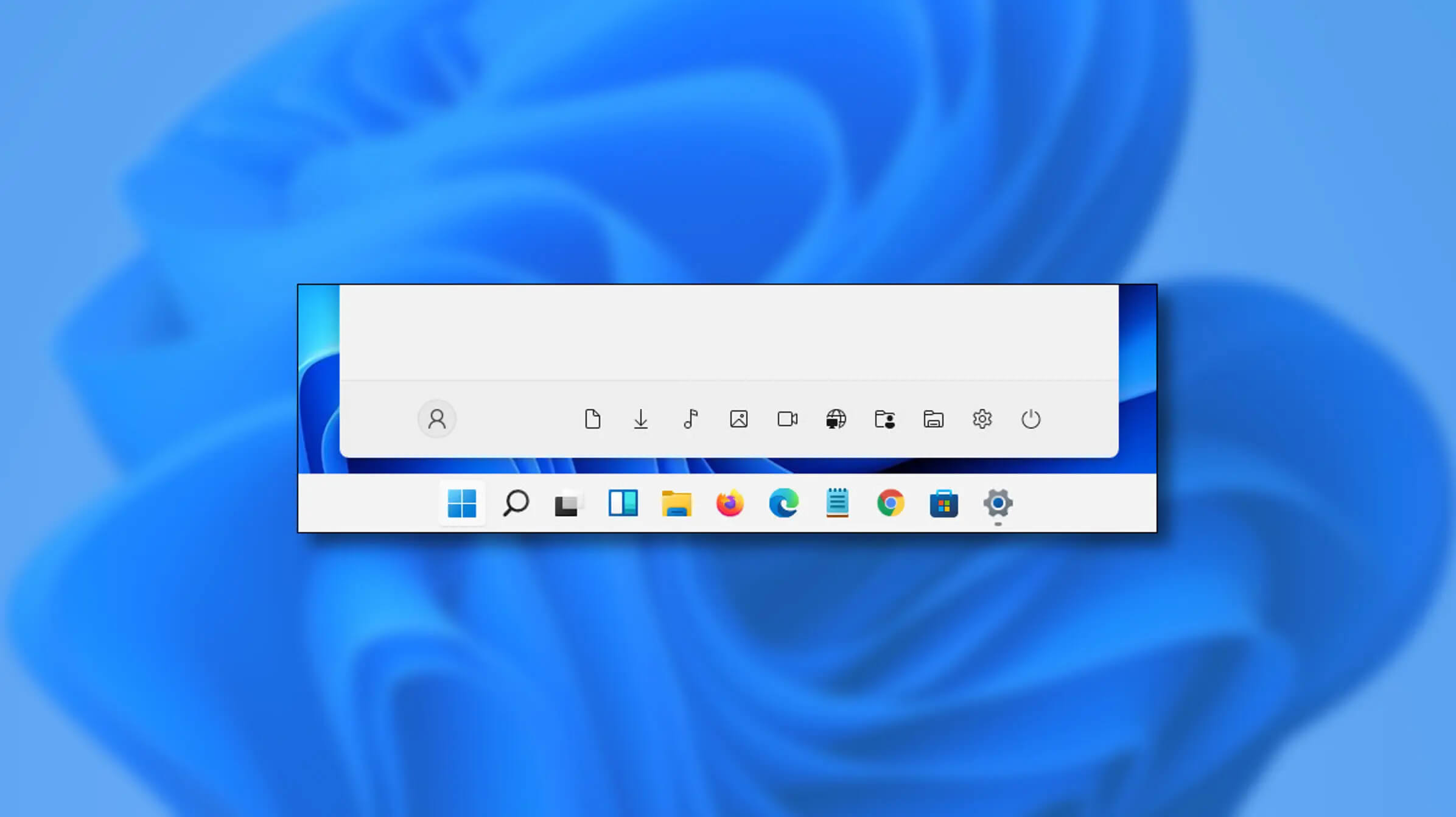 If you want to place these icons in your Star menu follow this step-by-step guide and you will have them in no time.
If you want to place these icons in your Star menu follow this step-by-step guide and you will have them in no time.
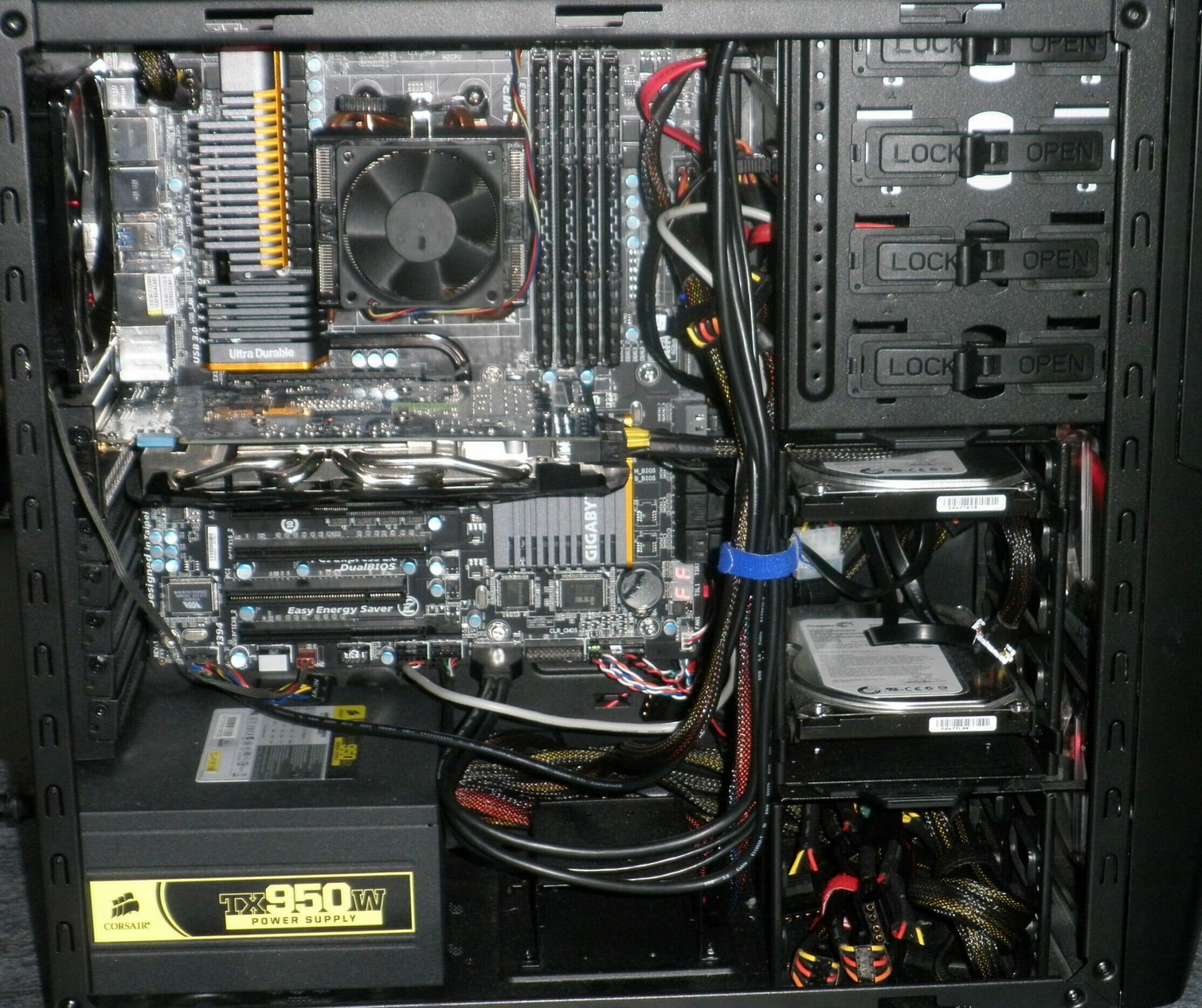
 Keeping your PC clean is not rocket science and you can do it with things you already and probably have in your house. One thing that I would recommend tho to purchase is antistatic gloves since they could prevent any kind of electrostatic discharges thus protecting your electric components.
If you have the option to disconnect your PC and get it outdoors, I would highly recommend this approach since all the dust will be dusted outside and not in the room where your computer is. If you can not it is still ok, but since some portion of dust will be set in the room, you might need to dust your room after cleaning your computer.
Keeping your PC clean is not rocket science and you can do it with things you already and probably have in your house. One thing that I would recommend tho to purchase is antistatic gloves since they could prevent any kind of electrostatic discharges thus protecting your electric components.
If you have the option to disconnect your PC and get it outdoors, I would highly recommend this approach since all the dust will be dusted outside and not in the room where your computer is. If you can not it is still ok, but since some portion of dust will be set in the room, you might need to dust your room after cleaning your computer.