The Event Viewer in the Windows operating system is used to troubleshoot any computer issues. It is one of the most useful tools that keep logs of both security and system events. It also monitors for both software and hardware problems in the computer. This tool is the only one with amazing features that maintain logs about everything that’s going on in the computer system. It keeps track of all the information to the point where going over them will take a lot of time.
Luckily, the Event Viewer tool now allows users to create custom views where you can set the filters and sort the data recorded to limit the information details to only what you’re interested in seeing. For instance, if you want to troubleshoot with one hard drive, you can just create a special custom view to display only the hard drive warnings in the security logs. This will save you hassle and time.
Take note that the logs in the Event Viewer are divided into two main categories namely the Window logs and the Application and Services logs. You can just set the filter to the logs by their event id, specific date, and many other events when you have to troubleshoot some problem in your computer. So if you are trying to troubleshoot a problem in your Windows 10 computer and you’re checking the Event Viewer, read on as this post will guide you in creating custom event views in the Event Viewer. To get started, refer to the instructions given below.
Step 1: Go to the Start menu and in the search box, type “event viewer” and then click on Event Viewer from the search results to open it.
Step 2: After opening Event Viewer, click on Custom Views located in the left pane of the window.
Step 3: Next, click on the Administrative events under the Custom View to create special log views.
Step 4: Then on the right side of the window, click on Create Custom View to open the Create Custom View window.
Step 5: There is a logged drop-down list under Filter. From there, you have the option to choose an appropriate predefined time or use a custom time range for your Custom log views.
Step 6: After that, select an appropriate event level for your custom view. You have fine entry-level options to choose from such as critical event level, error, warning, information and verbose.
- Critical – select this if you want to see the events that require your immediate attention in the custom view.
- Error – select this if you want your Event Viewer to display the events that are less critical but hints at the problems.
- Warning – select this event-level if you want to see the event with the potential problem but may not bound to happen.
- Verbose – select this if you want to see detailed information about all the events.
Step 7: After you’ve selected the event level, you now have to select how you want the events to be filtered. They can either be filtered By the log or By the source.
- By the log – you can select two options called Windows log and, Application and Service logs. The Windows logs allow you to filter the logs created during events like setup, security, applications, and system events. While the Application and Service logs filter the log created by the installed applications in your system.
- By the source – select this if you want your Custom View to search for information in event sources. It allows you to view events in detail for various applications and devices.
Note: You have the option to further customize the event logs with more filters like Event IDs, task category, keywords, User, and Computer. Using these additional filters, you can choose to filter the events in the special views by specifying event id numbers in the Event IDs, entering predefined Windows words in the Keyword, specify the user accounts in the User field, as well as choose the system from the server to maintain logs in the Computer field.
Step 8: Once you’re done customizing the log filter, click on OK to apply the changes made.
Step 9: After that, a Save Filter should be displayed in the Custom View window. Just enter the Custom View name and select the Event Viewer folder where you want to save the Custom view. The folder name should be Custom View by default. And if you want, you can also create your own folder if you want your custom views to be visible to all the system users.
Step 10: Next, check all the Users box located in the lower corner of the window and then click the OK button after you’re done.
You should now see the customized filter you just created on the left side of the window. Just click on it to check your filtered events in the center of the Event Viewer window. And for you to save the custom view logs, simply right-click on the Custom views you created and then click on Save All Events in the Custom View As from the drop-down menu. Then put a name on the file and select the appropriate location where you want to save the logs and click on the Save button. Note that the log file is saved with the “.EVTX” file extension and when you double click on it, it will open the file in the Event Viewer.

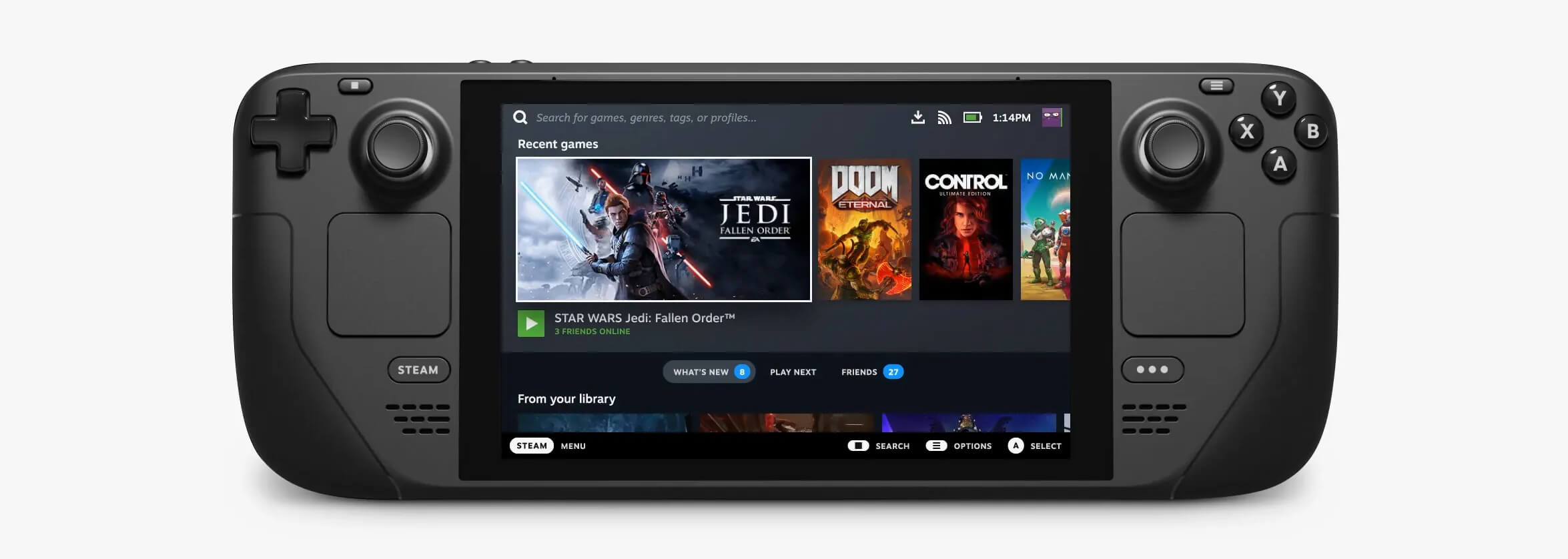 Valve has officially announced that Steam Deck will be compatible with Windows 11 despite TPM 2.0 Microsoft requirements.
From the beginning, Deck was announced like a mini handheld PC device. Powered with new Steam OS 3.0 based on Linux. However, besides out-of-the-box OS it was also stated that Deck will be a personal device meaning that other PC-based operating systems could be installed on it and even run your typical applications in it.
Since Microsoft announced Windows 11 hardware requirements, specifically the TPM 2.0 requirement many users voiced concern that Steam Deck will not be able to connect to Windows 11
TPM 2.0 is something that Microsoft requires for every internal and hardware component that is to connect on a Windows 11 device. This is to ensure that only trusted devices would be included in the array of a PC setup and avoid any problems like malicious hardware injecting software into a system.
This would also minimize the compromise Windows would have, as unverified or untrusted devices connect to a Windows PC.
However, Valve and AMD are ensuring us that Deck will not have any issue connecting to a PC running Windows 11 or even if you wish to transform Deck itself into a Device running Windows 11.
Valve has officially announced that Steam Deck will be compatible with Windows 11 despite TPM 2.0 Microsoft requirements.
From the beginning, Deck was announced like a mini handheld PC device. Powered with new Steam OS 3.0 based on Linux. However, besides out-of-the-box OS it was also stated that Deck will be a personal device meaning that other PC-based operating systems could be installed on it and even run your typical applications in it.
Since Microsoft announced Windows 11 hardware requirements, specifically the TPM 2.0 requirement many users voiced concern that Steam Deck will not be able to connect to Windows 11
TPM 2.0 is something that Microsoft requires for every internal and hardware component that is to connect on a Windows 11 device. This is to ensure that only trusted devices would be included in the array of a PC setup and avoid any problems like malicious hardware injecting software into a system.
This would also minimize the compromise Windows would have, as unverified or untrusted devices connect to a Windows PC.
However, Valve and AMD are ensuring us that Deck will not have any issue connecting to a PC running Windows 11 or even if you wish to transform Deck itself into a Device running Windows 11.  Odyssey Neo G9 is a successor to Odyssey G9 curved gaming monitor and it is aimed again at the gaming community with its specifications but of course, it can be used for work as well.
Gapping at a stunning $2500 USD price it is not really a cheap piece of hardware so it is normal to see what do you get for this kind of price and do features justify it, so let’s dive in.
Odyssey Neo G9 is a successor to Odyssey G9 curved gaming monitor and it is aimed again at the gaming community with its specifications but of course, it can be used for work as well.
Gapping at a stunning $2500 USD price it is not really a cheap piece of hardware so it is normal to see what do you get for this kind of price and do features justify it, so let’s dive in.
