What is Error 1723?
Error Code 1723 is a peculiar error type common in Windows PC. It is related to the Windows Installer package. This error is displayed in the following format:
"Error 1723- There is a problem with this Windows Installer package. A DLL required for this install could not be run. Contact your support personnel or package vendor...”
You are most likely to come across the error code 1723 if the Java installation is not completed successfully. In other words, the error indicates that the installation process has failed.
Solution
 Error Causes
Error Causes
The 1723 error may occur due to several reasons, the most common being:
- Corrupted installers
- Files are not extracted successfully
- Registry problems
- Missing DLL files
Further Information and Manual Repair
To resolve this issue on your PC, you don’t always have to hire a professional technician and pay hundreds of dollars to get it fixed. The error code 1723 may not be a common Windows PC error but it is easy to fix.
Here we have listed some of the best and easiest DIY ways to resolve this error on your system. These solutions are so easy to perform that even if you are not a computer programmer or technically adept, you can work through them and resolve the error in just a few simple clicks.
So, let’s get started:
Solution 1: Install the latest Java Version
If the Java version previously installed on your system is not working properly and showing 1723 error messages then it is advisable to install the
latest Java version.
However, to do this first you will have to uninstall the old version and then download the latest Java version on your PC from a trusted website to ensure it does not contain malicious viruses and malware.
Solution 2: Ensure the Required Files are extracted in the ‘Temp’ Folder for Installers
Another method to resolve the 1723 error code is to check whether the required files are extracted in the temp folder for installers or not.
The error may occur if the location is incorrect and the account is not permitted to extract files in the temp folder.
In this scenario, the best way to resolve the issue is to change the permissions of the temp folder. This can be done by logging in to your account and opening file explorer or ‘My Computer’. Now copy and paste this link address in the address bar: DL:UsersUSERNAMEAppDataLocal.
Please note, here DL is the drive letter of the Windows drive, and in the username insert the username of the account that you are using.
Now right-click the ‘temp’ folder. Select properties and click on the Security tab.
After that click edit below the list and press add. Again type the username here and click OK. The next step is to select the added account from the list and tick ‘FULL CONTROL’ box under ‘Permissions for Username’. Click OK and then close the properties. Once this process is complete, now try running the installer again. This will most likely resolve the issue.
Nonetheless, if the error still persists, then this means the underlying cause of the error is deeper than you think. The error may be related to registry issues. In such situations, try solution 3 to fix the error 1723 on your system.
Solution 3: Download Restoro.
When the error code 1723 is triggered due to registry issues, then it is advisable to scan your PC with Restoro. Registry issues should be resolved immediately because they pose serious threats to your system. It can lead to system failure, crash and valuable data loss.
Registry basically saves practically all the information and activities performed on your PC including the unnecessary and obsolete files like junk files, cookies, temporary files, and invalid entries.
If these files are not removed they can corrupt the registry, damage dll files and installers thereby generating error codes like 1723 on your system.
The easiest way to repair and
clean the registry in seconds is to run Restoro on your PC.
It is a smart, intuitive, advanced, and multi-functional PC repair tool. It is embedded with multiple powerful utilities and is a one-stop solution for all PC related issues. This software is compatible with all Windows versions.
It is deployed with a highly functional registry cleaner that scans and detects all registry issues on your PC and removes them right away. It wipes out the unwanted files, repairs the damaged dll files and restores the registry.
Other powerful utilities that are embedded in this software include an antivirus, a system optimizer and Active X controls and class modules.
To resolve 1723 error code on your PC today,
click here to download Restoro.
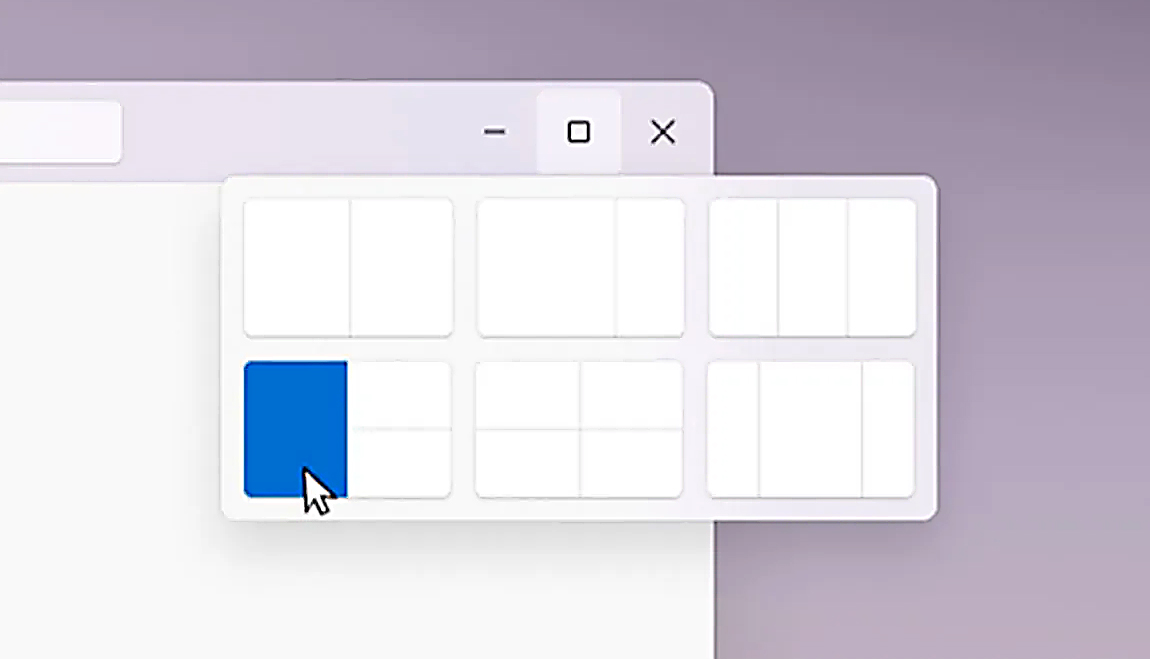
 Microsoft just released Windows 11 ISo file, based on the latest Insider Preview Build 22000.132. Inside build, you can try all-new features like clock updated app, snip tool, and everything releases so far via various patches. You can also use Windows 11 ISO file to do a clean install on your computer, but if you go with this option all of your existing files will be deleted.
Microsoft says it added the ability to name your PC during the setup experience. You’ll also get to experience the Get Started app that’s designed to help you get going on your new Windows 11 PC (even if it’s not actually a new one).
Microsoft just released Windows 11 ISo file, based on the latest Insider Preview Build 22000.132. Inside build, you can try all-new features like clock updated app, snip tool, and everything releases so far via various patches. You can also use Windows 11 ISO file to do a clean install on your computer, but if you go with this option all of your existing files will be deleted.
Microsoft says it added the ability to name your PC during the setup experience. You’ll also get to experience the Get Started app that’s designed to help you get going on your new Windows 11 PC (even if it’s not actually a new one).


 Removing options all together
Removing options all together As in most usual online scams, everything starts with a strange email containing threats and other poorly written and composed speech. At the end of the given email, there would be a link claiming that you, of course, need to read it and follow instructions about the threat, if you click the link it will open a web page where you will have an innocent-looking PDF file with more information about the threat itself.
If you click on a seemingly innocent PDF file it will summon Windows 10's AppInstaller.exe tool, kickstarting a download-and-run process that'll put you in a bad place very quickly. From there, you'll have to deal with the dangers of malware BazarBackdoor, including data and credential theft.
This kind of scam is nothing new but the interesting thing here is that it uses App installer and by clicking on a link you are opening and giving permission for a malicious crook to use it. So, stay safe and do not click on any links from unknown emails no matter what.
As in most usual online scams, everything starts with a strange email containing threats and other poorly written and composed speech. At the end of the given email, there would be a link claiming that you, of course, need to read it and follow instructions about the threat, if you click the link it will open a web page where you will have an innocent-looking PDF file with more information about the threat itself.
If you click on a seemingly innocent PDF file it will summon Windows 10's AppInstaller.exe tool, kickstarting a download-and-run process that'll put you in a bad place very quickly. From there, you'll have to deal with the dangers of malware BazarBackdoor, including data and credential theft.
This kind of scam is nothing new but the interesting thing here is that it uses App installer and by clicking on a link you are opening and giving permission for a malicious crook to use it. So, stay safe and do not click on any links from unknown emails no matter what. 