D3dx9_32.dll Error - What is it?
D3dx9_32.dll is basically a type of dynamic link library used to load and run different programs on the PC. The D3dx9_32.dll error message pops on the screen when this file is unable to load successfully. The error message is displayed in either of the following formats on the computer screen:
"The file d3dx9_32.dll is missing"
"D3DX9_32.DLL is missing. Replace D3DX9_32.DLL and try again."
"File d3dx9_32.dll not found"
"D3dx9_32.dll not found. Reinstalling might help fix this."
"Missing component d3dx9_32.dll"
This error usually pops while using gaming software. The D3dx9_32.dll error is displayed after a game is loaded or before the game-play begins. However, it may also appear in software that uses advanced graphic features.
Solution
 Error Causes
Error Causes
D3dx9_32.dll error may occur due to multiple causes. These include:
- The problem is related to Microsoft DirectX software. This software includes the D3dx9_32.dll file in its software collection.
- Incompatible Video Card Drivers
- Improper game installation
- DLL File Corruption
- Registry issues
- Viral infection
Further Information and Manual Repair
To avoid inconvenience, it is advisable to fix the error right away. To resolve it you don’t need to be a technical whiz or hire a technician. Luckily, the D3dx9_32.dll file error is quite easy to fix. Here are some of the best and effective DIY methods that you can try to remove the error:
Method 1 - Install the Latest Version of DirectX
Since D3dx9_32.dll error is related to DirectX software, it is advisable to make sure that you have the latest version of this software installed on your PC.
To install the updated version, simply go to Microsoft’s official website, download the software from there and install it on your PC. To activate changes, restart your computer.
Method 2 - Uninstall and then Re-install Gaming Application
If the error still persists, then the reason for it could be the gaming application. Sometimes D3dx9_32.dll error may also occur due to poor program installation.
Therefore, in this case it is recommended that you first uninstall the program by going to the Add/Remove program option. And once the program is uninstalled, try re-installing it on your PC. Hopefully, it will remove the error.
Method 3 - Restore the Damaged/Corrupt D3dx9_32.dll File
The error may also pop due to the damaged or corrupt D3dx9_32.dll file. This indicated registry issues.
When the registry becomes overloaded with unnecessary and obsolete files, there is not enough space for other files to store. Due to the poor registry maintenance, the system and dll files are often damaged. To restore the damaged D3dx9_32.dll file, you need to clean the registry first.
You can do this manually, but that will be quite time-consuming and slightly technical.
Therefore, download a registry cleaner. A registry cleaner scans all registry-related errors and removes them right away. It cleans the registry and restores the damaged dll files.
Method 4 - Scan for Viruses
If the D3dx9_32.dll error is triggered by viruses, then it is advisable to scan your PC with an antivirus. It will scan and removes all viruses from your system.
Whether D3dx9_32.dll error is related to registry issues or viral infection, download Restoro.
It is a cutting-edge, advanced, and multi-functional PC Fixer. A one-stop solution for all PC-related issues. It is deployed with a powerful registry cleaner, an antivirus, a system optimizer and several other scanners.
The registry cleaner detects and removes all registry errors and repairs damaged Dll files including D3dx9_32.dll file and simultaneously the antivirus utility scans your entire PC for all types of malicious software infecting your system including spyware, Trojans, adware and malware.
The system optimizer feature ensures your PC works at its optimal level.
Restoro PC Fixer is safe and efficient. It has a user-friendly interface which makes it quite easy for all levels of users to operate. In just a few simple clicks, errors are resolved.
In addition to this, you can download it on all Windows PC. It is compatible with all Windows versions.
Click here to download Restoro and resolve D3dx9_32.dll error code on your PC today.


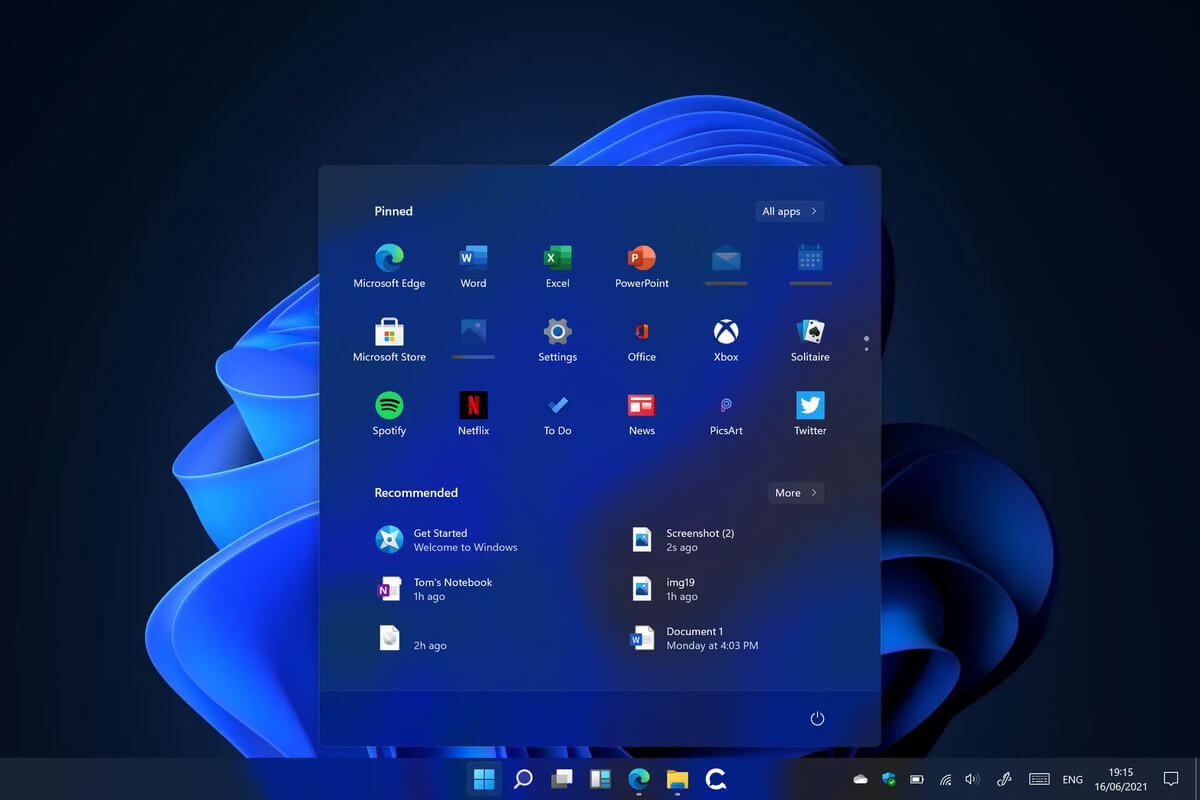 Microsoft’s initial Windows 11 hardware requirements were not really well received by users and they were not really clearly represented from the start making a lot of potential customers slowly drift away from the hype.
It seems that Microsoft has acknowledged this since they have changed their tune about system hardware requirements for the upcoming Windows 11.
It seems that Windows 11 will be able to be officially installed on unsupported computers but with a little inconvenience.
Microsoft’s initial Windows 11 hardware requirements were not really well received by users and they were not really clearly represented from the start making a lot of potential customers slowly drift away from the hype.
It seems that Microsoft has acknowledged this since they have changed their tune about system hardware requirements for the upcoming Windows 11.
It seems that Windows 11 will be able to be officially installed on unsupported computers but with a little inconvenience.
