We Couldn't Install Windows Technical Preview 0x80070070 - 0x20005 -- What is it?
Some Windows users have been experiencing errors in an attempt to upgrade to Windows 10 OS. This includes the “We Couldn’t Install Windows Technical Preview 0x80070070 – 0x20005” error code. If you’re one of the many users who’ve encountered this error, you might want to check the available space on your device. Error code 0x80070070 – 0x20005 occurs when you do not have the required space to be able to install the upgrade.
Solution
 Error Causes
Error Causes
Just like the other alternatives of error code 0x80070070 – 0x20005 such as
0x80070070 – 0x50011, 0x80070070 – 0x50012, and 0x80070070 – 0x60000,
We Couldn't Install Windows Technical Preview 0x80070070 - 0x20005 is most likely caused by the following:
- Insufficient disk space in your computer
- Incomplete installation or improper deletion of applications
- The device is infected with virus or malware
Further Information and Manual Repair
In order to upgrade to Windows 10, you need to have at least 40 to 50 GB of free space in your device. Thus, you need to free up some space in order to successfully upgrade your system to Windows 10. See below for the manual methods you can employ to solve your problem.
NOTE: It would be best to seek help from an experienced technician if you are not confident enough to perform the manual methods yourself or you can alternatively make use of an automated tool.
Method One: Clean Up Your Device
- Click Start then browse Afterwards, click on This PC.
- Right-click on Local Disk (C:) then choose
- Under the General tab, click on Disk Cleanup.
- Once the Disk Cleanup window appears, check all items you want to clear down, making sure that the recycle bin is empty and clear any temp files, as well as error logs. Click OK once you’re done.
- Repeating the same process above, clear down your system files as well to ensure that the old OS files from your previous system are taken down by clicking on Clean up system files in the Disk Cleanup window.
Method Two: Uninstall Unused Applications
Sometimes, there are unused applications just lying around your device. This may take up your needed space from your device for a system upgrade. Uninstalling these applications can make space that will eventually elude error code 0x80070070 – 0x20005 along with its alternatives – code 0x80070070 – 0x50011, code 0x80070070 – 0x50012, and code 0x80070070 – 0x60000.
- Open the Control Panel then select Programs and Features.
- Check on unused applications on your device
- Right-click on the unused application then select
Method Three: Remove or Archive Files
If there are tons of images, media, videos, or documents that you rarely use but will still be needing in the future, you can move these files to another drive where Windows 10 will not be installed on.
If there are no secondary drives in your device, consider using a USB Drive or external hard disk. Another option you can do is making use of cloud storage programs like One Drive or Google Drive. In this way, you’ll still have access to these files even if it’s not in a physical location while making larger space in your device.
Method Four: Scan Your Device For Viruses
Most Windows users download applications or software regularly. These applications or software might come from unsafe sites where you might have accidentally downloaded a virus or malware along with the legit application or software you intended to download.
With that said, it is highly recommended to download and install in your device a reliable and powerful antivirus. Using an antivirus, you can now perform an overall scan of your device’s system. Once you’re able to detect and remove any suspected virus or malware, you’ll now be able to get rid of the error code 0x80070070 – 0x20005. After solving the issue, you can now resume upgrading to Windows 10.
Method Five: Download An Automated Tool
Can’t seem to put up with the long and technical manual repair process? You can still fix this error by downloading and installing a powerful automated tool that will surely get the job done in a jiffy!

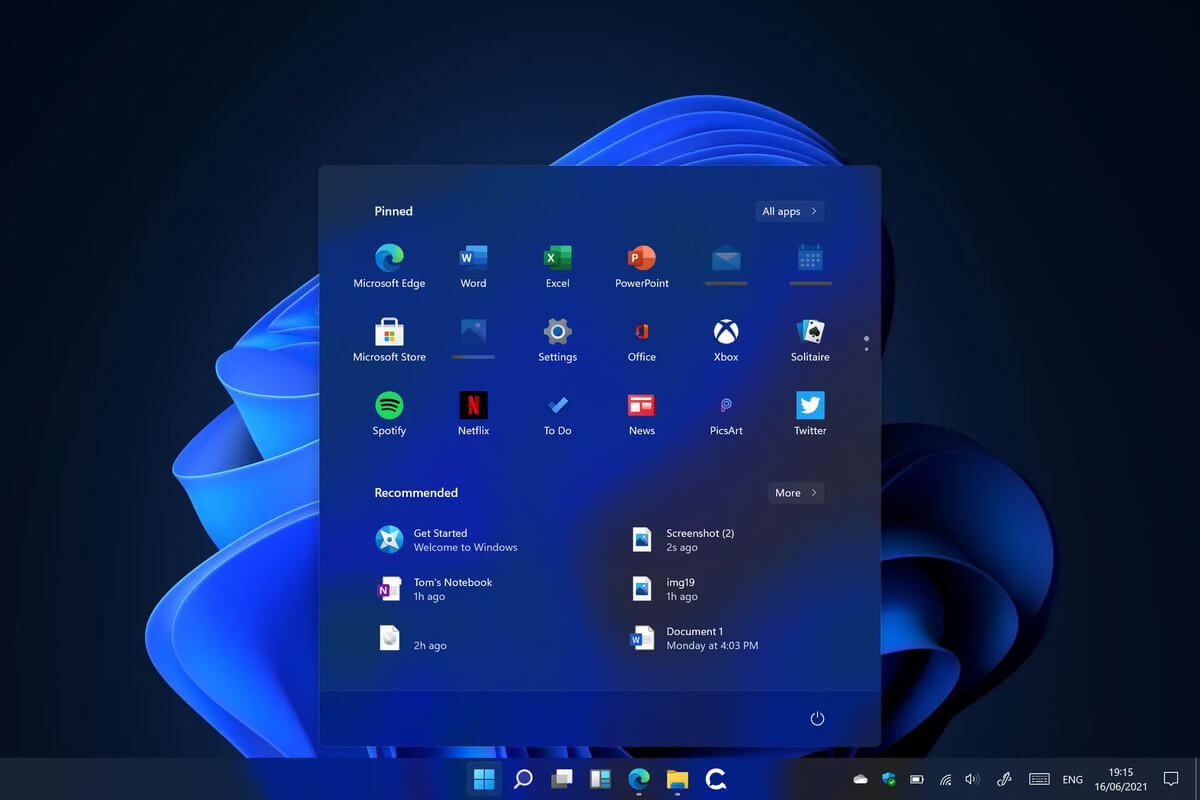 Microsoft’s initial Windows 11 hardware requirements were not really well received by users and they were not really clearly represented from the start making a lot of potential customers slowly drift away from the hype.
It seems that Microsoft has acknowledged this since they have changed their tune about system hardware requirements for the upcoming Windows 11.
It seems that Windows 11 will be able to be officially installed on unsupported computers but with a little inconvenience.
Microsoft’s initial Windows 11 hardware requirements were not really well received by users and they were not really clearly represented from the start making a lot of potential customers slowly drift away from the hype.
It seems that Microsoft has acknowledged this since they have changed their tune about system hardware requirements for the upcoming Windows 11.
It seems that Windows 11 will be able to be officially installed on unsupported computers but with a little inconvenience.

