Dxgkrnl.sys Error - What is it?
To understand Dxgkrnl.sys error code, it is important to develop an understanding about Dxgkrnl.sys file. Dxgkrnl.sys is a type of system file associated with Windows 8 Consumer Preview ISO images that are developed by Microsoft for the Windows OS.
System files like Dxgkrnl.sys are third-party device drivers, critical system files. These files enable attached PC hardware such as a printer to communicate with 3rd party software programs like web browsers and Windows 8 Consumer Preview ISO images.
Dxgkrnl.sys error code is a blue screen of death error. It occurs when the Dxgkrnl.sys files are unable to function properly. This is a critical error. It can cause system failure, crash, and data loss. Therefore, it must be resolved immediately before the damage is done.
The error may pop up in any one of the following formats
"STOP 0×00000050: PAGE_FAULT_IN_NONPAGED_AREA – dxgkrnl.sys"
A problem has been detected and Windows has been shut down to prevent damage to your computer. The problem seems to be caused by the following file: Dxgkrnl.sys."
"STOP 0x0000000A: IRQL_NOT_LESS_EQUAL – dxgkrnl.sys"
"Your PC ran into a problem and needs to restart. We’re just collecting some info, and then we’ll restart for you. If you would like to know more, you can search online later for this error: dxgkrnl.sys."
"STOP 0x0000001E: KMODE_EXCEPTION_NOT_HANDLED – dxgkrnl.sys"
Some of the common symptoms of this error code include
- Blue screen
- System freeze
- And sudden shutdown
Solution
 Error Causes
Error Causes
Dxgkrnl.sys error code may be triggered due to several reasons. These include:
- Incorrectly configured or corrupted Windows 8 Consumer Preview ISO images device drivers
- Windows registry issues
- Malware infection
- Hardware conflict
- Damaged hard disk
Further Information and Manual Repair
To resolve Dxgkrnl.sys error code on your PC, here are some effective and easy DIY methods that you can try:
Method 1 - Scan and Remove Viruses
Dxgkrnl.sys error may occur due to malware and viral infection. If this is the cause, then it is advisable to download a powerful antivirus and scan your entire PC. Remove all viruses from your system to resolve the error.
Method 2 - Utilize Windows System Restore to Undo Recent System Changes
Windows System Restore is an in-built powerful tool that enables Windows Operating System users to restore previous your PC to its former state. To repair Dxgkrnl.sys error, use this tool.
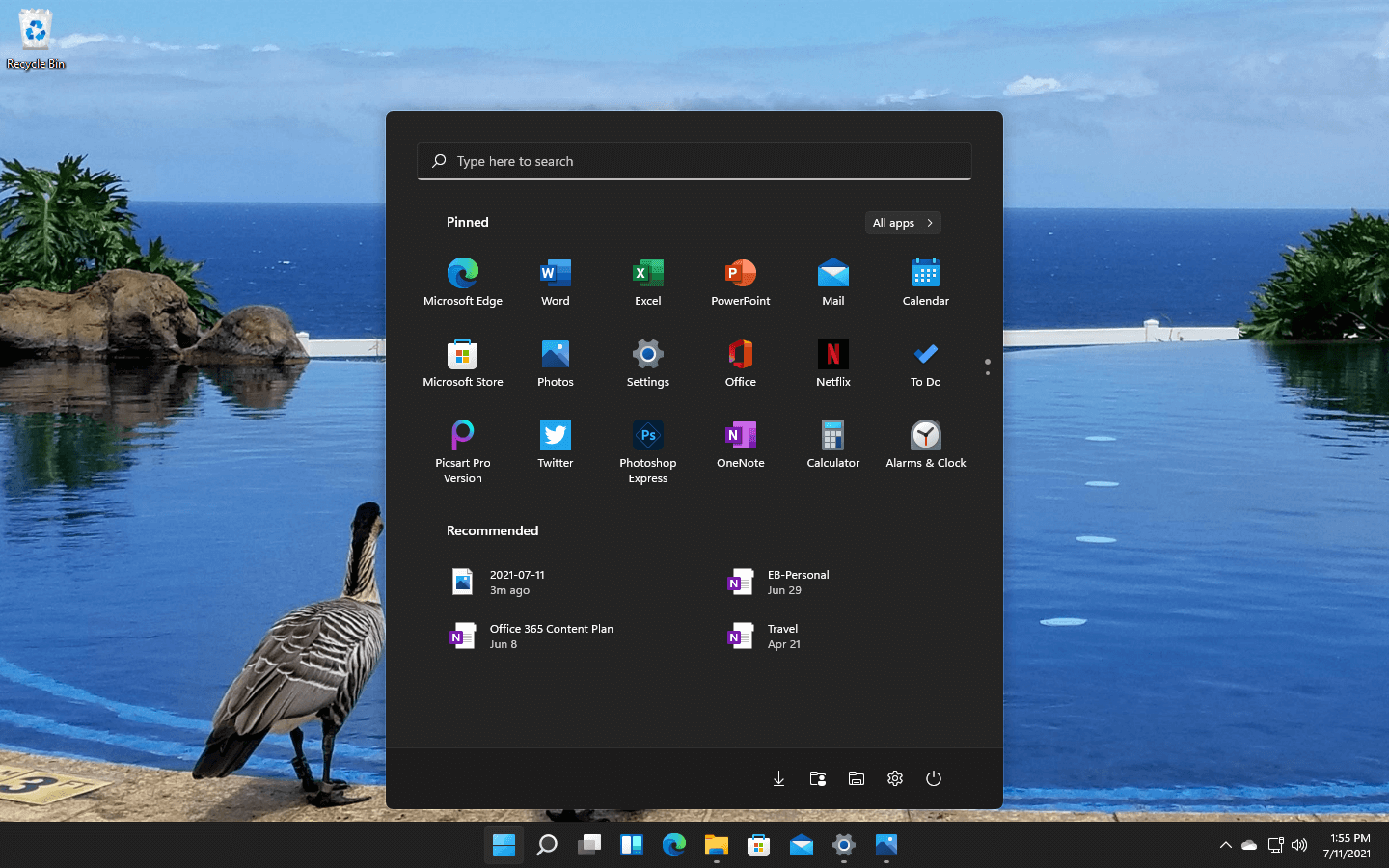
It can help you avoid hours of troubleshooting headaches associated with SYS errors. To get started, simply go to the start menu, type System Restore in the search box and press Enter.
Now click on System Restore to proceed. If you are prompted for an administrator password, insert it to move to the next step. Now to bring your computer to its former state, simply choose a restore point.
To activate these changes, reboot the PC. This is most likely to resolve the issue.
Method 3 - Clean the Registry
The registry is a collection of databases. It stores much of the information and activities you perform on your system including unnecessary and obsolete files like junk files, cookies, internet history, bad and invalid registry entries.
These files accumulate in the registry and damages and corrupt the registry itself. Due to this runtime and BSoD errors are triggered.
To repair and clean the registry manually can be time consuming and technical, therefore it is advisable to download Restoro. This is a user-friendly PC Fixer embedded with a powerful registry cleaner.
The registry cleaner scans your entire PC, wipes out all bad entries, cookies and unnecessary files, cleans the registry and repairs the damaged system files in seconds.
Click here to download Restoro and resolve Dxgkrnl.sys error today!


 Windows 11 has some cool animations including fading effects which make working in it feels nice and futuristic but the cost of this is that there is a slight delay to certain actions performed. If you want the snap fast feature in Windows 11 and do not care about this eye candy there is an easy way to turn animations off inside it.
Windows 11 has some cool animations including fading effects which make working in it feels nice and futuristic but the cost of this is that there is a slight delay to certain actions performed. If you want the snap fast feature in Windows 11 and do not care about this eye candy there is an easy way to turn animations off inside it.
