Error Code 0xc00007b – What is it?
Error code 0xc00007b usually manifests itself via the inability to start an application properly. It can occur when users attempt to run a game or other programs on their computer. In such a case, the application will not start and a message box will pop up stating that error code 0xc00007b has occurred. The error code is likely to occur when users attempt to run a program in the incorrect or inappropriate bit. For instance, if you try to load a 32bit location with a 64bit location.
Solution
 Error Causes
Error Causes
Error code 0xc00007b affects various versions of the Windows operating system, including Windows 7, 8, 8.1, and Windows 10. In the case of error code 0xc00007b for Windows 10, the error may be caused by issues related to software you’ve installed on your machine. This may cause software conflict resulting in the need to install programs like DirectX. Left unchecked, error code 0xc00007b could incite other error codes in Windows 10, such as error code 0xc004f034.
Further Information and Manual Repair
To repair error code 0xc00007b for Windows 10 devices, users will need to implement at least one manual repair procedure. Manual repair methods are effective in combating these issues as they can address the issues causing the error in the first place, thus fixing the problem.
The manual repair procedures for fixing error code 0xc00007b are very straightforward and can be implemented with little technical knowledge. However, you may need to contact a Windows repair technician if you have difficulty fixing the error code after completing the manual repair methods listed below.
Method One: Install Microsoft DirectX
Microsoft DirectX is an application usually included in the Microsoft operating system. It enables users to access high-speed gaming and multimedia on their PC. The latest version of this Windows technology is available on Microsoft’s official site.
Visit the Microsoft website and search for DirectX End-User Runtime Web Installer. Once you have located the latest version of the program, select the preferred language you would like DirectX to run in, and then click download. Run the program, then be sure to reboot your computer.
Note that this solution should only be applied if you are having issues running or displaying a gaming or multimedia application. Once you’ve correctly installed the latest version of DirectX, it should be able to fix underlying issues that may be causing error code 0xc00007b to occur. If you are still unable to run applications after completing this manual repair procedure, however, you will need to apply another method to fix error code 0xc00007b for Windows 10.
Method Two: Install Latest Version of .NET Framework
.NET Framework, a framework developed by Microsoft, provides solutions for users who may be having problems with applications. To download the latest version of the .NET framework, follow the steps listed below.
- Step one: Open your favorite web browser
- Step two: Enter www.microsoft.com/net
- Step three: Click Downloads
- Step four: Select the latest version of the .NET Framework by clicking the framework at the top of the list. (Currently, the latest version is .NET Framework 4.6.2.)
- Step five: Select preferred language, then download
- Step six: Run software.
To ensure you successfully download the latest version of the .NET Framework, verify your computer is properly connected to the Internet while downloading the software. Also, follow the instructions provided on the Microsoft website.
After completing the download process, reboot your computer then check if you have successfully resolved error code 0xc00007b for Windows 10. If this manual repair method is successful, you will be able to access your gaming and multimedia programs. Otherwise, the error code message box will reoccur, stating that the application error code is present on your device. Apply the next manual repair procedure to correct the error code if this reoccurs.
Method Three: Install Windows Updates
In certain instances, application error codes like error code 0xc00007b affect PC users who fail to install the most current Windows updates on their device. That is why it’s important to check your system and ensure you have installed all the latest updates.
The updates, if any are available, will automatically be installed on your PC once you access Windows Update in Settings. Reboot your computer then check if you are able to run programs that previously would not open due to error code 0xc00007b. If problems persist resulting in the reoccurrence of the error code, reinstall the applications you are unable to open or get help from a Windows repair technician.
Method Four: Download an Automated Tool
If you wish to always have at your disposal a utility tool to fix these Windows 8 and other related issues when they do arise, download and install a powerful automated tool.


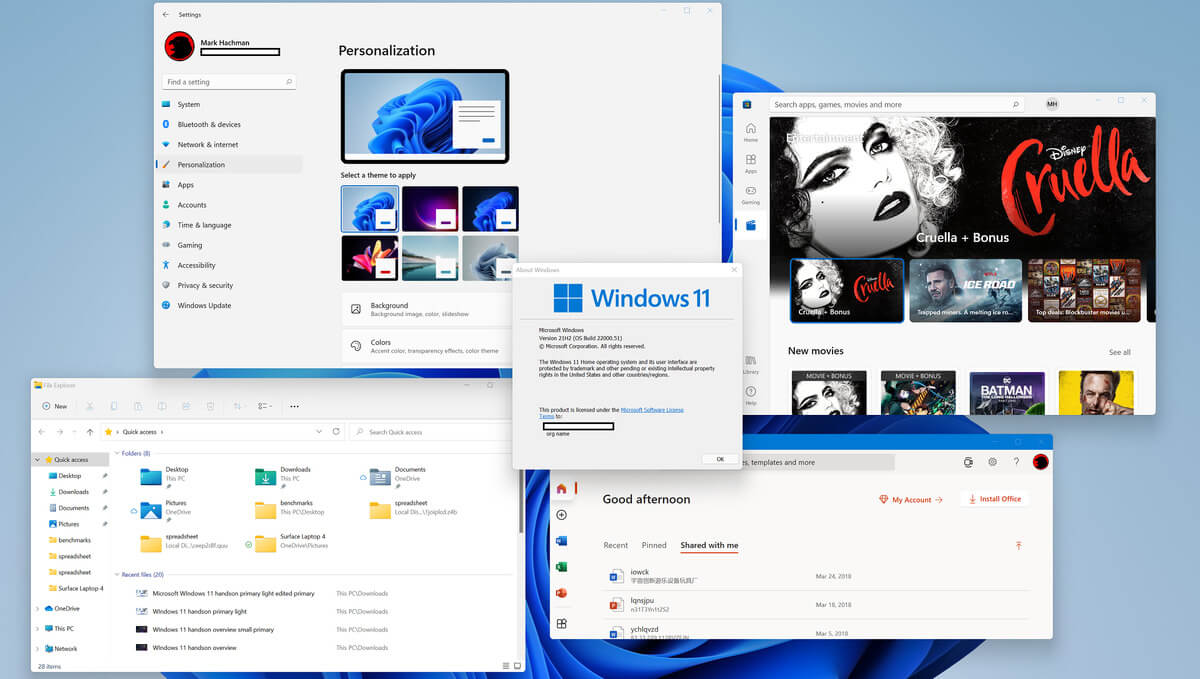 So far we probably all know what are good new and exciting features that W11 is bringing to the table, let’s talk now about features that will be removed and are not there but we had them in W10
So far we probably all know what are good new and exciting features that W11 is bringing to the table, let’s talk now about features that will be removed and are not there but we had them in W10
