ChatZum is a Potentially Unwanted Program that installs a Toolbar into your browser. This program allegedly allows users to zoom in on photos without clicking on them, however, upon further research, it was discovered that this function does not work on the latest version of browsers.
From the Author: ChatZum is a Browser add-on (toolbar) that enables its users to hover over images in Major Social network's websites and view a larger version of an image.
While installing this toolbar will track user web browsing sessions and will record website visits, clicks, and sometimes even personal information. This information is later used to display targeted ads to the user. To allow easier user tracking, the program changes the browser home page and default search engine to Nation Search Advanced, which injects additional advertisements and tracks user activity.
Several anti-virus applications have marked this program as Potentially Unwanted, and it is not recommended to keep it on your computer, especially considering the fact it will most likely not work on your browser.
About Potentially Unwanted Applications
If you have ever installed a free application or shareware, chances are high that the computer will get installed with a bunch of unwanted applications. A Potentially Unwanted Program, also called PUP, in short, is actually software that contains adware, installs toolbars, or has got other hidden objectives. These types of programs are generally bundled up with a free application that you download from the internet or may also be bundled inside the custom installers of many download websites.
PUPs aren’t always viewed as “pure” malware in the strictest sense. A fundamental difference between PUP and malware is distribution. Malware is normally dropped by silent installation vectors like drive-by downloads while PUP gets installed with the consent of the computer user, who knowingly or unknowingly approves the PUP installation on their computer system. But, there is no doubt that PUPs remain bad news for PC users as it could be quite dangerous to your computer in many ways.
The damage PUPs can do
The unwanted programs after installation display numerous annoying pop-up ads, trigger fake alerts, and sometimes even forces a computer owner to pay for the software. PUPs that come as browser add-ons and toolbars are commonly recognizable. These toolbars alter your homepage and your search engine in the installed web browser, track your web activities, modify your search results with redirects and sponsored links, and eventually slow down your browser and diminish your browsing experience.
Potentially unwanted programs use aggressive distribution methods to get onto your computer. The worst part of setting up a PUP is the adware, spyware, and keystroke loggers that could lurk inside. Even if the PUPs really aren’t inherently malicious, these applications still do practically nothing good on your PC – they’ll take valuable system resources, slow down your PC, weaken your computer security, making your PC more vulnerable to malware.
How to avoid ‘crapware’
• Read the EULA thoroughly. Look for clauses that state that you have to accept advertising and pop-ups or bundled applications from the company.
• Always opt for the custom if you’re offered an option between “Custom” and “Recommended” Installations – never ever click Next, Next, Next thoughtlessly.
• Use a good anti-malware application. Try Safebytes Anti-malware which can find PUPs and treat them as malware by flagging them for deletion.
• Be alert if you download and install freeware, open-source applications, or shareware. Do not ever install software applications that seem shady or malicious.
• Always download applications from the original website. The majority of PUPs find their way onto your laptop or computer is via download portals, so steer clear of it altogether.
Remember the fact that even though PUPs could potentially cause damage and hinder the proper functioning of the PC, they can’t enter into your system without your consent, so be alert not to provide them with it.
How One Can Get rid of Malware that is Blocking Websites or Preventing Downloads
Malware could potentially cause many kinds of damage to PCs, networks, and data. Some malware goes to great lengths to stop you from downloading or installing anything on your computer, especially antivirus software. If you’re reading this article, odds are you’re stuck with a malware infection that is preventing you to download or install the Safebytes Anti-Malware program on your PC. Even though this sort of problem can be tougher to circumvent, there are some steps you can take.
Make use of Safe Mode to resolve the issue
If the malware is set to run automatically when Microsoft Windows starts, stepping into safe mode could block the attempt. Just minimal required programs and services are loaded when you boot your computer in Safe Mode. To launch your Windows XP, Vista, or 7 computers in Safe Mode with Networking, do as instructed below.
1) Tap the F8 key repeatedly as soon as your PC boots, however, before the big Windows logo or black screen with white texts come up. This would invoke the Advanced Boot Options menu.
2) Choose Safe Mode with Networking with arrow keys and hit ENTER.
3) When this mode loads, you should have the internet. Now, obtain the malware removal program you want by utilizing the web browser. To install the program, follow the guidelines in the installation wizard.
4) Right after installation, do a full scan and allow the software program to get rid of the threats it detects.
Switch to an alternate internet browser
Some malware mainly targets certain browsers. If this is your situation, employ another internet browser as it might circumvent the computer virus. When you suspect that your Internet Explorer has been hijacked by a trojan or otherwise compromised by online hackers, the best thing to do is to switch over to an alternate internet browser such as Mozilla Firefox, Google Chrome, or Apple Safari to download your chosen security program – Safebytes Anti-Malware.
Create a portable USB antivirus for eliminating viruses
Another technique is to download and transfer an antivirus application from a clean computer to run a scan on the infected computer. Follow these steps to run the anti-malware on the affected computer.
1) Download the anti-malware on a virus-free PC.
2) Connect the flash drive to a USB slot on the clean computer.
3) Double click on the exe file to run the installation wizard.
4) Choose the USB stick as the location for saving the file. Follow the instructions on the screen to finish off the installation process.
5) Now, transfer the flash drive to the infected computer.
6) Run the Safebytes Anti-malware directly from the USB drive by double-clicking the icon.
7) Click the “Scan Now” button to start the virus scan.
Protect your PC from Malware With SafeBytes Security Suite
If you are looking to install an anti-malware program for your PC, there are lots of tools in the market to consider nonetheless, you just cannot trust blindly anyone, regardless of whether it is a paid or free program. A few of them are great but there are several scamware applications that pretend as authentic anti-malware programs waiting around to wreak havoc on your PC. You have to pick a company that develops industry-best anti-malware and it has earned a reputation as reliable. One of the highly recommended applications by industry analysts is SafeBytes Anti-Malware, the safest program for Microsoft Windows.
SafeBytes can be described as a highly effective, real-time antivirus application that is made to assist the average computer user in protecting their PC from malicious internet threats. Through its cutting-edge technology, this software will help you protect your computer against infections brought on by various kinds of malware and other internet threats, including spyware, adware, trojans, worms, computer viruses, keyloggers, ransomware, and potentially unwanted program (PUPs).
There are many wonderful features you’ll get with this particular security product. Listed below are some of the features you will like in SafeBytes.
Active Protection: SafeBytes offers a completely hands-free active protection and is set to observe, block, and kill all computer threats at its very first encounter. It will check your PC for suspicious activity at all times and its unrivaled firewall shields your computer from illegal entry by the outside world.
Robust, Anti-malware Protection: Using a critically acclaimed malware engine, SafeBytes offers multilayered protection which is made to catch and remove threats that are concealed deep inside your PC.
Web Security: Safebytes allots all sites a unique safety ranking that helps you to get an idea of whether the webpage you’re just about to visit is safe to view or known to be a phishing site.
Extremely Speed Scanning: SafeBytes’s virus scan engine is among the fastest and most efficient in the industry. It's targeted scanning significantly increases the catch rate for viruses which is embedded in various computer files.
Lightweight: SafeBytes is really lightweight software. It consumes an extremely small amount of processing power as it runs in the background which means you will not observe any computer performance difficulties.
24/7 Support: For any technical concerns or product assistance, you may get 24/7 expert assistance via chat and email.
To sum it up, SafeBytes Anti-Malware offers outstanding protection combined with an acceptable low system resources usage with both great malware detection and prevention. You now may realize that this particular tool does more than just scan and remove threats from your computer. You will get the best all-around protection for the money you pay on SafeBytes AntiMalware subscription, there’s no question about it.
Technical Details and Manual Removal (Advanced Users)
If you wish to do the removal of ChatZum manually rather than using an automated software tool, you can follow these simple steps: Navigate to the Windows Control Panel, click the “Add/Remove Programs” and there, choose the offending application to remove. In case of suspicious versions of web browser plug-ins, you can easily get rid of it through your web browser’s extension manager. You might also want to reset your home page and search providers, as well as delete browsing history, temporary files, and cookies.
If you choose to manually remove the system files and Windows registry entries, use the following list to make sure you know exactly what files to remove before undertaking any actions. Please note that only advanced users should try to manually edit the system files mainly because removing any single vital registry entry results in a serious problem or even a PC crash. In addition, certain malware is capable of replicating itself or preventing its removal. Doing this malware-removal process in Safe Mode is recommended.
Files:
Search And Delete:
tbcore3.dll
arrow_refresh.png
basis.xml
chatzum.dll
info.txt
inst.tmp
loaderie.js
suggestion_plugin.dll
TbCommonUtils.dll
tbcore3.dll
tbhelper.dll
TbHelper2.exe
uninstall.exe
uninstaller.exe
update.exe
Folders:
C:\Program Files\ChatZum Toolbar\
C:\Documents and Settings\username\Application Data\Mozilla\Firefox\Profiles\gb5e8gtn.default\extensions\staged\ADFA33FD-16F5-4355-8504-DF4D664CFE83
Registry:
Key HKLM\SOFTWARE\ChatZum Toolbar
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ChatZum Toolbar


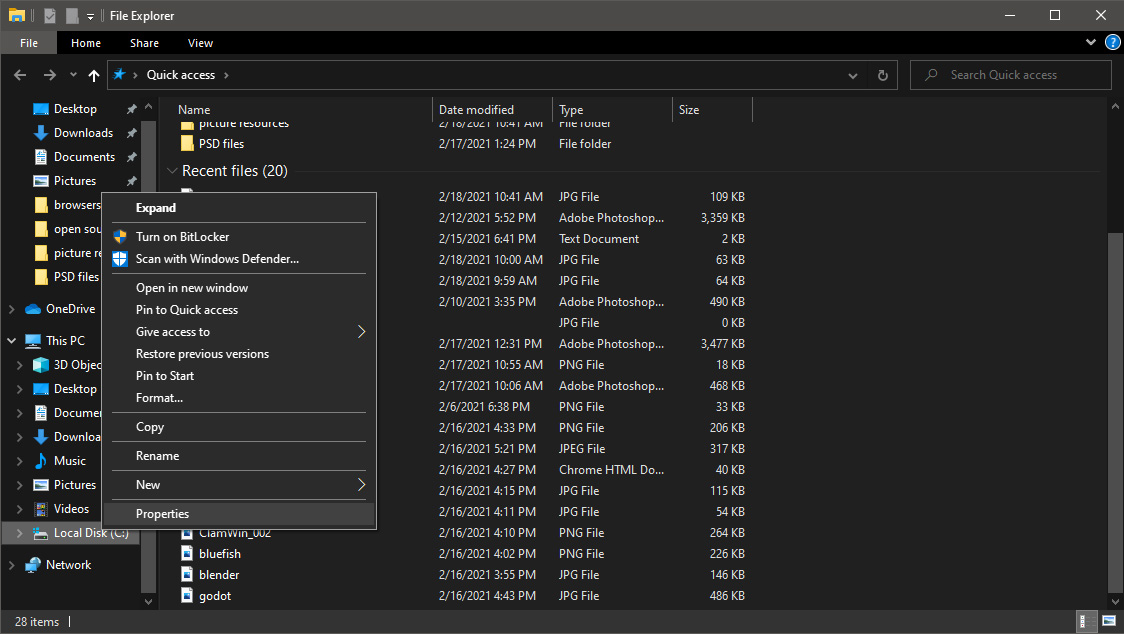
 Once File Explorer is up and running right-click on the hard drive you wish to run disk cleanup on and click on properties.
Once File Explorer is up and running right-click on the hard drive you wish to run disk cleanup on and click on properties.
 Properties Windows will open on the general tab, on that tab you have disk cleanup on the lower right part of properties, click on it.
Properties Windows will open on the general tab, on that tab you have disk cleanup on the lower right part of properties, click on it.
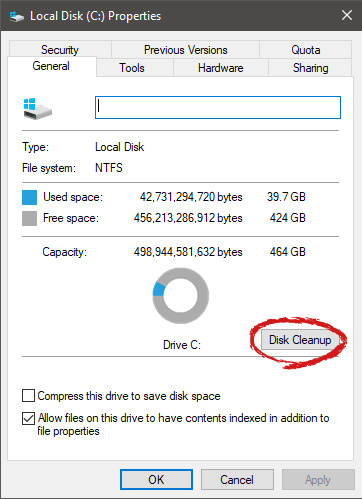 Wait for Windows to gather information about your hard drive and files on it. After it is finished you will be greeted with the next screen:
Wait for Windows to gather information about your hard drive and files on it. After it is finished you will be greeted with the next screen:
 Here you can thick and mark which items you would like to get rid of and which ones you would like to keep. Note that you can freely tick all of them and remove them since removing these files will not break WIndows in any way. make your choices and click on ok. You can also click on Clean up system files to run system files cleaner and get rid of junk there, you will not be able to choose any options there, Windows will alone clean up what is not needed.
After disk cleanup is finished least thing you will have is more free disk space, but like mentioned, keeping your Windows and computer healthy goes a long way in its usability, speed, and performance.
Here you can thick and mark which items you would like to get rid of and which ones you would like to keep. Note that you can freely tick all of them and remove them since removing these files will not break WIndows in any way. make your choices and click on ok. You can also click on Clean up system files to run system files cleaner and get rid of junk there, you will not be able to choose any options there, Windows will alone clean up what is not needed.
After disk cleanup is finished least thing you will have is more free disk space, but like mentioned, keeping your Windows and computer healthy goes a long way in its usability, speed, and performance. 
