HowToSimplified is a browser extension developed by MindSpark inc. This extension offers users easy access to DIY tutorials, guides, and websites just a few clicks away. There is also a top video selection with the most popular DIY videos at the moment.
This extension, though it may look useful in the beginning, hijacks your browser's default search provider, it changes your default home page to HowToSimplified, powered by the MyWay search engine. During your browsing sessions, it will record your website visits, collect information, clicks, and sometimes even personal data. This information is later used to deliver ads that are injected into your browser search results. Aside from sponsored links, and additional unwanted ads that this extension displays, it also may from time to time display pop-up ads during your browsing sessions.
Multiple anti-virus scanners have detected HowToSimplified as a Browser Hijacker and are therefore not recommended to keep on your computer for security and privacy reasons.
About Browser Hijackers
Browser hijacking means that a malicious program code has control over and altered the settings of your internet browser, without your approval. Almost all browser hijackers are made for marketing or advertising purposes. In most cases, browser hijacking is used for earning ad revenue that comes from forced advert clicks and site visits. It could seem naive, but most of such sites aren’t legitimate and could pose a severe threat to your online safety. In a much worst case, your browser can be hijacked to download malware that can do a lot of damage to your computer system.
How you can recognize a browser hijack
There are many symptoms that indicate your browser has been highjacked: home page is changed; bookmark and the new tab are also changed; the default web engine is changed and your browser security settings have been cut down without your knowledge; find new toolbars that you simply didn’t add; unstoppable flurries of popup advertisements show up on your personal computer screen; your internet browser has become unstable or starts running sluggishly; you can’t navigate to certain internet pages, like computer security software related websites.
How they invade PCs
Browser hijackers infect computer systems through malicious email attachments, downloaded infected documents, or by visiting infected websites. They can also be deployed via the installation of a web browser toolbar, add-on, or extension. Other times you may have accidentally accepted a browser hijacker as part of an application bundle (generally freeware or shareware). An example of some notorious browser hijacker includes Babylon, Anyprotect, Conduit, DefaultTab, SweetPage, Delta Search, and RocketTab, but the names are regularly changing.
Browser hijacking can lead to severe privacy issues and even identity theft, disrupt your browsing experience by taking command over outbound traffic, drastically slows down your personal computer by consuming a lot of resources, and cause system instability as well.
Browser Hijacker Malware – Removal
The one thing you can try to get rid of a browser hijacker is to find the malware inside the “Add or Remove Programs” list of the Windows Control Panel. It might or might not be there. When it is, uninstall it. However, many hijackers are harder to track down or remove since they might get themselves associated with some critical computer files that enable it to operate as a necessary operating-system process. Amateur computer users shouldn’t ever attempt the manual form of removal methods, since it requires detailed system knowledge to carry out repairs on the computer registry and HOSTS file.
How One Can Eliminate a Virus that is Blocking Websites or Preventing Downloads
Practically all malware is detrimental and the extent of the damage will vary greatly depending on the type of malware. Some malware is meant to hinder or block things that you want to do on your computer. It may well not let you download anything from the web or it will prevent you from accessing a few or all internet sites, especially the anti-malware websites. If you are reading this article right now, you may have perhaps realized that a malware infection is the cause of your blocked internet connectivity. So how to proceed if you need to install an anti-malware program like Safebytes? There are a few actions you can take to get around this problem.
Install the anti-malware in Safe Mode
The Windows operating system comes with a special mode referred to as “Safe Mode” where just the minimum required applications and services are loaded. If the malware is obstructing the internet connection and affecting your PC, starting it in Safe Mode allows you to download anti-malware and run a diagnostic scan while limiting potential damage. To enter into Safe Mode or Safe Mode with Networking, press the F8 key while the PC is starting up or run MSCONFIG and look for the “Safe Boot” options under the “Boot” tab. Once you’re in Safe Mode, you can attempt to install your anti-malware software application without the hindrance of the malicious software. At this point, you can actually run the antivirus scan to get rid of viruses and malware without interference from another malicious application.
Obtain the anti-malware program using an alternate web browser
Web-based viruses can be environment-specific, targeting a particular internet browser or attacking specific versions of the web browser. If you seem to have a trojan attached to Internet Explorer, then switch to a different browser with built-in security features, such as Firefox or Chrome, to download your favorite anti-malware program – Safebytes.
Install and run anti-malware from the USB drive
Another solution is to create a portable anti-malware program on your USB thumb drive. Try these simple measures to clear up your infected PC using portable anti-malware.
1) Download the anti-malware on a virus-free computer.
2) Plug the Thumb drive into the uninfected computer.
3) Double-click the Setup icon of the antivirus program to run the Installation Wizard.
4) Choose a thumb drive as the place when the wizard asks you where you want to install the application. Follow the on-screen instructions to complete the installation.
5) Transfer the USB drive from the uninfected PC to the infected PC.
6) Double-click the EXE file to run the Safebytes software right from the thumb drive.
7) Click on “Scan Now” to run a complete scan on the affected computer for viruses.
If, after all of these methods, you are still having troubles with the possible infection, feel free to write to us with your question, through chat or email. If you are unsure which method to employ, simply call our toll-free number 1-844-377-4107 to speak to our technical support team. Our experts can walk you through the virus removal process on the phone and fix the computer remotely.
Protect Your Personal Computer From Viruses and Malware With SafeBytes Security Suite
Nowadays, an anti-malware tool can protect your laptop or computer from various kinds of internet threats. But exactly how to choose the best one amongst the many malware protection software that is available on the market? Perhaps you might be aware, there are several anti-malware companies and products for you to consider. A few of them are great but there are lots of scamware applications that pretend as authentic anti-malware software waiting to wreak havoc on the computer. You must be careful not to choose the wrong product, especially if you purchase a paid application. When thinking about trustworthy programs, Safebytes AntiMalware is certainly the highly recommended one.
SafeBytes anti-malware is a powerful, highly effective protection tool designed to assist users of all levels of IT literacy in detecting and eliminating malicious threats from their PC. This tool can easily detect, eliminate, and protect your PC from the most advanced malware intrusions including spyware, adware, trojan horses, ransomware, parasites, worms, PUPs, as well as other possibly damaging software programs.
SafeBytes has great features when compared to other anti-malware programs. A few of them are listed as below:
Best AntiMalware Protection: Built on a highly acclaimed anti-virus engine, this malware removal application has the capacity to identify and remove various obstinate malware threats such as browser hijackers, potentially unwanted programs, and ransomware that other common anti-virus software will miss.
Live Protection: SafeBytes provides real-time active monitoring service and protection against all known computer viruses and malware. It’ll constantly monitor your computer for hacker activity and also gives users superior firewall protection.
Web Protection: Safebytes allots all websites a unique safety score that helps you to have an idea of whether the webpage you’re about to visit is safe to view or known to be a phishing site.
“Fast Scan” Features: SafeBytes Anti-Malware possesses a multi-thread scan algorithm that works up to five times faster than any other protection software.
Very Low CPU and RAM Usage: SafeBytes is a lightweight application. It uses up a really small amount of processing power as it works in the background therefore you won’t notice any computer performance difficulties.
24/7 Customer Support: You will get 24/7 technical support to quickly resolve any concern with your security tool.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove HowToSimplified without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by HowToSimplified
Files:
C:DOCUME1USER1LOCALS1Tempnsu1.tmp
C:76681c9c0f70e45328483cc27310678c28751a66f9849aa13f34d2e7f8c650
C:DOCUME1USER1LOCALS1Tempnsf2.tmp
C:DOCUME1USER1LOCALS1Tempnsf2.tmpnsDialogs.dll
C:DOCUME1USER1LOCALS1Tempnsf2.tmpSystem.dll
C:DOCUME1USER1LOCALS1Tempnsf2.tmpnsDialogs.dll
C:DOCUME1USER1LOCALS1Tempnsf2.tmpSystem.dll
C:Program FilesHowToSimplified_8e
Registry:
Key: HKCUSOFTWAREMicrosoftWindowsCurrentVersionExplorerBrowser Helper ObjectsValue: Verizon Broadband Toolbar Data: A057A204-BACC-4D26-8398-26FADCF27386
Key: HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun Value: Hoolapp Android Data: C:usersuserappdataRoamingHOOLAP~1Hoolapp.exe
Key: HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun Value: ctfmon.exe Data: C:Program Files3rundll32.exe C:Program Files3lni28.dat,FG00
 Click on command prompt (admin)
Click on command prompt (admin)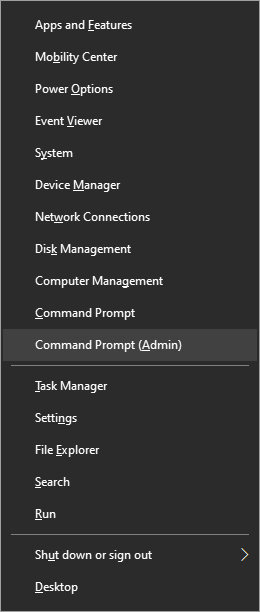 Type in command prompt following:
Type in command prompt following:
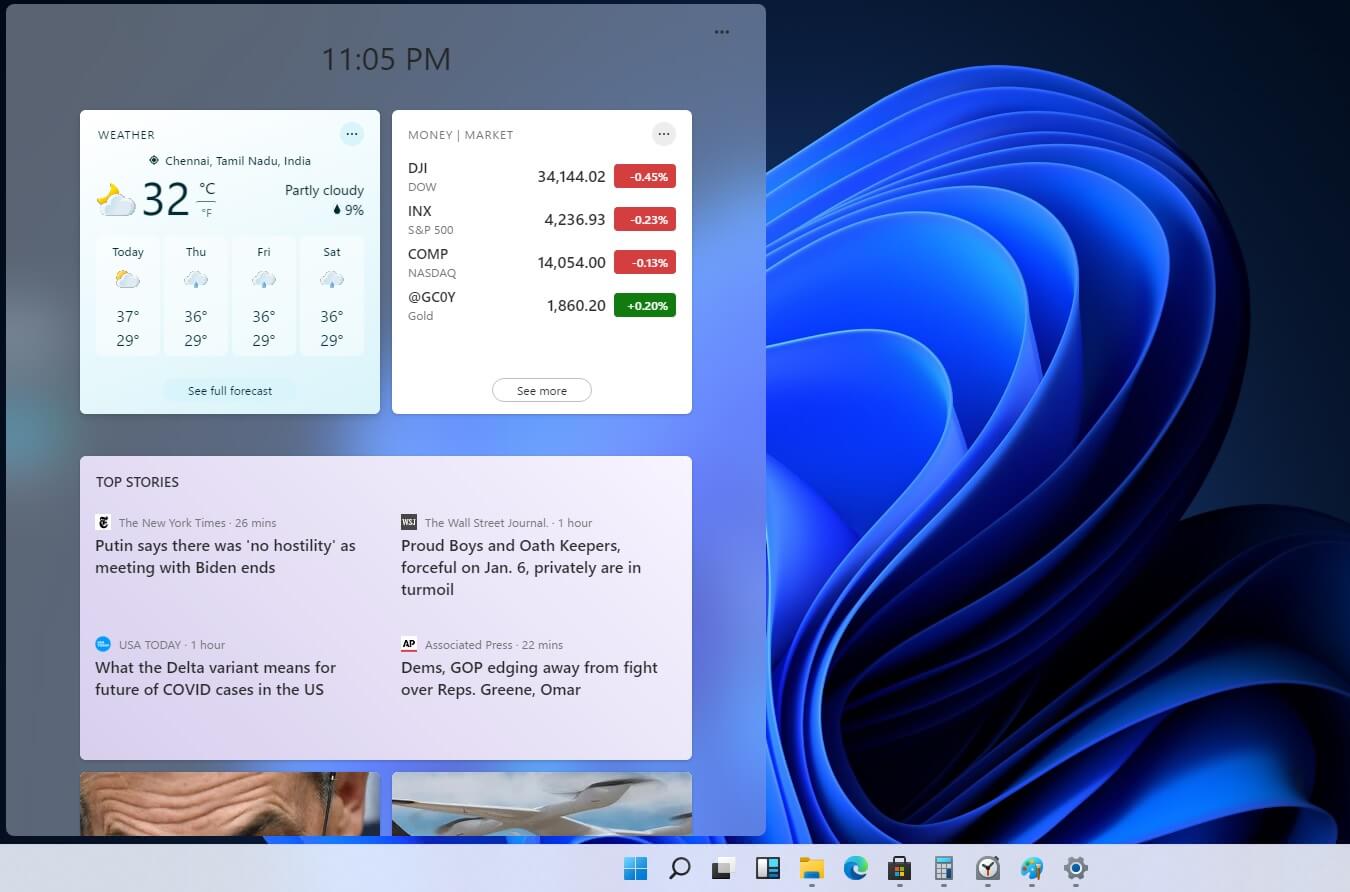 Originally Microsoft has imagined its widgets menu as Microsoft-only widgets but it seems that they have changed their mind.
Due to the latest leak, it seems that Microsoft will open the widgets menu to 3rd party developers as well but at launch, it will be only official widgets. It was hinted that later widgets menu will be open to developers who want to bring their own stuff into it.
Distribution, date, and technology that will need to be used in order to create your widget have not been discussed nor leaked at a given time but in some way, I am very glad that at least some customization will be in Windows 11.
It is funny and amusing how some things that were in Windows Vista are getting back like glass design, round corners, and widgets. Let’s just hope Windows 11 will be a better Windows than Vista was.
Originally Microsoft has imagined its widgets menu as Microsoft-only widgets but it seems that they have changed their mind.
Due to the latest leak, it seems that Microsoft will open the widgets menu to 3rd party developers as well but at launch, it will be only official widgets. It was hinted that later widgets menu will be open to developers who want to bring their own stuff into it.
Distribution, date, and technology that will need to be used in order to create your widget have not been discussed nor leaked at a given time but in some way, I am very glad that at least some customization will be in Windows 11.
It is funny and amusing how some things that were in Windows Vista are getting back like glass design, round corners, and widgets. Let’s just hope Windows 11 will be a better Windows than Vista was. 
