myBrowser is a Potentially Unwanted Program that allows users to access the internet. This browser suggests users install other PUP like myfiles, myemail, and others.
This application claims to be a good reliable portable internet browser, however during our test use of the program several website scripts crashed and were not able to open up all the website assets required, leaving the users with a mediocre browsing experience.
While browsing the internet through this program, you might see additional ads and sponsored links injected into your search results and/or websites.
About Potentially Unwanted Applications
What is a Potentially Unwanted Program (PUP)?
Everyone has experienced it – you download and install a free application, you then notice some unwanted programs on your computer system, come across a strange toolbar on your web browser, or find your default search engine has been changed to something else. You didn’t set them up, so how did they turn up? Potentially Unwanted Programs (PUP), also referred to as Potentially Unwanted Applications (PUA), are programs that you never wanted in the first place and often come bundled with freeware software. Once installed, most of these applications can be difficult to eliminate and become much more of an annoyance rather than a necessity.
PUP doesn’t involve malware in the traditional sense. A basic difference between PUP and malware is distribution. Malware is commonly dropped by silent installation vectors such as drive-by downloads while PUP gets installed with the consent of the user, who knowingly or unintentionally authorizes the PUP installation on their PC. PUP developers may argue that their programs aren’t malicious software but they can still be dangerous software and put the computer at risk much the same way a computer virus does.
What do PUPs do on your PC, precisely?
Unwanted programs can be found in various forms. Usually, they will be found in adware bundlers that are known to utilize aggressive and misleading advertising. The majority of bundlers install many adware applications from several vendors, each of which features its own EULA policy. Safebytes Anti-malware entirely removes this threat and protects your PC against unwanted programs or malware infection. PUPS also appear in the form of undesirable toolbars or web browser add-ons. They may change your internet browser settings, monitor your surfing activities and online searches, take up a large amount of space on your monitor, and degrade your web browsing experience.
Potentially Unwanted Programs at times act quite similarly to computer viruses or spyware. They will often carry keyloggers, dialers, and other programs built inside them that may track you or send your sensitive details to third parties. Even if the PUPs aren’t basically malicious, these programs still do absolutely nothing good on your computer – they will take precious resources, slow down your PC, weaken your device’s security, making your PC more vulnerable to trojans.
Protect yourself from PUPs
• Read very carefully before you install anything. Do not click accept till you have read the fine print. There will probably be a clause about PUPs.
• Always select “Custom” or “Advanced” installation and never blindly click the Next button, which will let you uncheck any foistware software programs you do not want.
• Use an anti-PUP program. Security software like Safebytes Anti-malware provides the very best real-time protection against PUPs and also other malware.
• Be alert if you install freeware, open-source software, or shareware. Don’t install programs that appear suspicious or malicious.
• Always download software from reliable sources like official websites instead of untrustworthy sharing space. Stay away from file-hosting sites where/when possible.
Comply with these guidelines and you should more or less never get potentially unwanted programs on your PC
What To Do When You Cannot Install Safebytes Anti-Malware?
Malware could cause all kinds of damage once they invade your PC, from stealing your private details to deleting files on your computer. Some malware is designed to restrict or prevent things that you wish to do on your computer. It may well not let you download anything from the internet or stop you from accessing a few or all of the internet sites, particularly the anti-malware sites. So what you should do if malware prevents you from downloading or installing Safebytes Anti-Malware? Follow the instructions below to eliminate malware by alternate methods.
Make use of Safe Mode to fix the problem
If any virus is set to run automatically when Microsoft Windows starts, stepping into safe mode could very well block this attempt. Since only the minimal programs and services launch in Safe Mode, there are hardly any reasons for issues to occur. Below are the steps you need to follow to start into the Safe Mode of your Windows XP, Vista, or 7 computers (check out the Microsoft website for instructions on Windows 8 and 10 computers).
1) Hit the F8 key repeatedly as soon as your PC boots, but before the big Windows logo comes up. This will bring up the Advanced Boot Options menu.
2) Make use of the arrow keys to select Safe Mode with Networking and press ENTER.
3) When this mode loads, you should have the internet. Now, make use of your internet browser to download and install an anti-malware application.
4) Right after the software is installed, let the scan run to remove viruses and other threats automatically.
Obtain the antivirus software using a different browser
Some malware mainly targets specific web browsers. If this sounds like your case, make use of another internet browser as it might circumvent the virus. If you’re not able to download the security application using Internet Explorer, this means the virus is targeting IE’s vulnerabilities. Here, you should switch to another internet browser such as Chrome or Firefox to download the Safebytes program.
Create a bootable USB antivirus drive
Here’s another solution which is creating a portable USB anti-virus software package that can scan your system for malware without needing installation. Adopt these measures to run the anti-virus on the affected PC.
1) Download Safebytes Anti-Malware or Microsoft Windows Defender Offline onto a clean PC.
2) Plug in the pen drive into the uninfected computer.
3) Double click on the exe file to open the installation wizard.
4) When asked, choose the location of the USB drive as the place in which you want to store the software files. Follow the directions to finish the installation process.
5) Now, transfer the flash drive to the infected computer.
6) Double-click the EXE file to open the Safebytes tool right from the flash drive.
7) Click the “Scan” button to run a full computer scan and remove malware automatically.
SafeBytes Anti-Malware: Lightweight Malware Protection for Windows Computer
If you’re looking to download the anti-malware program for your computer, there are numerous tools on the market to consider however, you should not trust blindly anyone, irrespective of whether it is a paid or free program. Some of them do a good job in removing threats while some will ruin your computer themselves. You have to select one that is reliable, practical and has a good reputation for its malware source protection. On the list of strongly recommended tool by industry experts is SafeBytes Anti-Malware, a well known security software for Microsoft Windows.
SafeBytes is a powerful, real-time anti-malware application that is designed to assist the common computer user in safeguarding their computer from malicious threats. With its outstanding protection system, this tool will quickly detect and eliminate the majority of the security threats, which includes adware, viruses, browser hijackers, ransomware, trojans, worms, and PUPs.
SafeBytes anti-malware takes computer protection to a whole new level with its enhanced features. The following are some of the great features included in the software.
Live Protection: SafeBytes offers real-time active checking and protection against all known viruses and malware. It will continuously monitor your pc for hacker activity and also gives end-users superior firewall protection.
Best AntiMalware Protection: This deep-cleaning anti-malware application goes much deeper than most antivirus tools to clean your computer. Its critically acclaimed virus engine locates and disables hard to remove malware that hides deep within your computer.
Website Filtering: SafeBytes provides instant safety rating to the webpages you’re going to visit, automatically blocking unsafe sites and to make sure that you are certain of your safety while browsing the internet.
Lightweight Utility: SafeBytes is a light-weight application. It consumes a very small amount of processing power as it works in the background so you are free to use your Windows-based computer the way you really want.
Premium Support: You will get 24/7 technical assistance to quickly resolve any concern with your security application.
SafeBytes can keep your PC protected from the latest malware threats automatically, thus keeping your online experience secure and safe. Now you may realize that this tool does more than just scan and delete threats in your computer. If you’re looking for the very best malware removal tool out there, and if you don’t mind spending some dollars for it, opt for SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
If you want to carry out the removal of myBrowser manually instead of using an automated software tool, you can follow these simple steps: Proceed to the Windows Control Panel, click on the “Add/Remove Programs” and there, choose the offending application to remove. In cases of suspicious versions of browser extensions, you can easily remove them through your web browser’s extension manager. You will most probably also want to totally reset your internet browser to its default settings.
Lastly, check your hard disk for all of the following and clean your Windows registry manually to remove leftover application entries after uninstalls. Please remember that only advanced computer users should try to manually edit the registry because incorrect file deletion leads to a major problem or even a PC crash. Moreover, some malicious programs have the capability to defend against its deletion. Carrying out this in Safe Mode is advised.

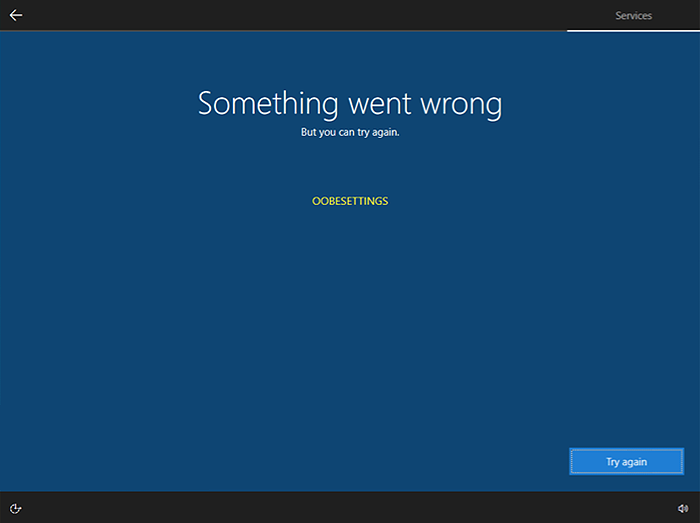 Oobesttings error is the blue screen of death error caused by some faulty settings inside the Windows registry. The good news is that this is not a hard error to fix and if by any chance you are one of the unfortunate people getting this dreaded annoying error, please do keep reading because we have several things that you can do in order to eliminate this issue from your computer.
Oobesttings error is the blue screen of death error caused by some faulty settings inside the Windows registry. The good news is that this is not a hard error to fix and if by any chance you are one of the unfortunate people getting this dreaded annoying error, please do keep reading because we have several things that you can do in order to eliminate this issue from your computer.


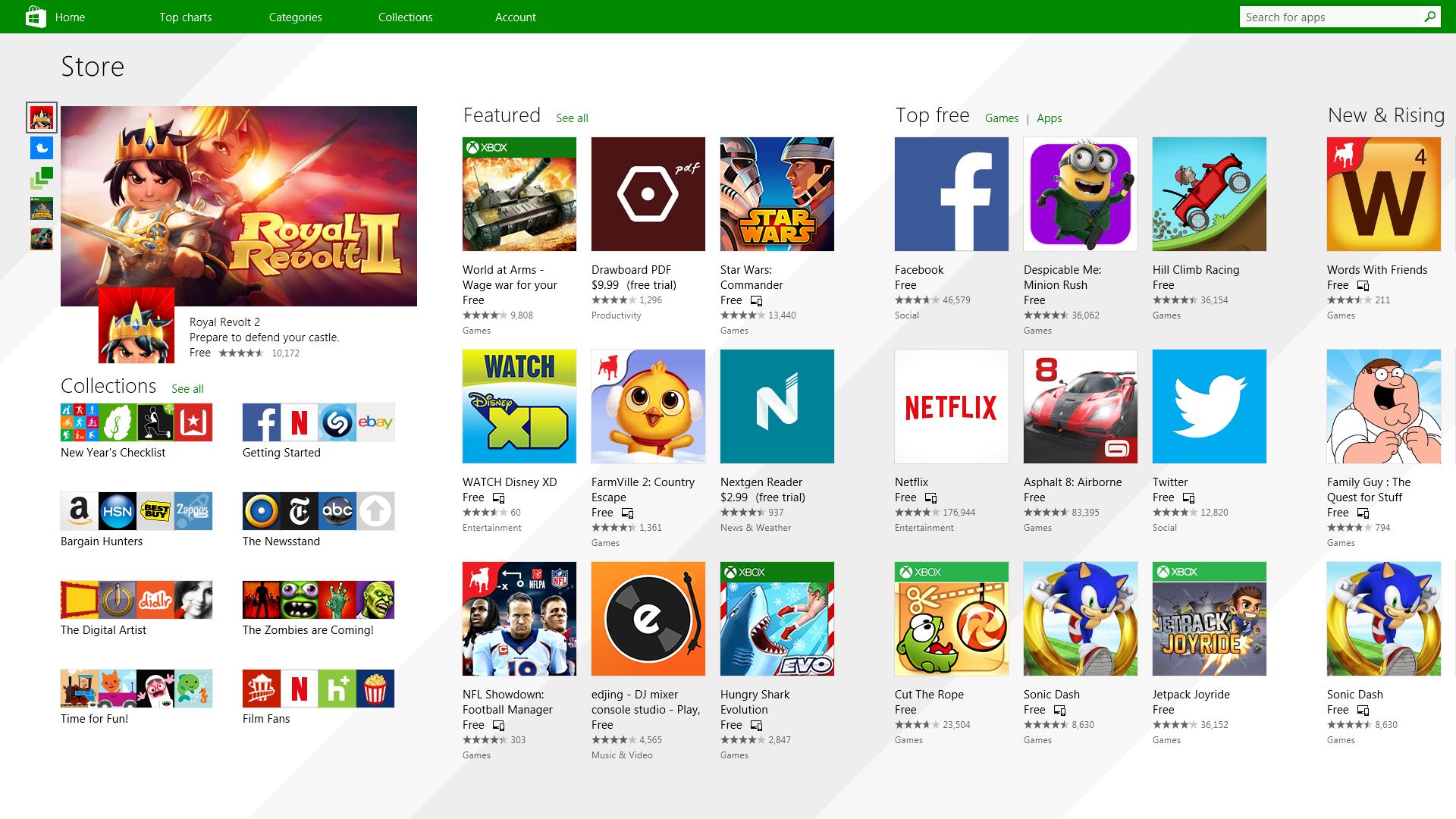 It has officially confirmed that many open source and free applications will be in it like Opera, VLC, discord, Libre office, etc. It seems that Microsoft wants to place its store as one place to go for all of your software needs.
Another great surprise is the coming of Epic games store implementation. It was officially confirmed but not explained in detail, will we have Epic store opened in Windows store or we will only get installer as a package we will see but this is some great news.
As for how it states now, it seems that the Windows store aims to eliminate searching the web for applications and bring them all into one environment with reviews and ratings so you know which one to install and use. It also features a great search engine to find proper applications for your needs.
The new store will come to Windows 10 as well but after all Windows 11 has been mostly released and adopted. So expect it via update in two or three months' time.
It would be great if some larger companies decide to join MS stores like Autodesk, Adobe, the Foundry, etc so you can install everything you need from it but one can only hope.
It has officially confirmed that many open source and free applications will be in it like Opera, VLC, discord, Libre office, etc. It seems that Microsoft wants to place its store as one place to go for all of your software needs.
Another great surprise is the coming of Epic games store implementation. It was officially confirmed but not explained in detail, will we have Epic store opened in Windows store or we will only get installer as a package we will see but this is some great news.
As for how it states now, it seems that the Windows store aims to eliminate searching the web for applications and bring them all into one environment with reviews and ratings so you know which one to install and use. It also features a great search engine to find proper applications for your needs.
The new store will come to Windows 10 as well but after all Windows 11 has been mostly released and adopted. So expect it via update in two or three months' time.
It would be great if some larger companies decide to join MS stores like Autodesk, Adobe, the Foundry, etc so you can install everything you need from it but one can only hope. 