GoodShopLanding is a browser extension for Google Chrome, Mozilla Firefox, and Safari. This extension offers the latest coupons from a range of variety stores. While this may seem useful, this extension only offers coupons from sponsored stores, not all coupons available, so the only coupons that you will get are from the Extensions Ad network. You may see additional new tabs opening randomly while browsing the internet, these tabs are opened by GoodShopLanding and usually contain last-minute store deals.
As it is often distributed via potentially unwanted advertising, and impacts browser performance in a way that many users do not want, it is classified as a Browser Hijacker and thus flagged for optional removal.
From the Author:
Shop online? Here’s your free automatic coupon finder, Gumdrop.
Never miss a coupon again
Gumdrop automatically applies the best coupons for you at checkout.
Get the best deals anywhere
With over 500,000 coupons, Gumdrop finds deals for thousands of stores, including Amazon, Expedia, and Papa John’s.
About Browser Hijackers
Browser hijackers (sometimes called hijackware) are a kind of malicious software that alters internet browser configurations without the computer owner’s knowledge or consent. These hijacks appear to be increasing at an astonishing rate around the globe, and it could be truly nefarious and sometimes harmful too. There are numerous reasons why you may have a browser hijack; but commercial, marketing, and advertising are definitely the primary purposes for their creation. Often, hijackers will force hits to sites of their choice either to increase traffic generating higher advertisement revenue, or to gain a commission for every user visiting there. However, it isn’t that harmless. Your web safety is jeopardized and it is extremely irritating. They not only mess up your web browsers, but browser hijackers can also modify the system registry, leaving your computer vulnerable to various other attacks.
Indications of browser hijack
There are many symptoms that indicate the browser is highjacked: your homepage is reset to some mysterious site; bookmark and the new tab are likewise changed; The default search page of web browser is changed; unwanted new toolbars are added to your web browser; you may see never-ending pop-up ads on your computer screen; web pages load very slowly and sometimes incomplete; you’re disallowed access to certain webpages, such as the site of an antimalware software developer like SafeBytes.
How they get into the computer
A browser hijacker can be installed on your computer if you go to an infected website, click an e-mail attachment, or download something from a file-sharing website. They can also be deployed via the installation of an internet browser toolbar, add-on, or extension. Browser hijackers sneak into your pc along with free software application downloads that you unknowingly install along with the original. A good example of some well-known browser hijackers includes Babylon, Anyprotect, Conduit, DefaultTab, SweetPage, RocketTab, and Delta Search, but the names are often changing.
Browser hijackers may record user keystrokes to collect potentially invaluable information that leads to privacy issues, cause instability on computers, significantly disrupt user’s browsing experience, and finally slow down the computer to a stage where it will become unusable.
How you can get rid of browser hijackers
Certain browser hijacking can be simply corrected by identifying and removing the corresponding malware program from your control panel. Unfortunately, most of the software programs utilized to hijack a web browser are intentionally designed to be hard to remove or detect. Moreover, manual removal requires you to carry out many time-consuming and intricate steps which are tough to conduct for new computer users.
Installing and running anti-malware software on the affected computer can automatically delete browser hijackers as well as other malicious applications. If you want to remove persistent browser hijackers quickly and effectively, install the top-rated Anti-Malware program Safebytes Anti-Malware. Along with anti-virus software, a system optimizer program can help you fix registry errors, get rid of unwanted toolbars, secure internet privacy, and enhance overall computer performance.
What you can do if Malware Stops You From Downloading Anti-virus?
Malware could cause all kinds of damage when they invade your system, from stealing your private information to deleting data files on your computer. Some malware sits in between the computer and the internet connection and blocks some or all sites that you really want to visit. It could also block you from adding anything to your machine, especially antivirus applications. If you are reading this, you may have got infected by malware that stops you from installing a computer security application like Safebytes Anti-Malware. Do as instructed below to get rid of the malware in alternate ways.
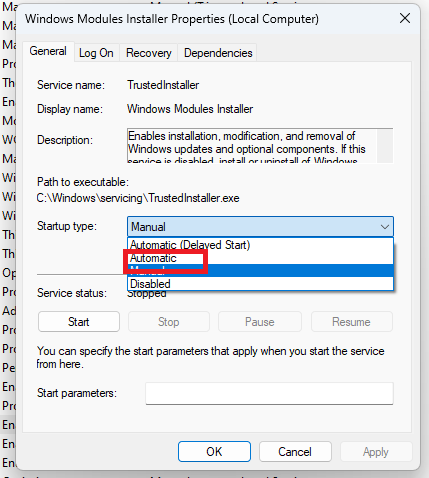
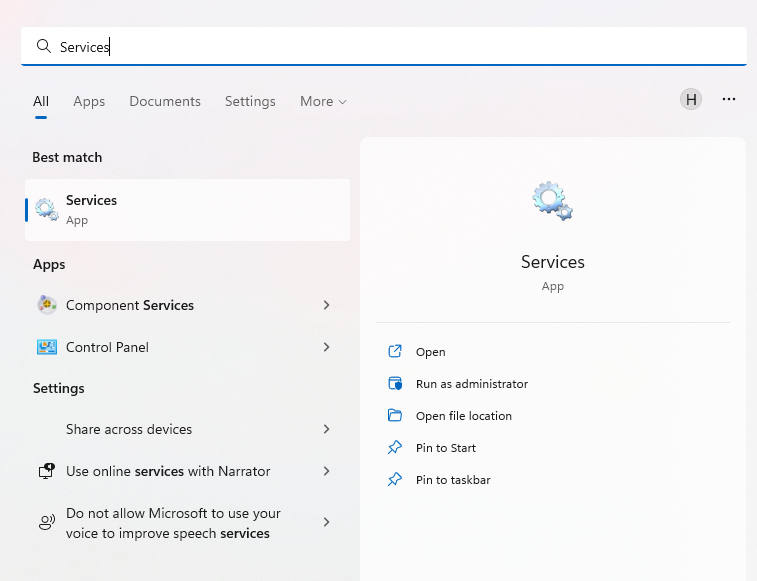
Download the application in Safe Mode with Networking
If the malware is set to load immediately when Microsoft Windows starts, entering Safe Mode could very well block the attempt. Since only the bare minimum applications and services start-up in safe mode, there are seldom any reasons for issues to take place. Here are the steps you should follow to boot into the Safe Mode of your Windows XP, Vista, or 7 computers (go to Microsoft site for instructions on Windows 8 and 10 computers).
1) At power-on/startup, press the F8 key in 1-second intervals. This will conjure up the “Advanced Boot Options” menu.
2) Use the arrow keys to select Safe Mode with Networking and hit ENTER.
3) When this mode loads, you should have internet access. Now, use your internet browser normally and navigate to https://safebytes.com/products/anti-malware/ to download Safebytes Anti-Malware.
4) Immediately after installation, do a full scan and allow the program to delete the threats it discovers.
Switch over to an alternate browser
Malicious program code could exploit vulnerabilities in a particular internet browser and block access to all anti-virus software sites. If you seem to have a virus attached to Internet Explorer, then switch over to an alternate web browser with built-in safety features, such as Firefox or Chrome, to download your favorite antivirus program – Safebytes.
Create a portable antivirus for removing malware
Another solution is to make a portable antivirus program on your USB stick. Adopt these measures to use a USB flash drive to fix your corrupted computer system.
1) Download Safebytes Anti-Malware or MS Windows Defender Offline onto a virus-free computer system.
2) Plug the USB drive into the clean PC.
3) Double-click the Setup icon of the antivirus software package to run the Installation Wizard.
4) Pick a USB flash drive as the location when the wizard asks you where you intend to install the software. Follow the directions to complete the installation process.
5) Remove the USB drive. You may now utilize this portable antivirus on the infected computer system.
6) Double click the Safebytes Anti-malware icon on the thumb drive to run the program.
7) Click the “Scan Now” button to begin the virus scan.
Let's Talk About SafeBytes Anti-Malware!
If you’re looking to download anti-malware software for your PC, there are numerous tools in the market to consider nonetheless, you cannot trust blindly anyone, regardless of whether it is paid or free program. Some of them are good but there are several scamware applications that pretend as legit anti-malware programs waiting to wreak havoc on your personal computer. When looking for antimalware software, pick one that provides solid, efficient, and total protection against all known computer viruses and malware. When thinking about reliable software programs, Safebytes AntiMalware is undoubtedly the highly recommended one.
SafeBytes anti-malware is a powerful, highly effective protection tool made to help users of all levels of IT literacy in identifying and eliminating harmful threats from their personal computers. Once you’ve got installed this tool, SafeBytes superior protection system will ensure that no viruses or malicious software can seep through your PC.
SafeBytes carries a variety of amazing features which can help you protect your PC from malware attack and damage. Listed below are some of the good ones:
Real-time Threat Response: SafeBytes delivers complete and real-time security for your PC. It’ll monitor your personal computer for suspicious activity at all times and safeguards your PC from unauthorized access.
Robust, Anti-malware Protection: With a critically acclaimed malware engine, SafeBytes gives multilayered protection which is made to catch and eliminate viruses and malware that are hidden deep inside your computer’s operating system.
Fast Scan: Safebytes Anti-Malware, using its enhanced scanning engine, offers extremely fast scanning which can promptly target any active online threat.
Safe Browsing: SafeBytes inspects the links present on a webpage for possible threats and alerts you if the site is safe to visit or not, through its unique safety rating system.
Light-weight Tool: This software program is not “heavy” on the computer’s resources, so you’ll not see any performance troubles when SafeBytes is working in the background.
24/7 Online Technical Support: For any technical issues or product guidance, you could get 24/7 professional assistance through chat and email.
To sum it up, SafeBytes Anti-Malware provides excellent protection combined with very low system resource usage with both great malware detection and prevention. You can be sure that your computer system will be protected in real-time once you put this software program to use. So if you’re searching for the absolute best malware removal application out there, and when you don’t mind shelling out some money for it, go for SafeBytes Anti-Malware.
Technical Details and Manual Removal (Advanced Users)
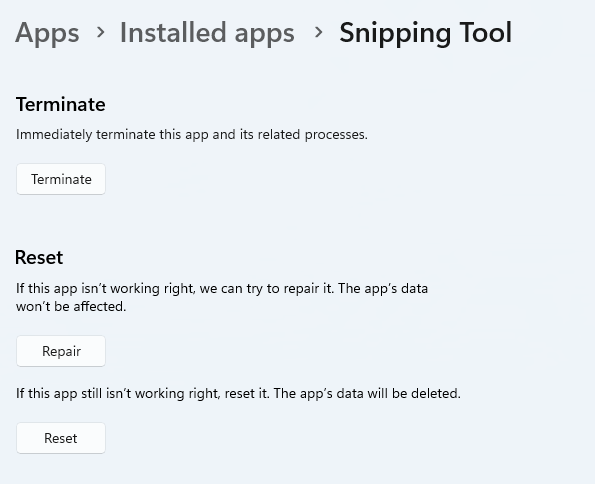
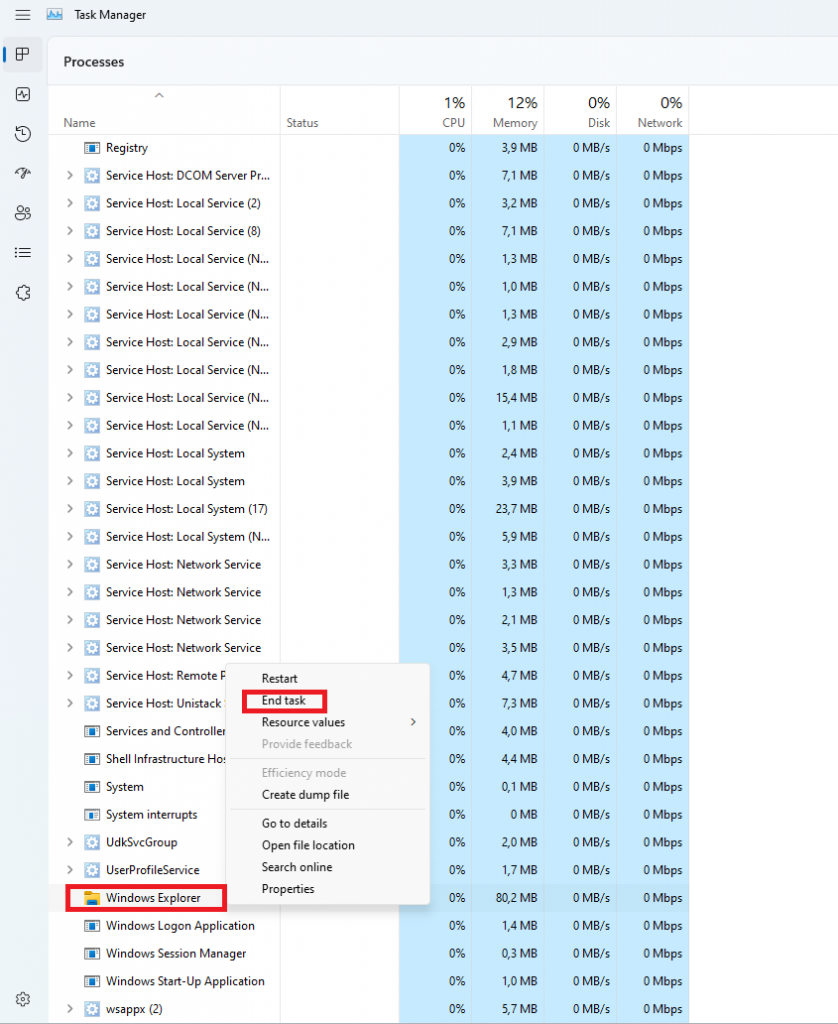
If you wish to do the removal of GoodShop Landing manually instead of employing an automated tool, you can follow these measures: Navigate to the Windows Control Panel, click the “Add or Remove Programs” and there, select the offending program to remove. In cases of suspicious versions of browser extensions, you can actually get rid of it through your browser’s extension manager. You will likely also want to reset your browser.
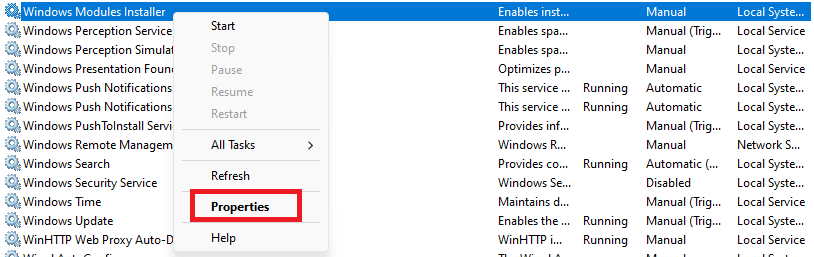
To be certain of complete removal, find the following registry entries on your computer and remove them or reset the values appropriately. Please note that this is for professional users only and might be difficult, with wrong file removal leading to additional system errors. Additionally, certain malicious programs are capable to defend against its deletion. Doing this malware-removal process in Safe Mode is suggested.