 Razer had some strange dives into stuff not really aimed at gamers and the gaming community overall like its Zephir smart mask and now it is venturing into the area of smartwatches teaming up with Fossil. I am not clear if this initiative was set in motion by Razer or Fossil and I really do not know why limited production numbers. Officially named RAZER X FOSSIL GEN 6 SMARTWATCH, this watch comes with the official following text on Razer's page:
Razer had some strange dives into stuff not really aimed at gamers and the gaming community overall like its Zephir smart mask and now it is venturing into the area of smartwatches teaming up with Fossil. I am not clear if this initiative was set in motion by Razer or Fossil and I really do not know why limited production numbers. Officially named RAZER X FOSSIL GEN 6 SMARTWATCH, this watch comes with the official following text on Razer's page:
Way more. Way faster. Way ahead of the game. Get time on your side with the limited-edition Razer X Fossil Gen 6 Smartwatch—only 1,337 pieces worldwide. Designed for the next generation of gamers, supercharge your style with customizable straps, dials, Razer Chroma™ RGB effects, and more.
Now, I am a fan of Razer and I like their products, mostly keyboards and mouse altho chair is also very good and in top of the product line in that field but I can not really stand behind this product and decision, and the only reason why I can not stand behind it is this 1337 (leet, or elite) a limited number of available pieces that is nothing more than a gimmick to sell watches at a higher price. Watch itself is not really bad, as a matter of fact, it has some solid hardware statistics.
Technical characteristics
Featuring a 1.28-inch AMOLED Display with 3 unique Razer watch faces (Analog, Text, Chroma*), 4 customizable Razer Chroma™ RGB effects, and 2 custom-designed, interchangeable straps, this Razer's baby is packing 44mm, Stainless Steel case with 22mm, straps. It runs on Wear OS by Google as an operating system of a choice and under software, it is packing Qualcomm Snapdragon Wear 4100+ CPU paired with 1GB of RAM and 8GB Storage. The display is running at 416x416 resolution with 326ppi.
Watch input is with 2 configurable Push buttons, One rotating Home button, touchscreen, and voice. It has in it a loudspeaker, microphone, and vibration. Connection is via Bluetooth 5.0, GPS, NFC SE, and Wi-Fi. The battery can in their word work for 24 Hr + multi-day Extended Mode **Varies based on usage and after updates install**. USB data cable with magnetic dock snaps to split rings on the watch case back and spins 360 degrees for ease of use. Approximately half an hour to reach 80%. Sensors included in the watch itself are: Accelerometer, Altimeter, Ambient Light, Compass, Gyroscope, Off-body IR, PPG Heart Rate, SPO2.
Smartwatch is water-resistant up to 3 ATM & it comes with preloaded apps like: Agenda, Alarm, Battery-Optimized Activity Mode, Calendar, Cardio Level Tracking, Cardiogram, Contacts, Enhanced Phone Dialer App, Google Assistant, Google Fit (Workout, Heart Rate, Goals, Breathe), Google Maps, Google Pay™, Google Play Store, Nike Run Club, Noonlight, Smart Battery Modes, Spotify, Stopwatch, Timer, Translate, Wellness Apps with Sleep Tracking.
Conclusion
Watch is Dropping on 01.10.22, 8 AM PST which is 4 days from now and altho it is an interesting device with solid hardware I can not stand behind it due to its limited edition numbers and with $329 price tag. With the same amount of money, you can get yourself Samsung or Apple watch with more features packing. But of course, that is just my personal preference and if you want to own this limited edition Razer smartwatch, go for it.
 Error Causes
Error Causes Razer had some strange dives into stuff not really aimed at gamers and the gaming community overall like its Zephir smart mask and now it is venturing into the area of smartwatches teaming up with Fossil. I am not clear if this initiative was set in motion by Razer or Fossil and I really do not know why limited production numbers. Officially named RAZER X FOSSIL GEN 6 SMARTWATCH, this watch comes with the official following text on Razer's page:
Razer had some strange dives into stuff not really aimed at gamers and the gaming community overall like its Zephir smart mask and now it is venturing into the area of smartwatches teaming up with Fossil. I am not clear if this initiative was set in motion by Razer or Fossil and I really do not know why limited production numbers. Officially named RAZER X FOSSIL GEN 6 SMARTWATCH, this watch comes with the official following text on Razer's page:
 Researchers have discovered 16 vulnerabilities in Bluetooth connections that could be exploited and make from minor to some serious damage to your device. The flaw can be used on chips manufactured by Intel, Qualcomm, and Texas Instruments while connecting to external devices like speakers, headphones, keyboards, mice, etc.
Researchers have discovered 16 vulnerabilities in Bluetooth connections that could be exploited and make from minor to some serious damage to your device. The flaw can be used on chips manufactured by Intel, Qualcomm, and Texas Instruments while connecting to external devices like speakers, headphones, keyboards, mice, etc.
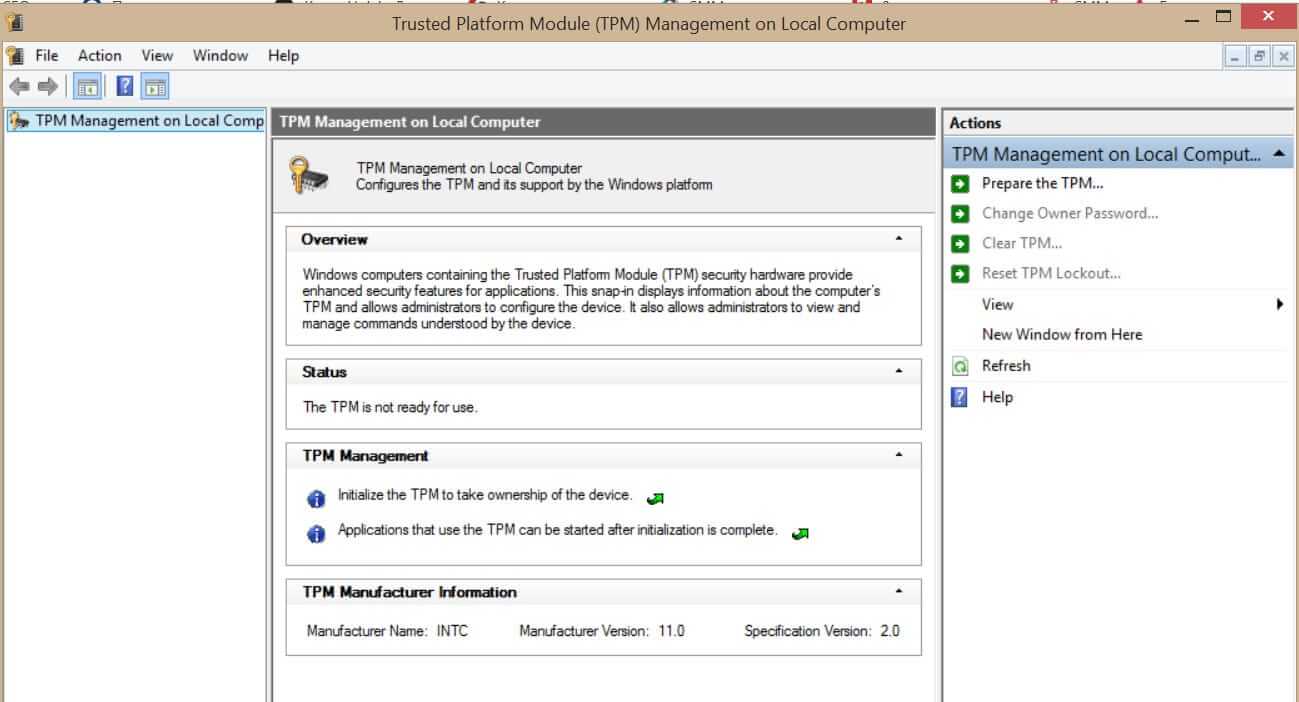 What exactly is TPM?
What exactly is TPM? Netflix was one that made streaming service standard and even after some stumbles even today it is still a respected service.
So in that spirit, we are bringing you the list of all new and old movies and TV series releasing to NETFLIX this September.
Netflix was one that made streaming service standard and even after some stumbles even today it is still a respected service.
So in that spirit, we are bringing you the list of all new and old movies and TV series releasing to NETFLIX this September.
