PC Optimizer Pro is a PC optimizer utility developed by Xportsoft Technologies. It is classified as a potentially unwanted program, due to its aggressive scan and registration reminders, and that it is often distributed bundled with other programs in a manner that leads many users to not know how it got on their computer. While not inherently malicious, PC Optimizer Pro adds numerous registry keys, startup entries and while running consumes a relatively high amount of system resources, especially during its scans. The software installs from a .exe file that is around 5.20 MB or 5.453.240 Bytes (depending on the version). As of the publication of these videos, the current version of PC Optimizer Pro was detected as malicious or potentially unwanted by at least 21 AntiViruses.
About Potentially Unwanted Applications
If you have ever installed freeware or shareware, chances are high that your computer can get installed with a bunch of unwanted applications. A Potentially Unwanted Program, also called PUP, in short, is actually software that contains adware, installs toolbars, or has other hidden goals. These kinds of programs are almost always bundled up with free software which you download from the net or are also bundled within the custom installers on many download sites.
PUPs did not really constitute pure “malware” in the strict sense of the term. Just like malicious software, PUPs cause problems when downloaded and installed on your PC, but what makes a PUP different is that you give consent to download it – although the truth is vastly different – the software installation package actually tricks you into accepting the installation. Irrespective of whether it is regarded as malware or not, PUPs are nearly always harmful to the user as they might bring on adware, spyware, keystroke logging, and also other bad crapware features on your computer.
What do PUPs do on your computer, exactly?
Potentially Unwanted Programs come in many forms and varieties, but in most instances, these are adware programs that show annoying pop-up adverts and advertisements on websites you check out. The PUPs also get installed into your computer in the form of web browser add-ons and toolbars. Not only they needlessly take up space on your computer screen, but toolbars may also manipulate search engine results, watch your web browsing activities, decrease your web browser’s efficiency, and decelerate your internet connection to a crawl.
Potentially Unwanted Programs at times act quite similarly to viruses or spyware. Some PUPs include keyloggers, dialers, along with other software to gather your private details that may result in identity theft. These are programs that don’t do anything good for you; in addition to taking over space on your hard drive, they also slow down your computer, often modify settings without your approval, the list of bothersome features goes on.
Ways to avoid PUPs
• Always study the EULA and privacy statement. Don’t agree until you know precisely what you are acknowledging.
• Choose the “custom” install whenever installing a software program. In particular, look closely at those small boxes that have been checked as default, where you may ‘agree’ to receive promotions or install software bundlers.
• Use good antivirus software, like Safebytes Anti-Malware that offers real-time protection against PUPs.
• Avoid adding a freeware program you do not use. Turn off or remove toolbars and web browser extensions you don’t really need.
• Always download software from reliable sources like official sites as opposed to untrustworthy sharing space. Avoid file-hosting sites where/when possible.
What you can do if Malware Prevents You From Downloading Or Installing Antivirus?
Practically all malware is bad, but certain types of malware do much more damage to your computer than others. Certain malware goes to great lengths to stop you from downloading or installing anything on your personal computer, particularly antivirus applications. If you are reading this right now, you have probably recognized that a malware infection is the real cause of your blocked web connectivity. So what to do if you need to install an antivirus program like Safebytes? There are a few steps you can take to circumvent this problem.
Install in Safe Mode
The Windows OS has a special mode known as “Safe Mode” in which just the bare minimum required programs and services are loaded. In the event the malware is blocking the internet connection and affecting the computer, running it in Safe Mode will let you download antivirus and run a diagnostic scan while limiting possible damage. To start the computer into Safe Mode, press the “F8” key on your keyboard right before the Windows boot screen comes up; Or right after normal Windows boot up, run MSConfig, look over “Safe Boot” under Boot tab, and click Apply. After you reboot into Safe Mode with Networking, you can download, install, and update anti-malware software from there. Right after installation, run the malware scanner to remove standard infections.
Switch to an alternate browser
Some malware may target vulnerabilities of a specific browser that block the downloading process. If you seem to have malware attached to Internet Explorer, then switch over to an alternate web browser with built-in safety features, such as Firefox or Chrome, to download your favorite antivirus program – Safebytes.
Install and run anti-virus from the USB drive
Another solution is to create a portable anti-malware program on your USB stick. Adopt these measures to employ a thumb drive to clean your infected computer system.
1) Download Safebytes Anti-Malware or MS Windows Defender Offline onto a clean PC.
2) Plug the Thumb drive into the clean computer.
3) Run the setup program by double-clicking the executable file of the downloaded software, with a .exe file format.
4) Choose the flash drive as the location for saving the file. Do as instructed on the screen to complete the installation process.
5) Now, plug the pen drive into the corrupted computer.
6) Double-click the anti-malware software EXE file on the USB flash drive.
7) Press the “Scan” button to run a full system scan and remove viruses automatically.
SafeBytes Anti-Malware: Lightweight Malware Protection for Windows PC
These days, an anti-malware tool can protect your computer from different types of online threats. But how to choose the best one amongst numerous malware protection application that’s available out there? You may be aware, there are numerous anti-malware companies and tools for you to consider. A few are well worth your money, but many aren’t. You have to be very careful not to choose the wrong application, especially if you buy a paid application. In terms of commercial anti-malware application options, many people select well-known brands, such as SafeBytes, and are quite happy with it.
SafeBytes anti-malware is a powerful, highly effective protection tool created to help end-users of all levels of IT literacy in detecting and eliminating malicious threats from their computer. Using its cutting-edge technology, this software can assist you to eliminate several types of malware such as computer viruses, trojans, PUPs, worms, ransomware, adware, and browser hijackers.
SafeBytes has excellent features when compared to other anti-malware programs. Let’s have a look at a few of them below:
Robust, Anti-malware Protection: Safebytes is made on the best virus engine within the industry. These engines will find and get rid of threats even during the initial phases of a malware outbreak.
Active Protection: Malware programs aiming to enter the system are discovered and stopped as and when detected by the SafeBytes active protection shields. It’ll check your PC for suspicious activity at all times and safeguards your personal computer from unauthorized access.
High-Speed Malware Scanning Engine: SafeBytes’s high-speed malware scanning engine minimizes scan times and extends the life of the battery. Simultaneously, it will effectively detect and eliminate infected computer files or any online threat.
Website Filtering: SafeBytes checks the hyperlinks present on a webpage for possible threats and informs you whether the site is safe to explore or not, through its unique safety rating system.
Lowest CPU/Memory Usage: SafeBytes is a lightweight and user-friendly antivirus and antimalware solution. Since it utilizes negligible computer resources, this tool leaves the computer’s power exactly where it belongs to: with you.
Premium Support: You may get high levels of support round the clock if you’re using their paid software.
Technical Details and Manual Removal (Advanced Users)
If you wish to manually remove PCOptimizerPro without the use of an automated tool, it may be possible to do so by removing the program from the Windows Add/Remove Programs menu, or in cases of browser extensions, going to the browsers AddOn/Extension manager and removing it. You will likely also want to reset your browser.
To ensure the complete removal, manually check your hard drive and registry for all of the following and remove or reset the values accordingly. Please note that this is for advanced users only and may be difficult, with incorrect file removal causing additional PC errors. In addition, some malware is capable of replicating or preventing deletion. Doing this in Safe Mode is advised.
The following files, folders, and registry entries are created or modified by PCOptimizerPro
Files:
DesktopPC Optimizer Pro.lnk.
%Programs%PC Optimizer ProLive Support.url.
%Programs%PC Optimizer ProPC Optimizer Pro.lnk.
%Programs%PC Optimizer ProUninstallation Guide.url.
%Programs%PC Optimizer ProVisit Website.url.
%ProgramFiles%PC Optimizer ProPCOptimizerPro.exe.
%ProgramFiles%PC Optimizer ProPCOptProCtxMenu.dll.
%ProgramFiles%PC Optimizer ProPCOptProTrays.exe.
%ProgramFiles%PC Optimizer ProStartApps.exe.
%ProgramFiles%PC Optimizer Prouninst.exe.
%QuickLaunch%PC Optimizer Pro.lnk.
WindowsTasksPC Optimizer Pro Idle.job.
WindowsTasksPC Optimizer Pro Scan.job.
WindowsTasksPC Optimizer Pro startups.job.
WindowsTasksPC Optimizer Pro Updates.job.
C:DOCUME1USER1LOCALS1Tempoptprosetup.exe
C:WINDOWSsystem32netmsg.dll
C:DOCUME1USER1LOCALS1Tempoptprosetup.exe
C:DOCUME1USER1LOCALS1Tempis-SJGJ9.tmpoptprosetup.tmp
C:DOCUME1USER1LOCALS1Tempis-NTRVH.tmp_isetup_shfoldr.dll
C:WINDOWSsystem32shfolder.dll
C:DOCUME1USER1LOCALS1Tempis-NTRVH.tmpOptProHelper.dll
C:DOCUME1USER1LOCALS1Tempis-NTRVH.tmpitdownload.dll
C:1e4e2d65e12311cac2c0eeb8c5c1d7bd1ddc865b367b98b56bc2330bf18436
C:WINDOWSRegistrationR000000000007.clb
C:DOCUME1USER1LOCALS1Tempoptprosetup.exe
C:WINDOWSsystem32shfolder.dll
C:1e4e2d65e12311cac2c0eeb8c5c1d7bd1ddc865b367b98b56bc2330bf18436
C:WINDOWSRegistrationR000000000007.clb
C:WINDOWSsystem32shell32.dll
C:DOCUME1USER1LOCALS1Tempis-SJGJ9.tmpoptprosetup.tmp
C:Program FilesOptimizer Pro 3.99OptimizerPro.exe
C:Program FilesOptimizer Pro 3.99unins000.exe
C:Program FilesOptimizer Pro 3.99OptProStart.exe
c:autoexec.bat
C:DOCUME1USER1LOCALS1Tempoptprosetup.exe
C:DOCUME1USER1LOCALS1Tempis-SJGJ9.tmpoptprosetup.tmp
C:DOCUME1USER1LOCALS1Tempis-NTRVH.tmp_isetup_shfoldr.dll
C:DOCUME1USER1LOCALS1Tempis-NTRVH.tmpOptProHelper.dll
C:DOCUME1USER1LOCALS1Tempis-NTRVH.tmpitdownload.dll
C:Program FilesOptimizer Pro 3.99is-BDCDJ.tmp
C:Program FilesOptimizer Pro 3.99is-DB4S5.tmp
C:Program FilesOptimizer Pro 3.99is-C16E7.tmp
C:Program FilesOptimizer Pro 3.99is-QE691.tmp
C:Program FilesOptimizer Pro 3.99is-GQ78C.tmp
Registry:
Key 003B9C22-6FE0-4BCA-A73F-9AA99B9BBDAA at HKEY_CLASSES_ROOTTypeLib.
Key 12AB121E-44C6-488B-8773-B0AE25E662E1 at HKEY_CLASSES_ROOTInterface.
Key 203ABD21-41F1-4F1B-BAE3-D6A89A90D239 at HKEY_CLASSES_ROOTCLSID.
Key PC Optimizer Pro at HKEY_CURRENT_USERSoftware.
Key PC Optimizer Pro at HKEY_LOCAL_MACHINESOFTWARE.
Key PC Optimizer Pro at HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionUninstall.
Key PCOptimizerPro.exe at HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionApp Paths.
Key PCProCtxMenu at HKEY_CLASSES_ROOT*shellexContextMenuHandlers.
Key PCProCtxMenu at HKEY_CLASSES_ROOTlnkfileshellexContextMenuHandlers.


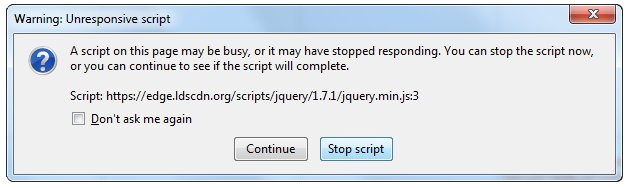 Check for a poorly functioning background process
Check for a poorly functioning background process The final solution. Contact Firefox about these errors on your browser. Oftentimes, these errors occur when you attempt to visit particular websites. Mark the offending websites' URLs and include them in your communications with Firefox.
Sometimes you can also contact the website owner yourself and request them to check their website's code.
Following are additional measures you can take to resolve the Unresponsive Script error.
The final solution. Contact Firefox about these errors on your browser. Oftentimes, these errors occur when you attempt to visit particular websites. Mark the offending websites' URLs and include them in your communications with Firefox.
Sometimes you can also contact the website owner yourself and request them to check their website's code.
Following are additional measures you can take to resolve the Unresponsive Script error.
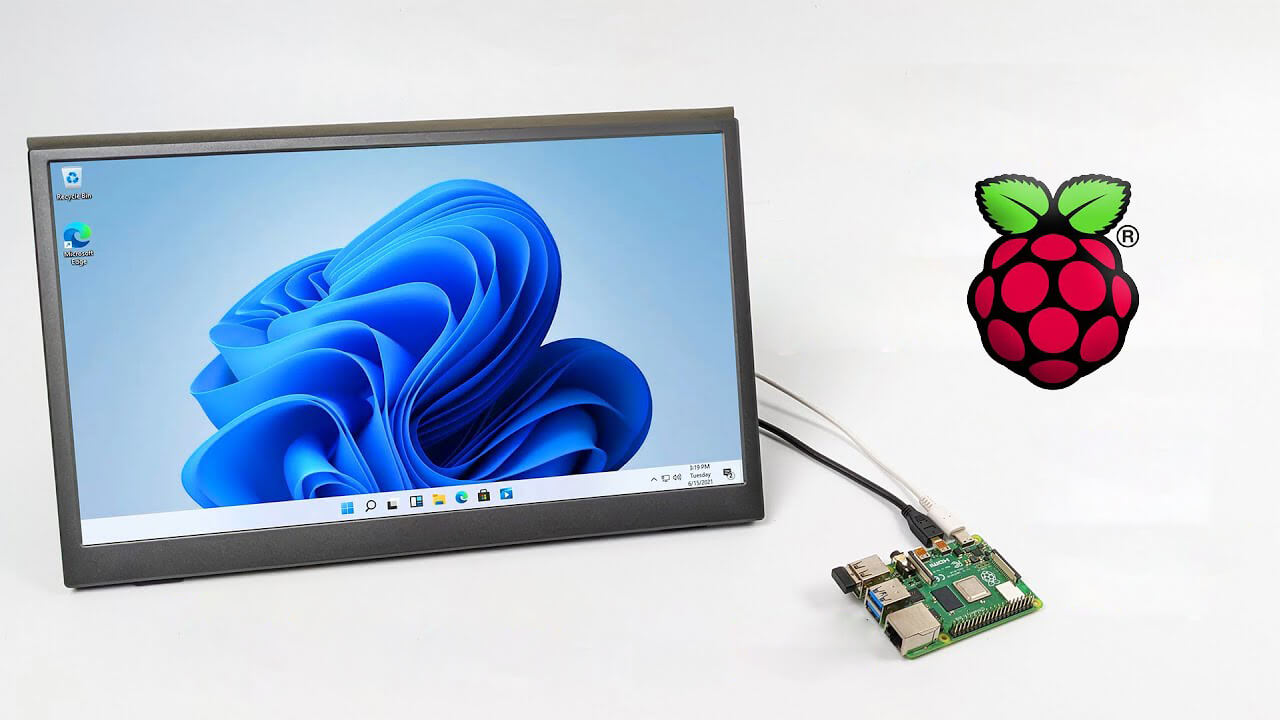 Raspberry Pi 4 and things you need for Windows 11 installation
Raspberry Pi 4 and things you need for Windows 11 installation Microsoft just released Windows 11 ISo file, based on the latest Insider Preview Build 22000.132. Inside build, you can try all-new features like clock updated app, snip tool, and everything releases so far via various patches. You can also use Windows 11 ISO file to do a clean install on your computer, but if you go with this option all of your existing files will be deleted.
Microsoft says it added the ability to name your PC during the setup experience. You’ll also get to experience the Get Started app that’s designed to help you get going on your new Windows 11 PC (even if it’s not actually a new one).
Microsoft just released Windows 11 ISo file, based on the latest Insider Preview Build 22000.132. Inside build, you can try all-new features like clock updated app, snip tool, and everything releases so far via various patches. You can also use Windows 11 ISO file to do a clean install on your computer, but if you go with this option all of your existing files will be deleted.
Microsoft says it added the ability to name your PC during the setup experience. You’ll also get to experience the Get Started app that’s designed to help you get going on your new Windows 11 PC (even if it’s not actually a new one).
