Error 651 - What is it?
Are you a Windows 7 PC user? Are you experiencing
error 651? If yes, then read on. We will discuss what is this error, the causes, and easy DIY solutions to help you resolve this issue immediately.
Error 651 is a common Windows 7 error. This error occurs when you try to connect using your PPPoE connections. The error message is displayed in the following format:
“Error 651: The Modem (or other connecting device) has reported an error.”
Solution
 Error Causes
Error Causes
The error code 651 occurs due to multiple reasons. However, some of the most common error causes include:
- The raspppoe.sys file saved in the wrong location
- IP setting issues
- Registry issues
Further Information and Manual Repair
Here are some of the best and easiest solutions to resolve the error code 651 on your system immediately. These solutions are so easy to perform that you don’t need any technical expertise or knowledge to get started. So here we go!
Solution 1: Reset TCP/IP Settings
To reset TCP/IP settings on your PC, here’s what you need to do.
Simply replace the RAS PPPoE driver. First open a command prompt, then write the following command in the command prompt: TAKEOWN /F"C:Windowssystem32driversraspppoe.sys" ICACLS "C:Windowssystem32driversraspppoe.sys" /grant administrators:F. After that, press enter to continue.
Now close the command prompt and go to the folder C:\Windows\system32\drivers, here rename the raspppoe.sys file to raspppoe2.sys. Now right click on save the link as Vista RAS PPPoE Driver and save it in the C:\Windows\system32\drivers folder.
Once this process is complete, to activate changes made, restart your PC.
This is most likely to resolve the error code 651 on your system.
Solution 2: Try Power Cycling your Modem and your Router
This is another way to resolve error 651. However, before you try this solution, it is recommended that you save all your work on your system, close all your open applications, and then shut down your PC.
After that first turn your router off and wait for about 2 minutes. Then turn off your modem too. Now disconnect all the Ethernet cables that are connected to your modem, router and your system.
Reconnect them again and make sure that the connections are not loose. After reconnecting the cables, reboot your PC and switch on the modem first.
After your modem gets initialized, turn on the router. See if this procedure works. If it does, then that’s great the issue is resolved. However, if the error persists, then this indicates deeper problems. The error message is triggered due to registry issues.
Solution 3: Clean and Repair the Registry
Sometimes the underlying cause of error 651 is a
corrupt and damaged registry. Registry is the database where operating system stores all the information associated with installed programs and activities performed on your PC. Registry issues typically result due to poor PC maintenance.
When you don’t clean the registry the unnecessary and obsolete files accumulate and acquire a lot space. It damages the registry and DLL files.
This often leads to disk fragmentation and files are then saved in segments in different locations. This also slows down your PC performance. This could also be the reason for why the raspppoe.sys file is saved in the wrong location.
Though you can repair the registry manually but it may be complex for you especially if you are not technically sound. And besides, it is also slightly time-consuming.
Restoro - Premier Registry Cleaner
Therefore, to resolve errors like 651 triggered by the registry issues on your system in seconds, it is advisable to download Restoro.
Restoro is a cutting-edge and multi-functional PC Fixer. It is deployed with a powerful intuitive algorithm and multiple highly functional utilities designed to resolve practically all types of PC errors. It includes utilities like a registry cleaner, an antivirus, and a system optimizer.
The registry cleaning feature scans for all types of registry issues and errors and resolves them instantly. It wipes out unnecessary and redundant files like cookies, internet history, junk files, and bad/ invalid registry entries. It cleans the registry freeing up space.
Furthermore, it also repairs the damaged files and restores the registry back to normal.
Restoro Special Features
Other features include an antivirus that removes all types of malicious software hiding in your PC including
viruses, Trojans, spyware, malware, and adware. The system optimizer feature ensures that your computer performs at its optimal level at all times.
Restoro is safe and bug-free. Its user-friendly interface and simple navigations makes it quite easy for users to operate it without any difficulty. Furthermore, compatibility is not an issue with this software. You can download it on any Windows version.
Click here to download Restoro and fix error 651 on your PC today!
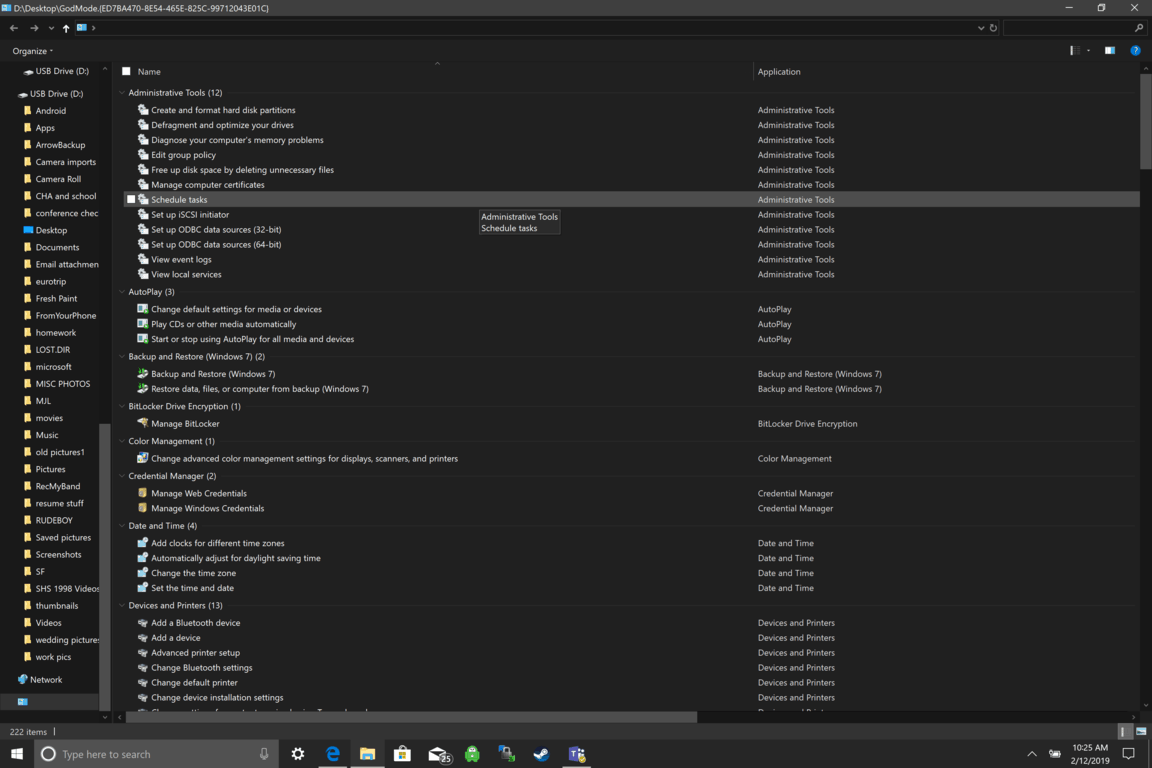 Like in Windows 10, Windows 11 will also support God mode to be enabled and used. For those readers that do know what God mode is, let me explain it in simple terms. God mode is the icon on the desktop that once clicked will open and let you adjust every option in the control panel and some hidden features for Windows inside one application.
Like in Windows 10, Windows 11 will also support God mode to be enabled and used. For those readers that do know what God mode is, let me explain it in simple terms. God mode is the icon on the desktop that once clicked will open and let you adjust every option in the control panel and some hidden features for Windows inside one application.

